From DKIM to DKIM2: How email authentication is evolving

Quick Answer
The three core email authentication standards - SPF (RFC 7208), DKIM (RFC 6376), and DMARC (RFC 7489) - work together to verify that an email genuinely originates from the domain it claims to represent. Since February 2024, Google and Yahoo require all three for bulk senders. DMARC Report
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DKIM Lookup
Auto-discover DKIM selectors for any domain - scan 185 common selectors across all major providers.
Discover DKIM Selectors →
DKIM is the authentication protocol that survives email forwarding, says Brad Slavin, General Manager of DuoCircle. When SPF fails because a forwarder’s IP isn’t in the original record, DKIM alignment is the only path to DMARC pass. That’s why we monitor DKIM alongside SPF in every DMARC Report dashboard.
The three core email authentication standards - SPF (RFC 7208), DKIM (RFC 6376), and DMARC (RFC 7489) - work together to verify that an email genuinely originates from the domain it claims to represent. Since February 2024, Google and Yahoo require all three for bulk senders. DMARC Report
From DKIM to DKIM2: How email authentication is evolving
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-22976">
<source src="https://media.mailhop.org/dmarcreport/images/2025/03/From-DKIM-to-DKIM2-How-email-authentication-is-evolving.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M32S">2:32</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-22976" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-22976" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-22976" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-22976" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/from-dkim-to-dkim2-how-email-authentication-is-evolving/&t=From DKIM to DKIM2: How email authentication is evolving" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/from-dkim-to-dkim2-how-email-authentication-is-evolving/&url=From DKIM to DKIM2: How email authentication is evolving" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/03/From-DKIM-to-DKIM2-How-email-authentication-is-evolving.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/from-dkim-to-dkim2-how-email-authentication-is-evolving/" class="input-link input-link-22976" title="Episode URL" readonly />
<button class="copy-link copy-link-22976" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-22976” readonly/>
<button class="copy-embed copy-embed-22976" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Email communications have always been one of the favorite targets among threat actors. To safeguard their email ecosystem, businesses and organizations use email authentication protocols such as SPF, DKIM, and DMARC. DKIM has been an integral part of email security mechanisms since 2007. This email authentication tool helps verify whether or not an email has been tampered with during its transit.
Given the **highly dynamic nature **of cyber threats, the security mechanisms need to be flexible as well. On that note, the cybersecurity ecosystem welcomes a highly evolved version of DKIM called DKIM2.
This blog post sheds light on the transition from DKIM to DKIM2.
DKIM2- The new face of the email authentication system!
Simply put, DKIM2 is the better and improved version of DKIM. Its ultimate goal is to fix DKIM’s shortcomings. With its upgraded features, DKIM2 is capable of offering boosted email security in the form of improved forwarded email management, easy key management, and enhanced encryption. This version will make it easy for you to **monitor and track your email activity without any complications. All the upgrades and enhancements make DKIM2 a perfect fit for you to strengthen your overall email security and minimize the risk of cyber threats such as phishing and spoofing.
Why DKIM2?
DKIM has been an efficient email authentication tool so far. However, it has its fair share of shortcomings and weaknesses. The increasingly sophisticated moves of cyberattackers are a **staggering reminder that DKIM, too, needs a thorough upgrade.
Here’s why DKIM should be replaced with DKIM2:
Email gets altered while being forwarded
DKIM is no longer very effective when it comes to email modifications. While going through spam filters or mailing lists, emails may get tampered with slightly. Now, these small changes can have a major impact on the DKIM’s digital signature. Ultimately, the email ends up failing the DKIM check because of a mismatched digital signature. So even if the email is a legitimate one, it will never reach the right recipient and will simply move to the spam folder.
Lack of standardized feedback on DKIM failures
As of now, there is no standardized way to be informed if your email fails the **DKIM check because of a digital signature failure. Because of this lack of feedback, it gets extremely cumbersome for organizations to monitor whether or not their emails are getting delivered properly to the recipients.

Backscatter problems for domains
Threat actors can easily create fake email sender addresses and send out malicious emails. The email does not get delivered, but your own email security system will send a ‘failure notice’ to you. The failure notice is also known as DSN or Delivery Status Notification. Not only such a notice will affect your peace of mind but it will also tarnish your domain’s reputation.
Replay attack
One of the biggest loopholes in DKIM is replay attacks. Basically, threat actors resend a specific email that was earlier authenticated by DKIM signature. This newly re-sent email now serves as an authentic message, too. However, the recipient server is not aware of this and may end up receiving this malicious email right in the inbox. This will not only put the recipient at risk of cyber threat but will also harm the reputation of the legitimate domain owner whose authenticated email has been misused by the threat actors.
How will DKIM2 bolster your email security system?
DKIM2 will help businesses overcome the above-mentioned weaknesses, thereby improving the overall email security system. Here’s how:
How Do You Prevent backscatter issues?
DKIM2, with its boosted features, helps in **fixing the backscatter issues by making sure that the failure notices are sent only to the last email server that handled them. So legitimate domain owners don’t get spammed with false error messages again and again.
Standardized header signing
DKIM is not able to sign all the email headers with perfection every time. This enables threat actors to carry out malicious activities. With DKIM2, it is possible to sign all critical email headers with uniformity. This eliminates even the slightest chance of vulnerabilities, leading to fool-proof email security.
Combatting DKIM replay attacks
DKIM2 has this incredible feature, which makes it way better than DKIM! It comes with timestamps and recipient information. This solves the issue of replay attacks. The timestamps and recipient information **enable domain owners to identify the emails that are being replayed by threat actors with malicious motives. The replayed emails can actually be identified and blocked easily, thanks to DKIM2.
Easy and seamless error handling
When an email fails the DKIM check, it is hard to understand the exact reason behind the authentication failure. However, DKIM2 enables domain owners to closely track the emails that fail authentication **checks and analyze why they failed in the first place. With DKIM2, mailing lists are able to track, manage as well as undo any alterations they made, thereby enabling one to understand if an email has been tweaked or tampered with.
Simplifying crypto-calculations
With DKIM, email servers are required to verify all the cryptographic signatures, which leads to unnecessary delays. But DKIM2 has been designed to simplify this process. DKIM2 verifies only the first **digital signature when the email hasn’t been tampered with in transit. This makes the entire verification process swift and easy.
Boosted algorithms
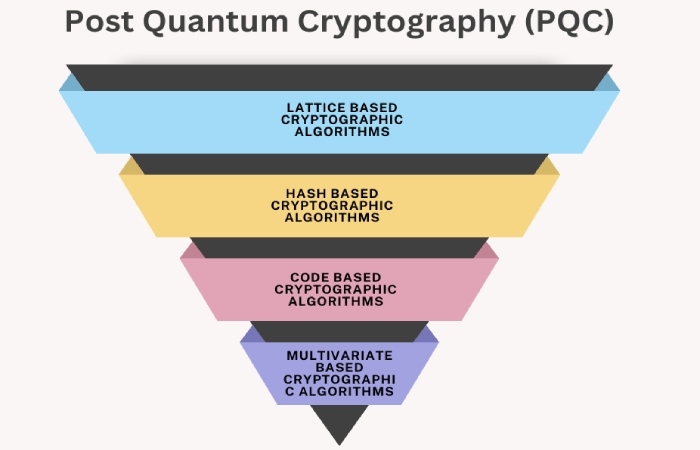
DKIM2 is known for its compatibility with different cryptographic algorithms such as elliptic curve, RSA, and post-quantum. A higher degree of compatibility with **multiple algorithms means that you are future-proofing your email authentication system by adding an element of flexibility to it. No rigidity, and hence no risk of obsolescence.
Wrapping Up!
DKIM2 is a crucial step forward in securing your email authentication system by replacing the older version. With DKIM2, a business organization can easily bolster its email security mechanism, improve email deliverability, and keep spoofing and phishing threats at arm’s length. If you’re still sitting on the fence and delaying the transition unnecessarily, you’re making your email ecosystem vulnerable to cyberattacks. Switching from DKIM to DKIM2 isn’t a luxury. It’s a necessity to survive in this digital world surrounded by threat actors.
Sources
Topics

CTO
CTO of DuoCircle. Leads engineering for DMARC Report and DuoCircle's email security product portfolio.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.