Steakhouse Financial Attacked, Indian Infrastructure Targeted, MEA Shipment Scams

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Steakhouse Financial Attacked, Indian Infrastructure Targeted, MEA Shipment Scams
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Steakhouse Financial Attacked, Indian Infrastructure Targeted, MEA Shipment Scams
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-41017">
<source src="https://media.mailhop.org/dmarcreport/images/2026/04/Steakhouse-Financial-Attacked-Indian-Infrastructure-Targeted-MEA-Shipment-Scams.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M11S">2:11</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-41017" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-41017" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-41017" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-41017" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/steakhouse-financial-attacked-indian-infrastructure-targeted-mea-shipment-scams/&t=Steakhouse Financial Attacked, Indian Infrastructure Targeted, MEA Shipment Scams" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/steakhouse-financial-attacked-indian-infrastructure-targeted-mea-shipment-scams/&url=Steakhouse Financial Attacked, Indian Infrastructure Targeted, MEA Shipment Scams" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2026/04/Steakhouse-Financial-Attacked-Indian-Infrastructure-Targeted-MEA-Shipment-Scams.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/steakhouse-financial-attacked-indian-infrastructure-targeted-mea-shipment-scams/" class="input-link input-link-41017" title="Episode URL" readonly />
<button class="copy-link copy-link-41017" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-41017” readonly/>
<button class="copy-embed copy-embed-41017" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Here are the top 4 cyber incidents from last week that every cyber enthusiast must be aware of. Steakhouse Financial , a crypto platform, was targeted by threat actors. A steep spike in cybersecurity threats against critical **infrastructure systems **in India is evident. The MEA region is experiencing a rise in fake shipment tracking scams. Meanwhile, the global healthcare industry is on the radar of cybercrooks and is looking forward to the deployment of stringent rules.
Steakhouse Financial targeted by threat actors!

One of the popular crypto platforms, Steakhouse Financial, fell prey to a phishing attack on March 30. They informed the users about the cyber mishap. It was a phishing attack that successfully targeted the Steakhouse Financial frontend.
They issued a statement on X urging Steakhouse users to “not interact with the Steakhouse app until further notice.”
Team Steakhouse has also clarified that the cyberattack did not affect any user deposits or smart contracts. The cyberattack was strictly limited to the frontend interface of Steakhouse Financial. However, this can be bad news for users, because the frontend is essentially the user interface layer. This implies that threat actors can try to compel users into signing malicious financial transactions.
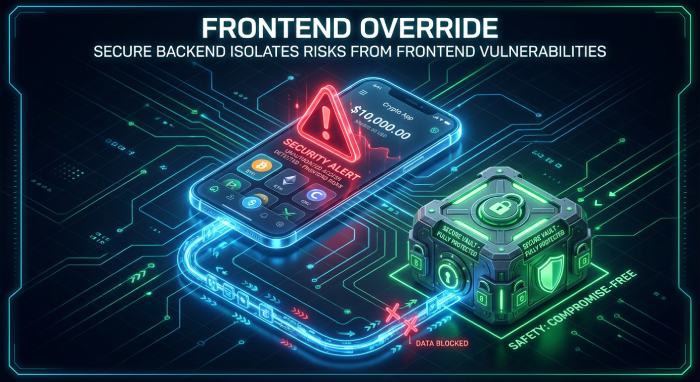
Blockaid, a reputed Blockchain security provider, detected the threat attack on Steakhouse Financial.Blockaid believes that this attack will majorly affect new users of Steakhouse who proceed to interact with the compromised user interface. So, existing deposits may not be at risk currently.
Steakhouse Financial is working closely with authorities and experts, and soon the **front-end interface will be restored after eliminating the malicious code. Users have been requested to wait until an all-clear notice is issued by the crypto platform.
Indian critical infrastructure on the radar of cybercrooks!
_Crucial infrastructural systems in India, like telecom networks, energy utilities, and financial institutions, are on the radar of threat actors. _The Reserve Bank of India, Indian Computer Emergency Response Team (CERT- In), the defence ministry, and Securities and Exchange Board of India have issued advisories for these sectors.
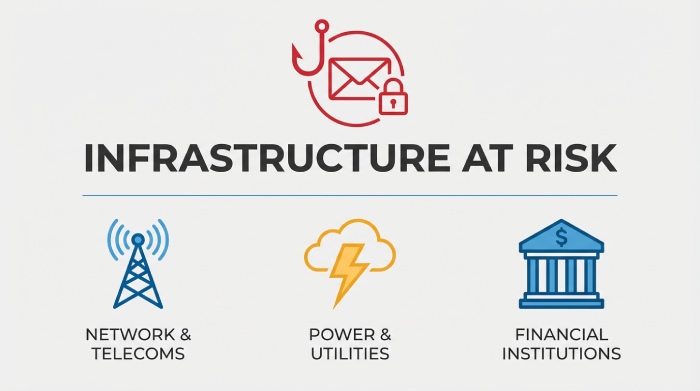
**Nation-state actors in Russia, Europe, Southeast Asia, etc., need a consistent supply of data to carry out malicious activities like blackmail. Indian infrastructure is increasingly becoming a favorite pick among hacktivist groups.
What’s most concerning is the fact that the phishing emails closely resemble genuine communications from military departments and ministries. In case malware gets into the system and infects it, everything gets compromised- from policy drafts to messaging data.
**Sundareshwar Krishnamurthy from PwC India states that the evolving threat landscape in India is actually becoming a cause of concern for Indian infrastructure and the related enterprises.
Not only India, but APT or Advanced Persistent Threat groups are also taking a keen interest in other nations like Ukraine, Algeria, Mongolia, and even the US. Recently, a group called **Handala managed to break into the personal email of the FBI’s director, Kash Patel, and leaked his personal photographs.
False shipment tracking scams across the MEA region

Group IB , the cybersecurity firm, has detected a steep spike in false shipment-tracking scams across the Middle East and Africa. This is an ongoing phishing campaign that targets buyers by abusing parcel tracking messages and delivery notifications.
The campaign has been active since December 2025, and so far, it has affected South Africa and Egypt the most. Threat actors have been using phishing-as-a-service platforms to carry out large-scale attacks. They send malicious tracking links to gain access to the **financial and personal data of consumers who are expecting parcel delivery.
**Logistics operators are recommended to implement DMARC, DKIM, and SPF to eliminate email spoofing risks. Companies must come up with verification tools on their official platforms that enable consumers to cross-check the delivery tracking numbers and other associated details.
GhostSocks allow threat actors to go into stealth mode!
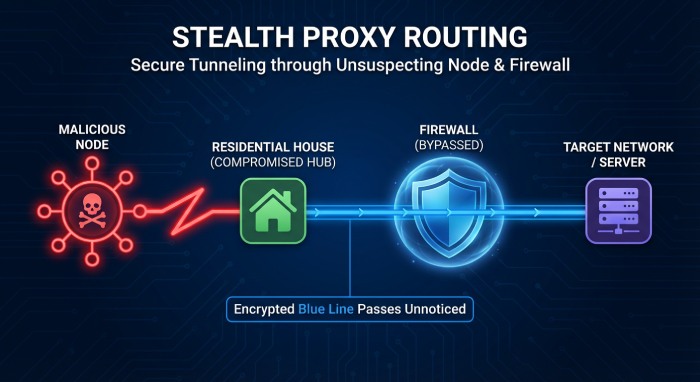
A new malware, GhostSocks, is slowly penetrating into the cybersecurity landscape. It helps threat actors to successfully evade detection. GhostSocks does so by turning the compromised systems into residential proxy nodes.
Residential proxies enable threat actors to carry out fraudulent activities through genuine home IP addresses. This detour creates the illusion that traffic originates from random users, thereby raising no suspicion against the threat actors.
With GhostSocks, cybercrooks can easily evade conventional IP-based detection mechanisms , anomaly detection tools, and geographic restrictions.
Researchers at Darktrace have revealed that threat actors have begun relying heavily on GhostSocks and Lumma Stealer to carry out stealthy cyberattacks.

With residential proxy abuse entering the mainstream attack landscape, enterprises can no longer stay lenient against cyberattacks. They need to be more proactive and ruthless. AI-backed defence mechanisms are required to identify any suspicious behavior or anomalies. **Traditional defence systems alone are no longer sufficient to combat modern threat attack mechanisms.

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.