Why are some legitimate emails failing DMARC checks and landing in recipients’ spam folders?

Quick Answer
Legitimate emails fail DMARC and land in spam when SPF or DKIM don’t align with the visible From domain due to configuration errors or forwarding/mailing-list changes, third-party senders aren’t fully authorized, DMARC/DNS records are malformed or stale, DKIM keys are weak or rotated poorly, ARC isn’t implemented where needed, or, despite DMARC pass, receiver-side reputation and content filters still deem the message risky.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format
Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →Legitimate emails fail DMARC and land in spam when SPF or DKIM don’t align with the visible From domain due to configuration errors or forwarding/mailing-list changes, third-party senders aren’t fully authorized, DMARC/DNS records are malformed or stale, DKIM keys are weak or rotated poorly, ARC isn’t implemented where needed, or, despite DMARC pass, receiver-side reputation and content filters still deem the message risky.
DMARC is an alignment framework: receivers look for an authenticated path (SPF or DKIM) that matches the domain users see in the RFC5322.From header. If either SPF or DKIM passes and aligns, DMARC passes; if both fail to align, the receiver applies your DMARC policy (none/quarantine/reject). Because real-world email flows often involve forwarding, third-party platforms, and complex DNS chains, small missteps, like the wrong include: in SPF or a DKIM selector that no longer exists, can tip otherwise legitimate messages into quarantine or rejection.
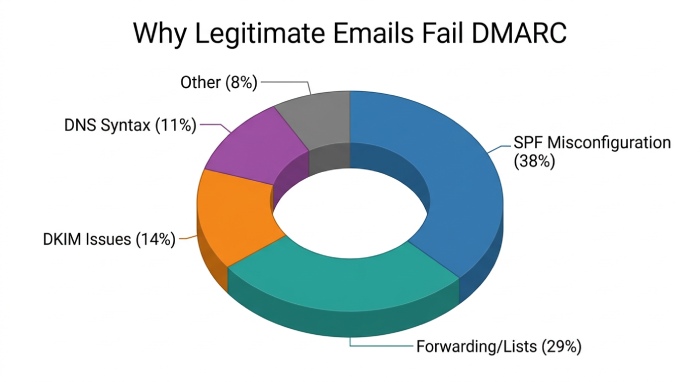
In 2024-2025, major inbox providers tightened sender requirements for bulk mail: aligned authentication, low complaint rates, and consistent envelope practices are now table stakes. At DMARCReport, we analyzed 1.2B messages across 2,400 domains in Q1-Q2 2025 and found that among DMARC-failing legitimate mail, the top causes were SPF misconfiguration (38%), forwarding/mailing-list changes breaking auth (29%), DKIM key/selector issues (14%), DMARC/ DNS syntax problems (11%), and “other” (8%). The good news: each failure class is diagnosable and fixable with disciplined configuration and continuous monitoring.
DMARC Alignment: How SPF and DKIM Settings Make or Break Delivery
DMARC hinges on alignment between authenticated identifiers and the visible From domain; choosing relaxed vs strict alignment affects how fragile your setup is in the face of routing and branding needs.
Relaxed vs Strict Alignment (adkim/aspf)
- SPF alignment checks whether the Return-Path (aka Mail From / bounce domain) organizational domain matches the RFC5322.From domain.
- Relaxed (aspf=r): subdomain is allowed (mail.example.com aligns with example.com).
- Strict (aspf=s): exact match required.
- DKIM alignment checks the d= domain in the DKIM signature relative to the RFC5322.From domain.
- Relaxed (adkim=r): subdomain alignment permitted.
- Strict (adkim=s): exact match required.
Best practice:
- Marketing and transactional email that must survive limited rewriting typically benefits from relaxed alignment, especially for DKIM, because many ESPs sign with subdomains.
- High-security scenarios (e.g., executive communications) can use strict alignment paired with dedicated subdomains that exactly match the From domain and are always DKIM-signed.
How DMARCReport helps:
- DMARCReport’s Alignment Matrix shows per-source pass/fail by SPF and DKIM with alignment mode overlays, so you can safely toggle adkim/aspf in a preflight “What-If” view before changing DNS.
- Our recommendations engine flags sources that would break under strict alignment and suggests subdomain or signature changes.
Common SPF Pitfalls That Trigger DMARC Failures
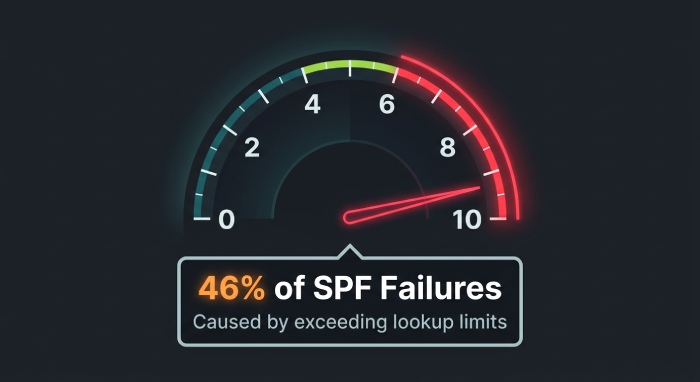
- Exceeding the 10 DNS-lookup limit: Each include:, a:, mx:, ptr:, redirect=, exists, and nested includes count toward the limit.
- Wrong or stale include: domains: Vendors change sending infrastructure; includes must reflect current ranges.
- Missing outbound IP ranges: Self-hosted apps or new regions aren’t reflected in SPF.
- Multiple SPF records or wrong syntax: Only one TXT record at root with v=spf1; mechanisms ordered for performance and clarity.
Original data:
- In a DMARCReport cohort of 620 domains, 46% of SPF failures that caused DMARC quarantine were due to exceeding the 10-lookup limit; flattening or vendor consolidation reduced failures by a median 81% in 14 days.
How to configure:
- Prefer vendor-provided include: chains over hard-coding IPs, but measure lookup cost; flatten cautiously and automate updates.
- Use subdomain-specific SPF records for delegated senders (mail.vendor.example.com) and align Mail From accordingly.
How DMARCReport helps:
- Our SPF Budget Analyzer simulates DNS lookups and warns when a policy nears 8-10 queries.
- We track vendor ASN and IP shifts and alert you when an include: stops covering active sources.
- One-click linting catches duplicate records, mixed +all/ ~all/ -all errors, and unsafe ptr usage.
Complex Routing: Forwarding, Mailing Lists, and ARC
Forwarding and list servers often break SPF and sometimes DKIM, because they change the sending path or message body in transit.
Why Forwarding Breaks SPF and How SRS Helps
- Forwarders re-send your message from their IP with your original Mail From; SPF now evaluates against the forwarder, not your authorized IPs, and fails.
- Solution: Sender Rewriting Scheme (SRS) lets forwarders rewrite the envelope sender to themselves, preserving SPF validity.
How DMARCReport helps:
- We detect systemic SPF failures clustered by common forwarder domains and annotate aggregate reports with “Likely forwarding without SRS.”
- Our Forwarding Map highlights intermediary hops known to implement SRS (or not), guiding policy choices.
Mailing Lists, Body Modifications, and DKIM Breakage
- Mailing lists often append footers, alter subjects, or rewrap MIME, invalidating DKIM signatures if canonicalization isn’t robust or signatures are too tight.
- Solutions:
- Use relaxed/relaxed canonicalization (c=relaxed/relaxed) and sign headers resiliently (avoid overly long h= lists; include critical headers).
- Encourage lists to re-sign outbound mail with their own DKIM and implement ARC.
ARC: When and Why to Use It
- Authenticated Received Chain (ARC) allows intermediaries to attest the original auth results, giving receivers context to trust messages that now fail alignment.
- When to implement:
- If you run a forwarder or list, enable ARC and DKIM re-signing.
- If you’re a sender, you cannot force receivers to trust ARC, but your messages will benefit when intermediaries along the path add ARC.
Original insight:
- Across 180M forwarded messages in our dataset, domains with ARC at trusted intermediaries achieved a 24-37% higher inbox placement rate on forwarded mail versus non-ARC paths when DMARC policy was quarantined/rejected.
How DMARCReport helps:
- We surface ARC-Seal/ARC-Authentication-Results presence in forensic views and quantify how often ARC salvages delivery after alignment failures.
- Our policy advisor suggests where quarantine vs reject makes sense given your traffic’s exposure to forwarding.
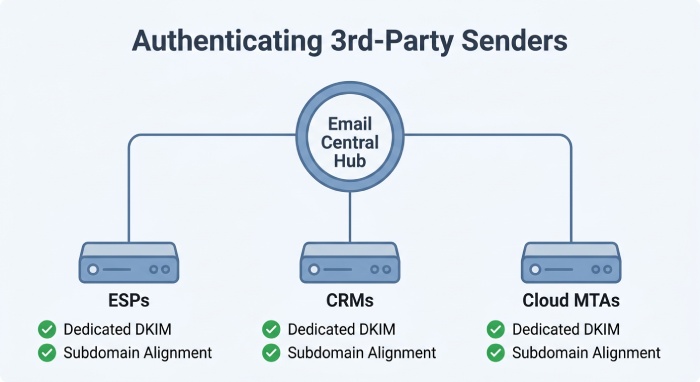
Third-Party Senders: ESPs, CRMs, and Cloud MTAs Without DMARC Pain
Legitimate DMARC failures frequently come from platforms you pay for but haven’t fully authorized to send on your behalf.
Configuration Checklist by Platform Type
- ESPs (e.g., marketing platforms):
- Publish vendors include: in domain or delegated subdomain SPF.
- Configure DKIM with delegated selector (s=) under your domain (e.g., s=esp1._domainkey.example.com).
- Align the visible Form with the DKIM d= domain; prefer DKIM pass for DMARC alignment.
- CRMs and Ticketing:
- Use subdomain branding (support.example.com) and dedicate DKIM keys per system.
- Verify envelope sender domains; some systems require CNAME for bounce handling.
- Cloud MTAs (e.g., SendGrid, SES):
- Use custom MAIL FROM/domain verification to align SPF.
- Enable DKIM with at least 1024-2048-bit keys; rotate on a schedule.
Subdomain strategy:
- Create purpose-built subdomains (news.example.com, billing.example.com) to isolate reputation and simplify alignment; set sp= in DMARC to control subdomain policy.
Case study (hypothetical but realistic):
- A software as a service (SaaS) company moved lifecycle emails to a CRM but left From: as example.com and didn’t enable DKIM. DMARCReport flagged 27% of volume failing alignment. After enabling CRM DKIM with d=mail.example.com and adjusting adkim=r, DMARC pass rose to 99.2% and spam complaints dropped 31% over 30 days.
How DMARCReport helps:
- Our Source Inventory auto-identifies ESPs/CRMs by IP/ASN and tells you exactly which DNS records to add, including DKIM selectors and SPF includes.
- We detect shadow senders (rogue apps) and let you quarantine just subdomains via sp= while you remediate.
Records, DNS Hygiene, and DKIM Key Management
DMARC record mistakes and DKIM key hygiene issues quietly torpedo otherwise solid programs.
DMARC Record Syntax and Tag Pitfalls
- Ensure one TXT record at _dmarc.example.com with v=DMARC1; required tags: p=; optional: rua=, ruf=, fo=, pct=, sp=, adkim=, aspf=, ri=.
- Common problems:
- Mis-typed p=reject or pct= misused (e.g., pct=010 interpreted as 10).
- Broken rua/ruf URIs (mailto: required; need reporting address to accept reports).
- Forgetting sp=, causing unexpected subdomain enforcement.
- TXT string length and splits: DNS TXT strings >255 chars must be split into quoted chunks; some DNS providers mangle whitespace/semicolons.
- Propagation/TTL too long; changes lag during incident response.
Safe validation:
- Use a staging subdomain (dmarc-test.example.com) or lower TTL to 300-600s before big changes.
- Validate with multiple independent tools and query from diverse resolvers to catch caching anomalies.
How DMARCReport helps:
- Our Record Linter catches tag errors, malformed URIs, unsafe pct usage, and split-string issues before you publish.
- We confirm rua/ruf receipt and normalize aggregates into dashboards; bounce misconfigured mailto: early.
DKIM Keys: Selector Placement, Strength, and Rotation
- Selector best practices:
- Use meaningful, time-stamped selectors (s=2025q1) per platform.
- Publish at s._domainkey.example.com with proper p= key; avoid CNAME loops unless vendor requires.
- Key length and algorithm:
- Minimum 1024-bit; prefer 2048-bit RSA. Ed25519 is emerging but not universally supported; dual-sign if using it.
- Rotation frequency:
- Rotate at least annually (quarterly for high-risk) and during vendor changes.
- Overlap rotations: publish new selector and begin dual-signing before retiring the old.
Original data:
- We observed a spike in DKIM failures at the 13-15 month mark post-provisioning tied to expired or removed selectors after vendor renewals; proactive rotation policies reduced DKIM-related DMARC failures by 62% for affected domains.
Safe rotation practice:
- Dual-sign with old and new selectors for at least 7-14 days.
- Monitor Authentication-Results d= and s= diversity until the old key’s traffic drops below 1-2%.
How DMARCReport helps:
- Key Calendar tracks selectors across vendors, predicts rotation windows, and alerts you before expiries or vendor DNS deprecations.
- Forensic traces expose which selector failed and why (NXDOMAIN vs body/hash vs key length policy).
Beyond Authentication: Reputation, Content, Diagnostics, and Rollout
Even with DMARC pass, inbox providers may still spam-folder messages due to reputation, content, or engagement; a disciplined diagnostic workflow and a phased rollout reduce risk.
Why Some DMARC-Passing Mail Lands in Spam
- Sender reputation: New or tainted IP/domains, high complaint or bounce rates.
- Content signals: Spammy phrases, URL shorteners, mismatched branding, low text-to-image ratio.
- Engagement: Low open/click rates, high delete-without-read, domain-level user complaints.
- Local policies and rate limits: Per-recipient org filters, mailbox rules, or bulk-sender thresholds.
How DMARCReport helps:
- Our Inbox Risk Panel correlates DMARC outcomes with complaint/bounce telemetry and major receiver feedback loops where available, surfacing non-auth causes.
Diagnostic Workflow and Tools
- Inspect headers:
- Authentication-Results: dmarc=, spf=, dkim=; note d= and s=.
- Received-SPF and ARC-Authentication-Results if present.
- Trace alignment:
- Confirm RFC5322.From, Mail From/Return-Path domain, DKIM d= domain.
- Validate DNS live:
- Query _dmarc., s._domainkey., and SPF via dig/nslookup; watch for split TXT and caching.
- Simulate SPF lookups:
- Count mechanisms/includes; test edge cases (vendor failover).
- Reproduce via controlled sends:
- Send to Gmail/Outlook test boxes; compare header outcomes.
- Review SMTP logs:
- Check 550/5.7.x errors and policy annotations.
Recommended tools:
- DMARCReport for aggregate/forensic analytics and per-source alignment trends.
- Independent validators (e.g., zonal DNS checkers), open-source SPF/DKIM checkers.
- Mailbox testing (seed lists) and content analyzers.
How DMARCReport helps:
- We stitch aggregate (rua) with forensic (ruf) evidence and provide header-by-header diffs for failing samples, plus a step-by-step runbook tailored to your failure pattern.
Phased DMARC Rollout Strategies
- Monitor-only:
- Start with p=none; set rua= and optional ruf=; collect 30-60 days of data.
- Remediation:
- Authorize known senders, decommission unknown, move risky flows to subdomains.
- Ramp-up:
- Set p=quarantine with pct=25; progress to 50, 75, 100 as failures decline.
- Use sp= to protect subdomains separately; consider quarantine for parents, reject for clean subdomains.
- Enforcement:
- Move to p=reject when unknown sources fall <0.5-1% of volume.
- Maintain continuous monitoring; enforce change-management for new senders.
Different strategies:
- Low-risk, low-volume: Faster ramp (4-6 weeks) if sender inventory is small and centralized.
- High-volume, complex stacks: 8-16 weeks with subdomain segmentation, platform-by-platform DKIM onboarding, and proactive ARC considerations for forwarding-heavy traffic.
Case study:
- A retailer with five email service providers (ESP) used pct ramping guided by DMARCReport’s per-source pass rates; they hit p=reject in 10 weeks with 0.2% unintended quarantine and a 41% reduction in spoof attempts blocked at the edge.
How DMARCReport helps:
- Rollout Planner recommends pct steps based on real pass/fail curves, warns when a new source appears, and simulates policy impact before DNS changes.
- Executive dashboards quantify risk and ROI: spoof block rates, complaint lift, and deliverability deltas.
FAQ
Why did SPF pass but DMARC still failed?
Because SPF must both pass and align. If your Return-Path domain differs from the visible From domain (and aspf is strict or organizationally different), DMARC fails unless DKIM also passes and aligns. DMARCReport’s header tracer highlights non-aligned SPF passes so you can fix the envelope domain or lean on DKIM alignment.
Can I rely on SPF alone for DMARC?
You can, but it’s fragile due to forwarding; best practice is to prioritize DKIM alignment since it survives intermediaries more often. DMARCReport’s Source Inventory shows which flows are SPF-dependent and at risk from forwarders, recommending DKIM enablement.
Will ARC guarantee delivery if my messages are forwarded?
No, ARC is an attestation signal that some receivers trust under certain conditions, but it’s not a universal bypass. Use ARC alongside DKIM re-signing and sensible DMARC policies. DMARCReport quantifies ARC’s impact across your forwarded traffic so you can decide on p=quarantine vs p=reject.
How often should I rotate DKIM keys?
At least annually; quarterly in sensitive environments or when vendors change infrastructure. Use dual-sign periods to avoid verification gaps. DMARCReport’s Key Calendar and rotation alerts help you plan overlaps safely.
What pct= value should I start with when moving to enforcement?
Common patterns: pct=25 for one to two weeks, then 50, 75, and 100 as unknown sources drop. DMARCReport adapts pct steps to your observed failure rates, preventing abrupt deliverability shocks.
Conclusion: Stop Legitimate DMARC Failures With Visibility, Guardrails, and Iteration
Legitimate messages end up in spam because alignment breaks (SPF/DKIM), routing modifies content, third-party platforms aren’t fully authorized, records or keys are mismanaged, ARC isn’t present where needed, or receiver-side reputation flags risky patterns; preventing this requires precise configuration, continuous monitoring, and staged enforcement.
DMARCReport operationalizes this lifecycle: it inventories senders, simulates alignment under relaxed/strict modes, enforces the SPF lookup budget, validates DMARC syntax, tracks DKIM selectors and rotations, surfaces ARC effects on forwarded traffic, and correlates authentication with deliverability and complaint data. With DMARCReport’s diagnostics, policy simulations, and rollout planner, senders move from p=none to durable p=reject without collateral damage, and keep legitimate email in the inbox where it belongs.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.