---
title: "Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing | DMARC Report"
description: "Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing from DMARC Report explains practical steps for email authentication, domain protection."
image: "https://dmarcreport.com/og/blog/adidas-data-breach-whatsapp-image-threat-silent-ransom-vishing.png"
canonical: "https://dmarcreport.com/blog/adidas-data-breach-whatsapp-image-threat-silent-ransom-vishing/"
---
Quick Answer
\_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing
Related: [Free DMARC Checker](/tools/dmarc-checker/) ·[How to Create an SPF Record](/tools/spf-record-generator/) ·[SPF Record Format](/blog/spf-format-checker-dos-and-donts-for-email-authentication/)
Share
[ ](https://www.linkedin.com/sharing/share-offsite/?url=undefined%2Fblog%2Fadidas-data-breach-whatsapp-image-threat-silent-ransom-vishing%2F "Share on LinkedIn") [ ](https://twitter.com/intent/tweet?text=Adidas%20Data%20Breach%2C%20Whatsapp%20Image%20Threat%2C%20Silent%20Ransom%20Vishing&url=undefined%2Fblog%2Fadidas-data-breach-whatsapp-image-threat-silent-ransom-vishing%2F "Share on X/Twitter") [ ](https://www.facebook.com/sharer/sharer.php?u=undefined%2Fblog%2Fadidas-data-breach-whatsapp-image-threat-silent-ransom-vishing%2F "Share on Facebook") [ ](https://reddit.com/submit?url=undefined%2Fblog%2Fadidas-data-breach-whatsapp-image-threat-silent-ransom-vishing%2F&title=Adidas%20Data%20Breach%2C%20Whatsapp%20Image%20Threat%2C%20Silent%20Ransom%20Vishing "Share on Reddit") [ ](mailto:?subject=Adidas%20Data%20Breach%2C%20Whatsapp%20Image%20Threat%2C%20Silent%20Ransom%20Vishing&body=Check out this article: undefined%2Fblog%2Fadidas-data-breach-whatsapp-image-threat-silent-ransom-vishing%2F "Share via Email")


> From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
\_According to the [FBI’s 2022 Internet Crime Report (IC3)](https://www.ic3.gov/Media/PDF/AnnualReport/2022IC3Report.pdf), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing
```
```
/
```
```
RSS Feed
```
Share
Link
Embed
```
/\*! This file is auto-generated \*/ ’ title=“Embed Code” class=“input-embed input-embed-25521” readonly/>
```
```
It’s the 4th week of May, and we are once again back with the latest cyber news. Our only goal is to \*\*safeguard your data and peace of mind by educating you about the current cybersecurity trends and latest cyber incidents. So stay with us and secure your data from [cybercriminals](https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/back-to-the-hype-an-update-on-how-cybercriminals-are-using-genai).
This week, we will talk about one of the most shocking cyberattack incidents- the Adidas data breach. Next, we will throw light on how [cybercrooks](https://wtop.com/local/2025/04/cyber-crooks-scam-dc-md-and-va-out-of-848-million-in-2024/) are misusing WhatsApp images to break into your device. Lastly, we will discuss vishing campaigns designed to target the USA-based legal firms .
Let’s not waste any more \*\*time and get straight into the details!
## Adidas’ company data breached by a threat actor!
Recently, Adidas has been targeted by a cybercrook through a [third-party service provider](https://www.websitepolicies.com/blog/third-party-service-provider). The threat actor has managed to gain access to the contact information of customers who have recently connected with the **customer service help desk**. _The lifestyle brand has assured that sensitive customer data, like passwords, financial details, and credit card information, has not been compromised_.
Adidas is informing all its customers about the cyberattack. Additionally, it’s working closely with [law enforcement](https://en.wikipedia.org/wiki/Law%5Fenforcement%5Fin%5Fthe%5FUnited%5FStates) authorities and [data protection agencies](https://epic.org/campaigns/dpa/). Adidas is also running a full-fledged investigation alongside **information security experts**. As of now, the attackers have not yet been identified. Also, Adidas has not revealed the name of the third-party customer service app.
Cybersecurity experts believe that third-party breaches can easily turn into organizational breaches. It is therefore important that organizations start taking security assessments seriously. [Multifactor authentication](https://www.onelogin.com/learn/what-is-mfa), [zero-trust architecture](https://www.zscaler.com/resources/security-terms-glossary/what-is-zero-trust-architecture) for **all the vendors**, as well as real-time identity infrastructure monitoring, can easily prevent such [third-party breaches](https://www.upguard.com/blog/third-party-breach).
What happened to Adidas is not a \*\*one-of-a-kind cyber incident. Similar [threat attacks](https://www.usatoday.com/story/news/world/2025/04/24/ukraine-war-russia-trump-putin-peace-talks/83244837007/) have affected other popular brands such as [Marks & Spencer,](https://www.aljazeera.com/news/2025/5/2/harrods-ms-hit-by-cyberattack-what-happened-whos-behind-it) Co-op Group, and Harrods lately.

## Still have the WhatsApp auto-download image feature on? You might be the next target of threat actors!
We all know how harmful it can be if you click on malicious links or share an OTP with a stranger. But do you know that even downloading WhatsApp images is no longer safe? WhatsApp is one of the most widely used apps across the world for communication with others. But over time, it has become a favorite among threat actors. From sending [malicious links](https://www.scworld.com/news/new-usps-text-scam-uses-unique-method-to-hide-malicious-pdf-links) to OTPs and now this [WhatsApp image scam](https://cybersecuritynews.com/whatsapp-image-lost-2-lakhs/#google%5Fvignette), WhatsApp is no longer as safe as it used to be a few years back!
[Threat actors](https://www.nbcnews.com/tech/security/us-treasury-says-computers-hacked-chinese-threat-actor-rcna185809) embed malicious software within so-called harmless images. This technique is also known as steganography. The malware stays hidden without raising any suspicion. Also, the \*\*standard security systems in your smartphone fail to detect such image files.
The moment a user downloads and opens the image, the malware is silently installed, accessing user data, passwords, OTPs, financial details , and so on without their knowledge.
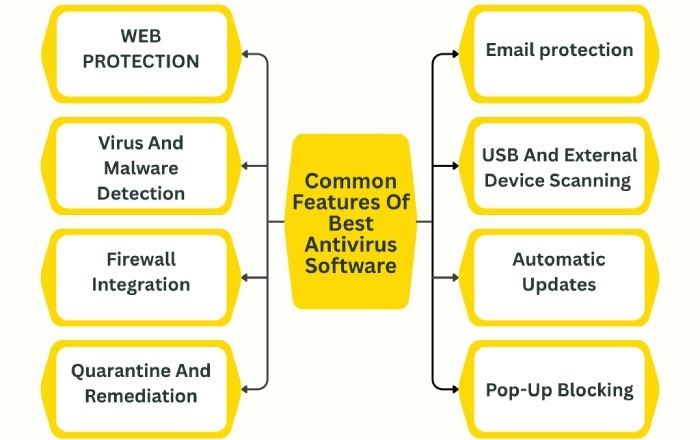
[Cybersecurity](https://dmarcreport.com/blog/how-to-educate-or-train-employees-on-cybersecurity/) experts recommend deploying two-factor authentication, **updating your device regularly**, and using credible [antivirus software](https://www.crn.com/news/security/2024/kaspersky-sad-to-exit-us-market-layoffs-ahead-at-antivirus-software-company). Also, they urge users to avoid downloading images from unknown WhatsApp chats. Turning off the auto download feature can be a smart move in such a situation.
Implementing [DMARC](https://dmarcreport.com/), [DKIM](https://dmarcreport.com/what-is-dkim/), and [SPF](https://autospf.com/blog/spf-guide-understanding-sender-policy-framework/) helps strengthen cybersecurity by authenticating email sources, while \*\*regularly updating your device ensures protection against the latest security threats.
## Silent Ransom Group using vishing campaign to target law firms!
The Silent Ransom Group has been targeting [USA-based law firms](https://www.clio.com/blog/best-law-firms-in-america/) with a specially designed [vishing campaign](https://www.darkreading.com/endpoint-security/fbi-silent-ransom-group-vishing-law-firms). Their ultimate goal is to leverage [social engineering](https://www.ibm.com/think/topics/social-engineering) tactics and gain access to the [sensitive data](https://www.csoonline.com/article/3819170/nearly-10-of-employee-gen-ai-prompts-include-sensitive-data.html) of the victims and then extort money for the same. _The group has other names as well- Chatty Spider, Luna Moth, and UNC3753_. They have been active since 2022\*\*. Their specialty lies in seeking ransom for the [stolen data](https://www.cbsnews.com/news/social-security-number-leak-npd-breach-what-to-know/) without using any kind of ransomware.

Their latest stunt involves \*\*setting up IT-themed calls with victims backed by callback [phishing emails](https://www.techtarget.com/searchsecurity/news/366547912/Researchers-put-LLMs-to-the-test-in-phishing-email-experiment). This keeps the victims engaged while the group gains remote access to the victim’s device. The style in which they carry out this campaign appears quite similar to the activities of ransomware groups [Black Basta](https://www.bleepingcomputer.com/news/security/microsoft-teams-tactics-malware-connect-black-basta-cactus-ransomware/) and 3 AM.
A member from the Silent Ransom Group calls an employee of the target company and poses as an employee from the IT department of the same company. \_They then direct the victim to a remote access session backed by Zoho Assist, AnyDesk, Syncro, etc. \_They try to create a sense of urgency and insist on the [device’s remote access](https://www.reuters.com/sustainability/climate-energy/ghost-machine-rogue-communication-devices-found-chinese-inverters-2025-05-14/).
The [FBI](https://www.bbc.com/news/articles/c0rqpp52j5vo) has issued a warning against similar attacks and is trying to understand the evolution of [cybercrime](https://english.elpais.com/technology/2024-12-31/cybercrime-hits-record-levels-in-2024-as-ai-makes-attacks-more-targeted.html) techniques. Voice-based social engineering tactics, or vishing, being used by this threat group is a staggering reminder that cybercrooks are already moving one step ahead and that they work persistently to **stay ahead of the game**.
The FBI highly recommends that organizations, especially law firms , maintain basic [cyber hygiene](https://www.k12dive.com/news/powerschool-data-breach-lawsuits-negligence/737900/), such as using strong passwords, enabling multifactor authentication, and avoiding unsolicited emails or calls to prevent such cyber mishaps.
## Topics
[ dkim ](/tags/dkim/)[ DMARC ](/tags/dmarc/)[ News ](/tags/news/)[ SPF ](/tags/spf/)

[ Vasile Diaconu ](/authors/vasile-diaconu/)
Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
[LinkedIn Profile →](https://www.linkedin.com/in/vasile-diaconu/)
## Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.
[Start Free Trial](https://app.dmarcreport.com/) [Check Your DMARC Record](/tools/dmarc-checker/)
## Related Articles
[ Foundational 4m Africa Fights Cybercrime, Attention Farmers Customers, Apple Prevents Threats Aug 28, 2025 ](/blog/africa-fights-cybercrime-attention-farmers-customers-apple-prevents-threats/)[ Foundational 4m AI Scam Alert, Federal Cuts Vulnerability, American Tire Cyberattack Sep 9, 2025 ](/blog/ai-scam-alert-federal-cuts-vulnerability-american-tire-cyberattack/)[ Foundational 4m Akira flaunts victims, Idaho targets orthodontist, AI granny protects Nov 22, 2024 ](/blog/akira-flaunts-victims-idaho-targets-orthodontist-ai-granny-protects/)[ Foundational 4m Ambient Light Spying, Cybersecurity Prices Drop, Euro 2024 Threats Jul 10, 2024 ](/blog/ambient-light-spying-cybersecurity-prices-drop-euro-2024-threats/)
```json
{"@context":"https://schema.org","@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138898167","name":"DMARC Report","url":"https://dmarcreport.com","logo":{"@type":"ImageObject","url":"https://dmarcreport.com/images/dmarcreport-logo.png"},"description":"DMARC reporting and email authentication management. Monitor aggregate and forensic DMARC reports, analyze authentication results, and enforce DMARC policies across all your domains.","parentOrganization":{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138883901","name":"DuoCircle LLC","url":"https://www.duocircle.com","sameAs":["https://www.wikidata.org/wiki/Q138883901","https://www.crunchbase.com/organization/duocircle-llc","https://www.linkedin.com/company/duocircle","https://github.com/duocircle"],"subOrganization":[{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138898167","name":"DMARC Report","url":"https://dmarcreport.com"},{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138897474","name":"AutoSPF","url":"https://autospf.com"},{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138897912","name":"Phish Protection","url":"https://www.phishprotection.com"}]},"sameAs":["https://www.wikidata.org/wiki/Q138898167","https://www.linkedin.com/company/duocircle","https://x.com/duocirclellc","https://www.g2.com/products/dmarc-report/reviews","https://github.com/duocircle","https://www.crunchbase.com/organization/duocircle-llc","https://www.trustradius.com/products/duocircle/reviews"],"aggregateRating":{"@type":"AggregateRating","ratingValue":"4.8","reviewCount":"470","bestRating":"5","worstRating":"1","url":"https://www.g2.com/products/dmarc-report/reviews"},"contactPoint":{"@type":"ContactPoint","contactType":"customer support","url":"https://dmarcreport.com/support/"},"knowsAbout":["DMARC","DMARC Reporting","DMARC Aggregate Reports","DMARC Forensic Reports","Sender Policy Framework","DKIM","Email Authentication","Email Security","DNS Management","Email Deliverability"]}
```
```json
{"@context":"https://schema.org","@type":"WebSite","name":"DMARC Report","url":"https://dmarcreport.com","description":"DMARC reporting and email authentication management. Monitor aggregate and forensic DMARC reports, analyze authentication results, and enforce DMARC policies across all your domains.","publisher":{"@type":"Organization","name":"DMARC Report","url":"https://dmarcreport.com","logo":{"@type":"ImageObject","url":"https://dmarcreport.com/images/dmarcreport-logo.png"},"description":"DMARC reporting and email authentication management. Monitor aggregate and forensic DMARC reports, analyze authentication results, and enforce DMARC policies across all your domains.","parentOrganization":{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138883901","name":"DuoCircle LLC","url":"https://www.duocircle.com","sameAs":["https://www.wikidata.org/wiki/Q138883901","https://www.crunchbase.com/organization/duocircle-llc","https://www.linkedin.com/company/duocircle","https://github.com/duocircle"],"subOrganization":[{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138898167","name":"DMARC Report","url":"https://dmarcreport.com"},{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138897474","name":"AutoSPF","url":"https://autospf.com"},{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138897912","name":"Phish Protection","url":"https://www.phishprotection.com"}]}}}
```
```json
[{"@context":"https://schema.org","@type":"BlogPosting","headline":"Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing","description":"Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing from DMARC Report explains practical steps for email authentication, domain protection.","url":"https://dmarcreport.com/blog/adidas-data-breach-whatsapp-image-threat-silent-ransom-vishing/","datePublished":"2025-05-29T08:13:24.000Z","dateModified":"2026-04-16T15:53:43.000Z","dateCreated":"2025-05-29T08:13:24.000Z","author":{"@type":"Person","@id":"https://dmarcreport.com/authors/vasile-diaconu/#person","name":"Vasile Diaconu","url":"https://dmarcreport.com/authors/vasile-diaconu/","jobTitle":"Operations Lead","description":"Vasile Diaconu is the Operations Lead at DuoCircle, the company behind DMARC Report and AutoSPF. He coordinates between engineering, product, and technical support - running project management, interfacing with developers on customer-reported issues, and making sure work that comes in through the support channel actually gets closed out. Vasile sits at the intersection of customer feedback and engineering execution, giving him a direct view of which email authentication problems customers hit most often in production.","image":"https://media.mailhop.org/dmarcreport/images/team/vasile-diaconu.jpg","knowsAbout":["SaaS Operations","Technical Support Coordination","Customer Issue Resolution","Engineering Program Management","Deployment Operations"],"worksFor":{"@type":"Organization","name":"DMARC Report","url":"https://dmarcreport.com"},"sameAs":["https://www.linkedin.com/in/vasile-diaconu/"]},"publisher":{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138898167","name":"DMARC Report","url":"https://dmarcreport.com","logo":{"@type":"ImageObject","url":"https://dmarcreport.com/images/dmarcreport-logo.png"},"description":"DMARC reporting and email authentication management. Monitor aggregate and forensic DMARC reports, analyze authentication results, and enforce DMARC policies across all your domains.","parentOrganization":{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138883901","name":"DuoCircle LLC","url":"https://www.duocircle.com","sameAs":["https://www.wikidata.org/wiki/Q138883901","https://www.crunchbase.com/organization/duocircle-llc","https://www.linkedin.com/company/duocircle","https://github.com/duocircle"],"subOrganization":[{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138898167","name":"DMARC Report","url":"https://dmarcreport.com"},{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138897474","name":"AutoSPF","url":"https://autospf.com"},{"@type":"Organization","@id":"https://www.wikidata.org/wiki/Q138897912","name":"Phish Protection","url":"https://www.phishprotection.com"}]},"sameAs":["https://www.wikidata.org/wiki/Q138898167","https://www.linkedin.com/company/duocircle","https://x.com/duocirclellc","https://www.g2.com/products/dmarc-report/reviews","https://github.com/duocircle","https://www.crunchbase.com/organization/duocircle-llc","https://www.trustradius.com/products/duocircle/reviews"],"aggregateRating":{"@type":"AggregateRating","ratingValue":"4.8","reviewCount":"470","bestRating":"5","worstRating":"1","url":"https://www.g2.com/products/dmarc-report/reviews"},"contactPoint":{"@type":"ContactPoint","contactType":"customer support","url":"https://dmarcreport.com/support/"},"knowsAbout":["DMARC","DMARC Reporting","DMARC Aggregate Reports","DMARC Forensic Reports","Sender Policy Framework","DKIM","Email Authentication","Email Security","DNS Management","Email Deliverability"]},"mainEntityOfPage":{"@type":"WebPage","@id":"https://dmarcreport.com/blog/adidas-data-breach-whatsapp-image-threat-silent-ransom-vishing/"},"articleSection":"foundational","keywords":"dkim, DMARC, News, SPF","wordCount":1124,"image":{"@type":"ImageObject","url":"https://media.mailhop.org/dmarcreport/images/2022/04/dmarc-alignment-6379.jpg","caption":"Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing","width":900,"height":600},"speakable":{"@type":"SpeakableSpecification","cssSelector":[".answer-block","h1"]}}]
```
```json
{"@context":"https://schema.org","@type":"BreadcrumbList","itemListElement":[{"@type":"ListItem","position":1,"name":"Home","item":"https://dmarcreport.com/"},{"@type":"ListItem","position":2,"name":"Blog","item":"https://dmarcreport.com/blog/"},{"@type":"ListItem","position":3,"name":"Foundational","item":"https://dmarcreport.com/foundational/"},{"@type":"ListItem","position":4,"name":"Adidas Data Breach, Whatsapp Image Threat, Silent Ransom Vishing","item":"https://dmarcreport.com/blog/adidas-data-breach-whatsapp-image-threat-silent-ransom-vishing/"}]}
```