Browser session hijacking, Email routing phishing, Instagram alert panic

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Browser session hijacking, Email routing phishing, Instagram alert panic
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Browser session hijacking, Email routing phishing, Instagram alert panic
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-37160">
<source src="https://media.mailhop.org/dmarcreport/images/2026/01/Browser-session-hijacking-Email-routing-phishing-Instagram-alert-panic.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M49S">2:49</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-37160" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-37160" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-37160" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-37160" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/browser-session-hijacking-email-routing-phishing-instagram-alert-panic/&t=Browser session hijacking, Email routing phishing, Instagram alert panic" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/browser-session-hijacking-email-routing-phishing-instagram-alert-panic/&url=Browser session hijacking, Email routing phishing, Instagram alert panic" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2026/01/Browser-session-hijacking-Email-routing-phishing-Instagram-alert-panic.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/browser-session-hijacking-email-routing-phishing-instagram-alert-panic/" class="input-link input-link-37160" title="Episode URL" readonly />
<button class="copy-link copy-link-37160" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-37160” readonly/>
<button class="copy-embed copy-embed-37160" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
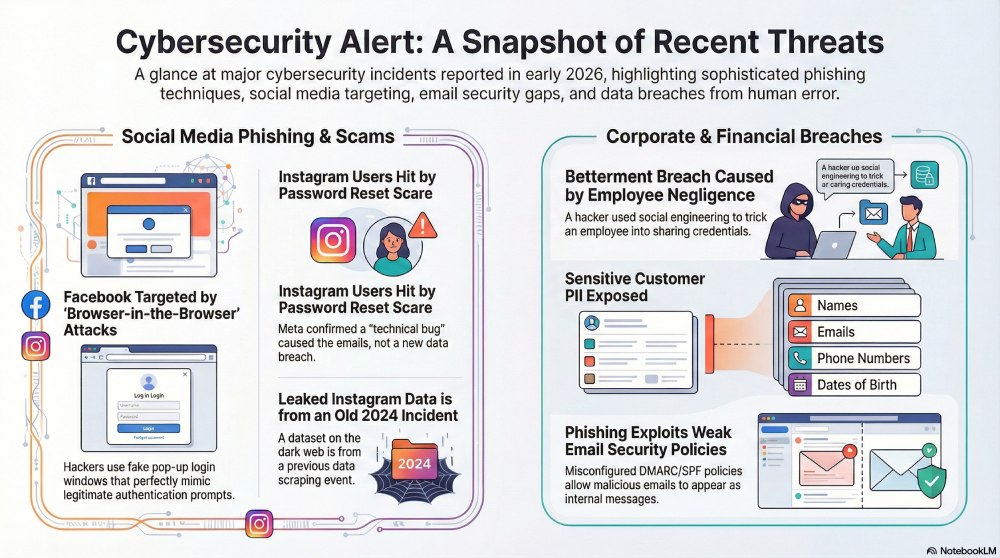
The third edition of the month revolves around key cybersecurity incidents. Cyber mishaps this week include a breach of Facebook login credentials, phishing attacks that exploit email routing gaps, fake Instagram password reset emails that sent a panic wave among the Indian user base, and a customer data breach at Betterment.
Facebook login credentials accessed by leveraging the Browser-in-the-Browser technique
Facebook has a huge user base of around 3 billion active users. This is exactly why hackers treat this social networking platform as a treasure trove of data. According to a group of cybersecurity researchers, the second half of 2025 experienced a sudden spike in Facebook phishing scams. Experts believe that the **“Browser-in-the-Browser” technique is being used to extract data at a large scale.

The Browser-in-the-Browser or **BitB technique is a highly sophisticated phishing tactic. The process involves creation of a custom-built, malicious login window that pops up on the target’s browser tab. It successfully mimics the original Facebook authentication prompts.
The false pop-up window consists of a Facebook URL, which makes it almost impossible even for proactive and wary users to set it apart from a legitimate Facebook page. Hackers send malicious emails while posing as the XYZ law firm. The phishing email talks about infringing content andlegal notices. Such emails often contain malicious URLs that redirect victims to malicious Meta captcha pages. This creates an added layer of deception and earns the credibility of the victim.

Microsoft urges users to stay wary of phishing attacks that abuse email routing gaps.
Cybercrooks are leveraging weak DMARC/SPF policies and misconfigured MX records to give an “internal” and credible appearance to malicious emails, as well as avoid detection by security tools.
The Threat Intelligence team at Microsoft has discovered that cybercriminals have been misusing intricate email routing and misconfigured domain protection systems.
The loophole lies with the recipient **email servers that interpret the incoming emails. Because of intricate email paths, DMARC enforcement and SPF hard-fail often do not work properly.In that case, a phishing email can easily reach the inbox of the target with an “own” address in both the From and To fields. This spoofed email successfully creates an illusion of the email being sent internally.

At other times, the hackers can sometimes alter the sender name to further boost the credibility of the email, while using a legitimate internal email address in the From field.
Experts suggest using stringent DMARC protocols and SPF hard fails. Further, it is important to set up all the legacy mail relays, spam filters, and archiving services correctly.
Instagram security alerts send shock waves among Indian users
Multiple Instagram users received Instagram password reset emails, triggering a fear of a mind-numbing data breach among the Indian user base. While Meta has denied the risk of a data breach and termed the incident a mere technical bug, the incident once again reminded users of the threat around these social networking apps.

Meanwhile, a leaked dataset is doing the rounds on darkweb. Meta claims that the leaked data is related to data scraping that most likely happened back in 2024. Malwarebytes, a renowned cybersecurity company, has found a spreadsheet on the dark web that contains data like Instagram usernames, addresses, phone numbers, emails, etc. Meta’s statement has made it clear that an external party leveraged a bug to send password reset emails to the users. However, no data breach took place.
Massive customer data breach at Bettermement due to an employee’s negligence!
Betterment has published a data breach notification on its official website . The notification states that a hacker managed to trick one of the employees into sharing their login credentials for a third-party software platform.
The cybercrook is yet unknown. It is highly likely that they have used the **identity impersonation technique to get access to the sensitive data. They chose social engineering tactics over attacking the technical infrastructure.
Betterment has mentioned that the cybercrooks have already started sending “fraudulent, crypto-related messages that appeared to come from Betterment.”
There has been no clarity yet around the number of people impacted in this cyber incident. Betterment has claimed that they take cybercrimes “very seriously” and that they have **managed to revoke **any kind of unauthorized access. A full-blown investigation is also underway.
Betterment has claimed that no customer accounts were breached as they are safeguarded “by multiple layers of security.”
However, the cybercrooks managed to gain access to highly sensitive personal data like email addresses, names, phone numbers, postal addresses, dates of birth, and so on.
Betterment has urged its customers to **stay careful and be wary of any unexpected communications.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.