US Cyber Weakened, China Implements Reporting, Volvo Hit Ransomware

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report US Cyber Weakened, China Implements Reporting, Volvo Hit Ransomware
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
US Cyber Weakened, China Implements Reporting, Volvo Hit Ransomware
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-32299">
<source src="https://media.mailhop.org/dmarcreport/images/2025/10/US-Cyber-Weakened-China-Implements-Reporting-Volvo-Hit-Ransomware.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M0S">2:00</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-32299" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-32299" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-32299" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-32299" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/us-cyber-weakened-china-implements-reporting-volvo-hit-ransomware/&t=US Cyber Weakened, China Implements Reporting, Volvo Hit Ransomware" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/us-cyber-weakened-china-implements-reporting-volvo-hit-ransomware/&url=US Cyber Weakened, China Implements Reporting, Volvo Hit Ransomware" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/10/US-Cyber-Weakened-China-Implements-Reporting-Volvo-Hit-Ransomware.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/us-cyber-weakened-china-implements-reporting-volvo-hit-ransomware/" class="input-link input-link-32299" title="Episode URL" readonly />
<button class="copy-link copy-link-32299" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-32299” readonly/>
<button class="copy-embed copy-embed-32299" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Hello cyber fam! It feels like 2025 started just a couple of months back, and now it’s already October. The cybercriminals are pulling up their socks to prepare for the upcoming festive rush. That’s exactly why we are here to “cyber” educate you so that you can enjoy Halloween, Thanksgiving, Christmas, and the New Year without any cyber mishap.
This week, we will talk about the ongoing US shutdown situation that’s affecting the USA’s cyber defense system. Next, we will focus on **China’s one-hour reporting rule for cyber incidents. Lastly, we will discuss the supply ransomware attack on Volvo’s employees.
Want to know the details? Stay with us!

The USA’s cyber defense mechanism has weakened because of the ongoing government shutdown!
The USA is going through a tough time as the US government shut down at 12:01 AM on Wednesday, October 1. The two major parties, Republicans and Democrats, have locked horns over issues like healthcare subsidies. They haven’t been able to agree on how much money to spend on different programs.
If the shutdown continues for a long time, the cybersecurity landscape will be worst hit. From disrupted critical cyber intelligence sharing to the mass termination of contractors and cybersecurity experts, the future of US cybersecurity appears bleak at present. The future of U.S. cybersecurity looks strong with increasing adoption of **authentication protocols like DMARC, DKIM, and SPF to combat phishing and email spoofing.

What makes things worse is the timing of the shutdown. The CISA 2015 Act has lapsed as the shutdown started. The key responsibility of CISA 2015 was to provide legal protection to organizations that shared critical threat intelligence for enhanced cyber protection. To renew the law, the shutdown must end. Additionally, US infrastructure and critical entities are currently vulnerable to cyberattacks. Cybersecurity experts, such as Crystal Morin, believe that CISA 2015 is non-negotiable when it comes to U.S. national security.
Mass layoffs at CISA will also bring down the agency’s productivity. From threat analysis and active support for **private sector partners to incident response, everything will slow down in the absence of a skilled workforce.

One-hour reporting rule implemented in China for cyber mishaps!
China is taking its **cybersecurity ecosystem quite seriously. Recently, it has imposed a one-hour reporting rule for all infrastructure providers across China. The rule will take effect on November 1, 2025. The Cyberspace Administration of China has published a notice that clearly explains all the reporting prerequisites. For a regular cyber incident, the affected network operators are required to report the incident within 60 minutes to the relevant ministry. But if it is a “major” cyber mishap, the victims are required to report the same in the next 30 minutes.
Things will become more complicated if the affected network operator is subject to specific industrial regulations. In that case, it should report the cyber mishap within the specified timeframe while complying with existing industrial regulations.
This newly imposed **60-minute reporting rule has made things difficult for the Chinese network operators. Any operator who fails to report within the given timeline will be punished. Additionally, those who attempt to conceal or manipulate the actual details will face severe consequences.
Volvo employees targeted by a supply ransomware attack!
A ransomware group has targeted Volvo Group North America. The data breach occurred due to a third-party **human resources software, Miljodata. Cybercriminals managed to breach the data of this Swedish SaaS company back in August. The cyber mishap affected multiple customers of Mijodata. Volvo NA was one of them.
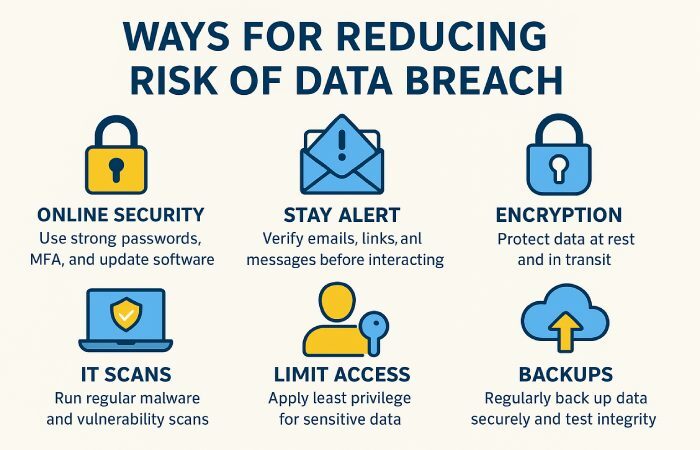
The ransomware gang didn’t interfere with Volvo NA’s systems. Yet they managed to gain access to highly sensitive data, including the names and Social Security Numbers of employees. It is highly likely that the stolen data has already been leaked on the Dark Web.
Miljodata has been working with 80% of Sweden’s municipal governments. One of its services includes Adato, a trademark platform that helps with easy tracking of employee sick leaves and rehabilitations.
The DataCarry ransomware group successfully breached the network of **Miljodata on August 20. Miljodata became aware of the cyber incident 3 days after the attack. The group of cybercrooks demanded a ransom of $165,000 or 1.5 Bitcoins. While Miljodata was still considering its next steps, DataCarry threatened the SaaS company that it would publish all the stolen data on the Dark Web. When they did not get the preferred response from Miljodata, they leaked the data online.
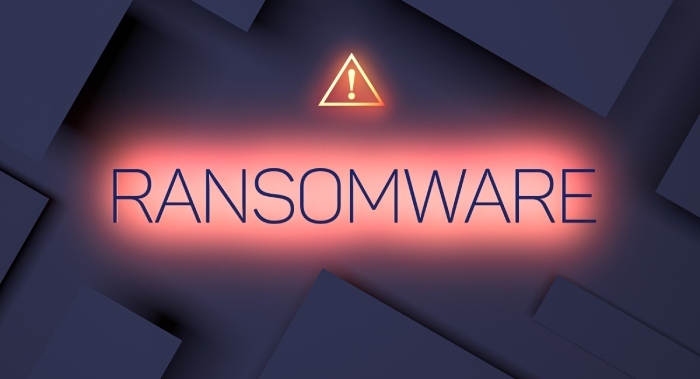
According to experts, the ransomware attack on Miljodata and its customers is “among the most disruptive to strike Sweden’s public sector in years.”
A similar incident occurred with two other major vehicle manufacturing companies, weeks after the Volvo NA cyberattack. _The ShinyHunters group successfully targeted Stellantis, the parent company of various consumer vehicle brands, including Jeep, Chrysler, Dodge, and Maserati. _The group of threat actors claims to have stolen sensitive information, including customer contact details and names. **Jaguar Land Rover also got attacked on August 31 by Scattered Lapsus$ Hunters.
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.