Phishing vs. Smishing vs. Vishing: Everything You Need to Know

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Phishing vs. Smishing vs. Vishing: Everything You Need to Know
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Phishing vs. Smishing vs. Vishing: Everything You Need to Know
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-11075">
<source src="https://media.mailhop.org/dmarcreport/images/2024/02/Phishing-vs.-Smishing-vs.-Vishing.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M8S">2:08</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-11075" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-11075" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-11075" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-11075" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/phishing-vs-smishing-vs-vishing-everything-you-need-to-know/&t=Phishing vs. Smishing vs. Vishing: Everything You Need to Know" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/phishing-vs-smishing-vs-vishing-everything-you-need-to-know/&url=Phishing vs. Smishing vs. Vishing: Everything You Need to Know" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/02/Phishing-vs.-Smishing-vs.-Vishing.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/phishing-vs-smishing-vs-vishing-everything-you-need-to-know/" class="input-link input-link-11075" title="Episode URL" readonly />
<button class="copy-link copy-link-11075" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-11075” readonly/>
<button class="copy-embed copy-embed-11075" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Have you ever received an email from a seemingly familiar sender only to realize that it was perhaps a fraudulent one, masquerading as a legitimate email ? Well, this looks like a classic case of a phishing attack that involves **deceitful communication designed to trick individuals into divulging sensitive information, such as login credentials, financial details, or other personal data. Guess what? You’re not alone in this! In the year 2022, nearly 25% of organizations across the globe encountered a breach that compromised at least one of their accounts.
As the digital landscape evolves, these attacks not only become more frequent but also more sophisticated in their approach. Cybercriminals have found new ways to enter your digital territories_ _to jeopardize the **integrity and operational capabilities of your business. These techniques include smishing and vishing.
Wondering how these attacks vary from each other? In this article, we’ll take you through the nuances of these attacks, delving into the tactics employed, their distinct characteristics, and how they pose a threat to digital security.

What are Phishing Attacks?
At its core, phishing is a kind of **social engineering attack where an attacker impersonates a reputable entity with the aim of making the victims open an email, message, or link. Lately, it has become more than a mere buzzword in the cybersecurity space. If you look at the trajectory of the evolution of these attacks, you will notice that they have grown from simple deceptive emails seeking personal information to complex schemes that exploit social engineering, technology, and psychological manipulation.
But why do cybercriminals feel the need to resort to such strategic tactics?
It is no surprise that your digital ecosystem is a treasure trove of valuable information and resources. Everything from your financial details to **sensitive personal information is stored and transmitted online , which means that they are as accessible to the attackers as they are to you. Adversaries leverage these vulnerabilities to trick you into handing over your personal information, financial details, or access credentials without a second thought.
How Do They Work?
We have already established that phishing attacks have grown in sophistication. This means that the attacks now put more thought and deliberation into deceiving you. Some of the common strategies employed by these threat actors include **fake websites that mirror legitimate ones to an uncanny degree, personalized emails that bypass spam filters and seem convincingly real , and social media campaigns designed to gather personal data under the guise of legitimate inquiries.
What are Smishing Attacks?
As you know, phishing attacks can be executed in more than one way; one such technique is called “smishing”. Smishing attacks - “SMS” +“phishing,” are a form of cyberattack that relies on text messages to deceive recipients into revealing personal information, clicking on malicious links, or performing actions that compromise their security.
These kinds of attacks are more common than you think! According to the reports, smishing attacks grew by over 700% in the first two quarters of 2021. These alarming **statistics raise various questions, one of them being - why has smishing gained such momentum lately?
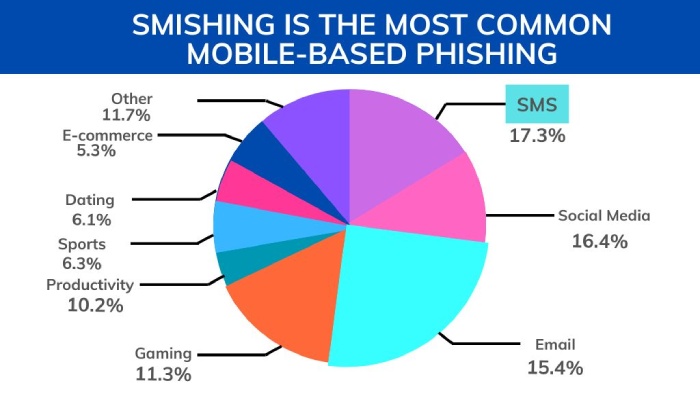
There are various factors that contribute to the rise of smishing attacks. Given the intimate and direct nature of SMSes, as compared to emails, it is more likely that you will open a text message than an email. Cyber attacks leverage this opportunity to exploit your trust and compromise security. Moreover, as the email ecosystem has now become challenging to trespass, thanks to spam filters and other authentication techniques, attackers have turned their attention to SMS as a less protected entry point.
How Do They Work?
Smishing attacks work like any other phishing attack, with the only difference being the **medium - SMSes instead of emails or calls.
To avoid scrutiny and evade detection, attackers get really crafty with the messages they send. By crafting messages that **mimic legitimate communications from trusted institutions or urgent alerts that require immediate action, they deceive you into clicking on malicious links, revealing sensitive information, or even downloading malware.
What are Vishing Attacks?
Another type of phishing attack that has garnered a lot of attention lately is the “vishing attack”. These kinds of social engineering attacks involve cybercriminals making phone calls to victims in an attempt to deceive them into divulging sensitive information or performing actions that compromise their security. Unlike traditional phishing attacks, these attacks rely on direct verbal interaction, which builds a sense of trust that is ultimately shattered.
Again, it is the rapid advancement in technology that has made voice calls a lucrative channel for cybercriminals and pull off scams worth $39.5 billion in 2021. Thanks to technologies like AI, it has now become easier than ever to spoof caller IDs and manipulate voice recordings.
Additionally, the **widespread adoption of digital communication platforms has provided attackers with a larger pool of potential victims to target, as more people rely on phones for both personal and professional purposes.
How Do They Work?
Just like any other phishing technique, vishing attacks work by exploiting human psychology and trust, relying on social engineering techniques to manipulate you into divulging sensitive information or **performing actions that compromise your security.
Imagine you receive a call from someone claiming to be your bank, mentioning all the important details about your account, the recent transactions, and more. Your first instinct would never be that of doubt, especially after they have revealed such sensitive information. The thing is, these attackers often employ persuasive tactics, citing urgent reasons such as suspicious account activity or security concerns to prompt you into divulging personal information.
In an attempt to steal money or personal information, they might even go as far as utilizing AI to create highly realistic voice imitations of trusted individuals, **including customer service representatives, colleagues, or even friends and family members.
All of this sounds daunting, right? Even if it feels like you’re heavily enmeshed in this pervasive issue, you can avert being a victim of such attacks. It all begins by fostering cyber consciousness and resilience, and an integral part of this preventive strategy can involve deploying email security measures such as SPF, DKIM, and DMARC. These measures can significantly reduce the risk of falling prey to cyber attackers. Need help fortifying your defenses as an organization? Trust our team of experts at DMARCReport! Book a demo with us today!
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.