Manufacturer Hit Cyberattack, Fake Teams Breach, AI Targets MSMEs

Quick Answer
Here’s a quick roundup of the latest cybersecurity developments grabbing eyeballs, from crucial infrastructure suppliers being targeted by cybercrooks to high-end phishing campaigns impersonating Microsoft Teams, and the surge of AI-driven cyberattacks primarily targeting Indian MSMEs. These cyber mishaps highlight how cyber threats are eventually becoming more sophisticated, industry-specific, and increasingly difficult to identify.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Here’s a quick roundup of the latest cybersecurity developments grabbing eyeballs, from crucial infrastructure suppliers being targeted by cybercrooks to high-end phishing campaigns impersonating Microsoft Teams, and the surge of AI-driven cyberattacks primarily targeting Indian MSMEs. These cyber mishaps highlight how cyber threats are eventually becoming more sophisticated, industry-specific, and increasingly difficult to identify.
A critical infrastructure equipment manufacturer falls prey to a cyberattack!

Threat actors managed to break into the networks of Itron, the supplier of critical devices used for measuring water and energy use. Itron revealed the cyber incident on Friday. It “took action to remediate and remove the unauthorized activity.” The infrastructure vendor believes the cyber intrusion occurred on April 13.
Itron has claimed that the cybercrooks could not access any customer data. Also, there has been no “subsequent unauthorized activity within its corporate systems.”
Itron has already filed the details with the SEC and has mentioned that the cyberattack could not affect its core operations. Also, Itron expects the insurance provider to cover “a significant portion of its direct costs incurred relating to the incident.”
Itron currently works with the government sector to provide smart meter devices. These devices are helpful for gas, electric, and water utility service providers. At present, Itron is working with 7700 utility providers across 100 nations.
Fake Microsoft Teams chats used to gain remote access and steal sensitive data!

Google has issued a warning against a new phishing campaign that uses fake Microsoft Teams chats. This phishing campaign targets unsuspecting employees by sharing credible text messages. They do so by closely mimicking the internal IT support of the same organization.
Initially, the victim receives bulk spam emails. This tactic is used to create a sense of panic and overwhelm. Next, the threat actors approach the victim on Teams while posing as a helpdesk executive. They try to create a sense of urgency by mentioning account issues and offering some quick-fix solutions.
A group of researchers has revealed that a group of threat actors named UNC6692 is carrying out these phishing attacks.
Cybersecurity experts have urged employees to deploy two-factor authentication. They must also completely avoid clicking on any links sent by unverified accounts. No passwords must be shared at any cost through links in any text messages. And if an employee notices any suspicious activity, they must report it directly to the organization.
Indian MSMEs are being targeted by AI-backed threat attacks!

A crucial advisory has been issued by CERT-In (Indian Computer Emergency Response Team), emphasizing the threat landscape across the South Asian country. CERT-In believes that AI has added a level of sophistication to the threat attacks. AI systems have enabled convenient “automation and scale” by scanning source code and identifying vulnerabilities. Cybercrooks are now leveraging AI to target India’s Micro, Small, and Medium Enterprises (MSMEs).
With AI, breaking into a secure network no longer requires precision and hours of manual work. Threat actors can now evaluate source code in bulk in just a fraction of a second. This is done to find “zero-day” vulnerabilities. The worst part is that AI helps create “chain” exploits, which connect different vulnerabilities across multiple platforms. This eventually enables cybercriminals to breach the entire network systems of an organization.
Since MSMEs do not have an adequate budget for deploying high-end cybersecurity systems or round-the-clock monitoring teams, they become an easy target for AI-backed cyberattackers. CERT-In believes that MSMEs can no longer survive without upgrading their cybersecurity mechanisms.
Robinhood tool misused to launch phishing attack!
A group of threat actors has discovered a vulnerability in the Robinhood trading platform, and since then they have been using it to successfully send phishing emails to the targets’ inboxes. Their ultimate goal is to gain access to the victim’s login details.
The threat actors discovered a flaw in Robinhood’s account creation emails. They are using the same flaw to successfully inject phishing content into the victim’s inbox. They are smartly redirecting the noreply@robinhood.com mails to credential-harvesting fake landing pages.
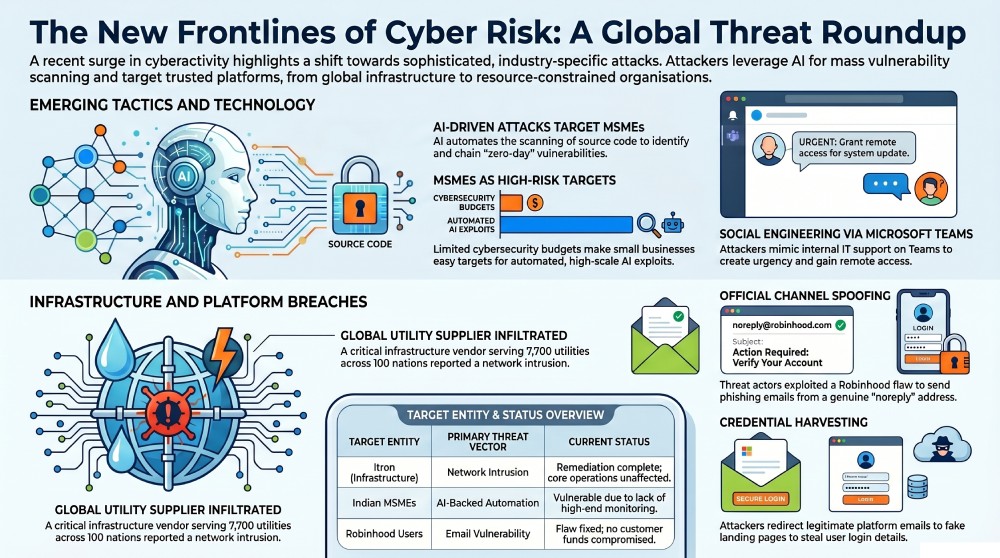
Robinhood, the popular e-trading platform, has claimed that the vulnerability has been fixed. It has also stated that so far, no customer funds or accounts have been compromised. However, some of its users have started receiving warning emails about suspicious login activity.
Robinhood enables its users to buy and sell ETFs, crypto, and Futures. The e-trading platform has stated that the phishing attempt “was not a breach of our systems or customer accounts, and personal information and funds were not impacted.”
The landing page created to harvest sensitive data from targets has now been taken down.
Rising cybersecurity threats, including AI-powered attacks and sophisticated phishing campaigns, highlight the urgent need for organizations to implement robust email authentication measures such as DMARC, SPF, and DKIM to prevent spoofing and protect sensitive data.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.