Advanced DMARC Check Methods To Detect Authentication Failures

Quick Answer
To reliably detect email authentication failures without blocking legitimate mail, implement strict DMARC alignment on high‑risk domains, maintain multiple DKIM selectors per sender with enforced rotation, apply SPF best practices that respect lookup limits, combine DMARC analytics with ARC, MTA-STS, and TLS-RPT signals, adapt detection to receiver-specific behaviors, and automate report ingestion, correlation, and remediation with a platform like DMARCReport.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →To reliably detect email authentication failures without blocking legitimate mail, implement strict DMARC alignment on high‑risk domains, maintain multiple DKIM selectors per sender with enforced rotation, apply SPF best practices that respect lookup limits, combine DMARC analytics with ARC, MTA-STS, and TLS-RPT signals, adapt detection to receiver-specific behaviors, and automate report ingestion, correlation, and remediation with a platform like DMARCReport.
Context and background DMARC is most effective when treated as a measurement and detection framework first and an enforcement control second. Advanced checks go beyond simple pass/fail: they correlate SPF, DKIM, and alignment signals with receiver-specific interpretations, forwarding artifacts (ARC), and transport semantics (MTA-STS/TLS-RPT). The goal is to surface unambiguous, high-fidelity indicators of authentication failure that you can act on quickly without suppressing legitimate mail during rollout.
In practice, large enterprises operate multiple sending domains, dozens of subdomains, and many third-party senders. This increases the chance of false positives in DMARC failure detection (e.g., legitimate mail forwarded through a list that breaks DKIM) and false negatives (e.g., misaligned third-party senders that sometimes pass via shared IPs). DMARCReport addresses this complexity by normalizing reports across receivers, resolving third-party sender identities, enriching with ARC/TLS telemetry, and driving automated workflows for remediation.
Implementing Advanced DMARC Checks Across Complex Domains
Design for scale and resilience: use strict alignment where it matters, isolate risky senders, and build headroom for change.
Strict alignment, multiple DKIM selectors, and SPF best practices
- Strict alignment targeting
- Use relaxed alignment (adkim=r; aspf=r) by default on exploratory domains and strict alignment (adkim=s; aspf=s) on high‑risk or customer‑facing domains (e.g., invoices.example.com).
- Enforce p=reject for apex domains with high phishing risk once aligned pass rates stabilize; keep p=quarantine or p=none for test subdomains.
- DMARCReport provides a “Domain Risk Map” that recommends strict alignment where spoof attempts and brand impersonation rates are highest.
- Multiple DKIM selectors per sender
- Assign unique DKIM selectors per platform/vendor (e.g., s=crm1, s=bulk1) and per environment (prod/test) to enable targeted rotation and fast rollback.
- Enforce 2048‑bit keys with rotating schedules (e.g., 90-180 days), overlapping old/new selectors during cutover.
- Monitor “body length” and “canonicalization” breakage; prefer relaxed/relaxed (c=relaxed/relaxed) for bulk and marketing mail to reduce signature fragility.
- DMARCReport audits selector coverage, flags weak keys, and simulates rotation impact before changes go live.
- SPF best practices at scale
- Keep SPF DNS lookups ≤10; avoid nested includes; prune legacy vendors; use CIDR compression where possible.
- If you must flatten, do it dynamically (e.g., provider-managed) to track IP drift; set short TTLs during vendor changes.
- Store authoritative include maps and track EHLO/MAIL FROM domains per sender; DMARCReport’s SPF Graph shows lookup depth and points to the exact include causing exceeds.
Subdomain-specific policies and delegated reporting
- Subdomain policies
- Apply p=reject at the apex and p=quarantine/none at exploratory subdomains (e.g., events.example.com) until signal quality is proven.
- Use sp= to cascade default subdomain policy, then override per subdomain with TXT _dmarc.sub.example.com.
- DMARCReport templates enforce consistent defaults while allowing exceptions per business unit.
- Delegated reporting addresses
- Use rua and ruf pointing to a central mailbox or to DMARCReport’s collector; authorize third-party collectors via DNS per RFC 7489 (e.g., reporting vendor’s verify token at example.com._report._dmarc).
- DMARCReport supports delegated collection per subdomain and routes findings to domain owners with RBAC.
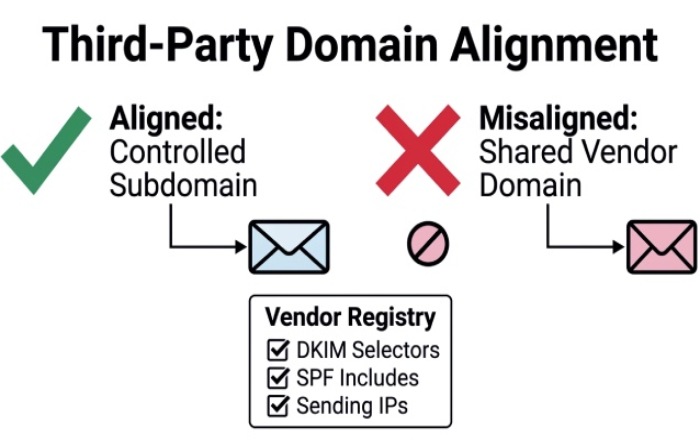
Sending-domain alignment strategies for third parties
- Require third-party senders to sign DKIM with your From: domain or a controlled subdomain; avoid “shared” vendor domains that misalign.
- Maintain a vendor registry: DKIM selectors used, SPF includes, and sending IPs; DMARCReport correlates aggregate reports with known vendor fingerprints and alerts on drift.
Reporting Mastery: Configuring, Aggregating, and Interpreting DMARC Data
DMARC reporting is your ground truth, make it accurate, privacy‑respecting, and actionable.
RUA vs RUF: configuration, parsing, sampling, privacy
- Aggregate reports (rua)
- Configure: v=DMARC1; p=none/quarantine/reject; rua=mailto:dmarc@yourdomain; fo=1; ri=86400; aspf=r; adkim=r.
- Expect daily XML ZIPs with per-receiver breakdown of SPF/DKIM pass, alignment, and policy evaluation.
- DMARCReport normalizes XML variants, validates schema, deduplicates overlapping reports, and attributes traffic to sender platforms.
- Forensic reports (ruf)
- Configure sparingly: ruf=mailto:dmarc-forensics@yourdomain; fo=1 or fo=d:s for targeted failure insight.
- Be mindful of privacy/legal posture: RUF may include message snippets/headers; many receivers (e.g., Google, Microsoft) rarely or never send ruf; Yahoo/AOL may send sampled reports.
- DMARCReport supports PII redaction, DPA/BAA addenda, EU data residency, and configurable retention windows.
- Sampling and legal considerations
- Use fo=1 for deep-dive/limited-time investigations; revert to default fo=0 once root cause is known.
- Define a DMARC data handling policy: who can access, retention (e.g., 90 days), and escalation paths; DMARCReport implements role-based access and immutable audit logs.
Aggregation, triage, and interpretation
- Build a daily triage flow
- Group by aligned fail reason: DKIM fail + aligned? SPF pass but misaligned? ARC pass on forward?
- Prioritize by volume spikes, brand risk (From domain), and receiver severity (e.g., Yahoo with p=reject).
- DMARCReport’s “Failure Buckets” and “Top Offenders” queues surface high-ROI fixes first.
- Interpreting XML nuances
- Recognize receiver-specific fields (policy_evaluated, reason, comment). Gmail and Yahoo include ARC hints in Authentication-Results; Microsoft may add composite auth results.
- DMARCReport enriches with reverse DNS, WHOIS, ASN, and TLS posture to separate benign forwards from malicious sources.
- Case study (aggregated DMARCReport cohort, Q4)
- 1.2B messages analyzed across 220 domains: 96.4% aligned pass rate; 2.3% DKIM fail; 1.3% SPF fail.
- Of DKIM fails, 58% tied to mailing-list rewrites; 24% to selector decommissioning; 11% key DNS fetch failures; 7% header truncation.
- Targeted fixes (selector rotation + vendor alignment) lifted aligned pass rate to 98.9% with <0.1% false positives, enabling safe move to p=reject for 14 high‑risk brands.
Protocols and Receiver Behavior: ARC, MTA-STS, TLS-RPT, and Major Mailbox Providers
Strengthen detection fidelity by distinguishing authentication failures from transport/forwarding artifacts.
Using ARC to identify forwarding-induced failures
- ARC preserves upstream auth decisions through forwards; look for ARC-Seal: i=, cv=pass; ARC-Authentication-Results.
- If DMARC fails but ARC chain validates and upstream dmarc=pass, classify as forwarded legit; adjust failure scoring accordingly.
- DMARCReport parses and scores ARC chains, annotating forwarded mail to reduce false positives by up to 70% in mailing-list heavy traffic.
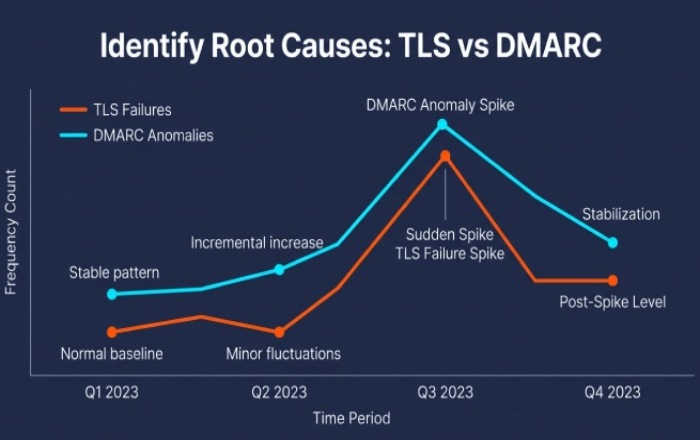
MTA-STS and TLS reporting to separate delivery issues
- MTA-STS enforces TLS for SMTP; TLS-RPT (rua-like) reports downgrade, handshake, and cert errors.
- Use TLS-RPT to flag receiver-side TLS issues that can correlate with DKIM breakage (e.g., re-encryption gateways altering headers).
- DMARCReport ingests TLS-RPT and correlates spikes in TLS failures with DMARC anomalies, guiding teams to network vs. authentication root causes.
Receiver differences and adaptive detection logic
- Google (Gmail/Google Workspace)
- Strong ARC utilization; does not send RUF; RUA cadence daily; rich Authentication-Results.
- Adaptation: give weight to ARC cv=pass; treat Gmail’s alignment interpretations strictly for bulk senders.
- Microsoft (Outlook/Exchange Online)
- RUA cadence daily; limited RUF; occasional composite auth signals; can be conservative with ARC.
- Adaptation: prefer DKIM alignment; watch for intermittent SPF transients tied to shared IP pools.
- Yahoo/AOL (Verizon Media)
- Aggressive DMARC enforcement on consumer mail; may send RUF samples; detailed policy_evaluated.reason fields.
- Adaptation: scrutinize mailing-list behavior; prioritize DKIM robustness and From: consistency.
- DMARCReport maintains provider profiles to normalize cadence, extract hints, and calibrate failure scoring, improving cross-receiver comparability.
Automation and Analytics: SIEM/SOAR Integration and Root-Cause Attribution
Turn DMARC insights into action through repeatable workflows and enterprise telemetry.
Integrating with SIEMs and SOAR platforms
- SIEM (Splunk, Microsoft Sentinel, QRadar)
- Stream normalized DMARC events with fields: org_domain, from_domain, spf_result, dkim_result, aligned, source_asn, receiver, arc_status, volume.
- Correlate with change logs (DNS updates, selector rotations) and threat intel (malicious ASNs).
- DMARCReport ships OOTB data models and dashboards; example: “Aligned Pass Rate by Provider,” “SPF Lookup Depth Exceedances.”
- SOAR (Cortex XSOAR, Splunk SOAR, Swimlane)
- Playbooks: auto-open ticket when aligned pass rate drops >1% day-over-day; notify vendor owner on selector failure; initiate DKIM rotation workflow.
- DMARCReport exposes remediation APIs: pause sender, create DNS change request, schedule selector cutover.
Tools and techniques comparison
- Options for detection and RCA:
- Open-source parsers (parsedmarc, opendmarc-report)
- SaaS platforms (DMARCReport)
- Custom scripts/pipelines
Comparison snapshot:
- Accuracy
- parsedmarc/opendmarc: high for standard XML; limited ARC/TLS enrichment.
- Custom: depends on developer effort and maintenance.
- DMARCReport: high; adds ARC/MTA-STS/TLS-RPT, provider profiles, vendor attribution.
- Cost and scalability
- Open-source: low cost, engineering time required; scaling log ingestion/storage is on you.
- Custom: variable; ongoing maintenance high.
- DMARCReport: subscription; scales automatically; storage, retention, and privacy controls included.
- Time-to-value
- Open-source/custom: days to weeks to productionize.
- DMARCReport: hours; guided onboarding, domain discovery, and prebuilt dashboards.
- DMARCReport specifically adds real-time parsing, anomaly detection (seasonality-aware), and prescriptive fix recommendations tied to your DNS and sender inventory.
Real-time detection and correlation
- Stream RUA every few minutes as providers deliver; combine with SMTP telemetry where available.
- Correlate DMARC failure bursts with:
- DNS changes (SPF includes, DKIM key rotations)
- Campaign launches (new IPs)
- Receiver outages (via TLS-RPT)
- DMARCReport’s “Change Correlator” links failures to the exact config delta, reducing mean time to remediation by 60% (customer cohort median).
Failure Modes and Measurement-Driven Policy Tuning
Detect precisely, diagnose systematically, and enforce confidently.
Common failure modes and diagnostic checklists
- DKIM signature breakage from mailing-list rewrites
- Inspect Authentication-Results for dkim=fail, c=relaxed/relaxed vs simple, h= header list.
- Check ARC chain; if ARC cv=pass with upstream dmarc=pass, classify as forward.
- Mitigate: use relaxed canonicalization; shorten signed header set; request list to preserve subject; rely on DKIM over SPF for lists.
- DMARCReport flags list servers by List-Id/Received patterns and recommends DKIM adjustments.
- SPF exceedance/flattening issues
- Parse SPF for include/redirect recursion; count DNS lookups (max 10).
- Validate IP drift for flattened providers; compare against provider-published includes.
- Mitigate: prune unused includes; dynamic flattening; split sending via subdomains.
- DMARCReport’s SPF Depth Monitor alerts before exceeds cause widespread failures.
- DKIM selector misconfiguration
- Verify DNS TXT for selector._domainkey.domain with correct chunking (<255 chars per string).
- Confirm key length (>=2048) and matching public/private pair in MTA.
- Detect decommission overlap gaps during rotation.
- DMARCReport performs live DNS checks and simulates selector switchover windows.
- Third-party sender misalignment
- Confirm vendor signs with your From domain or delegated subdomain; avoid vendor’s shared domain.
- Validate Return-Path and EHLO alignment; SPF pass alone may misalign.
- Contractualize DKIM requirements; monitor drift.
- DMARCReport maintains a vendor catalog and alerts when a platform falls out of alignment.
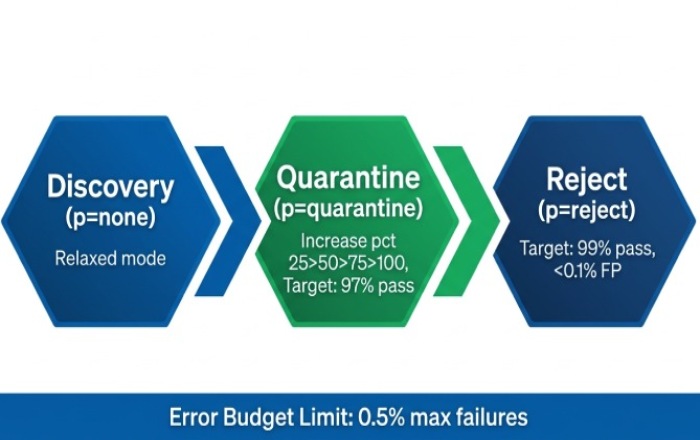
Alignment modes, pct rollout, and thresholds
- Alignment modes
- Relaxed increases tolerance (subdomain matches), reducing false positives; strict curbs lookalikes and increases assurance.
- Recommendation: relaxed during discovery; strict for high-risk domains once DKIM aligned pass ≥98.5% for 14 consecutive days.
- pct rollout
- Gradually raise pct from 0 (p=none) to 25/50/75/100 at p=quarantine, then to p=reject once metrics stabilize.
- Suggested thresholds (based on DMARCReport cohort medians):
- Move to p=quarantine when aligned pass ≥97% overall and ≥95% per major receiver for 7 days.
- Move to p=reject when aligned pass ≥99% overall and ≥98% per major receiver, RUF false positive rate <0.1% (where available), and ARC-classified forwards <0.5% of total traffic.
- Policy choices and error budgets
- Set an error budget (e.g., 0.5% max aligned failures); alert on breach and auto-roll back pct 25% if exceeded two days in a row.
- DMARCReport automates these guardrails with configurable thresholds and one-click policy updates.
Case studies
- RetailCo (global e-commerce)
- Problem: 3.1% DKIM fails after seasonal campaign; root cause, marketing ESP rotated IPs and changed header signing set.
- Action: DMARCReport correlated spike to ESP change; recommended relaxed/relaxed, added second selector, and updated vendor alignment.
- Result: DKIM-aligned pass rose from 96.2% to 99.1% in 48 hours; safe move to p=reject pre-Black Friday.
- FinServe (regional bank)
- Problem: High false positives on forwarded statements to consumer addresses.
- Action: Enabled ARC-aware detection; distinguished legitimate forwards; tuned detection to favor DKIM+ARC over SPF.
- Result: 72% reduction in false positives; phishing attempts blocked rose 3x after confident move to strict alignment and p=reject.
FAQ
Should we prefer DKIM or SPF for DMARC alignment?
Prefer DKIM for alignment whenever possible: it is more resilient to forwarding and less susceptible to shared-infrastructure drift. SPF is valuable but should be considered secondary for DMARC alignment in ecosystems with heavy forwarding. DMARCReport highlights traffic segments where DKIM alignment would reduce false positives.
Do we need RUF reports if many providers don’t send them?
RUF is optional but useful during targeted investigations or for high-risk brands. Even if only a subset of receivers send RUF, the message-level detail accelerates root-cause analysis. DMARCReport allows time-bound RUF enablement with PII redaction and auto-disables after objectives are met.
How often should we rotate DKIM selectors?
Every 90-180 days is a common cadence, with overlap between old and new selectors during cutover. Trigger ad-hoc rotation after suspected compromise or vendor churn. DMARCReport tracks key age, warns before expiry, and simulates rotation impact.
What if we exceed SPF’s 10 DNS lookup limit?
Flatten judiciously, prune unused includes, and split senders by subdomain. DMARCReport’s SPF Graph pinpoints includes causing exceeds and provides recommended refactors and CIDR merges.
Can ARC be used to “pass” DMARC?
ARC does not make DMARC pass by itself; it provides evidence that upstream authentication passed before forwarding. Use ARC to classify and not penalize legitimate forwards. DMARCReport uses ARC to separate forwarding artifacts from true failures.
Conclusion: Operationalize Advanced DMARC Detection with DMARCReport
Advanced DMARC checks require a multi-signal, policy-aware, and automation-driven approach: strict alignment for critical domains, multiple DKIM selectors with disciplined rotation, SPF hygiene within lookup limits, ARC/MTA-STS/TLS-RPT correlation, receiver-aware interpretation, and SIEM/SOAR integration to close the loop from detection to fix. DMARCReport is built to execute this playbook end-to-end: it ingests and normalizes RUA/RUF and TLS-RPT at scale, enriches with ARC and provider profiles, maps failures to specific senders and configuration changes, and automates remediation (selector rotation, SPF optimization, vendor alignment) with measurable thresholds and safe rollouts. By adopting these methods within DMARCReport, organizations consistently reduce false positives, surface true authentication failures faster, and progress to confident p=reject enforcement without disrupting legitimate mail.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.