Scan Carefully First, Education Under Threat, AI Phishing Surge

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Scan Carefully First, Education Under Threat, AI Phishing Surge
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


Domain spoofing is trivially easy without DMARC enforcement, says Brad Slavin, General Manager of DuoCircle. Anyone can send email that looks like it comes from your domain. DMARC with p=reject is the only way to tell receiving servers to block unauthorized senders completely.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Scan Carefully First, Education Under Threat, AI Phishing Surge
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">Pause Episode
</button>
<audio preload="none" class="clip clip-38909">
<source src="https://media.mailhop.org/dmarcreport/images/2026/02/Scan-Carefully-First-Education-Under-Threat-AI-Phishing-Surge.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M18S">2:18</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-38909" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-38909" title="Share">Share</button>
</nav>RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-38909" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-38909" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/scan-carefully-first-education-under-threat-ai-phishing-surge/&t=Scan Carefully First, Education Under Threat, AI Phishing Surge" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/scan-carefully-first-education-under-threat-ai-phishing-surge/&url=Scan Carefully First, Education Under Threat, AI Phishing Surge" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2026/02/Scan-Carefully-First-Education-Under-Threat-AI-Phishing-Surge.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/scan-carefully-first-education-under-threat-ai-phishing-surge/" class="input-link input-link-38909" title="Episode URL" readonly />
<button class="copy-link copy-link-38909" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-38909” readonly/>
<button class="copy-embed copy-embed-38909" title="Copy Embed Code" aria-label="Copy Embed Code"></button>Last week was all about phishing attacks that targeted naive users left, right, and center. Research findings revolved around an upsurge in AI-backed phishing attacks, while experts have noticed phishing QR codes as an emerging threat in the cybersecurity landscape. Meanwhile, India has been experiencing 3,100 phishing attacks per week.
The silver lining in the dark clouds is that a group of students used phishing tactics against their teachers, but with good intentions.
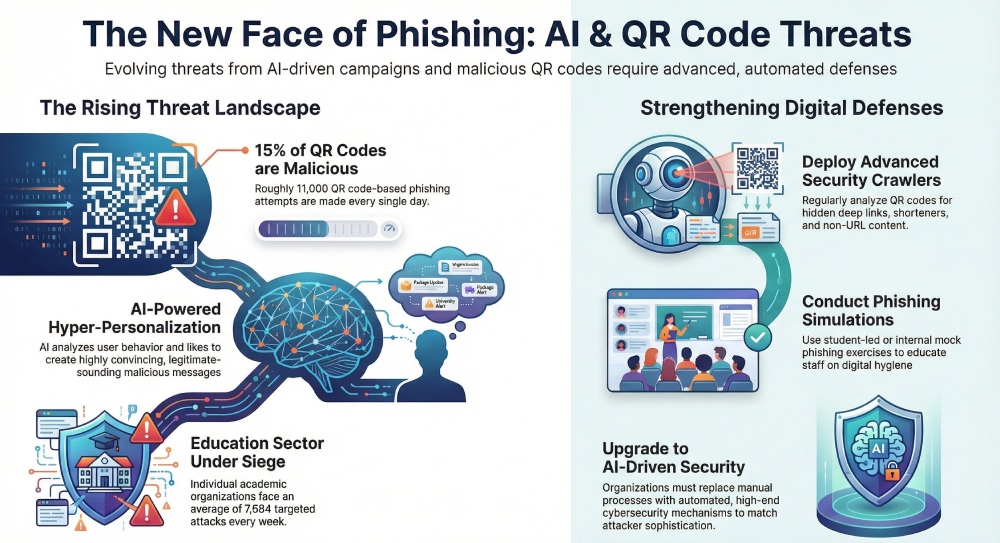
Think twice before scanning that QR code next time! QR codes have become popular since the advent of the pandemic. They have easily penetrated into our daily lives. But experts suggest using QR codes with extra caution, as phishing actors have started to abuse QR codes for their malicious intentions.

As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
On average, out of 75,000 QR codes, 15% are associated with malicious links. This means a whopping 11,000 QR code-based phishing attempts are being made on a daily basis.
Today, threat actors use multiple strategies and tactics to evade detection and security controls. Some of the common tricks that they use involve QR code shorteners, direct app file downloads, and in-app deep links. These are not the simple QR code scanning-based threat attacks. Rather, the evolution of attack strategies hints at the sophistication, intelligence, and adaptability of the phishing actors.
**Cybersecurity experts recommend regular analysis of QR codes on different websites. These can be done with the help of security crawlers and similar
security solutions
. Also, different QR code detection techniques, such as deep links, standard HTTPS URLs, and Non-URL content, can be used to understand the different types of data stored in QR codes.

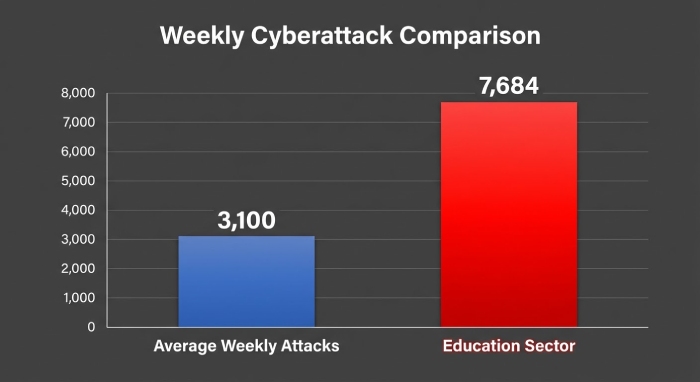
**The Indian education sector is facing 3,100 threat attacks per week India has a mind-boggling 950 million active users on the internet. At the same time, the South Asian nation is experiencing a spike in digital crimes. Experts believe that gen AI is further fueling the situation of crisis as more and more threat actors are getting sophisticated with their threat campaigns.
Areport suggests that India is experiencing **3,100 weekly threat attacks, which is 2% higher than last year. The worst-hit sector in India currently is the educational sector. Each academic organization is being targeted as many as **7684 times every week! Apart from the educational sector, business entities and government organizations are also being targeted by threat actors.
The VP of Research at Check Point, Lotem Finkelstein, believes that artificial intelligence is tremendously improving the game for the threat actors. AI not just helps them to boost the volume of the work, but it also enables them to transition from manual processes to high-end automations.
AI-backed phishing attacks spiked in 2025! Cybersecurity experts have noticed a significant spike in AI-powered phishing attacks that have the ability to bring a paradigm shift in the cyber fraud landscape. Conventional phishing tactics are no longer relevant. So cybercrooks use high-end, sophisticated AI-backed phishing tactics to evade security systems.
The reason for the increased success rate of AI-powered phishing attacks is the deep analysis of the target’s likes and dislikes, online behavior, and other factors. The same data is then leveraged to come up with hyper-personalized emails, voice calls, or text messages. These malicious messages and emails sound legitimate and safe .
Enterprises are required to analyze and upgrade their current cybersecurity mechanisms. From base-level employees to top-level executives, teams must be trained around basic digital hygiene and intricate cybersecurity mechanisms. Deploying apt cybersecurity setups and using AI tools cautiously can also help **safeguard your data **against AI-backed, sophisticated phishing campaigns.
Cybersecurity experts are urging organizations to **strengthen email security by properly implementing DMARC, DKIM, and SPF protocols to combat rising phishing and spoofing attacks worldwide.
Teachers duped by students, but with good intentions! 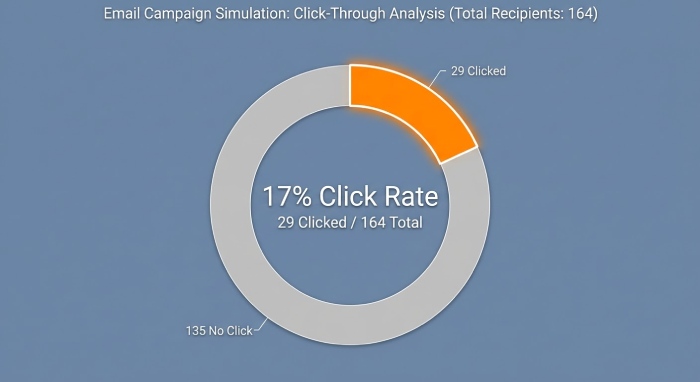
164 employees of the Eminence Independent School received malicious emails. Each of these emails looked urgent, genuine, and coming from an official source an educational institution based in a rural Kentucky district. The emails consisted of two very short, generic paragraphs that asked the staff to click on a link and acknowledge the latest guidelines. Out of the 164 recipients, **29 employees fell prey to the trap. When they clicked the allegedly malicious link, they were redirected to a page signed by the school’s students. The page informed employees that they had fallen victim to a malicious email.
The page also stated that these emails were sent to “inform people about the dangers of phishing and ways to avoid losing their personal information.” The page promised the recipients that more information would be shared in the upcoming days.
This was an assignment designed by Jennifer Gilbert, the school librarian, to educate school staff and students about phishing attacks. **Gilbert believes that basic cybersecurity lessons are non-negotiable in today’s time.
Sources
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.