Trellix Source Breach, MOVEit Auth Bypass, DAEMON Trojan Attack

Quick Answer
A quick roundup of the biggest cybersecurity stories of the week, from a massive breach at an edtech giant to supply chain attacks hitting AI developers, critical vulnerabilities in widely used platforms, and a landmark ransomware sentencing. In an ironic twist, cybersecurity firm Trellix disclosed a data breach after attackers gained access to a portion of its source code repository.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

A quick roundup of the biggest cybersecurity stories of the week, from a massive breach at an edtech giant to supply chain attacks hitting AI developers, critical vulnerabilities in widely used platforms, and a landmark ransomware sentencing.
Cybersecurity Firm Trellix Has Its Own Source Code Stolen
In an ironic twist, cybersecurity firm Trellix disclosed a data breach after attackers gained access to a portion of its source code repository. Trellix serves over 50,000 business and government customers worldwide and protects more than 200 million endpoints.
Trellix stated it has found no evidence that its source code release or distribution process was affected, or that its source code has been exploited. The company immediately began working with leading forensic experts and has notified law enforcement.
The timing suggests the breach may be related to a major supply chain attack targeting various open source applications to gain access to numerous companies. When a security vendor’s own code is targeted, the downstream risk to customers is significant, attackers with access to that code can study the product’s logic and engineer bypasses. This incident is a stark reminder that even cybersecurity companies must apply the same zero-trust principles they recommend to their clients.

MOVEit Is Back: Critical Authentication Bypass Threatens 1,400+ Exposed Instances
Progress Software has fixed a critical authentication bypass (CVE-2026-4670) and a privilege escalation (CVE-2026-5174) vulnerability in MOVEit Automation. Exploitation could lead to unauthorized access, administrative control, and data exposure.
Remote threat actors can exploit the flaw without any privileges on the targeted systems in low-complexity attacks that do not require user interaction. More than 1,400 MOVEit Automation instances are exposed online, and over a dozen are linked to U.S. state and local government agencies.
The vulnerabilities were reported privately by Airbus researchers, and upgrading to a patched release using the full installer is the only way to remediate the issue, as the system will experience an outage during the upgrade. Given that the Cl0p ransomware gang exploited a 2023 MOVEit zero-day to compromise over 2,100 organizations, security teams must treat this as an emergency, not a routine update.
DAEMON Tools Trojanized in Sophisticated Chinese-Linked Supply Chain Attack
Kaspersky describes the DAEMON Tools supply-chain attack as a sufficiently sophisticated compromise that evaded detection for almost one month. The attack is ongoing, and trojanized software includes DAEMON Tools versions from 12.5.0.2421 through 12.5.0.2434.
These compromised installers are notably signed with valid digital certificates belonging to the software’s developer, AVB Disc Soft. Thousands of infection attempts have been recorded across more than 100 countries, though attackers focused their post-compromise activity on high-value targets in government, scientific, manufacturing, and retail sectors in Russia, Belarus, and Thailand.
The payload establishes persistence and a backdoor on system startup, while also deploying an advanced RAT called QUIC RAT that can inject malicious code into legitimate processes to evade detection. Any organization with DAEMON Tools installed should immediately audit systems for unusual activity occurring on or after April 8, 2026.
PyTorch Lightning Supply Chain Attack: 11 Million Monthly Downloads Poisoned
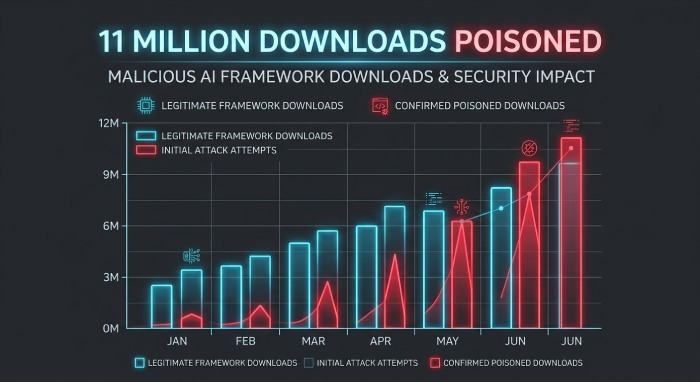
A malicious version of the PyTorch Lightning deep learning framework was published to PyPI on April 30, 2026, containing a hidden execution chain that silently downloads and executes a credential-stealing payload. PyTorch Lightning has over 11 million monthly downloads.
The payload, detected by Microsoft Defender as “ShaiWorm,” is an information-stealing malware that targets .env files, API keys, secrets, GitHub tokens, and data stored in Chrome, Firefox, and Brave browsers. It also interacts with cloud service APIs across AWS, Azure, and GCP to steal credentials and supports arbitrary system command execution.
Lightning AI quickly warned users about the risk, advising anyone who used version 2.6.3 to rotate all credentials and secrets immediately. The malicious release was removed and replaced with a safe version. AI and machine learning libraries are an increasingly attractive attack surface, developers with broad cloud access who routinely pull package updates represent a high-value target for supply chain attackers.
RMM Tools Weaponized in VENOMOUS#HELPER Phishing Campaign Hitting 80+ Organisations
A sophisticated phishing campaign has been uncovered, leveraging legitimate Remote Monitoring and Management (RMM) software to evade detection. The campaign, codenamed VENOMOUS#HELPER has impacted over 80 organizations, most of which are in the U.S.
Attackers used legitimate RMM software to establish persistence and bypass traditional security controls, allowing threat actors to blend in with normal IT activity and making detection and remediation far more challenging.
The campaign is assessed to be financially motivated, with overlaps pointing to an Initial Access Broker or ransomware precursor operation. Security teams should audit all RMM tools in use across their environments, enforce application allow-listing, and alert employees that legitimate IT helpdesks will never request remote access through unsolicited messages or emails.
Lotus Wiper Malware Deployed Against Venezuela’s Energy Sector
A destructive cyberattack using the Lotus Wiper malware targeted energy firms and utilities in Venezuela. Discovered on April 29, 2026, the attack aimed to disrupt operations by wiping critical systems. This incident is part of a broader trend of wiper malware being used for sabotage rather than financial gain, particularly against critical infrastructure in geopolitically sensitive regions.
Unlike ransomware attacks where data can potentially be recovered after paying, wiper malware permanently destroys data with no recovery path. The energy sector has become an increasingly popular target for destructive attacks, given its direct impact on national infrastructure and civilian populations. Operators of critical infrastructure must maintain air-gapped, offline backups and regularly test their incident response and recovery procedures.
Microsoft Exposes Large-Scale Credential Theft Campaign Targeting 35,000 Users in 26 Countries

Microsoft has disclosed details of a large-scale credential theft campaign observed between April 14 and 16, 2026, targeting more than 35,000 users across over 13,000 organizations in 26 countries, with 92% of targets located in the U.S. The majority of phishing emails were directed against healthcare and life sciences, financial services, professional services, and technology sectors.
The campaign used code of conduct-themed lures combined with legitimate email services to direct victims to attacker-controlled domains designed to steal authentication tokens. The use of legitimate email services to deliver phishing content is a growing trend specifically designed to defeat reputation-based filtering. Organisations must deploy advanced email authentication including DMARC, DKIM, and SPF, and train employees to be suspicious of any link requesting sign-in credentials, even if the sending email address appears legitimate.
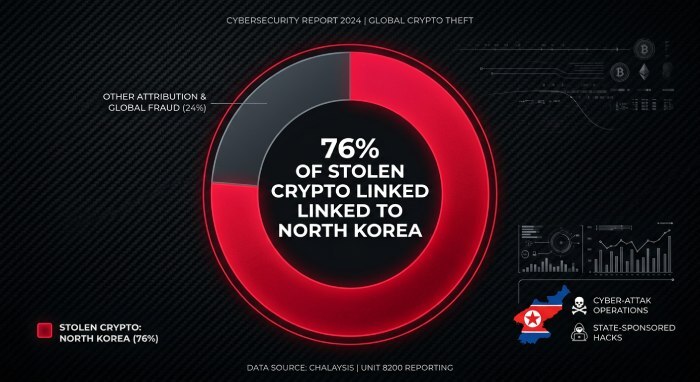
North Korea-Linked Actors Steal 76% of All Cryptocurrency Taken in 2026
A new analysis revealed that 76% of all cryptocurrency stolen in 2026 has been traced to North Korean threat actors, with billions of dollars in losses attributed to these campaigns. The findings have prompted renewed calls for international cooperation and enhanced security measures in the crypto sector.
A North Korea-linked threat actor also launched a social engineering campaign this week specifically targeting Web3 company executives to gain access to cryptocurrency wallets, using tailored phishing and social engineering tactics against founders and top executives.
The scale of North Korea’s crypto theft operations now represents a significant geopolitical and financial threat. Cryptocurrency firms and Web3 executives should implement hardware security keys for account access, restrict wallet signing permissions to multi-party approval workflows, and maintain extreme vigilance against social engineering attempts posing as investment or partnership inquiries.
France Titres Government Data Breach Exposes Citizen Records
France Titres, the French government agency responsible for issuing and managing administrative documents, disclosed a significant data breach this week. The breach was confirmed after a threat actor claimed responsibility for stealing citizen data. The agency is currently investigating the breach and has notified affected individuals and relevant authorities.
Government identity agencies hold some of the most sensitive personal data imaginable, passport records, identity card information, and address details. A breach at such an entity creates significant risk of identity fraud and targeted phishing for years to come. Citizens whose data may have been exposed should monitor their credit and identity closely and remain alert for phishing attempts that reference their personal details to appear credible.
Vect 2.0 Ransomware Behaves as a Wiper Due to Coding Flaw
A new variant of the Vect 2.0 ransomware has been observed acting as a wiper due to a design error. Instead of encrypting files for ransom, the malware irreversibly destroys data, leaving victims with no recovery options. This shift from extortion to destruction underscores the evolving threat landscape.
Whether intentional sabotage or an accidental bug, the outcome for victims is equally devastating. This variant highlights that relying on paying a ransom as a recovery strategy is never a safe assumption, organisations must maintain tested, offline backups and have a rehearsed recovery plan that does not depend on attacker cooperation.
Two US Cybersecurity Professionals Sentenced to Prison for BlackCat Ransomware Attacks
The U.S. Department of Justice announced the sentencing of two cybersecurity professionals to four years each in prison for their role in facilitating BlackCat ransomware attacks in 2023.Ryan Goldberg, 40, of Georgia, and Kevin Martin, 36, of Texas, were accused of deploying the ransomware against multiple victims located throughout the U.S.
This case is a significant reminder that cybersecurity expertise is no defence against prosecution when it is applied criminally. Law enforcement is increasingly focused on identifying and prosecuting individuals who use professional skills to facilitate ransomware, even when they serve as intermediaries or technical operators rather than leaders of the criminal enterprise.
PhantomCore Exploits TrueConf Video Conferencing Software to Breach Russian Networks
A pro-Ukrainian hacktivist group called PhantomCore has been attributed to attacks actively targeting servers running TrueConf video conferencing software in Russia since September 2025.
The exploitation of video conferencing and collaboration platforms has become a persistent attack vector, particularly in the context of geopolitical conflict. This incident is a reminder that collaboration tools, especially those deployed at scale across an organisation, represent a significant attack surface. Administrators must ensure these platforms are patched promptly and access is restricted through multi-factor authentication and network segmentation.
Amazon SES Increasingly Abused to Send Sophisticated Phishing Emails
Kaspersky reports that the Amazon Simple Email Service (SES) is being increasingly abused to send convincing phishing emails that can bypass standard security filters and render reputation-based blocks ineffective.
SES is a legitimate, trusted email delivery service used by thousands of businesses, which is precisely why attackers are exploiting it. Because emails sent via SES originate from Amazon’s infrastructure, they often pass IP reputation checks that would otherwise block malicious senders. Organisations should ensure their email security goes beyond reputation-based filtering and incorporates content inspection, anomalous link detection, and robust DMARC enforcement to catch emails that abuse legitimate cloud platforms.
Ukrainian Police Bust Roblox Account Hacking Ring That Stole 610,000 Accounts

Ukrainian law enforcement arrested three individuals on April 29, 2026, following an investigation into a cybercriminal operation that compromised more than 610,000 Roblox gaming accounts between October 2025 and January 2026. The operation was run out of Lviv by a 19-year-old organiser who recruited two accomplices. Rather than cracking passwords, the attackers deployed malicious software that harvested browser session cookies, allowing them to authenticate to victim accounts without needing credentials, a technique that bypasses passwords, SMS OTPs, and many 2FA implementations.
The hackers included at least 357 high-value “elite” accounts in their haul, making around $225,000 from selling access to them. The accounts were sold on a Russian website and in closed online communities.
This case is a reminder that session cookie theft is a growing and underappreciated threat. Browser-based session hijacking can bypass even MFA, making it critical to regularly terminate unused sessions and use isolated browser profiles for high-value accounts.

Critical cPanel Vulnerability Actively Exploited Against Government and MSP Networks
A critical flaw in cPanel and WebHost Manager (WHM) has come under active exploitation in the wild. The vulnerability, tracked as CVE-2026-41940, could result in an authentication bypass and allow remote attackers to gain elevated control of the control panel. In some cases, the attacks have led to a complete wipe of entire websites and backups.
A previously unknown threat actor has been observed targeting government and military entities in Southeast Asia, alongside a smaller cluster of managed service providers (MSPs) and hosting providers in the Philippines, Laos, Canada, South Africa, and the U.S., by exploiting this cPanel vulnerability.
CISA has added the bug to its Known Exploited Vulnerabilities catalog and ordered federal agencies to patch immediately. Website owners and hosting providers running cPanel must apply the emergency patch without delay. The combination of government targets and MSP victims in this campaign suggests a deliberate effort to compromise multiple downstream customers through a single attack vector.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.