Learning to find the source owner using the ‘envelope_to’ domain

Quick Answer
Learning to find the source owner using the ‘envelopeto’ domain Learning to find the source owner using the ‘envelopeto’ domain An ‘envelopeto’ domain is the domain in the recipient’s email address.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


The organizations that invest in email authentication early save themselves from expensive incidents later, says Vasile Diaconu, Operations Lead at DuoCircle. We see the pattern constantly: a domain gets spoofed, customers lose trust, and the remediation effort costs 10x what proactive DMARC setup would have cost.
DMARC Report
Learning to find the source owner using the ‘envelopeto’ domain
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-21293">
<source src="https://media.mailhop.org/dmarcreport/images/2025/02/Learning-to-find-the-source-owner-using-the-‘envelopeto-domain.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M19S">2:19</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-21293" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-21293" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-21293" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-21293" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/learning-to-find-the-source-owner-using-the-envelope_to-domain/&t=Learning to find the source owner using the ‘envelope_to’ domain" target="_blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/learning-to-find-the-source-owner-using-the-envelope_to-domain/&url=Learning to find the source owner using the ‘envelope_to’ domain" target="_blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/02/Learning-to-find-the-source-owner-using-the-‘envelope_to-domain.mp3" target="_blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/learning-to-find-the-source-owner-using-the-envelope_to-domain/" class="input-link input-link-21293" title="Episode URL" readonly />
<button class="copy-link copy-link-21293" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-21293” readonly/>
<button class="copy-embed copy-embed-21293" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
An ‘envelope_to’ domain is the domain in the recipient’s email address. This address can be used to understand how some of the legitimate emails are failing DMARC checks. If you are unsure about the troubleshooting methods, using the ‘envelope_to’ domain to find the source owner is a wise choice.
Using this technique, you get to know which third-party service providers are sending emails on your behalf and to whom. You can also trace incoming emails in your logs to know which employee is using which source to send official emails. If you spot an unauthorized source, you can take the requisite action before it becomes an exploitable vulnerability.
How to match sending sources with internal records?
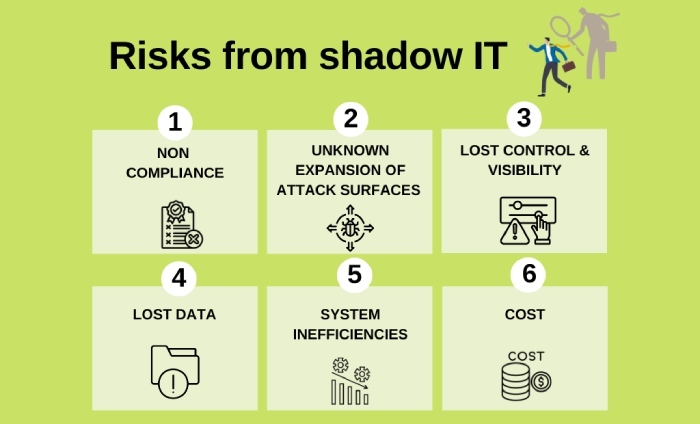
It’s important that you compare the sending sources with the internal records so that you know about the use of shadow IT and unauthorized mail servers being used in your company. This practice also helps bring misconfigurations to the surface. Here’s how you can match and verify-
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
Check against the list of officially authorized senders
DMARC is based on SPF results, and for SPF deployment , you need to create and upload a **list of authorized senders on your DNS. So, pull out the same list and check if the sending sources align with your records. If you find any unauthorized source, investigate further.
Cross-check with internal email infrastructure
Verify that sending sources (IPs, domains) align with your organization’s email gateways, servers, and internal applications. If an email appears to originate from an internal department but is sent from an unrecognized server, it could signal spoofing or a configuration issue.
Correlate with employees or team activity
If an email is sent from your domain but the source isn’t authorized, consult your internal team. It could be an unauthorized sender, a former employee’s access still in use, or a misconfigured application unintentionally sending emails.
Discovering source owners strengthens email security

Detecting an unapproved sender while discovering source owners using the ‘envelopeto’ domain indicates some misconfigurations or security gaps. Pay immediate attention to these so that a threat actor can’t exploit them to send phishing and spoofing emails on your behalf. Always opt-in to receive RUA and RUF reports, as they provide insights into your email activities , helping SPF, DKIM, and DMARC be highly efficient in securing emails.
If you monitor DMARC reports properly, you will also know if your DMARC record requires any adjustments in the policy-
-
The ‘none’ policy instructs the receiving server to take no action against emails that failed the DMARC checks. Such emails are treated normally.
-
The **‘quarantine’ policy instructs the receiving server to place such emails in the spam folder and treat them with caution because they are potentially risky.
-
The ‘reject’ policy instructs the receiving server to outrightly reject the entry of emails that don’t pass the authentication checks. Such emails bounce back to the sender, making **p=reject the strictest policy .
Also, with proper DMARC management, you stay compliant with industry standards, including GDPR, DORA, and HIPAA.
Sources
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.