Swedish Plant Hacked, UAE 800,000 Cyberattacks, Apple Alerts Exploited

Quick Answer
Last week saw a wave of high-impact cyber incidents, from the nation-state-backed “destructive” attack on a Swedish thermal plant to a sudden surge in cyberattacks in the UAE, to the abuse of legitimate iPhone notifications to carry out phishing scams, and a sophisticated cyberattack on a Massachusetts hospital.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format
Last week saw a wave of high-impact cyber incidents, from the nation-state-backed “destructive” attack on a Swedish thermal plant to a sudden surge in cyberattacks in the UAE, to the abuse of legitimate iPhone notifications to carry out phishing scams, and a sophisticated cyberattack on a Massachusetts hospital.
Swedish thermal plant targeted by state-sponsored hackers!
One of the Swedish thermal plants was targeted by hackers back in 2025. Their goal was to create a sense of chaos and disrupt critical operations. The Swedish authorities stated that the cybercrooks were unable to gain access to any crucial data.
Carl Oskar Bohlin, the civil defense minister of Sweden, just conducted a press conference this Wednesday. He has claimed that the cyber mishap had “connections to Russian intelligence and security services.”
Bohlin stated that the cyberattack was prevented “due to a built-in protection mechanism.” He explained that the attack was quite reckless and risky in nature.
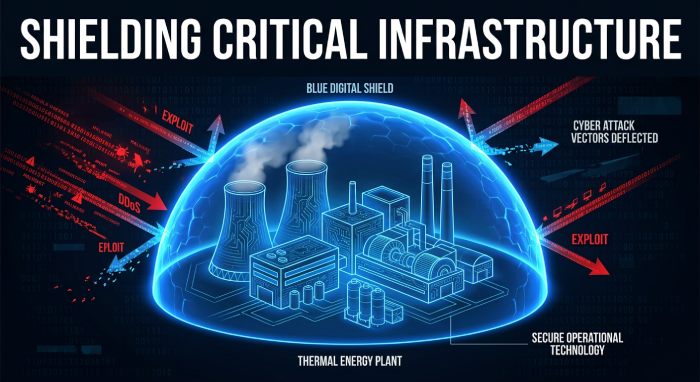
Threat attacks on critical infrastructures are increasingly becoming a common trend among cybercrooks. From water systems to energy infrastructures, cybercrooks strategically target these critical infrastructures in order to inflict severe damage to nations.
The UAE is experiencing 800,000 cyberattack attempts daily
The UAE is currently experiencing 800,000 threat attacks daily. The sheer volume of attacks points to the highly sophisticated nature of digital threats. The data has been shared by the head of the UAE Cyber Security Council, Dr. Mohammed Al Kuwaiti. During a public awareness session, he stated that attacks have surged amid ongoing geopolitical tensions. Not only the frequency, but even the level of sophistication has increased during this phase.
Earlier, the cyberattacks used to be quite direct and isolated in nature. But in the present day, the nature of attack has become more intricate. These cyberattacks look more organized, well-planned, and systematic. Further, they target systems, individuals, and institutions by leveraging multiple channels.
These modern-day threat attacks are backed by artificial intelligence. AI not only increases efficiency but also refines threat campaigns. Without AI, the number of threat attacks was stuck around 200,000. With AI, it is also possible to run the campaigns with minimal human involvement. Artificial intelligence has literally boosted the precision and speed of such threat attacks.
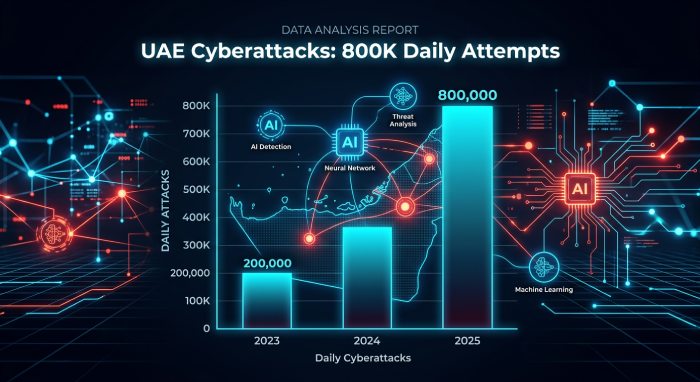
Cybersecurity experts believe there is a large ecosystem behind these coordinated threat attacks. Al Kuwaiti has confirmed that as many as 350 organized threat groups have been identified. Apart from them, the authorities have also pinpointed 320 newbie hackers and 120 entities involved in malicious software activity. Cybersecurity experts are also keeping tabs on 5,000 Telegram channels.
The sudden spike in the number of threat attempts indicates that threat actors no longer wait for peak periods or specific moments to carry out their campaigns. What’s more concerning is the consistency and adaptability of these threat campaigns.
Cybersecurity experts believe that public awareness is extremely important to prevent such threat attempts. Individuals and organizations have been requested to start practicing basic cyber hygiene. Apart from this, updating the devices regularly and bolstering the default passwords can be smart moves to prevent data breach incidents.
Cybersecurity experts warn that implementing DMARC, DKIM, and SPF is now essential to combat rising email spoofing and phishing threats in 2026.
Apple notifications abused to carry out iPhone phishing scams
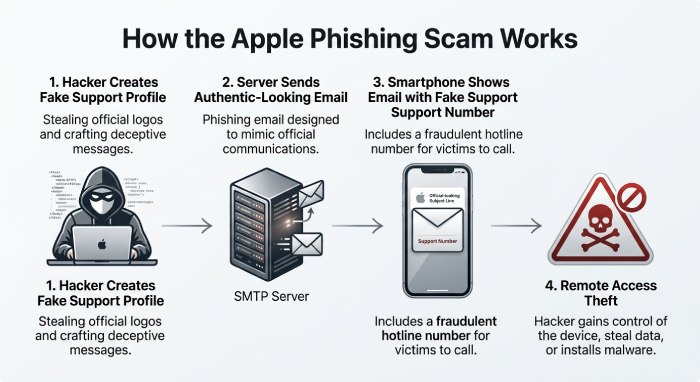
A new threat campaign is doing the rounds where cybercrooks are abusing a genuine Apple account notification system. Their primary goal is to carry out a high-end phishing scam that involves fake iPhone purchase alerts. These alerts appear to be coming from Apple servers. This clever strategy boosts the trustworthiness of the phishing campaign. Also, the credibility helps in bypassing spam detectors.
First of all, a scammer creates an Apple ID and then strategically places scam text in the name fields. Next, the threat actor smartly alters the shipping details of the account. Once done, Apple sends a notification email. The same email is then shared by the scammers with the targets. This so-called legitimate Apple alert now consists of an embedded phishing message. The message claims that the target has ordered an iPhone. In order to cancel the order, the target must make a call to a given number. When the victim makes the call, the hacker on the other side tries to get remote access to the victim’s device to gain access to sensitive data.
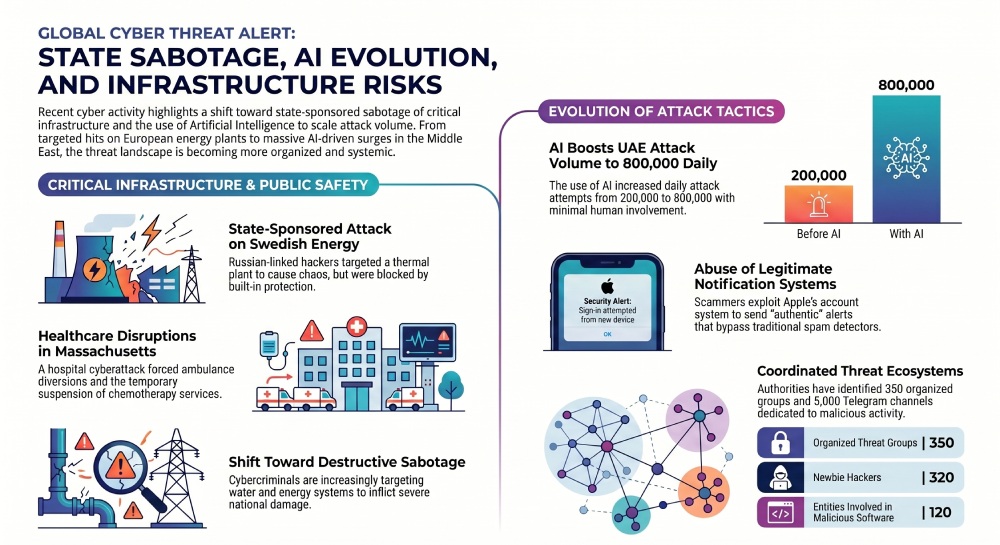
Massachusetts cyber mishap led to ambulance diversion
Threat actors targeted Massachusetts-based Brockton Hospital on Monday. Because of the threat incident, the hospital needed to divert ambulances to prevent critical disruptions. Meanwhile, the walk-in emergency and inpatient care services remained open.
The hospital authorities monitored suspicious activity in its systems and immediately deployed incident response protocols. Brockton Hospital prioritised high-quality patient care and safety, and that’s why they decided to opt for downtime procedures.
Thankfully enough, crucial operations like procedures and surgeries were not affected by the threat attack. However, chemotherapy infusion services had to be halted for some time.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.