Device Code Phishing, iOS 18 Relief, Global Fraud Disrupted

Quick Answer
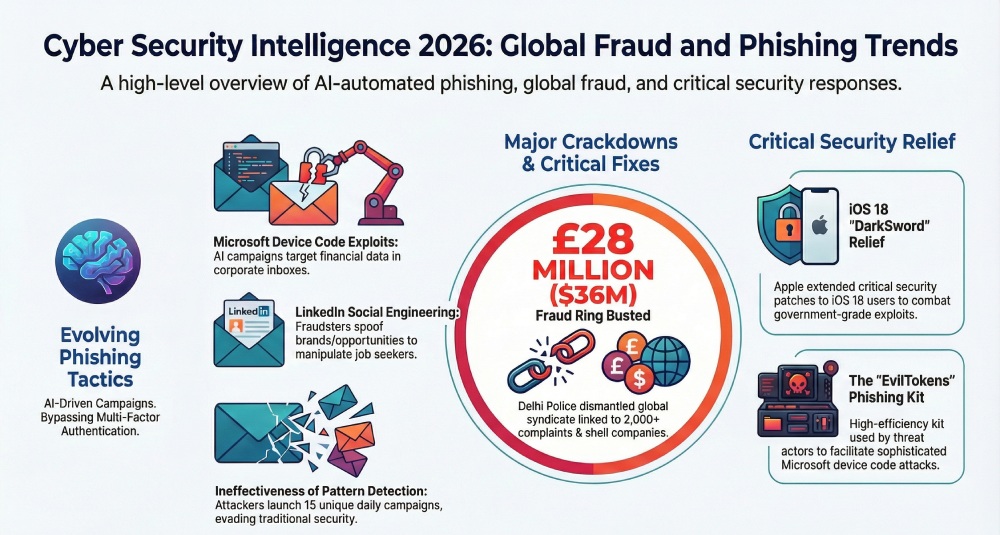
Microsoft device code phishing campaigns are launching 10 to 15 unique attacks daily, targeting hundreds of organizations across global sectors since March 2026. Simultaneously, Apple patched the DarkSword vulnerability for iOS 18 users, and Indian authorities disrupted a $36 million global cyber fraud syndicate operating through fake investment platforms.
Related: Free DMARC Checker

Recent cybersecurity incidents highlight escalating threats across multiple attack vectors. Microsoft device code phishing campaigns are targeting hundreds of organizations daily, Apple has extended critical DarkSword security patches to iOS 18 users, Indian authorities dismantled a $36 million global fraud ring, and a new LinkedIn phishing campaign is exploiting job seekers. According to Verizon’s 2024 DBIR, phishing remains involved in over 36% of confirmed data breaches, underscoring why email authentication protocols like DMARC are essential for every organization.
How Are Microsoft Device Code Phishing Attacks Exploiting Organizations?
A new phishing campaign involving Microsoft device codes and AI automation is successfully breaking into corporate email inboxes. Tanmay Ganacharya, VP of Security Research at Microsoft, confirmed that approximately 10 to 15 unique campaigns launch daily, a pattern sustained since March 15, 2026. Threat actors are leveraging each campaign to target hundreds of organizations across different global sectors and niches.

The finance sector is the hardest hit by these attacks. Because each campaign varies in its approach, pattern-based detection is proving inefficient at identifying and blocking the threats. While no specific threat group has been attributed, the tactics and patterns closely resemble EvilTokens, a high-efficiency Microsoft device code phishing kit that gained popularity in mid-February 2026. EvilTokens is specifically designed to bypass Multi-Factor Authentication (MFA) systems, making it particularly dangerous.
Microsoft recommends blocking device code flow wherever possible. Organizations should also conduct regular employee training to help staff recognize phishing techniques. Protocols like DMARC (Domain-based Message Authentication, Reporting, and Conformance) help authenticate emails and prevent spoofing, providing an additional layer of defense against phishing campaigns that impersonate trusted senders.
Why Did Apple Patch iOS 18 for the DarkSword Vulnerability?
For users who are unable or unwilling to update their iPhones to iOS 26, Apple delivered significant relief by patching the DarkSword vulnerability for iOS 18 users. This marks an unusual move: previously, Apple did not offer security patches to users who had not upgraded to the latest iOS version. The decision reflects the severity of the DarkSword exploit.

A similar precedent occurred in 2025 when security researchers discovered Coruna, a government-grade exploit kit. Apple patched all 23 associated vulnerabilities for iOS versions 13 through 17.2.1. This time, with DarkSword, Apple again extended the security fix to every iOS 18 user, signaling the threat’s gravity. Cybersecurity experts emphasize that if Apple is treating DarkSword with this level of urgency, users should understand the situation’s severity and remain vigilant about updating their devices promptly.
How Was the $36 Million Global Cyber Fraud Syndicate Disrupted?
Delhi Police dismantled a major global cyber fraud ring responsible for scams worth $36 million, with over 2,000 complaints filed against the syndicate. Authorities arrested the mastermind, Karan Kajaria, along with 10 other members of the highly organized network that operated across multiple Indian states with direct connections to international cyber fraud operations.
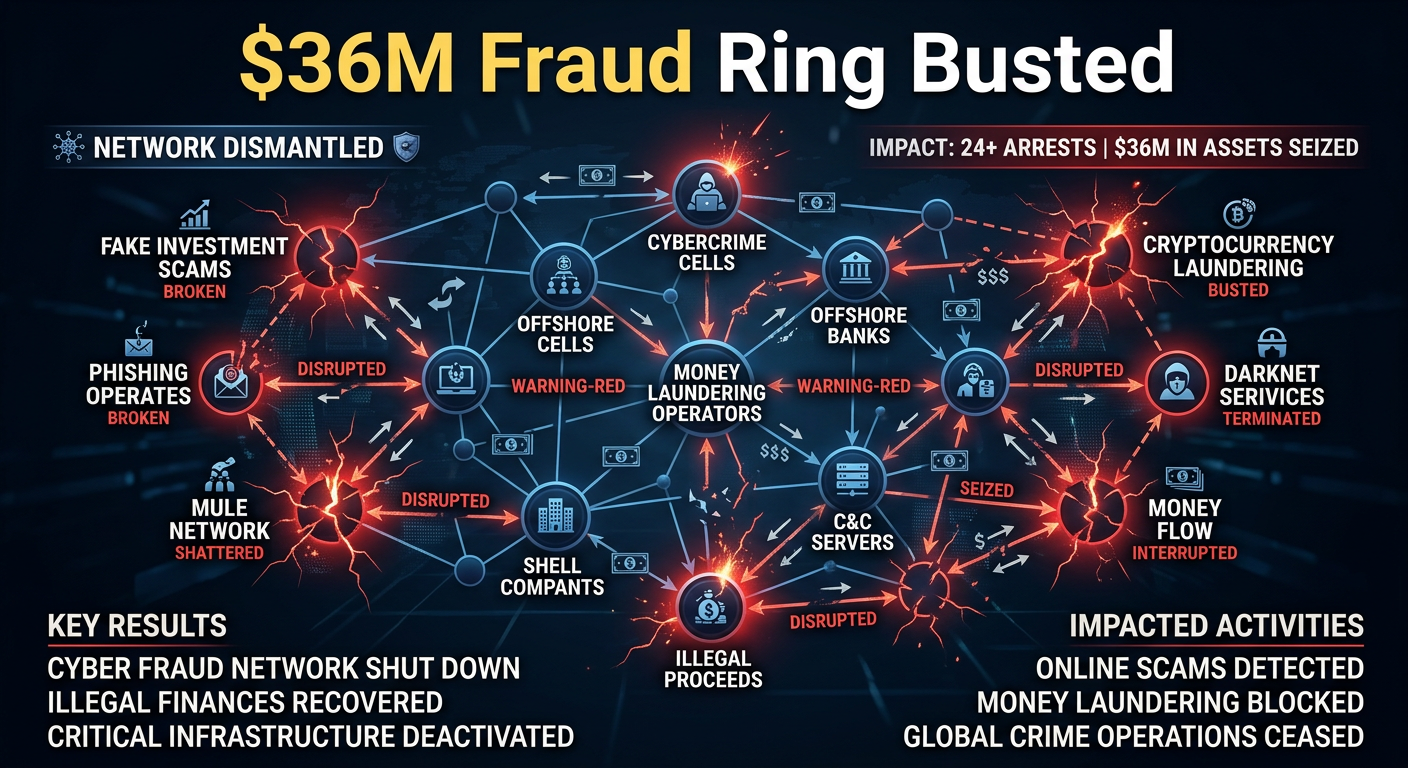
The syndicate created fake investment and messaging platforms to lure victims. They deployed malicious applications to capture one-time passwords (OTPs) and sensitive banking data from targets. To conceal money trails, the group routed stolen funds through an intricate web of mule bank accounts and shell companies. This case illustrates how sophisticated cybercriminal networks have become, reinforcing the need for robust authentication protocols at every level.
How Are Threat Actors Exploiting LinkedIn for Phishing Attacks?
LinkedIn is increasingly becoming a popular hunting ground for phishing attacks. A new campaign targets users through LinkedIn notification emails, often disguised as job opportunities. Threat actors exploit the desperation and curiosity of job seekers, using emotional triggers to bypass caution and drive clicks on malicious links. According to Google’s 2024 bulk sender requirements, domains sending over 5,000 messages per day must implement DMARC, SPF (Sender Policy Framework), and DKIM (DomainKeys Identified Mail) to prevent exactly this type of impersonation.
These phishing messages impersonate reputable companies and influential decision-makers, carrying the correct logos, branding assets, and formatting to appear credible. Cybersecurity experts advise LinkedIn users to verify sender authenticity before clicking any link and to be wary of unexpected notifications. Automated threat detection and human intelligence must work together to identify and neutralize these threats in real time.
Organizations should deploy email authentication protocols --- DMARC, DKIM, and SPF --- to authenticate outbound emails, prevent domain spoofing, and protect their brand from phishing attacks. An upgraded antivirus solution and a strong firewall provide additional defense against social media-based phishing. Regularly checking your DMARC configuration ensures your domain stays protected as threats evolve.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.