Secure Passkey Protection, Dismantling Lighthouse Phishing, Manufacturers Need Protection

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Secure Passkey Protection, Dismantling Lighthouse Phishing, Manufacturers Need Protection
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format


The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Secure Passkey Protection, Dismantling Lighthouse Phishing, Manufacturers Need Protection
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-33860">
<source src="https://media.mailhop.org/dmarcreport/images/2025/11/Secure-Passkey-Protection-Dismantling-Lighthouse-Phishing-Manufacturers-Need-Protection.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M29S">2:29</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-33860" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-33860" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-33860" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-33860" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/secure-passkey-protection-dismantling-lighthouse-phishing-manufacturers-need-protection/&t=Secure Passkey Protection, Dismantling Lighthouse Phishing, Manufacturers Need Protection" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/secure-passkey-protection-dismantling-lighthouse-phishing-manufacturers-need-protection/&url=Secure Passkey Protection, Dismantling Lighthouse Phishing, Manufacturers Need Protection" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2025/11/Secure-Passkey-Protection-Dismantling-Lighthouse-Phishing-Manufacturers-Need-Protection.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/secure-passkey-protection-dismantling-lighthouse-phishing-manufacturers-need-protection/" class="input-link input-link-33860" title="Episode URL" readonly />
<button class="copy-link copy-link-33860" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-33860” readonly/>
<button class="copy-embed copy-embed-33860" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Hello people!
It is the third week of November, and as promised, we are back again with our latest edition of cyber news. Meanwhile, we hope you have been able to safeguard your data from the cybercrooks. Even though they are getting sophisticated with every attack, it is up to us to bolster our data and networks. And that is possible when you stay fully prepared with cyber knowledge and awareness to combat the malicious activities of threat actors.
SPF, DKIM, and DMARC work together to strengthen email security by preventing spoofing and ensuring messages come from legitimate senders**.
This week, we will discuss the latest trend of switching to passkeys to protect crucial business data. Next, our focus will be on the Lighthouse phishing-as-a-service operations. Lastly, we will focus on why manufacturers are prone to ransomware attacks and how to overcome the threat.
**Passkeys over weak passwords - new tactic to combat cyberattacks Threat actors have already come a long way-thanks to easy AI access and digital advancements around the globe. We are living in a time where even some of the intricate security setups are not adequate to tackle the malicious attempts of the cybercriminals. To make things worse, employees are still using weak passwords in 2025. Organizations are therefore gradually moving to passwordless solutions to safeguard critical business data.

Multifactor Authentication is still a valid alternative. But experts feel that using MFA alone is not enough to protect your data from threat actors. A massive 96% of CISOs believe that MFA is not competent enough to **survive the contemporary threat landscape. Organizations have come to realize that password hygiene has its own set of disadvantages and that they need something better to protect their business data. So, gradually, they are moving to a completely new solution altogether - passwordless systems.
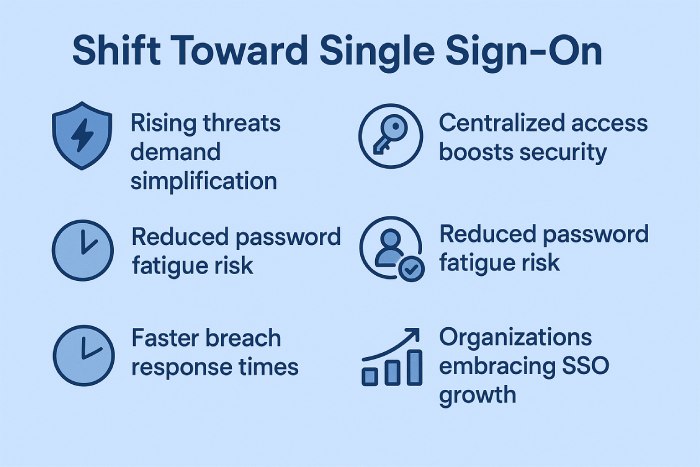
According to a survey conducted by Dark Reading, one-third of the participants have entirely shifted to Single Sign-On (SSO) or a passkey system to log into their accounts. One-fifth of the participants depend on password managers, which, again, is a comparatively safer solution for password authentication. 17% of the participants are coerced into using **secure passphrases that are random in nature yet easy to remember.
Cybersecurity experts believe that more and more organizations will eventually move to SSOs as the threat landscape keeps evolving .
Google seeks help from the US court to dismantle Lighthouse phishing-as-a-Service operations! Google needs the assistance of the US court to stop the Lighthouse Phishing-as-a-Service operations. This is a smart move made by the tech company to make the most out of **legal systems to combat cybercrime.
Google sought legal help as the cybercrooks have been abusing Google and other similar tech brands by misusing their trademarks, logos, and other brand assets. A **Google spokesperson stated **that as many as 107 fake websites were “featuring Google’s branding on sign-in screens” to trick people and earn their trust.
Basically, cybercrooks who use Lighthouse services tend to send malicious text messages to unsuspecting users, especially employees in any organization. These threat actors use the brand assets of popular companies to boost the credibility of the messages and hope to compel the message recipients to click on fraudulent links or share sensitive data.
This is not the first time that a renowned tech company has sought the court’s help. There are several other well-known companies that have started seeking legal help to fight cybercriminals. For example, back in September, Microsoft got the court’s order to seize as many as 338 websites. These fraudulent websites were using a phishing kit called RacoonO365 to get access to Microsoft 365 credentials. In August, too, something similar happened when the US Justice Department, with the help of the FBI and other enforcement agencies**, took down four servers and nine domains of the BlackSuit Ransomware group.
Why do manufacturers need to take more precautionary steps against ransomware? Ransomware attackers love targeting manufacturers. From **German manufacturer Schumag to Sensata Technologies, and then to Nucor, ransomware gangs targeted every manufacturing company, disrupting production and distribution.
According to the software firm Check Point, the global manufacturing sector experiences 1585 weekly attacks on average.

While some of the attacks are carried out by state-sponsored hacking groups for industrial espionage purposes, other ransomware attacks are financially motivated. The main reason behind targeting the **manufacturing sector **is the critical nature of its operational continuity.
That’s exactly why manufacturers must start building a robust, impenetrable safety system to prevent any cyberattack. It is advisable to use crisis communication strategies and intelligence-led defence systems to safeguard intellectual properties. Experts recommend investing in data-loss prevention, monitoring, and advanced detection systems.
Cyber resilience is no longer a luxury but a necessity for the manufacturing sector. It not only brings in the element of competitive advantage but also protects the future of a manufacturing business.
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.