The Cost of Email Spoofing: Quantifying Business Email Compromise Losses by Industry, And the ROI Case for DMARC Enforcement

Quick Answer
Business Email Compromise is not a sophisticated zero-day exploit. It does not require nation-state resources or advanced malware. It requires an email that looks like it came from someone you trust, your CEO, your vendor, your attorney, your title company, and a single employee who acts on it.
Related: Free DMARC Checker

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →Business Email Compromise is not a sophisticated zero-day exploit. It does not require nation-state resources or advanced malware. It requires an email that looks like it came from someone you trust, your CEO, your vendor, your attorney, your title company, and a single employee who acts on it. That simplicity is what makes BEC the most financially devastating category of cybercrime in America, and one of the most preventable.
In 2025, the FBI’s Internet Crime Complaint Center reported $3.046 billion in BEC losses across the United States, making it the single most financially damaging enterprise-targeted cybercrime for the fifth consecutive year (FBI IC3 2025 Annual Report). Over the past decade, cumulative global BEC losses have exceeded $55 billion (FBI PSA: BEC, The $55 Billion Scam). And yet BEC consumes a fraction of the cybersecurity attention and budget that ransomware receives.
This post aggregates data from FBI IC3 annual reports, the IBM Cost of a Data Breach Report, insurance industry claims data from Marsh McLennan and Travelers, the NAIC Cybersecurity Insurance Market Report, FinCEN advisories, HHS healthcare threat assessments, APWG phishing trends, and real estate wire fraud research to build the most comprehensive picture available of BEC’s financial impact by industry. More importantly, it translates those numbers into the ROI case for DMARC enforcement, the single most effective technical control for preventing domain spoofing, the foundation of most BEC attacks.
The Headline Numbers: BEC Losses Year Over Year
The FBI has tracked BEC losses through its Internet Crime Complaint Center since the early 2010s. The trajectory is relentless:
| Year | BEC Complaints | Reported Losses (USD) | Source |
|---|---|---|---|
| 2021 | 19,954 | $2.4 billion | FBI IC3 2021 |
| 2022 | 21,832 | $2.7 billion | FBI IC3 2022 |
| 2023 | 21,489 | $2.9 billion | FBI IC3 2023 |
| 2024 | 21,442 | $2.77 billion | FBI IC3 2024 / NAIC |
| 2025 | ~21,000+ | $3.046 billion | FBI IC3 2025 |
| Cumulative | Oct 2013, Dec 2023 | $55+ billion globally | FBI PSA April 2024 |
Sources: FBI IC3 Annual Reports 2021-2025; FBI PSA “BEC: The $55 Billion Scam”
Several things stand out in this data. First, complaint volume has remained remarkably stable at roughly 21,000-22,000 per year, suggesting that the number of organizations being targeted has plateaued but the dollar value per attack keeps climbing. Second, the $3.046 billion figure for 2025 represents a new record and a 10% increase over 2024. Third, the FBI explicitly notes that these figures are based solely on reported complaints, actual losses are almost certainly much higher.
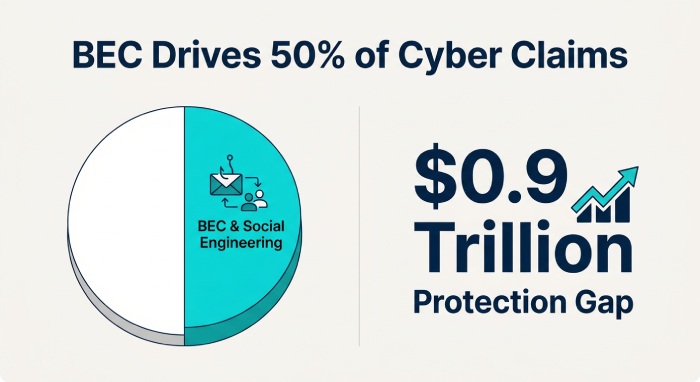
The Travelers insurance company, drawing from its own claims database, reports that BEC and social engineering fraud represented nearly half of all cyber claims over the past five years (Travelers Cyber Threat Report Q2 2025). The NAIC’s 2025 Cybersecurity Insurance Market Report confirms that BEC losses exceeded $2.77 billion in 2024, while phishing remains the leading initial attack vector linked to both ransomware and fraud (NAIC Cybersecurity Insurance Report 2025).
BEC is the most financially damaging enterprise-targeted cybercrime in America. It has caused more verified financial damage per year than ransomware for every year the FBI has tracked it. And it relies on a technique, domain spoofing, that DMARC enforcement is specifically designed to prevent.
What a Single BEC Attack Actually Costs
The FBI’s aggregate numbers tell one story. The per-incident data tells another, one that is often more persuasive for C-suite decision makers evaluating security investments.
According to the APWG’s Q2 2025 Phishing Activity Trends Report, the average amount requested in wire transfer BEC attacks in Q2 2025 was $83,099, nearly double the Q3 2024 average of $67,145 (APWG Q2 2025 Report). By Q4 2024, that average had already hit $128,980 (APWG Q4 2024 Report).
IBM’s Cost of a Data Breach Report provides the broader organizational cost. In the 2022 report, breaches initiated through business email compromise cost an average of $4.89 million, while breaches initiated through phishing cost $4.91 million, among the costliest of all attack vectors (IBM Cost of a Data Breach 2022). The 2025 edition reports that ransomware-initiated breaches now cost $5.08 million on average, but notes that email-based attack vectors including BEC and phishing continue to have among the longest breach lifecycles, meaning they are harder to detect and more expensive to contain (IBM Cost of a Data Breach 2025).
The FBI’s own case files illustrate the extremes. In March 2023, a critical infrastructure construction project in New York lost $50 million in a single BEC incident. The IC3 Recovery Asset Team was able to freeze $44.9 million, but the attack demonstrated that no industry and no transaction size is immune (FBI IC3 2023 Report). In April 2025, a city government in Oregon lost $6 million to a BEC attack on the same fraudulent bank account that had been used in a prior scheme (FBI IC3 2025 Report).
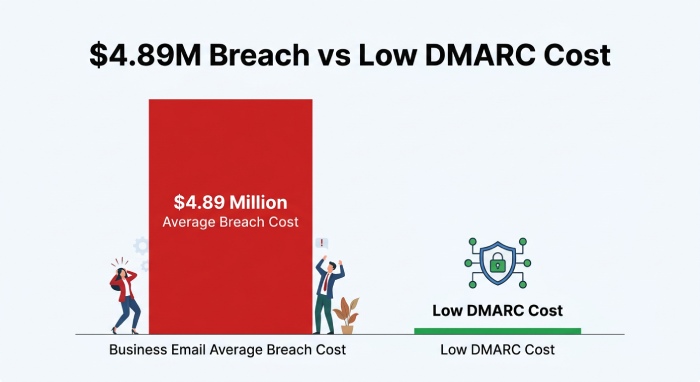
What This Means for Your Budget
If the average BEC wire transfer request is $83,099 and the average total cost of a BEC-initiated breach is $4.89 million, then the cost of DMARC enforcement, typically a few thousand dollars per year for a mid-market organization, represents a return on investment measured in orders of magnitude. A single prevented attack pays for years of enforcement.
BEC Losses by Industry: Where the Money Goes
BEC does not target every industry equally. The data reveals that certain sectors, those involving large financial transactions, sensitive data, or complex vendor relationships, bear disproportionate losses.
Healthcare
Healthcare is consistently one of the most targeted sectors. The U.S. Department of Health and Human Services’ Health Sector Cybersecurity Coordination Center (HC3) has published multiple threat assessments documenting BEC’s impact on the health sector. Email fraud attacks on healthcare jumped 473% between 2017 and 2019 according to HC3’s analysis (HC3 BEC Threat Assessment). A 2024 HC3 presentation confirmed that BEC remains a top threat to healthcare organizations, noting that copycat domain names were used in nearly 67% of BEC attacks against healthcare (HHS BEC & Healthcare 2024).
IBM’s data adds the cost dimension: healthcare has been the most expensive industry for data breaches for over 14 consecutive years. The 2022 report put the average healthcare breach at $10.10 million, more than double the cross-industry average. BEC and phishing are among the top initial attack vectors driving these costs.
Real Estate
Real estate is uniquely vulnerable to BEC because the industry runs on large wire transfers between parties who often communicate primarily by email. The FBI published a dedicated congressional report on BEC and real estate wire fraud in 2022, documenting the systematic targeting of homebuyers, title companies, and attorneys (FBI Congressional Report on BEC & Real Estate Wire Fraud).
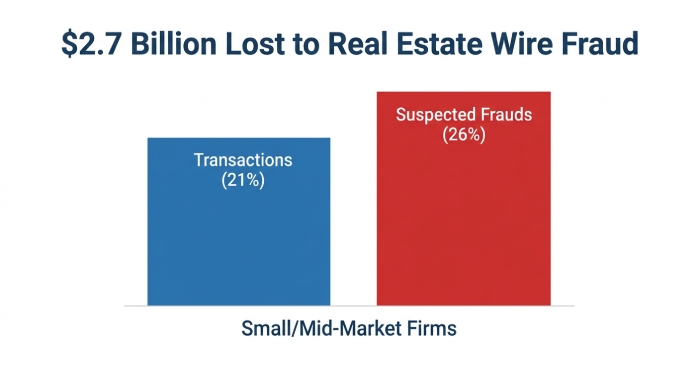
CertifID’s 2024 State of Wire Fraud Report found that BEC continued to be one of the top threats in real estate at $2.7 billion in total losses, with smaller and mid-market firms managing a disproportionately higher-risk portfolio, comprising 21% of transactions but 26% of suspected frauds (CertifID 2024 Wire Fraud Report). The FBI’s 2025 IC3 report documents a case where a senior citizen in Missouri received compromised wire instructions from a spoofed title company email and nearly lost $1.3 million.
Financial Services & Banking
Financial institutions are both targets and intermediaries in BEC schemes. FinCEN’s 2019 advisory on email compromise fraud noted that financial institutions filed thousands of Suspicious Activity Reports related to BEC, with losses frequently involving wire transfers to domestic accounts that were rapidly depleted (FinCEN Advisory FIN-2019-A005). IBM’s 2022 report showed financial services as the second most expensive industry for breaches at $5.97 million average, after healthcare.
The Idaho Department of Finance’s comprehensive BEC research report identified that the most attractive targets for BEC attackers are businesses that conduct large transactions through financial institutions, lending entities, real estate companies, and law firms (Idaho Dept. of Finance BEC Report).
Government & Critical Infrastructure
Government entities are increasingly targeted. The FBI’s 2025 IC3 report documents a $6 million BEC loss by a city government in Oregon. The 2025 report also shows that healthcare and public health was the most-targeted critical infrastructure sector, with 182 data breaches and 460 ransomware attacks, followed by critical manufacturing, financial services, and government facilities.
Construction & Manufacturing
The $50 million BEC loss from the New York critical infrastructure construction project in 2023 is the largest single BEC incident documented in the FBI’s public case files. Construction firms are particularly vulnerable because they routinely process large vendor payments and change orders by email, creating multiple opportunities for attackers to intercept and redirect funds.
SMBs Across All Industries
The Massachusetts Cybersecurity Center’s BEC investigations presentation noted that BEC attacks averaged roughly $137,000 per case and that the estimates are almost certainly low because organizations are reluctant to report (Mass Cyber Center BEC Presentation). Marsh McLennan’s analysis of its claims database, over 800,000 claims across multiple insurance lines, confirmed that BEC events are trending upward and that the initial financial loss can be severe relative to the victim’s revenue (Guy Carpenter/Marsh BEC Report).
The AI Accelerant: Why BEC Is Getting Worse
For the first time, the FBI’s 2025 IC3 report documented AI-enabled cybercrime as a distinct category. The bureau received 22,364 AI-related complaints with losses exceeding $893 million. AI is being used to generate convincing phishing emails, create synthetic video content for impersonation, and clone voices for social engineering calls.
BEC is particularly susceptible to AI enhancement. Traditionally, one of the few defenses available to employees was spotting grammatical errors or unusual phrasing in spoofed emails. AI-generated text eliminates that signal entirely. The NAIC’s 2025 report confirms that vishing (voice phishing) surged 442% in 2024, driven in part by AI voice cloning technology. Help desk social engineering also surged as adversaries became more organized.
This convergence, domain spoofing plus AI-generated content plus voice cloning, makes DMARC enforcement more critical than ever. DMARC cannot stop an AI-generated email, but it can stop that email from being sent from your exact domain. When your domain enforces p=reject, the spoofed email never reaches the inbox, regardless of how convincing the AI-generated content might be.
What the Insurance Industry Is Telling Us
The cyber insurance market provides a uniquely valuable lens on BEC losses because insurers see the actual claims data, not just what gets reported to law enforcement.
Travelers reports that BEC and social engineering fraud represented nearly half of all cyber claims over the past five years. Marsh McLennan’s Cyber Risk Intelligence Center, analyzing over 9,000 cyber policy claims and 6,000 crime policy claims from a database of 800,000+ total claims, confirmed that BEC events are trending upward and that the initial loss can be severe when measured against the victim’s revenue.
The NAIC’s 2025 Cybersecurity Insurance Market Report notes that the cyber insurance market is estimated at $14 billion in gross written premium and projected to more than double by 2027, but a $0.9 trillion cyber risk protection gap persists, the difference between insured losses and actual economic losses. BEC is a major contributor to this gap because many BEC losses are absorbed directly by the victim organization without triggering a cyber insurance claim.
The insurance industry’s message is clear: BEC is not a niche threat, it is one of the most frequent and financially damaging claims categories in the entire cyber insurance market. DMARC enforcement is one of the few technical controls that directly reduces this exposure.
The ROI Case for DMARC Enforcement
Every data point in this article converges on a single conclusion: the cost of not enforcing DMARC is orders of magnitude greater than the cost of implementing it. Here is the math:
| Cost of Inaction | Cost of DMARC Enforcement |
|---|---|
| Average BEC wire transfer request: $83,099 (APWG Q2 2025) | Annual DMARC enforcement platform: $2,000-$10,000 for SMBs |
| Average BEC breach total cost: $4.89 million (IBM 2022) | DNS record configuration: Free (internal IT) |
| Single large BEC loss: $6M (Oregon city, 2025) to $50M (NY construction, 2023) | Aggregate report monitoring: Included in platform cost |
| Insurance premium increases after a claim | Potential insurance premium reductions for enforcement |
| Reputational damage: Unquantifiable | Compliance with PCI DSS, Google/Yahoo, Microsoft requirements |
Marsh McLennan’s analysis identified the top controls correlated with lower BEC claim frequency. Among them: email filtering, employee training on identifying fraudulent emails, and multi-factor authentication. DMARC enforcement is the upstream control that prevents the spoofed email from reaching the employee in the first place, making all downstream controls less likely to be needed.
The UK’s NCSC demonstrated this at scale: after reaching 100% DMARC enforcement across central government departments, over 80 million spoofed emails were blocked in a single 30-day period (NCSC ACD 6th Year Report). That is 80 million opportunities for a BEC attack, eliminated before any employee had to make a judgment call.
Practical Next Steps by Audience
For C-Suite and Board Members
Frame DMARC enforcement as a financial risk control, not an IT project. The data from the FBI, IBM, and the insurance industry supports a clear ROI calculation. Ask your CISO one question: “What is our DMARC policy, and when will we reach p=reject?” If the answer is “p=none” or “I don’t know,” your domain is currently impersonatable by any attacker in the world.

For IT and Security Teams
If you are at p=none, begin analyzing your DMARC aggregate reports immediately. Identify all legitimate senders, align SPF and DKIM, and build a timeline to p=reject. A DMARC reporting platform like DMARC Report translates raw XML into actionable dashboards. If you have no DMARC record at all, publish one today with an RUA tag, it takes minutes at the DNS level.
For SMB Owners
You are disproportionately at risk. The Idaho Department of Finance’s research confirms that financial losses per BEC attack are increasing for both businesses and individuals. The average BEC loss of $137,000 can be existential for a small business. DMARC enforcement is not expensive, it does not require a dedicated security team, and it is one of the few controls that directly prevents your domain from being weaponized against your own customers and partners.
The Bottom Line
$3.046 billion. That is how much American businesses and individuals reported losing to BEC in 2025 alone. $55 billion globally over the past decade. $4.89 million per breach. $83,099 per wire transfer request. $893 million in AI-enabled cybercrime. Nearly half of all cyber insurance claims. Healthcare, real estate, financial services, government, construction, no industry is exempt.
Every one of these attacks begins with an email that appears to come from a trusted domain. DMARC enforcement, moving from p=none to p=reject, blocks that email before it ever reaches an inbox. The technology is proven. The data is unequivocal. The only remaining variable is whether your organization will act on it.
Sources & References
All statistics are drawn from publicly accessible PDF reports from government agencies, nonprofit research organizations, insurance industry publications, and institutional sources.
1. FBI IC3 2025 Annual Report, Source for $3.046 billion in BEC losses, 1,008,597 total complaints, $20.877 billion total cybercrime losses, 22,364 AI-enabled crime complaints, $6 million Oregon city government BEC case, and healthcare as most-targeted critical infrastructure sector.
URL: https://www.ic3.gov/AnnualReport/Reports/2025_IC3Report.pdf
2. FBI IC3 2024 Annual Report, Source for $16.6 billion in total losses, 21,442 BEC complaints, $2.7 billion in BEC losses in 2024.
URL: https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
3. FBI IC3 2023 Annual Report, Source for $2.9 billion in BEC losses, 21,489 complaints, $50 million single BEC incident (NY construction), and $426,000 real estate BEC case.
URL: https://www.ic3.gov/AnnualReport/Reports/2023_IC3Report.pdf
4. FBI IC3 2022 Annual Report, Source for $2.7 billion BEC losses, 73% FFKC recovery rate, $590 million in domestic BEC FFKC incidents.
URL: https://www.ic3.gov/AnnualReport/Reports/2022_ic3report.pdf
5. FBI IC3 2021 Annual Report, Source for $2.4 billion in BEC losses and 19,954 complaints.
URL: https://www.ic3.gov/AnnualReport/Reports/2021_ic3report.pdf
6. FBI PSA: BEC, The $55 Billion Scam, Source for cumulative global BEC losses exceeding $55 billion (Oct 2013-Dec 2023).
7. FBI Congressional Report on BEC & Real Estate Wire Fraud (2022), Congressional report documenting systematic BEC targeting of real estate transactions.
8. APWG Phishing Activity Trends Report Q2 2025, Source for $83,099 average BEC wire transfer request.
URL: https://docs.apwg.org/reports/apwg_trends_report_q2_2025.pdf
9. APWG Phishing Activity Trends Report Q4 2024, Source for $128,980 average BEC wire transfer request.
URL: https://docs.apwg.org/reports/apwg_trends_report_q4_2024.pdf
10. IBM Cost of a Data Breach Report 2022, Source for $4.89M average BEC breach cost, $4.91M phishing breach cost, $10.10M healthcare breach cost, $5.97M financial services breach cost.
URL: https://www.key4biz.it/wp-content/uploads/2022/07/Cost-of-a-Data-Breach-Full-Report-2022.pdf
11. IBM Cost of a Data Breach Report 2025, Source for $5.08M ransomware breach cost and email-based attack lifecycle data.
URL: https://www.bakerdonelson.com/webfiles/Publications/20250822_Cost-of-a-Data-Breach-Report-2025.pdf
12. Travelers Cyber Threat Report Q2 2025, Source for BEC/social engineering representing nearly half of all cyber claims; $50 billion cumulative global BEC losses.
URL: https://www.corvusinsurance.com/hubfs/Ransomware_Reports/Q2_25_Travelers_Cyber_Threat_Report.pdf
13. Guy Carpenter/Marsh McLennan, Cyber’s Sleeper Threat: BEC, Insurance claims analysis from 800,000+ claims database showing BEC trending upward and initial loss severity.
14. NAIC 2025 Cybersecurity Insurance Market Report, Source for $2.77 billion BEC losses in 2024, 442% vishing surge, $0.9 trillion cyber protection gap, and $14 billion cyber insurance market size.
URL: https://content.naic.org/sites/default/files/inline-files/2025_Cybersecurity_Insurance%20Report.pdf
15. FinCEN Advisory FIN-2019-A005, Email Compromise Fraud Schemes, U.S. Treasury advisory on BEC financial red flags for financial institutions.
URL: https://www.fincen.gov/system/files/advisory/2019-07-16/Updated%20BEC%20Advisory%20FINAL%20508.pdf
16. HHS HC3, BEC: Deception and Theft (Healthcare Sector), Source for 473% increase in email fraud attacks on healthcare and 67% copycat domain usage.
17. HHS, BEC & Healthcare (May 2024), Updated HC3 presentation on BEC threats to healthcare organizations.
URL: https://www.hhs.gov/sites/default/files/business-email-compromise-healthcare-tlpclear.pdf
18. Idaho Dept. of Finance, BEC Report, Source for analysis of BEC targeting patterns, financial institution intermediary role, and policy recommendations.
19. Massachusetts Cybersecurity Center, BEC Investigations, Source for $137,000 average BEC loss per case and municipal BEC attack patterns.
URL: https://masscybercenter.org/sites/default/files/2024-09/Business%20Email%20Compromise%209.12.24.pdf
20. CertifID, 2024 State of Wire Fraud Report, Real estate wire fraud data showing SMB disproportionate risk (21% of transactions, 26% of frauds).
21. UK NCSC Active Cyber Defence 6th Year Report, Source for 80 million spoofed emails blocked in 30 days after 100% central government DMARC enforcement.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.