DMARC Compliance Mandates: How Government and Industry Regulations Are Making Email Authentication Mandatory

Quick Answer
Two years ago, DMARC was a best practice. Today, it is increasingly a compliance requirement. The shift happened fast: in February 2024, Google and Yahoo began requiring DMARC for bulk email senders. By November 2025, Gmail escalated to actively rejecting non-compliant emails. Microsoft followed suit. PCI DSS made email authentication mandatory for the payments industry.
Related: Free DMARC Checker

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →Two years ago, DMARC was a best practice. Today, it is increasingly a compliance requirement. The shift happened fast: in February 2024, Google and Yahoo began requiring DMARC for bulk email senders. By November 2025, Gmail escalated to actively rejecting non-compliant emails. Microsoft followed suit. PCI DSS made email authentication mandatory for the payments industry. The EU’s NIS2 Directive and DORA regulation positioned DMARC as integral to operational resilience.
The UK’s NCSC retired its centralized monitoring tools, pushing DMARC responsibility directly onto organizations. And behind all of it, the U.S. government’s 2017 Binding Operational Directive 18-01 remains the template that proved government mandates work.
This post maps every major DMARC-related compliance mandate currently in effect or emerging, organized by jurisdiction and industry, so that IT leaders, compliance teams, and business owners can assess their exposure and build an enforcement timeline. Every mandate cited is linked to its original source document.
DMARC is no longer optional. It is a regulatory requirement across government, financial services, healthcare, and any organization that sends bulk email. The question is not whether your organization needs DMARC, it is whether you are compliant with the mandates that already apply to you.
United States: The Federal Mandate That Started It All
DHS Binding Operational Directive 18-01 (October 2017)
The foundational government DMARC mandate. Issued by the Department of Homeland Security (now CISA), BOD 18-01 required all federal civilian executive branch agencies to: publish a DMARC record with p=none within 90 days, set the DMARC policy to p=reject for all second-level domains within one year, deploy STARTTLS on all internet-facing mail servers, and deploy valid SPF records.
A Government Accountability Office audit (GAO-20-133) confirmed that the directive produced measurable improvements across federal cybersecurity. The Federal Housing Finance Agency OIG audit documented how individual agencies navigated compliance, including challenges with third-party vendors managing internet-facing systems.
What This Means for You
If you are a federal contractor, partner, or vendor that exchanges email with federal agencies, your domain is being evaluated against the same standards. Federal agencies enforce DMARC on inbound email, meaning your messages may be quarantined or rejected if your domain lacks proper authentication. BOD 18-01 also set the precedent that other governments worldwide have followed.
United Kingdom: From NCSC Guidance to Mandatory Enforcement
The UK government has taken a multi-layered approach to DMARC, combining policy mandates with free tooling and active change management.
Minimum Cyber Security Standard & NCSC Mail Check
The UK’s Minimum Cyber Security Standard requires all central government departments to have DMARC at p=quarantine or p=reject, SPF, DKIM, and TLS for all email services. The Government Digital Service provides detailed implementation guidance covering DNS record configuration.
The NCSC’s Active Cyber Defence 6th Year Report documented the landmark achievement: 100% of UK central government departments reached strict DMARC enforcement by 2022. In a single 30-day period, over 80 million spoofed emails were blocked from these domains. The NCSC also ran a targeted campaign helping 90 local councils progress from p=none to enforcing policies.
NCSC Mail Check Retirement (March 2026)
In a significant shift, the NCSC announced the retirement of its centralized Mail Check and Web Check services by March 31, 2026. This means organizations that previously relied on NCSC’s free monitoring must now implement their own DMARC reporting and monitoring infrastructure (PowerDMARC UK Report 2026). PowerDMARC’s analysis of 875 UK domains found that 12.2% of government domains still lack any DMARC record, and 42.9% have not yet reached p=reject, creating an urgent compliance gap just as the safety net disappears.
European Union: NIS2 and DORA, Email Security as Operational Resilience
NIS2 Directive (Directive (EU) 2022/2555)
The NIS2 Directive, which entered into force in January 2023 with a transposition deadline of October 17, 2024, significantly expands the scope of EU cybersecurity requirements. It applies to essential and important entities across energy, transport, banking, health, digital infrastructure, and ICT service management. Article 21 requires “appropriate and proportionate technical, operational and organisational measures to manage the risks posed to the security of network and information systems.”
The European Parliament’s briefing on NIS2 outlines how the directive introduces more stringent supervisory measures and harmonised sanctions. ENISA’s Technical Implementation Guidance provides detailed requirements for each of the 13 titles in the implementing regulation. While NIS2 does not name DMARC explicitly, its requirements for network security, access control, encryption, and incident reporting make email authentication a practical necessity for compliance. As one analysis notes, DMARC is positioned as essential for its ability to report on and block email impersonation, a core NIS2 concern.
DORA (Digital Operational Resilience Act)
DORA, which applies to the EU financial sector from January 2025, establishes requirements for ICT risk management, incident reporting, and testing. Email-based attacks, particularly BEC, are among the most common ICT incidents in financial services. DORA’s emphasis on operational resilience and incident prevention makes DMARC enforcement a practical requirement for financial institutions operating in the EU, even though the regulation does not prescribe specific technical protocols.
Australia: ASD Essential Eight and Information Security Manual
The Australian Signals Directorate’s Strategies to Mitigate Cyber Security Incidents explicitly includes “Block spoofed emails” as a mitigation strategy, advising organizations to “Use ‘hard fail’ SPF TXT and DMARC DNS records to mitigate emails that spoof the organisation’s domain.”
The Essential Eight Maturity Model provides a tiered framework for implementing the ASD’s top mitigation strategies, including email spoofing controls. A Western Australian government audit found that none of the 10 audited entities had achieved Maturity Level One across all eight controls, highlighting the gap between policy and implementation.
Mailbox Provider Requirements: The Industry Mandates That Changed Everything
While government mandates affect public-sector organizations, the mailbox provider requirements affect everyone who sends email. These are the mandates with the broadest impact.
Google Gmail (February 2024, November 2025)
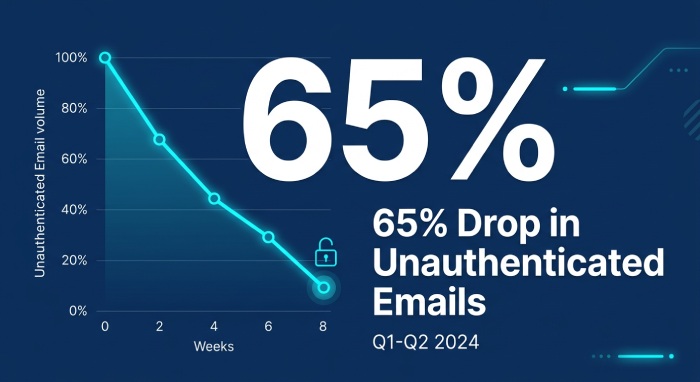
Google’s Email Sender Guidelines introduced requirements in February 2024 for anyone sending more than 5,000 emails per day to Gmail accounts. Bulk senders must implement SPF, DKIM, and DMARC (at minimum p=none), enable one-click unsubscribe, and maintain spam complaint rates below 0.3%. In November 2025, Gmail escalated to actively rejecting non-compliant emails at the SMTP level, ending the grace period of soft enforcement. The impact has been dramatic: Google reported a 65% reduction in unauthenticated messages reaching Gmail inboxes and 265 billion fewer unauthenticated messages sent in 2024 (Google/Valimail).
Microsoft Outlook (May 2025)
Microsoft announced that Outlook.com, Hotmail.com, and Live.com would begin rejecting emails from non-compliant bulk senders as of May 5, 2025. Requirements mirror Google’s: SPF, DKIM, DMARC alignment, and TLS encryption (dmarcreport.com Implementation Guide).
Yahoo and Apple (February 2024)
Yahoo and Apple announced similar authentication requirements alongside Google in February 2024. Together, Gmail, Yahoo, Microsoft, and Apple collectively serve approximately 90% of consumer and business email users globally. The convergence across all four major providers creates a unified set of requirements that effectively makes DMARC mandatory for any organization that sends commercial email at scale.
Gmail, Yahoo, Microsoft, and Apple now collectively enforce email authentication requirements for bulk senders. If you send more than 5,000 emails per day and do not have SPF, DKIM, and DMARC in place, your messages are being rejected, not filtered to spam, but rejected outright.

PCI DSS v4.0.1: DMARC for the Payments Industry
The Payment Card Industry Data Security Standard version 4.0.1 introduced Requirement 5.4.1, which mandates anti-phishing mechanisms for organizations that process, store, or transmit cardholder data. While the requirement does not name DMARC explicitly, industry guidance from the PCI Security Standards Council’s own Phishing Resource Guide identifies SPF, DKIM, and DMARC as the primary technical controls for email authentication.
These requirements became mandatory on March 31, 2025, having been “best practice until that date” in the original v4.0 release (PCI DSS v4.0 New Requirements Summary). As Proofpoint’s analysis notes, “auditors could fail companies that have not implemented DMARC” under this requirement (Proofpoint DMARC E-Book).
What This Means for You
If your organization accepts credit cards, whether you are a retailer, SaaS provider, healthcare system, or nonprofit, PCI DSS v4.0.1 applies. Anti-phishing controls including email authentication are now auditable requirements, not optional best practices. Failing a PCI audit carries financial penalties, increased transaction fees, and potential loss of the ability to process card payments.
Additional Mandates and Standards
NIST Technical Guidance (United States)
The National Institute of Standards and Technology published NIST Technical Note 1945, which provides a detailed technical analysis of DMARC, SPF, and DKIM email authentication mechanisms. While not a mandate, NIST guidance is referenced extensively in federal procurement and compliance frameworks, making it a de facto standard for organizations working with the U.S. government.
FTC Staff Perspective (United States)
The Federal Trade Commission published a staff perspective on email authentication analyzing DMARC adoption across major commercial domains. The FTC found that only about 20% of financial services domains used the strictest p=reject setting, and explicitly recommended that businesses implement DMARC to protect their brands from phishing.
Japan’s Unified Security Standards
Japan set a July 2024 target date for all government agencies to implement DMARC, adding another major economy to the list of nations with explicit government DMARC mandates.
FinCEN Advisory on BEC (United States)
The Financial Crimes Enforcement Network’s Advisory FIN-2019-A005 instructs financial institutions to file Suspicious Activity Reports for BEC-related transactions and outlines red flags for detecting email compromise fraud. While not a DMARC mandate per se, the advisory positions email authentication as a critical control for financial institutions’ anti-money laundering compliance.
The Complete Compliance Timeline
The following table consolidates every major DMARC-related mandate and requirement currently in effect or emerging, organized chronologically:
| Date | Mandate / Requirement | Jurisdiction / Scope | DMARC Requirement |
|---|---|---|---|
| Oct 2017 | DHS BOD 18-01 | U.S. Federal Civilian Agencies | DMARC at p=reject for all domains within 1 year |
| Jan 2023 | NIS2 Directive enters force | EU Essential & Important Entities | Email security measures required under Art. 21; DMARC is practical necessity |
| Feb 2024 | Google & Yahoo Sender Rules | Global: Bulk senders (5,000+/day) | DMARC record required (min. p=none); SPF + DKIM mandatory |
| Jul 2024 | Japan Unified Security Stds | Japanese Government Agencies | DMARC implementation target date |
| Oct 2024 | NIS2 transposition deadline | EU Member States | National laws must be in place implementing NIS2 requirements |
| Jan 2025 | DORA enforcement begins | EU Financial Sector | ICT risk management incl. email-based threat prevention |
| Mar 2025 | PCI DSS v4.0.1 enforcement | Global: Card payment processors | Anti-phishing mechanisms (incl. DMARC) now auditable |
| May 2025 | Microsoft Sender Rules | Global: Bulk senders to Outlook | SPF, DKIM, DMARC required; non-compliant mail rejected |
| Nov 2025 | Gmail Full Enforcement | Global: Bulk senders to Gmail | Non-compliant emails actively rejected at SMTP level |
| Mar 2026 | NCSC Mail Check Retirement | UK Public Sector | Organizations must self-manage DMARC monitoring |
| Ongoing | UK Min. Cyber Security Std | UK Central Government | DMARC at p=quarantine or p=reject required |
| Ongoing | ASD Essential Eight | Australian Government | SPF hard fail + DMARC DNS records to block spoofed email |
Sources: Original directive/regulation documents as cited throughout this article.
What to Do: A Compliance Action Plan
Step 1: Identify Which Mandates Apply to You
Audit your regulatory exposure. Do you process card payments (PCI DSS)? Send bulk email (Google/Yahoo/Microsoft)? Operate in the EU (NIS2/DORA)? Work with the U.S. federal government (BOD 18-01)? Operate in the UK public sector (Minimum Cyber Security Standard)? Most organizations are subject to at least two of these mandates simultaneously.
Step 2: Assess Your Current DMARC Status
Check your DMARC record using a free lookup tool at dmarcreport.com. If you have no DMARC record, you are non-compliant with virtually every mandate listed above. If you are at p=none, you meet the minimum for Google/Yahoo but are non-compliant with BOD 18-01, the UK standard, and likely PCI DSS v4.0.1 auditors’ expectations.
Step 3: Implement Reporting Immediately
Add an RUA tag to your DMARC record to begin receiving aggregate reports. This is the foundational data you need to identify all legitimate senders and progress toward enforcement. A platform like DMARC Report translates raw XML reports into actionable dashboards, drastically reducing the time and expertise required to reach compliance.
Step 4: Progress to Enforcement on a Documented Timeline
Create a written compliance timeline that maps your DMARC progression (p=none → p=quarantine → p=reject) against the mandates that apply to you. Regulators and auditors increasingly expect not just a published record, but documented evidence of policy progression and monitoring. This is especially important for PCI DSS assessments, where the auditor may ask for evidence of anti-phishing controls including DMARC enforcement.
Step 5: Maintain Ongoing Monitoring
DMARC is not a one-time deployment. New email-sending services, vendor changes, and infrastructure updates can break alignment and create authentication failures. Continuous monitoring through aggregate reports is a requirement under multiple frameworks, and it is the only way to ensure your enforcement remains effective over time. The UK NCSC’s retirement of Mail Check makes this self-monitoring capability particularly urgent for UK organizations.
The Bottom Line
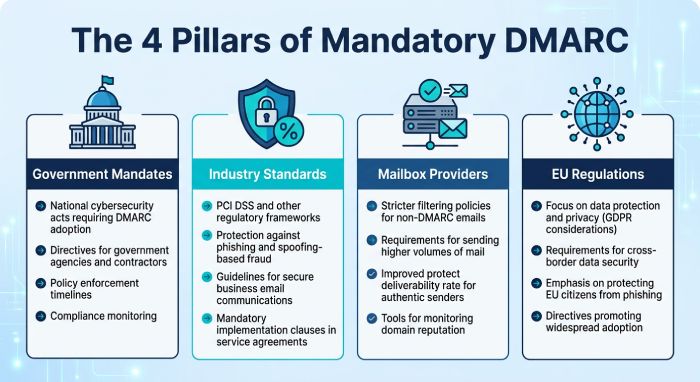
The regulatory landscape for email authentication has transformed in under three years. What was a voluntary best practice in 2023 is now a compliance requirement across multiple jurisdictions and industries:
Government mandates in the U.S. (BOD 18-01), UK (Minimum Cyber Security Standard), Australia (Essential Eight), and Japan require DMARC enforcement for public-sector domains, and increasingly expect it from private-sector partners.
Industry standards including PCI DSS v4.0.1 make anti-phishing controls auditable for any organization that processes payments. EU DORA extends similar expectations to the financial sector.
Mailbox provider requirements from Google, Yahoo, Microsoft, and Apple collectively enforce authentication standards for approximately 90% of the world’s email users. Non-compliant bulk senders are rejected outright.
EU-wide cybersecurity regulation through NIS2 requires proportionate measures to manage network and information system risks, making email authentication a practical necessity across 27 member states.
DMARC enforcement is no longer a security nice-to-have. It is a multi-jurisdictional compliance requirement. The organizations that treat it as such, and invest in proper implementation, monitoring, and ongoing management, will avoid regulatory penalties, protect their deliverability, and demonstrably reduce their exposure to the most financially damaging form of cybercrime.

Sources & References
All mandates and regulations cited are linked to their original source documents. Government directives, EU legislation, and industry standards are cited from official government and institutional sources.
1. DHS Binding Operational Directive 18-01, U.S. government directive requiring federal civilian agencies to implement DMARC at p=reject.
URL: https://cyber.dhs.gov/assets/report/bod-18-01.pdf
2. GAO Report GAO-20-133, Government Accountability Office audit confirming DHS directives strengthened federal cybersecurity.
URL: https://www.gao.gov/assets/gao-20-133.pdf
3. FHFA OIG Audit AUD-2022-010, Federal Housing Finance Agency compliance review documenting BOD 18-01 implementation challenges.
URL: https://www.fhfaoig.gov/sites/default/files/AUD-2022-010.pdf
4. UK Government, Securing Government Email, UK Minimum Cyber Security Standard implementation guidance for DMARC, SPF, DKIM, TLS.
5. UK Government, Set Up Government Email Services Securely, Technical implementation guide for UK government DMARC deployment.
6. UK NCSC Active Cyber Defence 6th Year Report, Source for 100% central government DMARC enforcement and 80 million blocked spoofed emails.
URL: https://www.ncsc.gov.uk/files/acd6-summary.pdf
7. PowerDMARC UK DMARC & MTA-STS Adoption Report 2026, Analysis of 875 UK domains; source for NCSC Mail Check retirement impact and sector-level data.
URL: https://powerdmarc.com/uk-dmarc-mta-sts-adoption-report/
8. NIS2 Directive, Directive (EU) 2022/2555, Full text of the EU’s Network and Information Security Directive (NIS2).
URL: https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32022L2555
9. European Parliament Briefing on NIS2, Legislative analysis of NIS2 scope, requirements, and implementation timeline.
URL: https://www.europarl.europa.eu/RegData/etudes/BRIE/2021/689333/EPRS_BRI(2021)689333_EN.pdf
10. ENISA Technical Implementation Guidance for NIS2, Detailed guidance on implementing cybersecurity risk management measures under NIS2.
11. Australian ASD, Strategies to Mitigate Cyber Security Incidents, Source for “Block spoofed emails” mitigation strategy including DMARC DNS records.
12. Australian ASD, Essential Eight Maturity Model, Tiered maturity framework for implementing Essential Eight controls including email spoofing prevention.
13. Western Australia, Essential Eight Implementation Audit, Government audit finding none of 10 entities achieved Maturity Level One across all controls.
14. Google, Email Sender Guidelines FAQ, Official documentation for Gmail bulk sender requirements and November 2025 enforcement escalation.
URL: https://support.google.com/a/answer/14229414?hl=en
15. Google/Valimail, Gmail Authentication Impact Data, Source for 65% unauthenticated message reduction and 265 billion fewer unauthenticated messages in 2024.
URL: https://www.valimail.com/blog/google-stats-dmarc/
16. dmarcreport.com, SPF/DKIM/DMARC Implementation Guide, Source for Microsoft May 2025 enforcement date and bulk sender compliance requirements.
17. PCI DSS v4.0 New Requirements Summary (BDO), Summary of new requirements including Requirement 5.4.1 anti-phishing mechanisms.
18. PCI SSC Phishing Resource Guide, PCI Security Standards Council guide identifying DMARC as an anti-phishing control.
URL: https://www.pcisecuritystandards.org/documents/PCI_SSC_Phishing_Resource_Guide_v05.pdf
19. Proofpoint, DMARC: The Key to Email Deliverability, Industry analysis of PCI DSS 4.0 DMARC implications and mailbox provider requirements.
20. NIST Technical Note 1945, Email Authentication Mechanisms, NIST technical analysis of DMARC, SPF, and DKIM protocols.
URL: https://nvlpubs.nist.gov/nistpubs/TechnicalNotes/NIST.TN.1945.pdf
21. FTC Staff Perspective, Email Authentication, FTC analysis of DMARC adoption across commercial domains with enforcement recommendations.
22. FinCEN Advisory FIN-2019-A005, U.S. Treasury advisory on BEC email compromise fraud schemes for financial institutions.
URL: https://www.fincen.gov/system/files/advisory/2019-07-16/Updated%20BEC%20Advisory%20FINAL%20508.pdf
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.