Verified Email Threat, Costly Ransomware Attacks, Deepfake Audio Shock

Quick Answer
Verified Email Threat, Costly Ransomware Attacks, Deepfake Audio Shock Verified Email Threat, Costly Ransomware Attacks, Deepfake Audio Shock /! This file is auto-generated / !function(d,l){"use strict";l.querySelector&&d.addEventListener&&"undefined"!=typeof URL&&(d.wp=d.wp||{},d.wp.receiveEmbedMessage||(d.wp.receiveEmbedMessage=function(e){var t=e.data;if((t||t.secret||t.message||t.value)&&!/[^a-zA-Z0-9]/.test(t.secret)){for(var s,r,n,a=l.querySelectorAll('iframe[data-secret="'+t.secret+'"]'),o=l.querySelectorAll('blockquote[data-secret="'+t.secret+'"]'),c=new RegExp("^https?:$","i"),i=0;i ' title="Embed Code" class="input-embed input-embed-24028" readonly/> Hey people! Hope you all are safe and sound, away from the clutches of the cybercrooks.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
DMARC Report
Verified Email Threat, Costly Ransomware Attacks, Deepfake Audio Shock
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-24028">
<source src="https://media.mailhop.org/dmarcreport/images/2025/04/Verified-Email-Threat-Costly-Ransomware-Attacks-Deepfake-Audio-Shock.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M6S">2:06</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-24028" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-24028" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-24028" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-24028" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/verified-email-threat-costly-ransomware-attacks-deepfake-audio-shock/&t= Verified Email Threat, Costly Ransomware Attacks, Deepfake Audio Shock" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/verified-email-threat-costly-ransomware-attacks-deepfake-audio-shock/&url= Verified Email Threat, Costly Ransomware Attacks, Deepfake Audio Shock" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/04/Verified-Email-Threat-Costly-Ransomware-Attacks-Deepfake-Audio-Shock.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/verified-email-threat-costly-ransomware-attacks-deepfake-audio-shock/" class="input-link input-link-24028" title="Episode URL" readonly />
<button class="copy-link copy-link-24028" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-24028” readonly/>
<button class="copy-embed copy-embed-24028" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Hey people! Hope you all are safe and sound, away from the clutches of the cybercrooks.
It is week 4, and we are here with the 4th cyber bulletin of the month. This week, we will talk about the latest flaw in Google’s email system. Also, we will have a look at the expenses of ransomware attacks on banks. Lastly, we will talk about the intricacies of AI-generated deepfake voices.
Let’s not waste any time!
Scroll down and get started**.
Google warns Gmail users against malicious emails from verified IDs!
Gmail users, this one is for you!
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
Recently, Google has detected a flaw in its email system, because of which threat actors are trying to carry out phishing attacks even from verified emails. Google is currently working on the utmost priority to fix the issue.
These malicious emails are difficult to detect, as they appear to be originating from legitimate domains. Through these emails, the cyberattackers try to convince Gmail users to share their account credentials. While Google is trying to come up with an instant solution, the tech giant has urged Gmail users to stay vigilant .
Software developer Nick Johnson shared his experience on X. He received an email that seemed to be coming from “no-reply@google.com.” The link in that email claimed to take users to one of the Google support pages. However, Nick realized that this malicious link would direct users to a phishing site on “Google’s own platform.”
The concerning part is that this malicious email was able to go undetected despite email authentication checks such as SPF, DKIM, and DMARC. Also, the email was delivered within the same thread in which Gmail had been sending genuine security alerts. The phishing email campaign has been **designed to collect the user credentials and thereby gain complete access to Gmail accounts and other related data.

Google is currently working to find a quick and permanent fix for this issue. It has also urged Gmail users to go for two-factor authentication and leverage passkeys to bolster their email systems .
Ransomware attacks cost banks as much as $6.08 million, leading to severe downtime and reputational damage
**Global financial institutions are facing a staggering upsurge in ransomware attacks. As per a recent discovery, a single ransomware attack may cost a bank as much as $6.08 million on average. This excludes any charges that are required to bring in the cybersecurity upgrades and regulatory expenses.
Another major repercussion of ransomware attacks on financial organizations is operational downtime and reputational damage. Both lead to severe loss of credibility and customer trust. Also, in the long run, it may have a negative impact on stock prices.
Over the last couple of years, ransomware attacks have emerged as one of the major threats to the financial sector. In 2024 alone, cybercrooks managed to carry out a whopping 3348 attacks globally on banks and other financial institutions.
To curb this situation, regulatory bodies are doubling down with stringent cybersecurity norms and regulations. For instance, now the banks are required to inform authorities about a cyberattack within the first **36 hours of the incident. Any leniency in compliance will further put a strain on finances because compliance failure will lead to substantial fines.

Deepfake voices can sound more real than you think!
Deepfake voices are increasingly becoming a major cause of concern. Threat actors use deepfake voices to manipulate you into sharing personal details, which they can later use to gain access to your network and systems . The worst part is that AI-generated deepfake voices are getting real with time. More and more people are now finding it hard to tell apart deepfake voices from human ones.
With time, AI is continually improving, and the eerie similarity between these deepfake voices is definitely a cause for concern. Deepfake voices can mimic that accent, initiate realistic conversations, and even incorporate brief pauses and whispers to sound more authentic.
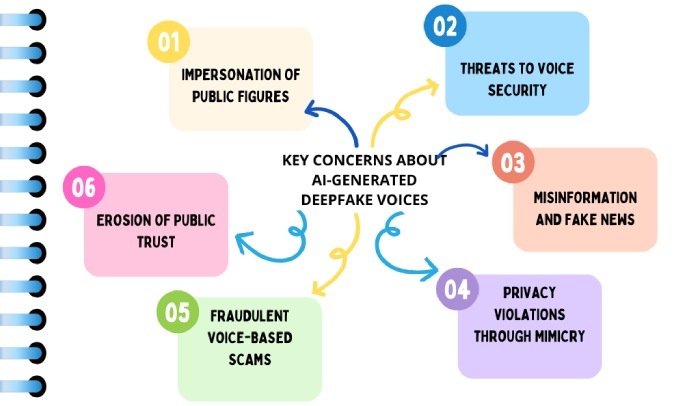
As AI gradually improves at replicating human voices, here’s what cyberexperts suggest to help you spot a deepfake voice.
Lack of coherence in speech
Deepfake voices are often not conversational enough. You will see that gap, that unnecessary jump from one topic to another. The natural flow that you generally experience while talking to your loved ones will be missing.
So, if you hear unusual background noise, then it is highly likely that it is a deepfake voice. Also, listen carefully and be alert if you hear **mispronounced words or slurred speech. Pay extra attention if you hear them stumbling over certain phrases.
Sources

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.