$20M Phishing Bust, Pension Scam Alert, Booking Data Breach

Quick Answer
The cybersecurity landscape witnessed multiple impactful developments last week, capturing the attention of cyber experts as well as common users. A major global phishing operation worth $20 million got disrupted by the FBI and the Indonesian National Police. UK pensioners have been requested to stay on high alert against the Winter Fuel Payment scam.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

The cybersecurity landscape witnessed multiple impactful developments last week, capturing the attention of cyber experts as well as common users. A major global phishing operation worth $20 million got disrupted by the FBI and the Indonesian National Police. UK pensioners have been requested to stay on high alert against the Winter Fuel Payment scam. Booking.com, the popular online travel agency, was compromised, resulting in a customer data breach. iPhone users may receive malicious emails that appear to be Apple alerts.
Global phishing syndicate linked to $20 million in attempted fraud, busted!
The FBI Atlanta Field Office and the Indonesian National Police carried out a joint operation to disrupt a global phishing syndicate. The operation led to the successful seizure of the core infrastructure. They also managed to nab a key suspect.
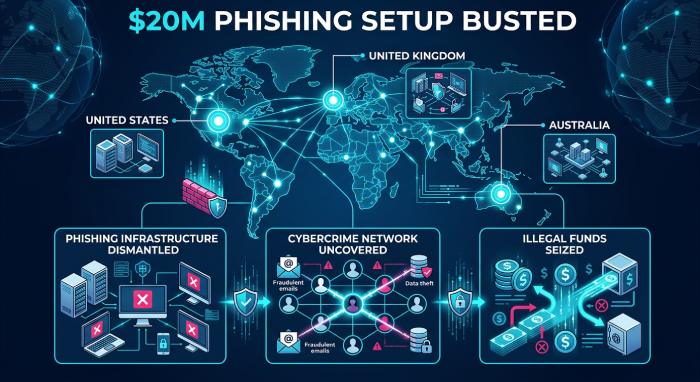
The phishing operation revolved around the W3LL phishing kit. This is one of the most popular phishing kits, worth $500, that helped threat actors design credible fake login pages to harvest sensitive data such as passwords and usernames.
The phishing kit is just a small part of the notorious cybercrime platform named W3LLSTORE. Between 2019 and 2023, the same platform facilitated the sale of 25K+ compromised accounts. Once they shut down the platform, the threat actors continued to operate via encrypted messaging. Between 2023 and 2024, the W3LL phishing kit was used by cybercrooks extensively to target the UK, the US, and Australia. Technology, manufacturing, and professional services were the hardest hit.
UK pensioners are facing the risk of a Winter Fuel Payment scam!
The Winter Fuel Payments are all set to begin this month in the UK. However, cybercrooks have been waiting for the same with eagerness. Experts have urged pensioners to stay cautious against cyber fraud related to Winter Fuel Payments.

Two million people will be repaying their winter 2025 payment since their annual income is higher than $45,000. The repayment is processed automatically.
Authorities and cybersecurity experts believe that the threat actors can pretend to be HMRC people and try to connect with their targets through emails, calls, letters, and text messages. To stay safe and avoid being scammed, people are urged to use GOV.UK to verify whether or not their payment is going to be recovered.
HMRC has also made it clear that they will not connect with people through text messages and emails for the repayment of the Winter Fuel Payment. Also, no one from HMRC will be requesting people to share their bank details.
Booking.com data breach compromises customer data!
Booking.com, the popular online travel agency known for its lucrative travel deals, has been targeted by threat actors. As a result of the data breach, Booking.com’s customer data has been compromised.
There’s still no clarity on which Booking.com systems have been compromised by the cybercrooks. One of their spokesperson stated that they “recently noticed suspicious activity affecting a number of reservations.” A detailed investigation has found that customer data, including names, phone numbers, and addresses, may have been compromised. They have confirmed that customer financial data has not been accessed yet.
Booking.com believes that the cyber “issue” has been sorted. They are informing affected customers and assisting with their bookings.
Reddit is replete with screenshots of alert emails shared by Booking.com customers. Some customers even claim to have experienced WhatsApp fraud attempts.

iPhone users are once again vulnerable to a whole new phishing campaign
iPhone users may receive fake emails claiming to offer iCloud storage availability. This is a new phishing campaign that has been targeting iPhone users by sending malicious emails. These emails will claim that the iCloud storage of the recipient is full, and that they are facing a serious threat of data loss. The idea is to create a sense of panic and urgency so that the targets click on the malicious links to upgrade their storage.
These fake alerts have been smartly designed to target the global user base of iPhone. The core idea is to gain access to their banking details, passwords, and personal data. The fake emails often try to play with the emotions of the victims, threatening them with account suspension and permanent data deletion warnings.
The malicious link that is supposed to help the users upgrade their iCloud storage, in reality, directs the victims to phishing websites. These malicious websites are designed to capture the sensitive data of victims, such as login credentials and payment details.
To increase the element of credibility, the fake emails are signed off as “The iCloud Team.” Also, the overall structure and design of these phishing emails are quite similar to Apple’s official branding.

Experts have urged iPhone users to delete any suspicious emails and avoid sharing any sensitive data in reply to such phishing emails.Cybersecurity experts emphasize that implementing DMARC, DKIM, and SPF is essential to protect domains from spoofing and strengthen email authentication against evolving cyber threats.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.