Major Cybersecurity Trends That Will Reign in 2024

Quick Answer
Gartner projected global cybersecurity spending of $215 billion in 2024, a 14.3 percent jump from 2023, against a backdrop of AI-enabled attacks, cloud and IoT exposure, and state-sponsored campaigns. The article frames AI as both an attacker tool (deepfakes, voice cloning, AI-driven malware) and a defender capability (real-time anomaly detection, smarter authentication), and points to SPF, DKIM, and DMARC as the email-security baseline. Other 2024 themes include the security-team shift toward automation, more sophisticated ransomware, and a broader move from prevention-only thinking toward cyber resilience.


The email authentication landscape changed permanently in 2024, says Brad Slavin, General Manager of DuoCircle. Google, Yahoo, and now Microsoft all require DMARC. What used to be a best practice is now a hard prerequisite for reaching inboxes. Organizations that delayed are now paying the price in deliverability.
DMARC Report
Major Cybersecurity Trends That Will Reign in 2024
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-11285">
<source src="https://media.mailhop.org/dmarcreport/images/2024/02/Major-Cybersecurity-Trends-That-Will-Reign-in-2024.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M29S">2:29</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-11285" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-11285" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-11285" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-11285" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/major-cybersecurity-trends-that-will-reign-in-2024/&t=Major Cybersecurity Trends That Will Reign in 2024" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/major-cybersecurity-trends-that-will-reign-in-2024/&url=Major Cybersecurity Trends That Will Reign in 2024" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/02/Major-Cybersecurity-Trends-That-Will-Reign-in-2024.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/major-cybersecurity-trends-that-will-reign-in-2024/" class="input-link input-link-11285" title="Episode URL" readonly />
<button class="copy-link copy-link-11285" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-11285” readonly/>
<button class="copy-embed copy-embed-11285" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
2023 was a testament to the relentless advancement of cyber threats, as we witnessed a wave of sophisticated attacks ranging from damaging phishing scams to complex ransomware operations. And to think that dealing with the wrath of these attacks would have been easy is a mistake! Keeping the business up and running , protecting sensitive information, and keeping systems going is hard enough; add to this a layer of complexity - doing all of it in the face of grave cybersecurity attacks.
The struggle does not end here! Even though we have entered 2024, to expect even a fleeting moment of respite from these attacks would be juvenile on our part. This has necessitated organizations to pull up their socks and step up their cybersecurity game. According to a report by Gartner, cybersecurity spending is set to hit $215 billion in 2024. That’s a **14.3% jump from the estimated $188.1 billion spent in 2023 !
Wondering what the cybersecurity landscape will look like in 2024? Through this article, we’ll take you through the **key trends of 2024 and better prepare you to tackle the blow with confidence.
The Rise of AI
There’s been enough talk about AI, both about what’s good and bad. Things aren’t any different when it comes to cybersecurity. AI is like a double-edged sword. On one side, AI is leveraged by cybercriminals to launch more sophisticated attacks. Nowadays, they’re leveraging AI to generate deepfakes and AI-generated voice and video simulations, not to mention AI-driven malware. The real catch is that these tactics usually go undetected until it’s too late.
Well, when it comes to responding to these attacks, the security teams realize that they cannot afford to be complacent. They’re also tapping into AI’s potential to fortify defenses, utilizing real-time anomaly detection, intelligent authentication methods, and more. These authentication methods, particularly in the context of email, include techniques like Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting & Conformance (DMARC).
Security Loopholes in Cloud Infrastructure
It’s 2024! It’s officially the era of cloud solutions. Over the years, the cloud has taken precedence over all other data storage and processing solutions - it has transformed the way we interact and process data. Did we mention that it has also transformed the way cybercriminals interact with your data?
This means in 2024, the task of securing our cloud environments will become far more complex than it already is. This is not to say that the shift to the cloud is riddled with challenges, but it means that you’ll have to be all the more careful about protecting your sensitive data from the prying eyes of cybercriminals. Seems a bit overwhelming? A good starting point involves **adopting advanced security solutions and policies such as real-time threat detection and conducting regular security assessments and audits.
The Interconnectedness of Devices Presents a Challenge
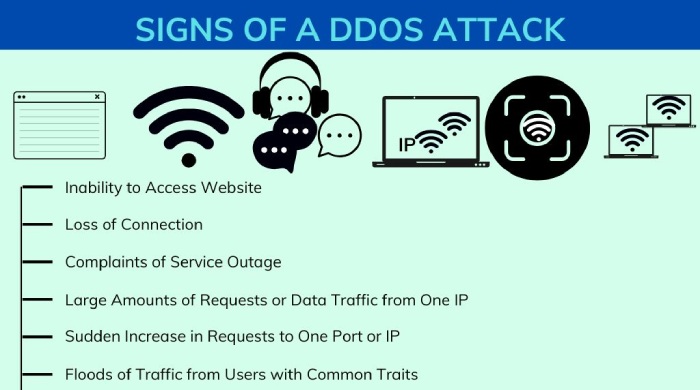
Take a moment and glance around; you’ll see how gadgets and devices are more than just tools - they’re practically extensions of ourselves. Well, these devices have not only made our lives simpler but also that of cyberattackers. After all, each device serves as a gateway through which these unwanted guests might enter and cause trouble. It’s not just about someone peeking into your personal life; the ripple effects can be massive. They can go as far as dreaded DDoS attacks.
Security Teams will Prioritize Automation
As you know, cybercriminals are getting craftier with their approach. This means it’s time for organizations to step up and take proactive measures to protect their digital infrastructure. Thanks to automation, keeping up with cybercriminals and outpacing them has now become easier. Automation offers a solution by enabling rapid, real-time analysis and response. This not only speeds up the detection of threats but also enhances the accuracy of identifying potential dangers. Going forward in 2024, automation will become a norm and a formidable force in tackling malicious cyberattacks.
Ransomware Attacks will be at an All-Time High
Heading into 2024, it looks like we’re in for a tougher battle against ransomware attacks. But ransomware attacks of today aren’t your typical attacks. Thanks to cybercriminals using AI and machine learning to find new loopholes and avoid getting caught, they’re getting more innovative, more sophisticated, and more capable of causing significant financial and operational damage. The complexity and intelligence of these threats require a more dynamic and proactive approach to cybersecurity.
State-Sponsored Cyber Warfare Will Prevail
Think you can keep the worlds of geopolitics and cybersecurity neatly apart? It turns out that these two domains are more intertwined than it ever was! These days, governments are turning into a new kind of battlefield - the digital space. In an attempt to take down the other party, the governments are **launching attacks that target crucial infrastructure, swipe sensitive data, and peek into other countries’ secrets. These state-backed hackers are using tricks like phishing - that’s when they send fake emails to get inside systems for spying or causing trouble - and DDoS attacks.
Strengthening Security with Enhanced Awareness
Building a sound security posture takes more than just deploying the latest technological tools and strategies. It requires creating a culture where every team member feels responsible for the digital safety of the organization. This is an important aspect of safeguarding your digital infrastructure as it empowers teams with the knowledge and tools necessary to recognize and mitigate risks. While it might seem like a small effort on each individual’s part, it is certainly not insignificant.

The Era of Cyber Resilience
Up until now, the primary motive of organizations was to prevent cyberattacks before they happen. However, in 2024, the narrative is expanding, and the organizations are now focusing on not only preventing but also ensuring robust protection of sensitive data and maintaining **business integrity through comprehensive cyber resilience.
From what it looks like, 2024 will be a year of more sophisticated attacks. But this does not mean that organizations will simply surrender. The good news is that in 2024, we will also see a shift from reactive defense mechanisms to a more dynamic, proactive posture. Are you ready to face what the year ahead has in store for us? If not, it’s high time you take matters into your own hands. Get in touch with our team of **experts at DMARCReport today!
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.