The DMARC Readiness Gap in Healthcare: Why the Most Targeted SectorIs the Least Protected

Quick Answer
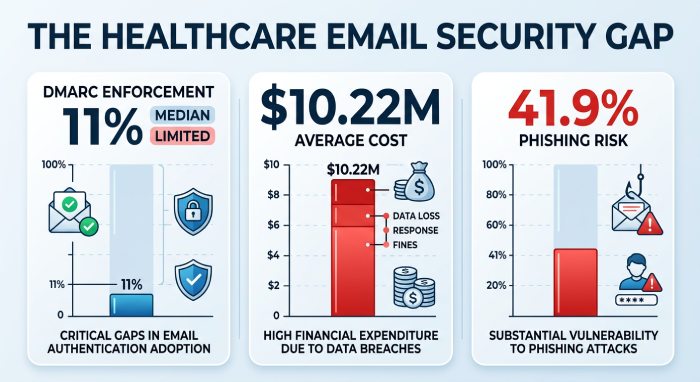
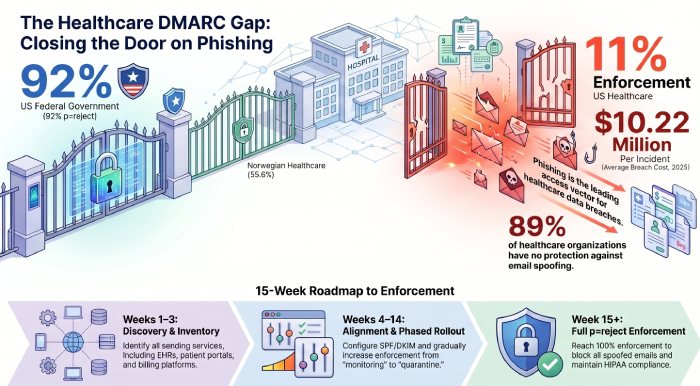
There is a statistic buried in Valimail’s industry-level DMARC analysis that should alarm every healthcare executive, every CISO, and every compliance officer in the sector: US healthcare sits at just 11% DMARC enforcement. That means 89% of healthcare organizations have either no DMARC record at all, or have published one at p=none, the monitoring-only policy that provides zero protection against email spoofing.
Related: Free DMARC Checker

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →11% Protected. 289 Million Records Breached. The Numbers Do Not Lie.
There is a statistic buried in Valimail’s industry-level DMARC analysis that should alarm every healthcare executive, every CISO, and every compliance officer in the sector: US healthcare sits at just 11% DMARC enforcement. That means 89% of healthcare organizations have either no DMARC record at all, or have published one at p=none, the monitoring-only policy that provides zero protection against email spoofing.
Now put that number next to these: In 2024, 289,162,330 individuals had their protected health information exposed or impermissibly disclosed in healthcare data breaches reported to the HHS Office for Civil Rights. Healthcare breaches cost an average of $10.22 million per incident in 2025, the highest of any industry. And 79% of healthcare providers were targeted by emails involving hacking incidents and unauthorized access in 2024.
Healthcare is simultaneously the most attacked sector and the least protected by the very authentication standard designed to prevent the attacks. This report examines why, what it is costing the industry, and what it takes to fix it.
The Healthcare Phishing Crisis: A Sector Under Siege
Email is the front door for healthcare cyberattacks. CISA’s dedicated healthcare DMARC guidance, one of only a handful of sector-specific DMARC documents the agency has ever published, states directly: “Phishing and spearphishing are among the top attack vectors for healthcare organizations, which can lead to patient care impact, financial fraud, or protected health information (PHI) breaches and HIPAA fines.”
KnowBe4’s research found that healthcare is more susceptible to phishing than any other major industry, with 41.9% of organizations vulnerable, compared to 39.2% for insurance and 36.5% for retail. DMARCian’s analysis of healthcare phishing cites research showing that one in seven phishing emails sent to healthcare employees are opened, a dramatically higher engagement rate than in other sectors.
The consequences are catastrophic. The HIPAA Journal’s 2025 Healthcare Data Breach Report shows that more than 700 large healthcare data breaches have been reported to OCR each year for three consecutive years, plateauing at roughly two large breaches per day. In 2024, the Change Healthcare ransomware attack alone affected an estimated 192.7 million individuals, accounting for 66.7% of all healthcare records breached that year. 57 million individuals were affected by healthcare data breaches in 2025.
And phishing is not just an entry point, it is the entry point. As of September 2025, phishing represents the most common access vector for healthcare data breaches, accounting for 16% of all breaches. 96 email fraud attempts per quarter target the average healthcare organization. The Numotion breach in March 2025, affecting 529,004 individuals, was caused by employees responding to phishing emails, compromising multiple email accounts over a two-month period. DMARC enforcement on the spoofed sending domains would have prevented the initial phishing emails from reaching those employees.
The paradox: Healthcare is the most phished sector, the most costly to breach, and the most critical to protect. Yet it has one of the lowest DMARC enforcement rates of any major industry. This is not a technology gap. It is a priority gap.
The Healthcare DMARC Gap: How Bad Is It?
Multiple independent datasets confirm that healthcare’s DMARC posture is among the weakest of any sector.
| Metric | Finding | Source |
|---|---|---|
| US healthcare DMARC enforcement rate | 11% at p=reject | Valimail (via AutoSPF) |
| Healthcare DMARC adoption (any policy) | ~60% have published a record; only 1 in 5 at p=reject | EasyDMARC/Dark Reading |
| Healthcare DMARC status (Valimail) | Just over one-third at even p=none (the bare minimum) | Valimail 2025/2026 |
| Norwegian healthcare enforcement | 55.6% at p=reject (5x the US rate) | PowerDMARC Norway 2025 |
| Italian healthcare enforcement | 12.8% at p=reject; 1 in 4 domains lack DMARC entirely | PowerDMARC Italy 2025 |
| US federal government enforcement | 92% (for comparison) | Valimail |
| Banking DMARC gaps | 41% of banking institutions lack DMARC | PowerDMARC |
The contrast with Norway is particularly instructive. PowerDMARC’s Norway 2025 report found Norwegian healthcare leading all sectors in p=reject adoption at 55.6%. Why is Norwegian healthcare five times more protected than US healthcare? The answer is regulatory pressure: GDPR, NIS2, and direct regulator requirements on healthcare specifically, not just payment processors. Where regulators explicitly demand email authentication, healthcare organizations deliver it.
Why Healthcare Struggles with DMARC: The Unique Challenges
1. Complex, Fragmented Email Ecosystems
Healthcare organizations are among the most complex email environments in any industry. A typical hospital system sends email from its corporate platform, its electronic health records (EHR) system, its patient portal, its lab results notification system, its appointment scheduling system, its billing platform, its pharmacy notifications, its HR and recruitment systems, and dozens of specialized clinical applications. Each one is a potential third-party sender that needs SPF and DKIM alignment. The sheer number of sending services makes DMARC enforcement significantly harder than in simpler industries.
2. Legacy Systems and Underfunded IT
Healthcare allocates less than 6% of IT budgets to security, far below the industry average. The average cyber maturity score for healthcare is just 54%. Many healthcare organizations still rely on legacy email infrastructure that predates modern authentication standards. These systems often cannot support DKIM signing or custom Return-Path configuration, creating alignment failures that block the path to DMARC enforcement.
3. Vendor and Third-Party Dependencies
94% of healthcare organizations report vendor access to internal systems, with 72% granting high-level permissions. Many of these vendors send email on behalf of the healthcare organization. HIPAA Journal data shows that 30% of healthcare data breaches in 2024 occurred at business associates, third-party vendors. These same vendors are often the ones sending unauthenticated email from healthcare domains, creating DMARC failures that the healthcare organization cannot fix without vendor cooperation.
4. No Explicit DMARC Mandate (Yet)
Unlike the US federal government (BOD 18-01 mandating p=reject), PCI DSS (mandating anti-phishing controls), or Google/Yahoo (mandating DMARC for bulk senders), there is no explicit regulatory requirement forcing healthcare organizations to implement DMARC at enforcement. CISA has published healthcare-specific DMARC guidance, but it is advisory, not mandatory. HIPAA requires “safeguards to protect against unauthorized access to ePHI” but does not name DMARC specifically. This regulatory ambiguity allows healthcare organizations to deprioritize DMARC in favor of other compliance requirements.
5. Fear of Disrupting Patient Communications
Healthcare organizations are acutely aware that blocking a legitimate email could mean a missed lab result, a delayed appointment notification, or a lost prescription alert. CISA’s healthcare guidance acknowledges this concern directly, recommending a staged approach with feedback loops between IT departments and staff. But this caution often becomes permanent paralysis, with organizations staying at p=none indefinitely because they are afraid of what enforcement might break.
The root cause: Healthcare’s DMARC gap is not caused by a single factor. It is the intersection of ecosystem complexity, underfunded security, vendor dependencies, regulatory ambiguity, and operational caution. A DMARC report analyzer addresses every one of these barriers by providing automated sender discovery, guided remediation, phased enforcement, and the confidence to move forward safely.
The Cost of Inaction: What Healthcare Pays for Not Enforcing DMARC
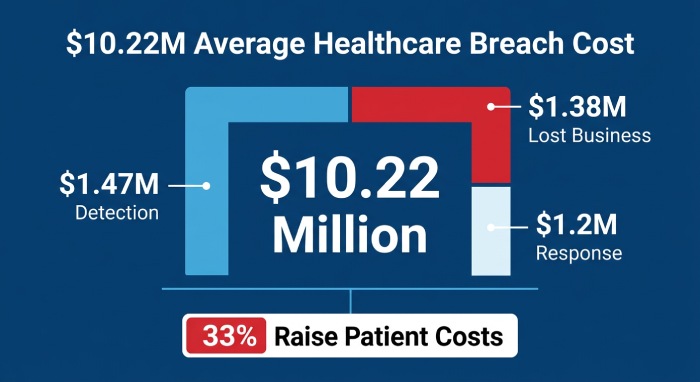
Healthcare breaches cost an average of $10.22 million per incident in 2025, the highest of any industry and more than double the global average. This includes $1.47 million for detection and escalation, $1.38 million in lost business, and $1.2 million in post-breach response. Nearly a third of breached healthcare organizations have raised costs of goods and services 15% or more to offset losses, meaning patients ultimately pay for their provider’s security failures.
HIPAA enforcement adds additional financial exposure. HHS OCR closed 22 investigations with financial penalties in 2024, collecting $12.8 million in penalties. Penalties are tiered based on negligence and can range from $141 per violation up to $2.1 million annually for the same violation type. OCR almost always requires a formal Corrective Action Plan, which involves multiple years of strict government monitoring and mandated security improvements.
And the phishing-specific losses are enormous. The FBI’s 2025 IC3 report recorded over one million cybercrime complaints for the first time in history, totaling $20.877 billion in losses, a 26% increase over 2024. BEC alone accounted for $3.05 billion. Healthcare’s share of these losses is disproportionately large given its combination of high-value targets, weak email authentication, and a culture of compliance-driven urgency that attackers exploit.
What the Government Says: CISA’s Healthcare DMARC Guidance
CISA’s healthcare-specific DMARC fact sheet is one of only a handful of sector-specific DMARC documents the agency has published. Its key recommendations:
DMARC provides an automated approach to reducing fraudulent email, before it ever reaches an employee’s inbox. This is not a suggestion, it is a direct statement from the US government’s cybersecurity agency that DMARC is the solution for healthcare phishing.
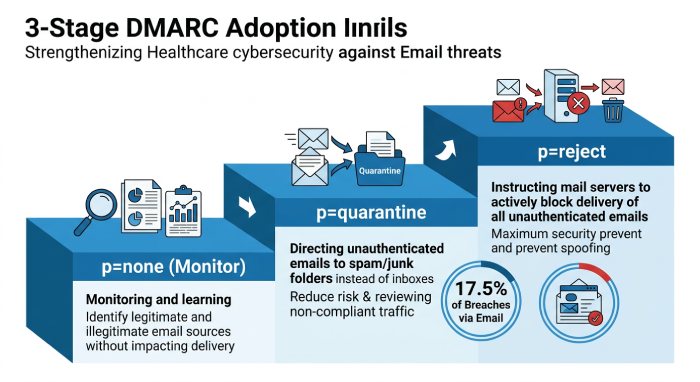
Adopt DMARC in a staged approach: Start with p=none for monitoring, progress to p=quarantine, and ultimately reach p=reject. Use feedback loops between IT departments and staff to identify any legitimate email that might be affected.
DMARC helps prevent adversaries from sending email to your organization or others using your domain. This dual protection, both inbound and outbound, is particularly important for healthcare, where spoofed emails impersonating hospitals and health systems can trick patients, partners, and vendors.
In addition, CISA’s broader email and web security guidance recommends setting DMARC to p=reject and explicitly states that reading and understanding DMARC reports is extremely difficult without a tool. BOD 25-01 reinforces these requirements for federal agencies and explicitly warns that mandates expanding into healthcare, finance, and insurance are forthcoming.
HIPAA Times analysis of CISA’s guidance notes that email accounted for approximately 17.5% of breaches in healthcare between 2010 and 2019, second only to paper/film records breaches, and that incidents involving email-based breaches have been increasing sharply since 2016.
The Healthcare DMARC Enforcement Roadmap
Healthcare’s unique challenges require a tailored approach. The following roadmap accounts for the sector’s complex email ecosystems, vendor dependencies, and patient-communication sensitivity.
Phase 1: Discovery and Inventory (Weeks 1-3)
Publish DMARC records at p=none for every domain the organization owns, including hospital system domains, clinic domains, patient portal domains, and parked domains. Point rua tags at a DMARC report analyzer. In parallel, inventory every system that sends email: EHR platforms, patient portals, lab systems, pharmacy notifications, appointment scheduling, billing, HR, marketing, and vendor communications. Healthcare organizations typically discover 30-50% more sending services than they expected during this phase.
Phase 2: Authentication and Alignment (Weeks 4-8)
For each identified sender, configure SPF and DKIM alignment. Work directly with EHR vendors (Epic, Cerner, etc.), patient portal providers, and lab notification systems to configure DKIM signing with your domain. Monitor SPF lookup counts carefully, healthcare’s large vendor ecosystem often pushes organizations past the 10-lookup limit. Consider subdomain segmentation for high-volume clinical senders.
Phase 3: Phased Enforcement (Weeks 9-14)
Move to p=quarantine with pct=10. Monitor closely for any patient-facing email being quarantined. Use your analyzer’s alerting to catch issues within hours, not days. Gradually increase pct to 25, 50, then 100. The phased approach, guided by analyzer data, eliminates the fear of disrupting patient communications, because you can see exactly what is affected at each stage.
Phase 4: Full Enforcement and Ongoing Monitoring (Weeks 15+)
Move to p=reject with pct=100. All spoofed email is now blocked. Set up ongoing monitoring for new vendors, system changes, and authentication drift. Generate compliance documentation for HIPAA audits showing your DMARC posture, policy progression, and sender authentication status. Consider BIMI implementation to display your verified hospital logo in patient inboxes, increasing trust in legitimate communications.
Why a DMARC analyzer is non-negotiable for healthcare: Healthcare’s complex ecosystem makes manual DMARC management impossible. The analyzer provides automated vendor discovery, alignment diagnostics with exact DNS fixes, SPF lookup monitoring, phased enforcement simulation, and the audit trail that HIPAA compliance requires. It is the tool that makes the difference between permanent p=none paralysis and a 90-day path to enforcement.
The Bottom Line: Healthcare Cannot Afford to Wait
The data across every source, CISA, HHS OCR, Valimail, PowerDMARC, EasyDMARC, HIPAA Journal, and KnowBe4, tells a consistent and urgent story: healthcare is the most targeted sector, the most costly to breach, and the least protected by DMARC enforcement.
11% enforcement. 289 million records breached in a single year. $10.22 million per incident. 41.9% phishing susceptibility. One in seven phishing emails opened. 700+ large breaches annually. And a government agency that has published sector-specific guidance explicitly telling healthcare organizations to implement DMARC.
Norwegian healthcare proves that this gap is not inevitable. At 55.6% enforcement, it is five times more protected than US healthcare. The difference is not technology or capability. It is regulatory pressure and organizational will. Until DMARC enforcement becomes a regulatory requirement for healthcare, and that day is coming, the organizations that act proactively will be protected. Those that wait will continue to be targets.
A DMARC report analyzer is the operational tool that makes enforcement achievable for healthcare’s uniquely complex email environments. It discovers vendors you did not know were sending email as you. It diagnoses the alignment failures your EHR system is creating. It manages the SPF lookups your vendor ecosystem is consuming. And it guides you safely from p=none to p=reject without risking a single patient notification.
The most targeted sector deserves the strongest protection. DMARC at enforcement delivers it. The only question is how much longer healthcare can afford to wait.
References and Sources
All sources referenced, with full URLs:
1. CISA: DMARC for Healthcare Delivery Organizations (PDF)
https://www.cisa.gov/sites/default/files/publications/CISA%20DMARC%20HDO_040721_508.pdf
2. CISA Insights: Enhance Email & Web Security (PDF)
3. AutoSPF: DMARC Adoption Benchmarks by Industry (11% healthcare)
https://autospf.com/blog/dmarc-adoption-benchmarks-by-industry-protection-gaps-and-sector-comparison
4. Valimail 2026 State of DMARC Report
https://www.valimail.com/dmarc-report-2026
5. PowerDMARC: Norway DMARC Adoption Report 2025 (55.6%)
https://powerdmarc.com/norway-dmarc-adoption-report
6. PowerDMARC: Email Phishing and DMARC Statistics
https://powerdmarc.com/email-phishing-dmarc-statistics
7. PowerDMARC: UK DMARC & MTA-STS Adoption Report 2026
https://powerdmarc.com/uk-dmarc-mta-sts-adoption-report
8. DMARCian: CISA Recommends DMARC for Healthcare
https://dmarcian.com/cisa-dmarc-healthcare/
9. DMARCian: CISA BOD 25-01 DMARC Requirements
https://dmarcian.com/cisa-bod-25-01-dmarc-requirements-microsoft-google/
10. DMARCReport: State of DMARC Adoption 2026 (FBI $20.877B)
https://dmarcreport.com/blog/the-dmarc-adoption-2026-domains-records-only-9-percent-protected
11. HIPAA Journal: Healthcare Data Breach Statistics (Updated 2026)
https://www.hipaajournal.com/healthcare-data-breach-statistics
12. HIPAA Journal: 2025 Healthcare Data Breach Report
https://www.hipaajournal.com/2025-healthcare-data-breach-report
13. HIPAA Journal: 2024 Healthcare Data Breach Report
https://www.hipaajournal.com/2024-healthcare-data-breach-report
14. HIPAA Journal: Largest Healthcare Data Breaches of 2025
https://www.hipaajournal.com/largest-healthcare-data-breaches-of-2025
15. HIPAA Journal: March 2025 Healthcare Data Breach Report
https://www.hipaajournal.com/march-2025-healthcare-data-breach-report
16. DeepStrike: Healthcare Data Breaches 2025 ($10.22M)
https://deepstrike.io/blog/healthcare-data-breaches-2025-statistics
17. Cobalt: Healthcare Data Breach Statistics 2025
https://www.cobalt.io/blog/healthcare-data-breach-statistics
18. Bright Defense: 60+ Healthcare Data Breach Statistics
https://www.brightdefense.com/resources/healthcare-data-breach-statistics/
19. Sprinto: Healthcare Data Breach Statistics
https://sprinto.com/blog/healthcare-data-breach-statistics
20. HIPAA Times: CISA Email Security Guidance for Healthcare
https://hipaatimes.com/how-the-cisa-email-and-web-security-guidance-contribute-to-email-practices
21. Dark Reading: Time to Get Strict with DMARC (healthcare 60%/1-in-5)
https://www.darkreading.com/cybersecurity-operations/time-get-strict-dmarc
22. EasyDMARC 2026 DMARC Adoption Report
23. Red Sift: Global DMARC Adoption Guide (73.3M domains)
https://redsift.com/guides/red-sifts-guide-to-global-dmarc-adoption
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.