Ensuring Easy and Secure Authentication: A Guide

Quick Answer
Modern authentication has to balance compliance with GDPR and CCPA, the realities of SaaS and ecommerce data sprawl, and user experience. The recommended approach is to assess current authentication posture, pick solutions that integrate with existing IAM, cloud services, and VPNs, then roll out next-gen authentication in phases with monitoring. SPF, DKIM, and DMARC act as the foundational email layer for blocking phishing and spoofing without adding user friction.
Related: Free DMARC Checker


DMARC is the only email authentication protocol that gives you both enforcement and visibility, says Brad Slavin, General Manager of DuoCircle. SPF and DKIM authenticate silently - DMARC tells you what happened and lets you control the outcome. That combination of reporting and policy is why DMARC adoption is accelerating.
DMARC Report
Ensuring Easy and Secure Authentication: A Guide
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-12191">
<source src="https://media.mailhop.org/dmarcreport/images/2024/04/Ensuring-Easy-and-Secure-Authentication-A-Guide.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M39S">2:39</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-12191" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-12191" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-12191" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-12191" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/ensuring-easy-and-secure-authentication-a-guide/&t=Ensuring Easy and Secure Authentication: A Guide" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/ensuring-easy-and-secure-authentication-a-guide/&url=Ensuring Easy and Secure Authentication: A Guide" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/04/Ensuring-Easy-and-Secure-Authentication-A-Guide.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/ensuring-easy-and-secure-authentication-a-guide/" class="input-link input-link-12191" title="Episode URL" readonly />
<button class="copy-link copy-link-12191" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-12191” readonly/>
<button class="copy-embed copy-embed-12191" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
News Flash! Implementing an **iron-clad authentication for every login and online transaction is no longer a “good-to-have” aspect of your online existence. Thanks to the latest crackdown on loose security practices by tech giants, your authentication game cannot be like perfunctory frisking. After all, would you ever let a stranger enter your home if they simply introduced themselves by their name and gave no other information?
So, what does this mean for you and your business?
Given the hyperconnected nature of the digital world, we understand that it is very challenging for security teams to protect sensitive data and **patch vulnerabilities without requiring disruptive manual processes. Imagine the plight of these teams if they had to execute all the nitty gritty of increased security requirements manually!
So, how do you ensure that your emails and other **online interactions meet industry standards while evading the risk of malicious attacks that have the potential to take down your entire digital architecture?
In this article, we’ll delve into all the strategies you can adopt to ensure a **seamless transition to robust authentication.
The Imperative of Secure and Effortless Authentication
Before we get into the strategic approach that you should follow for implementing secure and effortless authentication, it’s crucial to understand why this balance is not just beneficial but necessary.
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
The Perilous Threat Landscape
We hate to tell you, but there is little to **no scope for redemption from the dangers that lurk in today’s digital environment. As if the current frequency and severity of cyberattacks weren’t bad enough, the situation is only getting worse.
This calls for organizations to follow a more **stringent approach to cybersecurity, which includes moving beyond one-time passcodes (OTP), push-to-text or push-to-email , etc.
Compliance with Data Protection Regulations
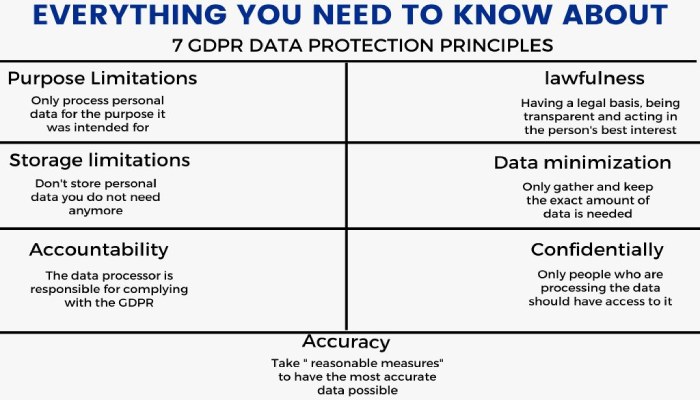
Whether you’re a large organization with a **global footprint or a small startup making its mark, you’d agree with us when we say that adhering to data protection regulations is no easy feat. Regulations like GDPR (General Data Protection Regulation) in the EU and CCPA (California Consumer Privacy Act) require organizations to stick to strict data protection standards, ensuring the privacy and security of both consumer and employee information.
And what if you fail to do so?
In that case, you would want to brace yourself for the **financial and reputational damage that will cause. Therefore, it is crucial for your company, regardless of its size, to implement the necessary measures.
The Era of SaaS And E-Commerce
It’s no surprise that SaaS and E-commerce are witnessing a golden era, but then again, not all that glitters is gold! That is to say, this digital growth driven by SaaS and e-commerce brings along a **massive influx of data from various digital interactions, integrations, and transactions. This is also where the problem comes in! Managing such a large amount of data not only becomes a challenge for security teams but also opens doors for adversaries to creep in.
In order to **protect sensitive data and maintain the confidence of important stakeholders, it is crucial to adopt a strategic approach to safeguarding data against the constantly evolving landscape of cyber threats.
Crafting a User-Friendly, Secure Authentication Journey
Who said authentication could not be fuss-free and secure? Gone are the days when heightened security meant a complicated process for users and organizations. In fact, it comes with added benefits, like reduced risk of cyber threats and enhanced user engagement and trust.
Here’s how you can create a **safe digital environment for your users and enable them to interact with services and platforms with confidence and ease.
Know Thy Security Posture
Before getting into the **nitty-gritty **of revamping your security processes, it is crucial to take a closer look at what your current authentication techniques look like. By going deep into the intricacies of the existing security landscape, you can pinpoint vulnerabilities, assess the effectiveness of current authentication methods, and understand the evolving needs of their users.
Understand the Importance of User Experience
The last thing you’d want for your users is to struggle with multiple unnecessary steps in the name of enhanced security**. After all, robust authentication does not necessarily mean it should be arduous and overlook your users’ convenience.
That’s why it’s super important to pick an authentication solution that seamlessly integrates with everything your team uses - from the identity access management (IAM) system that keeps things tight, to the **cloud services that let you work from anywhere, and even the VPNs that act as private tunnels for your internet activity.
Enforce Next-gen Authentication
We understand that setting up the latest authentication techniques can be very tricky and exhausting, especially when it comes to integrating them with your apps and on multiple devices . Platforms like Auth0 are popular for simplifying this process, but many organizations look for Auth0 alternatives due to reasons like scalability costs, specific customization requirements, or integration flexibility.
To ensure that everything goes as smoothly as possible, try following a phased approach - pick a group of users or certain apps and introduce the new system there first. This allows you to even out any bumps that you might encounter along the way and ensure that everything’s working perfectly before you launch it to your users.
Keep an Eye on Your Solutions
Once you’ve put the **new authentication system in place, watch closely to see how well everyone’s getting used to it. Make sure everything’s set up just right. Seeing how quickly and easily users get on board with the new setup is a great way to tell if it’s hitting the mark.

Summing it Up
Seamless and secure authentication is like a jigsaw puzzle and one of its most important pieces is email authentication. By implementing standards like DMARC, your organization can verify sender identities, prevent email spoofing, and block phishing attempts, all without adding any friction for the end user.
Feeling overwhelmed by the idea of striking a balance between ease of use and robust protection? The thing about maintaining a resilient authentication process is, that it is not as complex as it seems but is surely an ongoing one. This leaves no scope for complacency and requires you to stay informed and adaptive.
If you want to craft an email authentication strategy that’s both user-friendly and defensible, DMARCReport is here to your rescue. Contact us to learn more about how we can assist in enhancing your email authentication process and ensuring your communications are secure, compliant, and effective.
Sources
Topics

Content Specialist
Content Specialist at DMARC Report. Writes vendor-specific email authentication guides and troubleshooting walkthroughs.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.