Browser ransomware threat, Interpol arrests 306, Password hacking escalates

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Browser ransomware threat, Interpol arrests 306, Password hacking escalates
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Browser ransomware threat, Interpol arrests 306, Password hacking escalates
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-23317">
<source src="https://media.mailhop.org/dmarcreport/images/2025/04/Browser-ransomware-threat-Interpol-arrests-306-Password-hacking-escalates.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M23S">2:23</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-23317" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-23317" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-23317" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-23317" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/browser-ransomware-threat-interpol-arrests-306-password-hacking-escalates/&t=Browser ransomware threat, Interpol arrests 306, Password hacking escalates" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/browser-ransomware-threat-interpol-arrests-306-password-hacking-escalates/&url=Browser ransomware threat, Interpol arrests 306, Password hacking escalates" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/04/Browser-ransomware-threat-Interpol-arrests-306-Password-hacking-escalates.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/browser-ransomware-threat-interpol-arrests-306-password-hacking-escalates/" class="input-link input-link-23317" title="Episode URL" readonly />
<button class="copy-link copy-link-23317" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-23317” readonly/>
<button class="copy-embed copy-embed-23317" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Hello people! It’s the first week of Q2, and we are here to welcome you with a fresh dose of cyber news. Educate yourself about the latest trends in the cybersecurity world and **safeguard your data in the digital arena. Only when you know the cyber world from the inside out will you be able to stay away from the malicious advances of cybercriminals.
Today, we will talk about browser-native ransomware emerging as the next big threat trend. Next we will discuss Interpol’s operation to crack down on cross-border cybercrime. Lastly, our focus will be on the latest buzz in the cybersecurity landscape - the password hacking machine.
**Scroll down and jump straight to the cyber details!
Browser-native ransomware- The emerging cyber threat!
Ransomware attacks have recently emerged as one of the most popular forms of cyber threats. Over the last 5 years, ransomware attacks have resulted in losses worth $276 billion. The traditional norm is to target devices as most of the data gets stored in those devices only. However, with new technologies such as **cloud storage and SaaS (Software as a Service) solutions, the conventional data storage system has gone through a major shift.
Now, a huge chunk of **organizational data is stored as well as shared through browsers. Since cyberattackers love staying updated with the latest technology, they have finally come up with a browser-native malware tactic to gain unauthorized access to cloud-based data.
Browser-native ransomware can be too hard to detect. Besides, it easily evades detection because its work process that does not require any file downloads. Threat actors are, therefore, gradually shifting to browser-native attacks.

Experts believe that, as of now, hackers are in the process of figuring out the right “ingredients” for carrying out browser-native ransomware. They may soon connect all the dots, find the missing pieces, and come up with full-fledged, large-scale browser-native ransomware campaigns.
Interpol busts cross-border cybercrime, arrests as many as 306 suspects!
Interpol has carried out a massive cyber hunt called **Red Card across seven African countries and ended up arresting 306 cyber suspects. It managed to confiscate 1842 devices. Operation Red Card was carried out over a time span of three months- November 2024 to February 2025. Interpol worked with local authorities to “disrupt and dismantle cross-border criminal networks which cause significant harm to individuals and businesses.”
This time, **Interpol focused closely on investment, banking, and messaging app cyber scams. These scams have so far affected a staggering 5000 users. Most of these victims are from nations like India, Canada, Malaysia, Bangladesh, Singapore, Pakistan, the US, and Thailand.The scammers used to coerce them into paying ransom amounts by threatening to leak sensitive data on the dark web.
Operation Red Card was carried out across Benin, Nigeria, Rwanda, Togo, Cote d’Ivoire, Zambia, and South Africa. Interpol’s director, Neal Jetton, is extremely happy with the success of Operation Red Card. The way international agencies worked hand in hand is testament to the fact that **international cooperation can disrupt and destroy cross-border cybercrime completely.
While the Nigerian police managed to arrest 130 suspects, the **South African authorities arrested 40 people and seized over 1000 SIM cards. Similarly, Namibian police caught hold of 14 suspects. Rwandan police arrested 45 cyber suspects and seized almost 300 devices.
Just before launching Operation Red Card, **Interpol also partnered with the African Development Bank Group with the core purpose of fighting financial crimes, corruption, money laundering instances and cyber frauds across Africa.
Get over passwords as an automatic password hacking machine just entered the scene!
Are you still relying on just passwords to secure your digital accounts? Then you need to read this!
Atlantis AIO is a high-end hacking tool that uses stolen data to gain unauthorized access to accounts across 140 platforms. These platforms include financial institutions, email services, and streaming platforms. Basically, hackers are **using automated bots to come up with the right passwords and thereby bypass security mechanisms.
Cybersecurity experts warn that threat actors are now using sophisticated hijacking tactics to penetrate into 2FA security setups. If they manage to steal active session cookies, then they no longer require security codes or passwords. DMARC, DKIM, and SPF are essential email authentication protocols that help prevent phishing and spoofing, while cybersecurity measures like 2FA security setups add an extra layer of protection by requiring multiple forms of verification to access sensitive accounts.
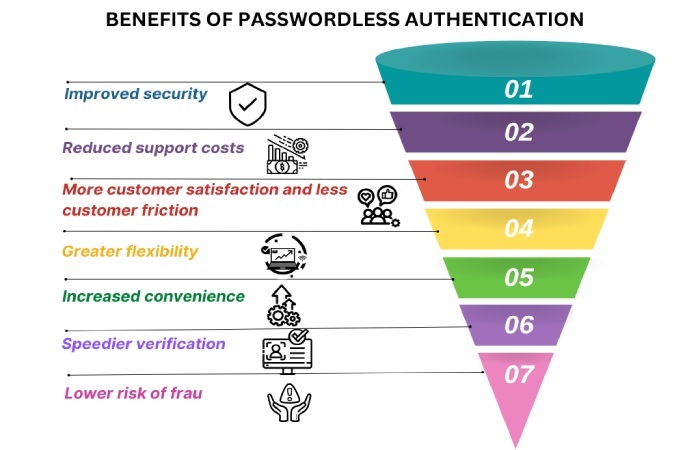
As a result, some of the biggest tech companies are gradually moving toward a passwordless future. Microsoft, too, is transitioning to passwordless authentication by April 2025. Apple and Google, too, are now encouraging passkey usage.
As cyberattacks are getting sophisticated with every passing day, experts urge users to take prompt actions toward creating a secure and safe digital presence. They recommend safe practices such as deploying MFA or multi-factor authentication systems, creating strong, unique combination passwords, and transitioning to passkeys. Staying well-prepared and anticipating potential cyberattacks can also be a significant move towards preventing threat attacks.

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.