Cybersecurity threatens water, Android users warned, Mexico faces cyberattacks

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Cybersecurity Threatens Water, Android Users Warned, Mexico Faces Cyberattacks
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Cybersecurity Threatens Water, Android Users Warned, Mexico Faces Cyberattacks
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-18670">
<source src="https://media.mailhop.org/dmarcreport/images/2024/11/Cybersecurity-Threatens-Water-Android-Users-Warned-Mexico-Faces-Cyberattacks.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M1S">2:01</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-18670" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-18670" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-18670" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-18670" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/cybersecurity-threatens-water-android-users-warned-mexico-faces-cyberattacks/&t=Cybersecurity Threatens Water, Android Users Warned, Mexico Faces Cyberattacks" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/cybersecurity-threatens-water-android-users-warned-mexico-faces-cyberattacks/&url=Cybersecurity Threatens Water, Android Users Warned, Mexico Faces Cyberattacks" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/11/Cybersecurity-Threatens-Water-Android-Users-Warned-Mexico-Faces-Cyberattacks.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/cybersecurity-threatens-water-android-users-warned-mexico-faces-cyberattacks/" class="input-link input-link-18670" title="Episode URL" readonly />
<button class="copy-link copy-link-18670" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-18670” readonly/>
<button class="copy-embed copy-embed-18670" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
It’s already week four of November, and the holidays are just around the corner. Leniency at workplaces is already resulting in increased cases of cyberattacks. Before you get too busy with vacation plans and late-night parties with your loved ones, here’s a gentle reminder from our side that your data needs **protection and deserves your complete attention. That’s why we bring this weekly bulletin to keep you enlightened about what’s ongoing in the world of cybersecurity.
Strengthen your organization’s defenses by implementing SPF, DKIM, and DMARC protocols to protect against email-based threats and ensure your communication channels remain secure From data breaches to new cybersecurity policies, there’s so much to learn about and implement into your daily life.
Today, we will talk about the water system risks in the US, the steep increase in cybersecurity cases in Mexico, as well as data leaks of Yakuza victims online.

Let’s get started!
US water systems at risk because of cybersecurity vulnerabilities
Cybersecurity attacks are increasingly targeting critical infrastructures across the globe. Currently, the US water systems are on the radar of threat actors. The water supply system of as many as 27 million Americans is under severe risk because of specific internet-facing vulnerabilities. More than 100 community water systems (CWS) have security weaknesses, and that’s exactly what makes them the soft targets of threat actors. An EPA (Environmental Protection Act) report indicates that around **1062 water systems have severe vulnerabilities that can impact a whopping 50,000 users if immediate mitigation steps are not taken.
Schools, hospitals, businesses, and households - people from all strata depend on these water systems**. **Experts believe if appropriate action is not taken at the right time, threat actors can cause irreparable damage to the water system infrastructure.

Two months back, the Arkansas City water treatment plant experienced a cyber incident, and as a result, it had to go offline and operate manually to prevent the extent of damage. On the other hand, 3 years ago, a hacker managed to target a Floridian water system. They altered the chemical composition of water. Fortunately, the alteration was detected before it was too late.
Such **unfortunate incidents are a glaring reminder of the sophistication and malicious intention of threat actors who are ready to target something as crucial as drinking water to make some quick and illegitimate money.
High-risk warning against Android users in India
It seems like Android users in India are no longer safe with their sensitive data, given that the Indian Computer Emergency Response Team has discovered severe vulnerabilities in the Android ecosystem. The warning is specifically addressed to those who are using Android 15. Cybersecurity experts believe that multiple vulnerabilities exist in the Android 15’s operating system. Threat actors can easily exploit these vulnerabilities and gain access to sensitive user data. The level of damage can range from illegitimate access to personal data, instability in the Android system, and complete denial of service.

CERT India has identified the vulnerability note
- CIVN-2024-0349. They believe that the vulnerabilities can impact all the operating systems ranging from Android 12 to Android 15. The CERT India has also stated that the vulnerabilities originate from components developed by third-party vendors like Qualcomm, Imagination Technologies, and MediaTek.
If threat actors manage to exploit the vulnerabilities, this can lead to instances of data breach. They can access your **corporate or personal data and misuse it for quick gains. Or, unauthorised access can lead to system instability, such as system crashes, thereby making your Android device non-usable. Threat actors can even disrupt the entire functionality of your Android device.

Experts have advised the users to update their devices as soon as Google and the respective OEMs release the updates. Meanwhile, Android users must download apps only from the Google Play Store. Also, it is better to use features such as two-factor authentication, app permissions and device encryption. They have also urged users to look out for signs of potential exploitation, such as excessive battery drain and frequent device crashes.
Mexico grappling with sudden increase in cyberattacks
Mexico accounts for around 50% of all the cyberattacks in Latin America. The threat actors are targeting both the public and private sector entities. The vulnerabilities in the country’s digital infrastructure are the biggest reason for this sudden increase in cyberattacks across Mexico. From identity theft to data breaches, threat actors are leaving no stone unturned to gain access to the sensitive data of Mexican people.
Mexico is currently focusing on its digital economy. Also, it embraces the latest technology across different sectors such as healthcare, banking, finance, and so on. With most of the services going online, Mexico is becoming a treasure trove of data for threat actors.
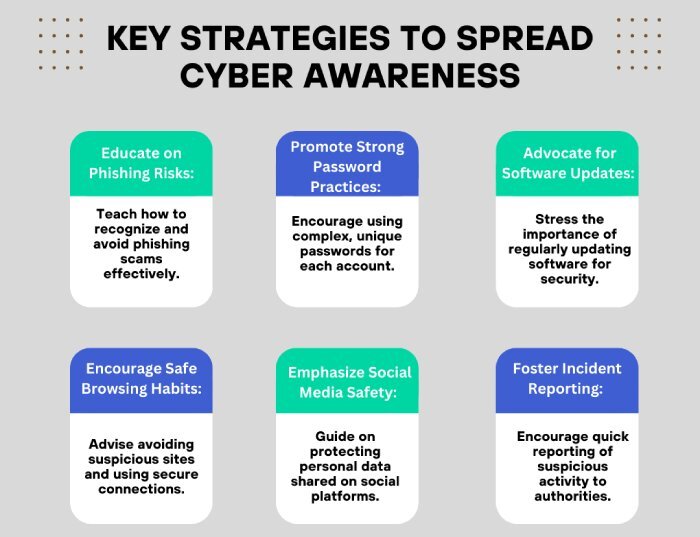
The need of the hour is to invest in cybersecurity mechanisms and **spread cyber awareness among Mexicans to bring this cyber invasion to a halt.

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.