Jaguar Cyber Breach, Cybersecurity Geolocation Link, India Cybersecurity Burnout

Quick Answer
Jaguar Cyber Breach, Cybersecurity Geolocation Link, India Cybersecurity Burnout Jaguar Cyber Breach, Cybersecurity Geolocation Link, India Cybersecurity Burnout /! This file is auto-generated / !function(d,l){"use strict";l.querySelector&&d.addEventListener&&"undefined"!=typeof URL&&(d.wp=d.wp||{},d.wp.receiveEmbedMessage||(d.wp.receiveEmbedMessage=function(e){var t=e.data;if((t||t.secret||t.message||t.value)&&!/[^a-zA-Z0-9]/.test(t.secret)){for(var s,r,n,a=l.querySelectorAll('iframe[data-secret="'+t.secret+'"]'),o=l.querySelectorAll('blockquote[data-secret="'+t.secret+'"]'),c=new RegExp("^https?:$","i"),i=0;i ' title="Embed Code" class="input-embed input-embed-31465" readonly/> It’s September, the first week, and we are back again with our weekly bulletin.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
DMARC Report
Jaguar Cyber Breach, Cybersecurity Geolocation Link, India Cybersecurity Burnout
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-31465">
<source src="https://media.mailhop.org/dmarcreport/images/2025/09/Jaguar-Cyber-Breach-Cybersecurity-Geolocation-Link-India-Cybersecurity-Burnout.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M15S">2:15</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-31465" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-31465" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-31465" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-31465" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/jaguar-cyber-breach-cybersecurity-geolocation-link-india-cybersecurity-burnout/&t=Jaguar Cyber Breach, Cybersecurity Geolocation Link, India Cybersecurity Burnout" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/jaguar-cyber-breach-cybersecurity-geolocation-link-india-cybersecurity-burnout/&url=Jaguar Cyber Breach, Cybersecurity Geolocation Link, India Cybersecurity Burnout" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/09/Jaguar-Cyber-Breach-Cybersecurity-Geolocation-Link-India-Cybersecurity-Burnout.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/jaguar-cyber-breach-cybersecurity-geolocation-link-india-cybersecurity-burnout/" class="input-link input-link-31465" title="Episode URL" readonly />
<button class="copy-link copy-link-31465" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-31465” readonly/>
<button class="copy-embed copy-embed-31465" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
It’s September, the first week, and we are back again with our weekly bulletin. The ultimate goal is to keep you informed about the latest global cyber developments. It is only through **cyber education and a proactive approach that you can safeguard your data from highly sophisticated cyberattacks.
This week-1 edition will focus on the recent threat attack on Jaguar Land Rover. Secondly, we will talk about geolocation and cybersecurity. Lastly, we will discuss the rising instances of cyber burnout across India.
If this sounds like an interesting read, stay with us and keep reading!

Jaguar Land Rover experienced a cyberattack
Jaguar Land Rover (JLR), the luxury automobile manufacturer, has recently experienced a cyberattack. Because of this cyber incident, Jaguar had to shut down its worldwide IT infrastructure. It also stopped the production operations at the Halewood plant.
The breach took place on Monday, September 1. Since then, a global operational crisis has ensued. JLR has taken swift mitigational steps to limit the extent of the cyber damage. JLR instructed the Merseyside workers to stay put inside their homes. Production staff received emails at dawn break around 4:30 AM on Monday. The emails instructed them to avoid their shifts that day.
Those who were on duty at the Halewood plant were sent back home. This resulted in the complete shutdown of **manufacturing operations at Halewood.
JLR informed its workforce about the cyber mishap and stated that they are “proactively shutting down our systems.” Halewood management has further confirmed that the shutdown will continue until Wednesday. The shutdown extension hints at the severity of the threat.

While the production and IT infrastructure are currently non-functional, JLR has assured its customers that no customer data has been compromised. They are working incredibly hard to restore their digital mechanism.
The **online restoration process is complicated and cumbersome because the ultimate goal is to eliminate the slightest risk of data breach first.
Cybersecurity and geolocation: What’s the connection?
Geolocation is one of the most potent features that cybercrooks can misuse to exploit victims. Threat actors actively use geolocation data to carry out phishing campaigns that involve targeting the victims with localized malicious advertisements. Geolocation adds that extra layer of precision to the cyberattacks. The worst aspect of this attack is that the malicious files manage to evade detection through the networks and are activated only once they reach the targeted geographical location.
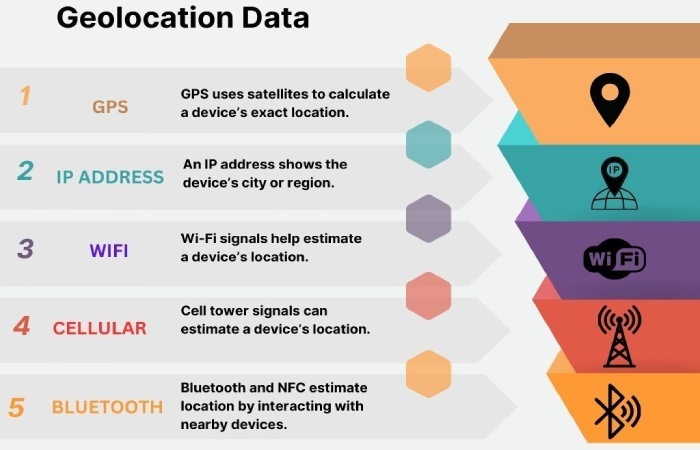
Cybercriminals love to exploit geolocation data to carry out threat attacks because the data allows them to make hyper-personalized campaigns. For example, one of the groups of cybercrooks, SideWander APT group, used geo-location data effectively to target specific nations like Sri Lanka and Bangladesh. Threat actors are gradually getting sophisticated with each cyberattack. They have learnt to bypass the **cybersecurity defense systems by manipulating the already established patterns that are supposed to be “normal.” They use botnets to go undetected, even when IT departments and Managed Service Providers are using VPNs and encryption technologies.

Cybersecurity burnout is real in India!
The Future of Cybersecurity in Asia Pacific and Japan report by Sophos states that Indian organizations are increasingly facing cybersecurity burnout. While the percentage was 83% last year, in 2025, it has hit 95%. According to the study, the reason behind the steep rise in burnout instances is due to a spike in threat activities, alert overloads, and excessive pressure from executive leadership. Due to burnout, the productivity of cybersecurity experts is taking a nosedive. The incident response times have been slower than ever. Burnout instances are also leading to increased data breaches and employee resignations.
According to the same report, around 87% of organizations offer employee counseling to prevent instances of burnout and excessive stress.
Artificial Intelligence usage stands at a crossroads. While 97% of Indian organizations rely on AI tools like **ChatGPT and Co-Pilot for increased productivity, 62% of Indian organizations admit to using shadow AI or unauthorized AI tools. Experts like Aaron Bugal believe that the use of shadow AI can further increase the risk of cyberattacks.

The study further found that enterprises are struggling to keep pace with the rapidly evolving cybersecurity challenges and regulations. Additionally, 71% of Indian organizations plan to increase their cybersecurity budgets in 2026. Around 30% of these organizations have decided to increase their cybersecurity budget by **10% **or more in the upcoming years.
Cybersecurity standards like DMARC, DKIM, and SPF are strengthening email defenses against phishing and spoofing attacks.
_The sophistication of threat attacks in recent times has not only affected the financial systems and crucial infrastructures of nations like India, Africa, Singapore, and Japan, but it has also left cybersecurity experts exhausted and numb. _The advent of **artificial intelligence has further added to the complications. It is therefore high time that organizations start taking cyber threats more seriously and educate themselves about cybersecurity mechanisms and AI.

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.