PayPal Email Scam, BreachForums Operators Detained, Hackers Target Airlines

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. PayPal Email Scam, BreachForums Operators Detained, Hackers Target Airlines
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses.
The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
DMARC Report
PayPal Email Scam, BreachForums Operators Detained, Hackers Target Airlines
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-29256">
<source src="https://media.mailhop.org/dmarcreport/images/2025/07/PayPal-Email-Scam-BreachForums-Operators-Detained-Hackers-Target-Airlines.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M8S">2:08</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-29256" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-29256" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-29256" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-29256" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/paypal-email-scam-breachforums-operators-detained-hackers-target-airlines/&t=PayPal Email Scam, BreachForums Operators Detained, Hackers Target Airlines" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/paypal-email-scam-breachforums-operators-detained-hackers-target-airlines/&url=PayPal Email Scam, BreachForums Operators Detained, Hackers Target Airlines" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/07/PayPal-Email-Scam-BreachForums-Operators-Detained-Hackers-Target-Airlines.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/paypal-email-scam-breachforums-operators-detained-hackers-target-airlines/" class="input-link input-link-29256" title="Episode URL" readonly />
<button class="copy-link copy-link-29256" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-29256” readonly/>
<button class="copy-embed copy-embed-29256" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Hello people! It’s July already, and we’re here once again with the latest global cybersecurity incidents. The threat actors are getting sophisticated with their approach, one cyberattack at a time. So, you must **stay alert and aware to prevent any kind of potential cyber mishap.
With this intention, we bring to you the first edition of the month. This bulletin involves the details of the latest PayPal scam. We will also focus on how **French police nabbed the BreachForum operators. Lastly, we will discuss how a group of threat actors is now targeting airlines and the transportation sector.
Let’s not waste time anymore and jump into the details that matter!
PayPal scam using real emails to trick users!
If you use PayPal for receiving and sending funds, this is something you cannot afford to ignore. A new PayPal scam is doing the rounds. The worst thing is that scammers have managed to carry out this cyberbreach in a highly convincing manner. Even the most aware and vigilant users are falling prey to this latest PayPal scam.
The cyberattackers are abusing the PayPal domain itself to send out malicious emails that look **100% **real and convincing. You will receive real-life messages through these emails that are too hard to tell apart. Threat actors are misusing the “money request” or “add address” feature of PayPal to send out real emails from PayPal’s original domain. Since each of these emails is coming from the real PayPal domain, they pass through the **authentication checks easily and land in your primary inbox. Also, there are rarely any malicious links added to these emails. All you will get to see is a phone number (the contact number of the scammer). The emails are designed in a way to grab your attention and compel you to take swift action without thinking much.
Once they have sent the first email, it is highly likely that they will follow up by connecting with you while pretending to be someone from the PayPal support team. Some emails can also contain a malicious link to “ secure your account ”. Eventually, this link will lead you to a fake login page designed to harvest your login credentials and other personal data.
Reddit and other **cybersecurity forums are already buzzing with reports around this ongoing PayPal scam.
BreachForums operators arrested in France!
The French police claims to have arrested the five main operators of the BreachForum cybercrime forum. Basically, it was a website where threat actors used to leak as well as sell stolen data. Le Parisien claims that a law enforcement operation was conducted by BL2C, the cybercrime unit in Paris, this Monday. The **Paris police department managed to raid different regions such as Seine-Maritime, Hauts-de-Seine, and Réunion. During the raids, the police nabbed four hackers who were popular online as “Noct,” “Hollow,” “Depressed,” and “ShinyHunters.” The police department has claimed that the 5th operator, “IntelBroker,” has already been arrested back in February 2025.
The original BreachForums community shut down in 2023 after its operator, Conor Brian FitzPatrick, also known as Pompompurin , was arrested. The 2.0 BreachForums was launched by other active members of the original community. These five operators are accused of being involved in major data breach instances against France Travail, the French Football Federation, and SFR.
The BreachForums V2 was forced to go offline **back in April 2025 after someone managed to exploit the site, leveraging a MyBB zero-day vulnerability. Since then, it has been offline.
FBI and cybersecurity firms claim a specific hacking group is targeting airlines and the transportation sector!
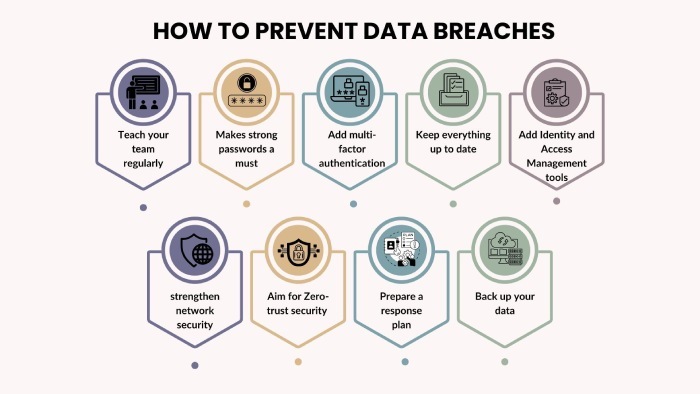
Scattered Spider, a hacking group, is currently targeting the airlines and transportation sector. Experts like Mandiant and the security research division Unit 42 also claimed to have witnessed Scattered Spider’s attempts to target the airline industry. The FBI and cybersecurity firms are urging airlines and the transportation sector to implement DMARC, DKIM, and SPF protocols to defend against escalating email-based threats.
This is a group of mainly English-speaking hackers, specifically young adults and teenagers. Their primary goal is to steal and extort personal data from company networks. They are well-versed in their hacking techniques, such as phishing, social engineering, ransomware deployment, and subtle threats.

FBI believes that hackers can target anyone and everyone who comes under the airline ecosystem . WestJet, Canada’s second-largest airline, as well as Hawaiian Airlines, have already been targeted by threat actors in recent times. However, it is yet not clear whether or not Scattered Spider is behind both of these cyberattacks. Media reports, though, claim that the WestJet attack was carried out by the Scattered Spider group.
Apart from airlines, Scattered Spider group is also eyeing the transport industry, insurance sector, and the UK retail sector. Before this shift in interest, Scattered Spider used to hack into the networks of casinos, technology giant,s and hotel chains.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.