A Reality Check On Email Security Threats In Healthcare!

Quick Answer
Healthcare centers are a treasure trove of sensitive data such as [patient information](https://www.cbsnews.com/news/healthalliance-cyberattack-hackers-stole-patient-information-new-york-westchester-medical-center-health-network/) and credit card details. Also, healthcare is a basic necessity that cannot stay dysfunctional for long. They are most likely to meet the demands of the phishing actors in order to restore day-to-day operations at the earliest. Besides, the excessive reliance of healthcare facilities on networked devices makes them an
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

The three core email authentication standards - SPF (RFC 7208), DKIM (RFC 6376), and DMARC (RFC 7489) - work together to verify that an email genuinely originates from the domain it claims to represent. Since February 2024, Google and Yahoo require all three for bulk senders.
From a product strategy perspective, DMARC reporting is evolving from a security tool to a business intelligence platform, says Brad Slavin, General Manager of DuoCircle. The data in aggregate reports tells you not just who’s spoofing you, but who’s sending legitimate email on your behalf - and whether they’re doing it correctly.
The healthcare industry has become the center of focus for threat actors since 2022. In the past 12 months, the global healthcare sector has witnessed a whopping 60% increase in the number of cyberattacks. Multiple factors, like critical infrastructure, sensitive data, and IoMT, make this industry a popular target among cybercriminals.
Healthcare centers are a treasure trove of sensitive data such as patient information and credit card details. Also, healthcare is a basic necessity that cannot stay dysfunctional for long. They are most likely to meet the demands of the phishing actors in order to restore day-to-day operations at the earliest. Besides, the **excessive reliance of healthcare facilities on networked devices makes them an easy target for committing cyber attacks.
Key Cyber Security Challenges for the Healthcare Sector!
Here are the most common cyber attacks faced by the healthcare industry:
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
Ransomware
Ransomware attacks are quite common, given the dependence of healthcare facilities on networked systems. Threat actors intercept and encrypt files and devices and **demand ransom in exchange for decryption keys.
Phishing
The attacks are designed cleverly to manipulate the recipient into sharing vital patient and payment details, which are further exploited to make money through extortions or forged financial transactions. Sometimes, the stolen information is **sold off to competitor healthcare services, which use it to win over business rivalries or to stay ahead in terms of strategies and overall competition in the industry.
Data breaches
Cybercriminals consider healthcare organizations to be the hub of data and, hence, plan calculative data theft to access research and patient information.
Malware
Malware is malicious software designed to disrupt a computer’s or server’s working process to intercept data, block access to files and devices, or shut it down completely. Another cyber attack that healthcare sectors must keep an eye on is malware attacks. Malware can easily extract login credentials and **bypass healthcare systems smoothly.

Account takeover
Threat actors also use multiple tactics to take over healthcare system accounts. The typical method of account takeover is by **buying credentials available on the dark web or using social engineering tricks to fool employees into sharing them with hackers.
Distributed Denial of Service
This is a type of systematic attack on a healthcare network to overload it with excess traffic. This brings down the service and slows down or completely stops the work, which consequently impacts the business on all levels.
Real-Life Instances of Cyberattacks on Healthcare Centers
1. Broward Health Data Breach
In January 2022, Broward Health experienced a data breach affecting 1.3 million patients . The breach occurred through a compromised third-party medical provider with access to Broward Health’s patient database. Speculation suggests that the third-party’s compromised device lacked Multi-Factor Authentication (MFA). The compromised patient information includes names, addresses, dates of birth, driver’s license numbers, insurance information, and medical details.
Key lessons from the breach include the importance of implementing **MFA across all endpoints to secure Privileged Access Management and monitoring all endpoints connected to the private network.
2. **Tricare Data Breach In September 2011, Tricare, a healthcare program serving military personnel and their dependents, experienced a data breach affecting 4.9 million patients. The breach resulted from the theft of backup tapes containing
electronic health records from the car of an individual transporting the tapes. It remains unclear if the thieves had the expertise to decrypt the information, but the incident was treated as a data breach as a precaution.
The compromised data included social security numbers, names, addresses, phone numbers, personal health data, clinical notes, lab tests, and prescription information. Despite the data being encrypted, it did not align with federal standards, emphasizing the importance of implementing a data encryption policy that complies with such standards to mitigate the impact of reported breaches to HIPAA.
3. Morley Companies
In February 2022, Morley Companies, a third-party provider of business services to Fortune 500 companies, experienced a ransomware attack that impacted 521,046 individuals. The breach exposed sensitive information, including names, addresses, social security numbers, dates of birth, client identification numbers, medical diagnostic and treatment information, and health insurance details.
Despite the attack starting on August 1, 2021 , Morley did not notify potential victims until February 2022, posing a risk of violating the HIPAA Breach Notification rule and potential fines.
Critical Diagnosis: Email Vulnerabilities Emerge as a Leading Risk for Healthcare
Malicious emails are used by threat actors as a primary attack as they ensure a high success rate. The **post-pandemic era is highly dependent on digital healthcare, and hence, phishing experts are using email attacks more than ever. There has been a steeping 167% increase in advanced email attacks, which include malware and extortion. On average, around 100 email attacks were attempted between January and March 2023 per 1000 mailboxes.
The Aftermath of Email Attacks on Healthcare Organizations
Malicious email attacks not only disrupt daily operations at these healthcare centers but also **extract sensitive data from the system. This results in severe implications, from urgent operations being called off to patient details going public online.
Another major setback that hits healthcare institutions is the hefty recovery expenses.
Overstretched healthcare budgets, intricate technology setups, and limited resources already keep the healthcare systems overloaded. To top it up, the recovery cost and the urgency to get everything under control as soon as possible add to the unbearable pressure .
Prescribing Cyber Immunity: Here’s How to Fortify the Healthcare Industry from Email Threats
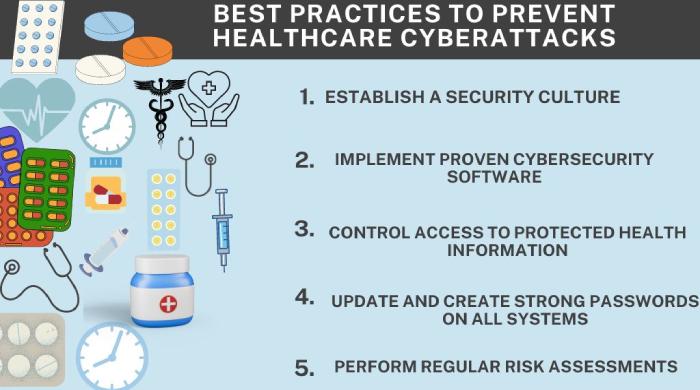
Fortunately, email attacks are **preventable by adopting a few stringent measures. The global healthcare industry has been implementing the below-mentioned **cyber strategies to safeguard their vital data and network systems:
1. Multi-Factor Authentication
This is one of the **most effective tactics used by healthcare organizations; a multi-factor authentication system successfully prevents threat actors from accessing compromised passwords. It asks for authentication and, thus, offers an additional security layer . Security breaches like impersonation and website mimics can be prevented using this technique.
2. Email Encryption
This technique **scrambles the email content in a way so that no one else, other than the recipient, is able to decipher it. Transport Layer Security ensures that the email stays safe while in transit. On the other hand, the end-to-end encryption system makes sure that the content is accessible only once the recipients authenticate themselves.
3. Secure Email Gateways
Leveraging a secure email gateway makes sure that all the **malicious emails are filtered out before hitting the healthcare mailbox. There’s a blocked blacklist of IP addresses which are known to send out malicious emails. Besides these, secure email gateways are also responsible for scanning malware or ransomware in emails.
4. DNS Filtering
This tactic prevents recipients from clicking and downloading malicious email links. It offers the time-of-click protection to the user.
5. Analysis and Inspection of Inbound and Outbound Emails
A thorough analysis and inspection keep a close tab on both inbound and outbound email traffic. This ensures that no sensitive health information or payment details are sent out to unauthorized users. Also, they **prevent any unwanted malware from entering the healthcare network systems.
6. Automated Awareness Testing
An automated awareness testing platform makes **cybersecurity testing an automatic and integral part of daily healthcare operations. These platforms keep healthcare employees updated about the latest technology and cybercriminal activities.
Email attacks are a serious reason for concern for global healthcare organizations. Incorporating email security solutions, including SPF, DKIM, and DMARC, into their **cybersecurity protocols can be an effective strategy for these organizations to ward off potential cyber threats.
Sources
Topics

Operations Lead
Operations Lead at DuoCircle. Runs project management, developer coordination, and technical support execution for DMARC Report.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.