How does DMARC shield your business from different email-based cyber threats?

Quick Answer
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible `From` header. According to Google's February 2024 bulk sender requirements, a DMARC policy of at least `p=none` is now mandatory for any domain sending 5,000+ messages per day to Gmail users. DMARC Report
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →DMARC is the only email authentication protocol that gives you both enforcement and visibility, says Brad Slavin, General Manager of DuoCircle. SPF and DKIM authenticate silently - DMARC tells you what happened and lets you control the outcome. That combination of reporting and policy is why DMARC adoption is accelerating.
DMARC (RFC 7489) ties SPF and DKIM together by requiring alignment between the envelope sender and the visible From header. According to Google’s February 2024 bulk sender requirements, a DMARC policy of at least p=none is now mandatory for any domain sending 5,000+ messages per day to Gmail users.
DMARC Report
How does DMARC shield your business from different email-based cyber threats?
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-21529">
<source src="https://media.mailhop.org/dmarcreport/images/2025/02/How-does-DMARC-shield-your-business-from-different-email-based-cyber-threats-1.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M10S">2:10</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-21529" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-21529" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-21529" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-21529" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/how-does-dmarc-shield-your-business-from-different-email-based-cyber-threats/&t=How does DMARC shield your business from different email-based cyber threats?" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/how-does-dmarc-shield-your-business-from-different-email-based-cyber-threats/&url=How does DMARC shield your business from different email-based cyber threats?" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/02/How-does-DMARC-shield-your-business-from-different-email-based-cyber-threats-1.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/how-does-dmarc-shield-your-business-from-different-email-based-cyber-threats/" class="input-link input-link-21529" title="Episode URL" readonly />
<button class="copy-link copy-link-21529" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-21529” readonly/>
<button class="copy-embed copy-embed-21529" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
The **last two decades have witnessed a steep surge in cyberattacks, and 2025 is not going to be any different. What’s extremely concerning is that as many as 3.4 billion emails are sent out by threat actors every single day! This is precisely why businesses, as well as individuals, must prioritize cybersecurity at any cost. This can be done with the help of DMARC or Domain-based Message Authentication, Reporting, and Conformance. DMARC is one of the three most popular email authentication protocols, which helps **verify the authenticity of the email sent from a specific domain. When enforced by the legitimate domain owner , DMARC enables the recipient email server to take necessary actions based on whether or not the email received is genuine.
This article aims to explore the different types of cyberattacks that can impact your business in 2025 and how you can prevent those attacks by deploying the DMARC protocol.
Top 5 cyberattacks that can be prevented with the help of DMARC authentication
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
1. Phishing attacks
Phishing is one of the most **prevalent cyberattacks across the globe, and it involves sending out fraudulent communications that appear to be coming from a reputable and renowned source. Cybercriminals impersonate any trusted brand or entity and send malicious emails to the recipients. The goal is to trick them into sharing highly sensitive details such as usernames, passwords, bank account details, and so on. There are majorly four types of phishing attacks: deceptive phishing, spear phishing, whaling, and pharming
How to prevent phishing with DMARC?
Enforcing DMARC ensures that only legitimate emails from an authorized domain reach the users’ inboxes. In case an email fails DMARC authentication, the domain owner can instruct the recipient email server to take specific actions. The failed email can either be moved to the spam folder or rejected straightaway. However, if the email seems genuine, then it will reach the inbox safely. This significantly prevents phishing attempts. Later on, you will receive detailed reports on unauthorized attempts to send malicious emails through your domain. That report can be used to analyze and take action accordingly.
2. Email spoofing

Email spoofing involves cyberattacks in which threat actors try to disguise their real identity. They do this easily by tweaking the sender details in emails. Because of this manipulation, victims see the fraudulent emails as genuine and as having come from a reputed and trusted source. Email spoofing can impart extreme damage to businesses in the form of tarnished goodwill and lack of credibility. Such attacks can force customers to face attacks like financial fraud, identity theft, and data breaches.
How to prevent email spoofing with DMARC?
When a business enforces DMARC alongside SPF and DKIM protocols, it gets easier to verify the email sender’s identity. In case the email fails an authentication check, the recipient email server can follow the instructions given by the domain owner. The unauthorized mail can be blocked or quarantined based on DMARC policy (quarantine or reject).
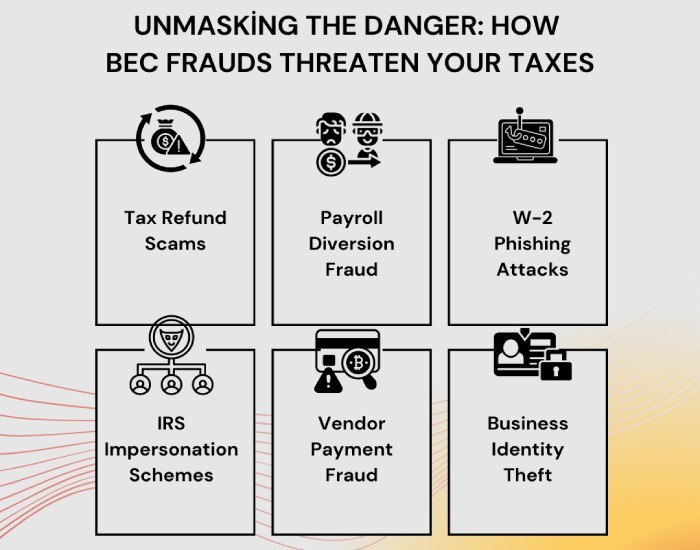
3. Business Email Compromise (BEC)
Business Email Compromise is a serious threat that involves a threat actor gaining unauthorized access to a company’s email account. They pretend to be the account holder and carry out frauds against the company. The primary targets of BEC attacks are vendors, executives, or business partners who can manipulate the employees of that company into making malicious transactions or even sharing personal data. Some of the most common BEC frauds are tax threats, attorney impersonation, fake charities, and so on.
How to prevent BEC attacks with DMARC?
When enforced successfully, the organization can make the best use of the DMARC reports to figure out and take strict actions against the malicious sender sources. DMARC blocks any fraudulent email that appears to be coming from a company’s official domain. By rejecting such unauthorized emails, DMARC protects the executives’ or vendors’ email addresses from being misused in BEC scams.
4. Ransomware distribution
The ransomware attack, an extremely common threat attack that has **gained immense popularity **among cybercriminals in the past five years, involves sending out fraudulent emails that contain malicious links or attachments. Clicking on them inadvertently can lead to downloading harmful malware that encrypts your data. The threat actors then ask for ransom payments in exchange for data retrieval.
How to prevent ransomware attacks with DMARC?
Mostly, ransomware emails use spoofed domains. If you are using DMARC protocol to safeguard your email communications, then it will simply block the unauthorized emails before they reach the target inboxes. This will significantly lower the chance of any naive user clicking on those harmful links or attachments.
5. Credential harvesting
Another common cyberattacking tactic, credential harvesting, is a technique that uses fake login pages that are shared via email with the purpose of stealing user credentials such as usernames and passwords. These emails often pretend to be coming from a high-profile service provider.
How to prevent credential harvesting with DMARC?
DMARC protocol ensures that the malicious emails that impersonate a legitimate domain or a trusted brand domain get either **quarantined or rejected as per the instructions of the authorized domain owner. This drastically brings down the chances of users receiving fake email messages, thereby further reducing the chances of credential harvesting attacks.
Enforcing DMARC for enhanced protection against cyberattacks!
DMARC can offer maximum protection when accompanied by SPF (Sender’s Policy Framework) and DKIM (DomainKeys Identified Mail). Initially, a business must proceed with a p=none policy in DMARC settings. This enables the **domain owner to closely monitor the email traffic without accidentally blocking any genuine email communications. Meanwhile, DMARC reports can be used to identify unauthorized email sources. Based on those reports, the domain owner can then choose either p=quarantine or p=reject to safeguard the recipients.
Businesses must always stay a step ahead of the cybercriminals by adopting stringent measures such as enforcing DMARC protocol. It ensures that your business email ecosystem is equally **safe and secure for all the stakeholders. Wait no more and set up a robust email authentication system like DMARC today!
Sources

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.