QR Code Phishing or Quishing is on the Rise; Here’s How You Can Prevent it

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report QR Code Phishing or Quishing is on the Rise; Here’s How You Can Prevent it


The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
QR Code Phishing or Quishing is on the Rise; Here’s How You Can Prevent it
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-11322">
<source src="https://media.mailhop.org/dmarcreport/images/2024/02/QR-Code-Phishing-or-Quishing.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M3S">2:03</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-11322" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-11322" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-11322" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-11322" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/qr-code-phishing-or-quishing-is-on-the-rise-heres-how-you-can-prevent-it/&t=QR Code Phishing or Quishing is on the Rise; Here’s How You Can Prevent it" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/qr-code-phishing-or-quishing-is-on-the-rise-heres-how-you-can-prevent-it/&url=QR Code Phishing or Quishing is on the Rise; Here’s How You Can Prevent it" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/02/QR-Code-Phishing-or-Quishing.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/qr-code-phishing-or-quishing-is-on-the-rise-heres-how-you-can-prevent-it/" class="input-link input-link-11322" title="Episode URL" readonly />
<button class="copy-link copy-link-11322" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-11322” readonly/>
<button class="copy-embed copy-embed-11322" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
QR codes are seen everywhere for directing users to URLs with a tap; and just as every coin has two slides, these **Quick Response codes are also being used negatively. In fact, in May 2023, a U.S.-based energy firm encountered nearly 29% of more than 1000 malicious emails containing QR codes.
Adversaries are developing newer and more sophisticated strategies involving QR codes in their phishing strategies to acquire credentials and personal details, trick victims into paying off hackers, install malware, gain remote access to devices, etc.
Now, this blog walks you through quishing, how it works, ways to **stay protected against it, and more.
What is Quishing?
Quishing is a relatively new term in the cybersecurity dictionary. It’s short for QR and phishing, which indicates phishing attacks involving the exploitation of QR codes.
QR codes are two-dimensional barcodes that store information, often scanned using smartphones to access data or websites quickly. They were invented by **Masahiro Hara and a team at Denso Wave, a subsidiary of Toyota, in 1994 to track automotive parts .
Off lately, phishing experts have been using QR codes to direct victims into visiting websites containing malware or designed to harvest credentials. These code images circumvent security controls and commonly evade link filters, proving to be more harmful than other phishing methods.
Amid the pandemic, service providers increasingly embraced QR codes to keep their businesses up and running while adhering to social distancing guidelines. That’s why users have become accustomed to scanning QR codes. It’s expected that 99.5 million users in the US will use their phones for QR code scanning by 2025, while 59% believe QR code scanning will be a lasting aspect of their phone usage in the future.
How Quishing Works
Quishing works pretty much like phishing, not to forget it’s anyway a type of phishing only.
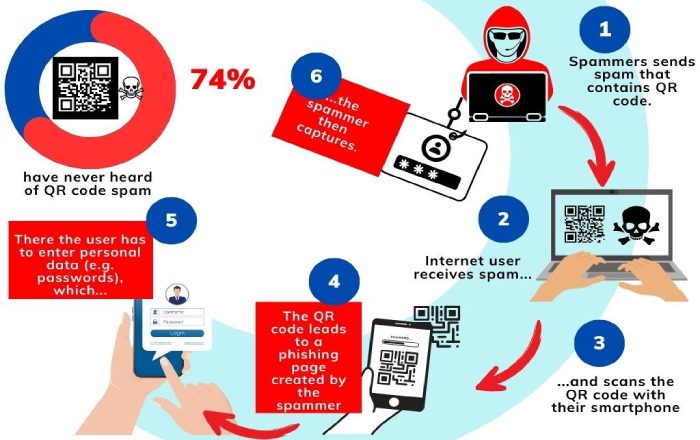
In most cases, these QR codes are part of sophisticated phishing emails sent from impersonated senders (typically trusted sources like relatives, friends, colleagues, banks, reputed businesses, etc.), requesting recipients to scan QR codes and **take quick action in favor of adversaries.
Since it takes no time to create QR codes, hackers don’t reuse them, making it unlikely for secure email gateways to catch and blocklist them. This is also why legitimate businesses should rely on QR code tracking to monitor scan behavior, detect anomalies early, and reduce the risk of malicious misuse. On the downside, quishing isn’t yet a very talked-about topic in cybersecurity training sessions, online articles, news, etc., making it an alluring option for bad actors.
Common targets of QR code phishing are businesses and infrastructures holding financial and personal details. Even individuals aren’t safe; hackers victimize users on Amazon, LinkedIn, Wells Fargo, and similar online platforms . People are highly likely to fall for the trap on such platforms as they trust them and have been using them for a long time.
Real-Life Quishing Scam
In 2022, a quishing campaign was launched impersonating the Chinese Ministry of Finance in emails faking a new government grant. The emails prompted recipients to scan a QR code using WeChat, leading them to an application page asking for credit card and bank account details.
However, it’s still unclear if the details were misused for making **fraudulent transactions or if the data was sold to someone. But no matter what, a large chunk of financial details was compromised.
How to Detect a Quishing Attempt?
Identifying red flags can help you **spot potential QR code phishing attacks. Here are some warning signs to look for:
Unsolicited QR Codes
Be cautious if you receive QR codes unexpectedly, primarily through unsolicited emails, messages, or social media. Legitimate entities usually do not send QR codes without prior context.
Additionally, consider learning how to make QR codes yourself, as this can help you understand how the data is encoded and increase your awareness of potential scams.

Unknown Sources
If the QR code comes from an unknown or untrusted source, think twice before scanning. Verify the legitimacy of the sender through other means before proceeding. This could be through phone calls, SMSes, or in-person meetings. Avoid taking confirmation over an email if the QR code is sent to you through an email itself; this is because the responder is more likely to be the hacker rather than the authorized person themselves.
Misspelled URLs or Domains
Check the URL embedded in the QR code for misspellings or variations of well-known domains. Phishers often use similar-looking URLs to deceive users. They deploy homoglyph techniques, which means using characters that look alike.
For example, the uppercase letter “I” (the 9th letter of the English alphabet series) and the lowercase letter “l” (the 12th letter of the English alphabet series) can appear **almost identical in some typefaces.
Overly Complex URLs
If the QR code contains a lengthy or complicated URL , it might be an attempt to confuse the destination. **Be wary of complex URLs that seem unnecessary.
Too Good to Be True Offers
QR codes promising incredible deals, discounts, or prizes may be phishing attempts. If it sounds too good to be true, it probably is.
Urgent or High-Pressure Tactics
Phishing attempts often use **urgency or pressure tactics to manipulate users into taking quick actions. Be suspicious of QR codes that claim immediate action is required. Some alarming phrases are: within 10 minutes, immediately, quickly, otherwise you’ll lose the deal, limited-time offer, your account requires immediate action, etc.
Mismatched Branding
**Check for inconsistencies in branding, logos, or design elements within the QR code. Genuine QR codes from reputable sources maintain consistent branding.
Requests for Personal Information
Avoid scanning QR codes that prompt you to provide sensitive information or grant excessive permissions. Legitimate sources typically don’t ask for such details through QR codes.
Lack of Encryption
Legitimate websites use encryption (https://) to secure data transmission. If the QR code directs you to a non-secure site (http://), it could be a phishing attempt.
Unusual QR Code Behavior
If the QR code leads to unexpected actions, such as downloading unknown apps or requesting excessive permissions, exercise caution and reconsider scanning.
Staying Safe
To stay safe from QR code phishing, verify the source, especially if it’s from strangers or offers enticing deals. Use reliable QR code readers, either built into smartphones or trusted third-party apps, to avoid malware risks. Preview the destination URL before scanning to prevent automatic malware downloads. _Be cautious when providing personal information after scanning, cross-check logos and URLs**, and prefer typing URLs manually_.
Apart from this, employing email authentication methods can also enhance security. Protocols such as SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting & Conformance) can verify a sender’s identity and prevent spoofing. These methods authenticate the **email sender’s domain and provide a layer of protection against quishing and other email-related threats.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.