Piggybacking Attack: Understanding Piggybacking In Cybersecurity

Quick Answer
In cybersecurity, piggybacking describes an adversary attaching their unauthorized activity onto an authorized channel, process, or identity to bypass controls. Conceptually, it borrows from networking where efficiency gains come from combining acknowledgment signals with user data during data transmission. In both domains, the working principle is the same: leverage existing two-way communication between a sender and a receiver to ride.
Related: Free DMARC Checker

In cybersecurity, piggybacking describes an adversary attaching their unauthorized activity onto an authorized channel, process, or identity to bypass controls. Conceptually, it borrows from networking where efficiency gains come from combining acknowledgment signals with user data during data transmission. In both domains, the working principle is the same: leverage existing two-way communication between a sender and a receiver to ride along without drawing attention.
When a malicious actor rides an established session, an authenticated token, or a physical entry event, the attack inherits trust and reduces detection. Within email systems, authentication protocols such as DMARC (Domain-based Message Authentication, Reporting, and Conformance) play a crucial role in identifying and mitigating misuse. They achieve this by allowing only verified senders to utilize a domain, thereby minimizing chances for unauthorized access to reliable communication channels.
How It Differs from Tailgating and Session Hijacking
- Tailgating is a physical access control lapse where an intruder follows someone through a secured door. Piggybacking may include tailgating, but more broadly covers digital contexts (Wi‑Fi use, token abuse, or control frame manipulation during data transfer).
- Session hijacking takes over a live connection by stealing cookies or sequence information. Piggybacking often keeps the legitimate session intact while the attacker appends their traffic or actions to the same channel or data packet flow.
Variants of Piggybacking
Physical Entry
An attacker times entry to pass alongside a legitimate user - sometimes even after initiating an intercom request and then “sharing” the opening. The user becomes an unwitting sender of access, and the intruder becomes the unauthorized receiver of the same door event.
Wi‑Fi and Network Piggybacking
Here, the adversary latches onto open or poorly authenticated wireless networks, reusing SSIDs, weak pre‑shared keys, or MAC spoofing to blend into normal data transmission. Attackers may also exploit misconfigured guest VLANs, injecting control frame traffic or malformed data frames to escalate from access to compromise.
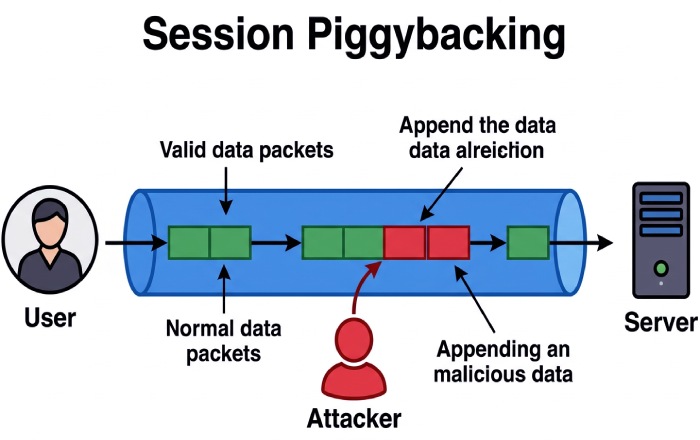
Session and Token Piggybacking
Attackers leverage valid tokens (e.g., OAuth, SSO cookies) and append transactions, API calls, or a PUSH packet at the application layer to an active session. Unlike outright theft, the attacker’s actions ride the legitimate channel, where the network layer usually sees “normal” data packets and confirmation exchanges.
Protocol Piggybacking: The Networking Concept Behind the Name
OSI Model Context: Data Link and Network Layer
In computer networking literature (see Andrew Tanenbaum and David Wetherall, Computer Networks, Pearson Education Limited), piggybacking refers to sending acknowledgment (ACK) information within an outgoing data frame rather than as a separate control frame. Within the OSI model:
- At the data link layer, sliding window protocols carry ACK information as an additional field inside a data frame to optimize channel bandwidth.
- At the network layer, routers focus on data packet forwarding, but the efficiency benefits are realized end-to-end as fewer standalone ACK frames traverse the path.
ACK Piggybacking Mechanics
- Working principle: In two-way communication, each side alternates roles as sender and receiver. When the receiver has data to send, it includes the ACK in the same frame - an outgoing data frame - rather than emitting a separate acknowledgment.
- Elements: sequence number management, a counter for frames in flight, delayed acknowledgment to wait briefly for payload to attach, and logic for duplicate ACK on perceived packet loss.
- Trade-offs: If the receiver timeout or emitter timeout expires (a timeout period governed by Timeout (computing)), a separate ACK or retransmission is sent. Too much delay increases latency and risks retransmitted frames; too little delay reduces efficiency.
- Edge cases: Loss of an ACK frame bundled inside a data frame can be misread as duplication or packet loss, prompting unnecessary retransmission. PUSH packet semantics can force immediate delivery, skipping delayed ACK logic.
Advantages and Disadvantages in Protocol Terms
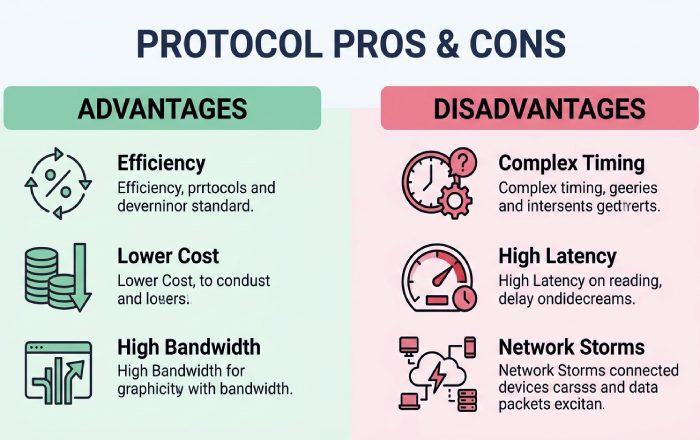
- Advantages: Improved efficiency, reduced usage cost, and better channel bandwidth utilization by cutting separate acknowledgements and standalone control frames.
- Disadvantages: Complex timing, potential for increased latency if delayed acknowledgment is mistuned, susceptibility to duplicate ACK storms under loss, and ambiguity during confirmation when a retransmitted frame races an original ACK.
Common Attack Paths and Real-World Examples
Physical Entry Examples
- Lobby slipstream: The attacker “helps” hold an elevator or door, piggybacking on the badge event already accepted by the reader (a control frame in the physical sense).
- Loading dock tail‑piggyback: Delivery timing coincides with a legitimate shipment; the intruder merges into the flow without additional confirmation.
Wi‑Fi Piggybacking Examples
- Open hotspot abuse: The attacker consumes a company’s guest SSID to stage internal scans, blending malicious data transmission with normal traffic. Packet loss and retransmission noise can mask scanning spikes.
- Evil twin and captive portal: A rogue AP mimics the corporate SSID; victims send credentials and data packets to the attacker acting as a man‑in‑the‑middle at the network layer, who then piggybacks the session upstream.
Session/Token Abuse Examples
- OAuth replay: The attacker reuses a valid bearer token to append API calls. Observers at the network layer see plausible data frames and ACK exchanges between the sender and receiver.
- Shared device misuse: On kiosks, an attacker rides a still‑logged‑in session to execute privileged actions before timeout.
Risks and Business Impact
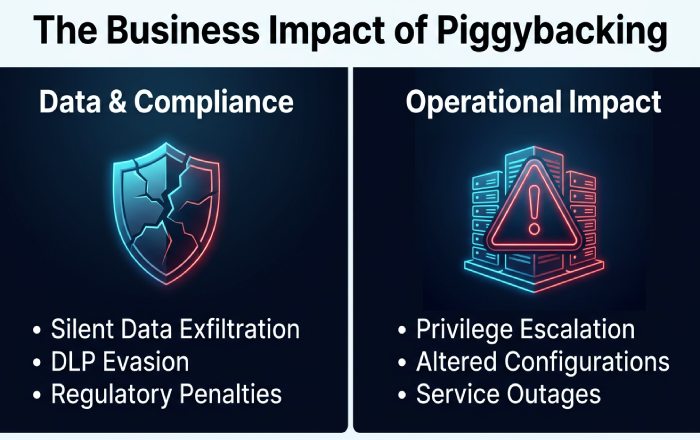
Data Exposure and Compliance
Piggybacking frequently leads to silent exfiltration of data packets, sidestepping DLP triggers when traffic appears as routine two-way communication. Consequences include regulatory penalties (e.g., under GDPR, HIPAA, or PCI DSS), breach of contractual obligations, and reputational damage. Because the ACK/confirmation cadence looks normal, detection gaps can persist across the OSI model, from the data link layer through the network layer and into application logic.
Privilege Escalation and Operational Impact
Attackers may escalate privileges by inheriting the trust of the original sender’s identity, altering configurations, or issuing administrative frames disguised among normal data transmission. Operationally, outages can result from misconfigurations or deliberate retransmission floods that exploit duplicate ACK behavior to degrade services.
Prevention and Detection Strategies
Technical Controls
- Strong identity and session controls: Short token lifetimes, device binding, proof‑of‑possession tokens, and continuous authentication reduce token piggybacking windows.
- Network segmentation and WPA3‑Enterprise: Limit lateral movement on Wi‑Fi; monitor for anomalous control frame rates and abnormal ACK frame patterns indicative of abuse.
- Access control hardening: Anti‑passback on doors, mantraps, and turnstiles reduce physical piggybacking. Use cameras with analytics to flag multiple persons per badge event.
Monitoring and Analytics
- Layered telemetry across OSI: Collect data from the data link layer (frame errors, retransmitted counts, packet loss), network layer (flow baselines), and application logs (sequence number anomalies, PUSH packet spikes).
- Behavioral analytics: Detect deviations in two-way communication symmetry, unusual ACK/confirmation ratios, or a sudden rise in delayed acknowledgment intervals that mask covert data transfer.
- Threat hunting: Query for duplicate ACK storms, unexpected additional fields in data frames, and timeout period anomalies that correlate with exfiltration.
User Awareness
- Train staff to challenge tailgating and report physical anomalies.
- Educate users on hotspot risks, token protections, and signs of session piggybacking (e.g., prompts for unexpected confirmation or out‑of‑sequence access).
Incident Response and Recovery
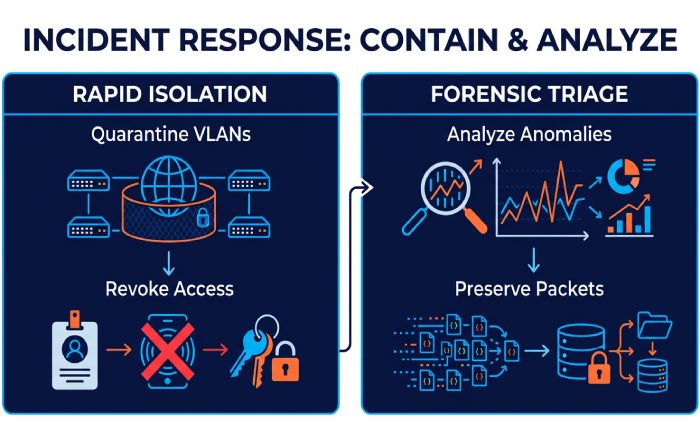
Containment and Forensics
- Rapid isolation: Quarantine affected VLANs, revoke tokens, and disable compromised accounts or badges.
- Forensic triage: Reconstruct sequence numbers, identify retransmission patterns, and examine control frame anomalies to separate normal congestion from attacker‑driven noise. Preserve data packet captures across layers for chain-of-custody.
Communication and Hardening
- Stakeholder updates: Provide clear status to executives, legal, and compliance on scope, data exposure, and remediation timelines.
- Hardening: Tune delayed acknowledgment thresholds, reset counters and timeout periods to sane defaults, enforce stricter ACK information validation, and require separate acknowledgements for high‑risk workflows. For physical security, shorten door open times and add secondary confirmation for after‑hours entries.
Cross‑Domain Insight: Why Piggybacking Persists
The Shared Assumption of Trust in Two-Way Communication
Whether a building door, a Wi‑Fi SSID, or an API session, piggybacking succeeds because infrastructures optimize for smooth data transmission and user experience. Systems expect predictable sender‑receiver interplay, timely ACKs, and orderly frames. Attackers exploit this predictability, slipping malicious data packets into trusted flows where controls prioritize efficiency over suspicion.
References and Further Reading Notes
Canonical Sources and Terminology
- Wikipedia and English Wikipedia, along with Espanol Wikipedia and Italian Wikipedia, host accessible primers on the OSI model, Network layer concepts, Sliding window protocol, Timeout (computing), Packet loss, and ACK frame behavior under Creative Commons, curated by the Wikimedia Foundation and broader Wikimedia communities with cross‑links to Wikidata.
- For rigorous treatments, see Andrew Tanenbaum and David Wetherall, Computer Networks (Pearson Education Limited), and articles discoverable via JSTOR and Google Scholar on sliding window protocols, data link layer efficiency, sequence number design, and duplicate ACK handling.
Application behavior notes, including PUSH technology and PUSH packet handling, illuminate how higher‑layer semantics interact with lower‑layer frames and confirmations during data transfer, highlighting both advantages and disadvantages for defenders modeling usage cost, channel bandwidth, and latency trade‑offs.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.