The State of DMARC Adoption in 2026:938,000 Domains Have DMARC Records, But Only 9% Are Actually Protected

Quick Answer
Here is a number that should alarm every IT leader, business owner, and security professional reading this: in 2025, the FBI’s Internet Crime Complaint Center received over one million cybercrime complaints for the first time in its history, totaling $20.877 billion in losses, a 26% increase over 2024.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →Here is a number that should alarm every IT leader, business owner, and security professional reading this: in 2025, the FBI’s Internet Crime Complaint Center received over one million cybercrime complaints for the first time in its history, totaling $20.877 billion in losses, a 26% increase over 2024. Business email compromise alone accounted for $3.05 billion of that total, and phishing was the single most-reported crime type with 191,561 complaints (FBI IC3 2025 Annual Report).
For the first time, the FBI also documented AI-enabled cybercrime as a distinct category, with 22,364 complaints and over $893 million in losses attributed to AI-generated phishing, voice cloning, and deepfake schemes. Email remains the primary gateway for these attacks. And the single most effective protocol designed to stop domain-based email fraud, DMARC, is being adopted at record rates but enforced at alarmingly low ones.
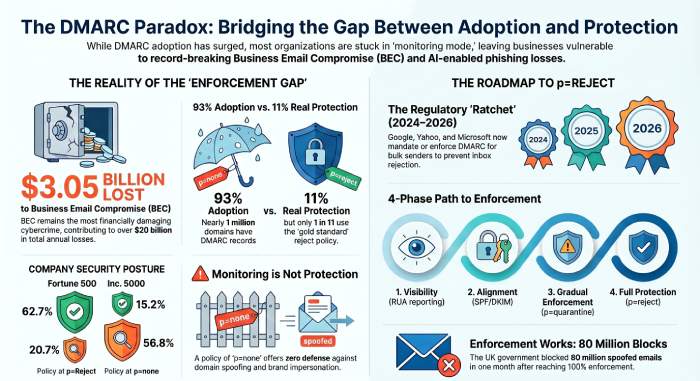
This is the central paradox of email security in 2026: adoption is surging, but protection is not. The latest data from the EasyDMARC 2026 DMARC Adoption & Enforcement Report confirms that valid DMARC records have grown to 937,931 domains, up from 858,782 in 2025 and 523,921 in 2023. Yet more than half a million of those domains remain at p=none, the monitoring-only policy that offers zero protection against spoofing.
This post breaks down the most current data available from government reports, industry whitepapers, and nonprofit research to give you an honest, data-driven view of where DMARC stands today, and what it will take to close the gap between having a DMARC record and being protected by one.
The Adoption Surge: Three Years of Record Growth
Let’s start with the good news. The EasyDMARC 2026 DMARC Adoption & Enforcement Report analyzed 1.8 million of the world’s most-visited domains across three snapshots, 2023, 2025, and early 2026, providing the clearest picture yet of DMARC’s trajectory. Valid DMARC records grew from 523,921 domains in 2023 to 858,782 in 2025 and 937,931 in early 2026. That is a 79% growth rate over three years. Meanwhile, Google reported that its sender requirements drove a 65% reduction in unauthenticated messages reaching Gmail inboxes, with 265 billion fewer unauthenticated messages sent in 2024 alone (Google/Valimail).
Several forces drove this acceleration. Google and Yahoo began requiring DMARC for bulk senders in February 2024. In November 2025, Gmail escalated from soft warnings to actively rejecting non-compliant emails at the SMTP level (Google Sender Guidelines). Microsoft followed in May 2025, with Outlook.com, Hotmail.com, and Live.com rejecting emails from non-compliant bulk senders (dmarcreport.com SPF/DKIM/DMARC Implementation Guide). PCI DSS v4.0.1 made stricter email security measures mandatory in March 2025 for the payments sector. The EU’s Digital Operational Resilience Act (DORA) also positions DMARC as essential for reporting on and blocking email impersonation. And in the UK, the NCSC announced the retirement of its centralized Mail Check service by March 31, 2026, shifting full responsibility for DMARC enforcement directly to individual organizations (PowerDMARC UK Report 2026).
So the momentum is real. Nearly half of the internet’s most prominent domains now have a published DMARC record. But that number tells a dangerously incomplete story.
The Enforcement Gap: Why Having DMARC Is Not the Same as Being Protected
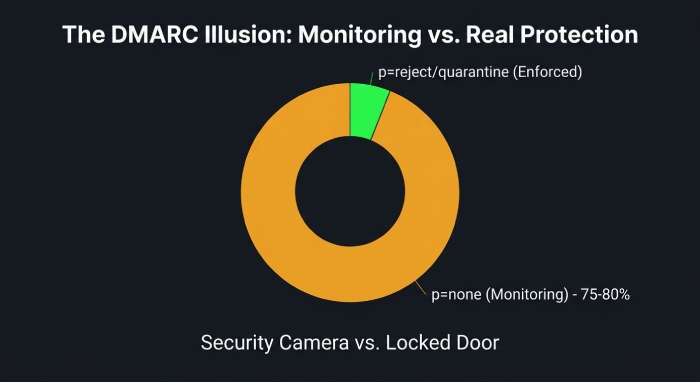
DMARC works in three modes. At p=none, the protocol is in monitoring mode: it watches and reports but takes no action against fraudulent emails. At p=quarantine, suspicious emails are sent to spam. At p=reject, they are blocked entirely. Only quarantine and reject actually protect a domain from being impersonated. A policy of p=none is essentially a security camera with no locks on the doors.
Here is the uncomfortable reality: of the 937,931 domains with valid DMARC records in early 2026, 525,996 remain at p=none, monitoring only, no protection. Enforcement-level policies (p=quarantine and p=reject combined) account for 411,935 domains, up from 233,249 in 2023 but still representing less than a quarter of the 1.8 million domains analyzed (EasyDMARC 2026 Report). Separate monitoring by DmarcDkim.com across 859,048 domains confirms the pattern: as of February 2026, only 10.7% have full p=reject protection (DmarcDkim.com DMARC Adoption Statistics).
Only 159,691 domains in the world meet the gold standard of DMARC best practices, a p=reject policy combined with RUA aggregate reporting. Out of 1.8 million analyzed domains, that is fewer than 1 in 11.
This is not just an EasyDMARC finding. Research from Valimail, one of the leading DMARC enforcement platforms, confirms that 75 to 80 percent of domains with published DMARC records are unable to reach enforcement, remaining stuck at p=none for months or even years (Valimail, The Guaranteed Path to DMARC Enforcement). And PowerDMARC’s 2026 country-level analysis of Canada found the same pattern at a national scale: while 88.7% of Canadian domains have DMARC records, only 28.1% enforce p=reject (PowerDMARC Canada Report 2026).
What This Means in Practice
If your organization has published a DMARC record at p=none and considers the job done, your domain is no more protected than it was before you started. Attackers can still send emails that appear to come from your domain. Your customers, employees, and partners can still receive spoofed messages impersonating your brand. And here is the additional cost: mailbox providers like Google and Microsoft are increasingly using DMARC status to determine inbox placement. Without proper enforcement, even your legitimate marketing emails may land in spam.
What to Do Next
If you are at p=none: You have completed step one. Now you need to analyze your DMARC aggregate reports to identify every legitimate service sending email on your behalf. Authorize each one through SPF and DKIM alignment. Then progressively move to p=quarantine and finally p=reject. A DMARC reporting platform like DMARC Report makes this process significantly easier by translating raw XML reports into actionable dashboards.
If you have no DMARC record at all: You are among the 52.3% of top domains with no DMARC presence. Start by publishing a simple p=none record with an RUA tag to begin collecting data. This takes minutes at the DNS level and immediately gives you visibility into who is sending email using your domain.
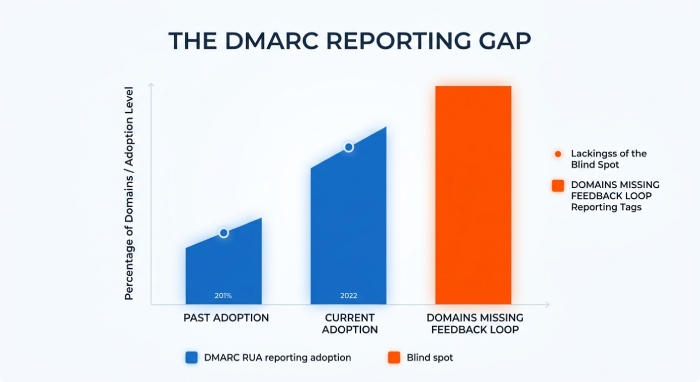
The Reporting Blind Spot: Flying Without Instruments
Even among domains that do have DMARC records, visibility remains poor. EasyDMARC’s 2026 data shows that 553,586 domains now have RUA reporting tags, up from 347,602 in 2023, meaningful progress, but still leaving a significant portion of DMARC-enabled domains without any feedback loop. Many organizations that rushed to publish DMARC records in response to Google and Yahoo’s 2024 requirements did so without configuring reporting, leaving them unable to see who is sending email on their behalf or whether authentication is passing or failing (EasyDMARC 2026 Report).
Think of it this way: DMARC without reporting is like installing an alarm system but never connecting it to the monitoring station. You may have a policy, but you have no data to improve it, no alerts when something goes wrong, and no way to identify legitimate senders you may have missed before tightening your policy.
What to Do Next
Add an RUA tag to your DMARC record immediately if you do not have one. The tag instructs mailbox providers to send aggregate reports about every email claiming to be from your domain. Then use a platform that can parse these XML reports into human-readable insights. Without this data, progressing from p=none to enforcement is guesswork, and guessing wrong means blocking your own legitimate emails.
The Enterprise Advantage: Fortune 500 vs. Mid-Market Companies
The enforcement gap is not evenly distributed. Large enterprises are dramatically more likely to have implemented and enforced DMARC than smaller organizations. The EasyDMARC 2026 report shows the divide has actually widened: Fortune 500 adoption reached 475 out of 500 companies (95%), with more than 80% at enforcement-level policies. Inc. 5000 companies showed strong adoption but significantly slower progress toward enforcement (EasyDMARC 2026 Report). Here is the comparative data from the 2025 baseline:
| Metric | Fortune 500 | Inc. 5000 |
|---|---|---|
| Valid DMARC Records | 93.8% | 76.2% |
| No DMARC at All | 6.0% | 22.4% |
| Policy at p=reject | 62.7% | 15.2% |
| Policy at p=none (Monitoring Only) | 20.7% | 56.8% |
| RUA Reporting Enabled | 97.9% | 67.4% |
| Enforcement (Quarantine + Reject) | 79.3% | 43.2% |
Source: EasyDMARC 2025 DMARC Adoption Report
The numbers tell a clear story. Nearly four times as many Fortune 500 companies have reached p=reject compared to Inc. 5000 firms (62.7% vs. 15.2%). More than half of mid-market companies remain parked at p=none. And while reporting is nearly universal among the Fortune 500 (97.9%), a third of Inc. 5000 companies with DMARC still lack aggregate reporting.
What This Means in Practice
If you are a mid-market company, you are disproportionately at risk. You handle the same kinds of sensitive transactions, customer data, wire transfers, vendor payments, as large enterprises, but your domain is four times less likely to be fully protected against impersonation. Attackers know this. They increasingly target organizations they perceive as having weaker email defenses, using BEC tactics to redirect payments and steal credentials.
The gap is not because the technology is harder for smaller companies. It is because large enterprises dedicate security teams, budget, and vendor support to the multi-step DMARC enforcement process. Mid-market organizations need tools that simplify this journey, automated sender discovery, guided policy progression, and clear reporting dashboards that do not require a dedicated email security analyst to interpret.
The Financial Cost of Not Enforcing DMARC
The financial argument for DMARC enforcement is overwhelming. Let’s put the numbers in perspective.
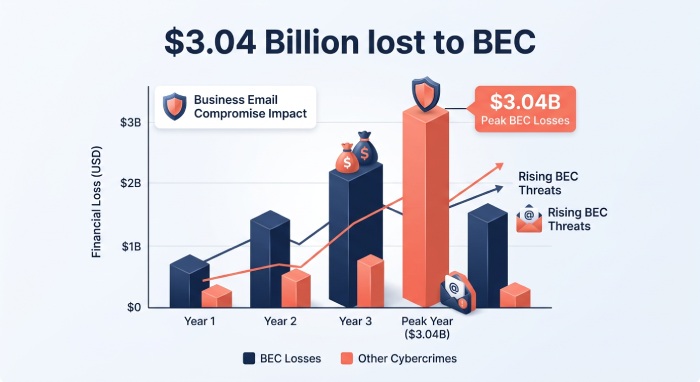
Business Email Compromise, the attack type most directly mitigated by DMARC enforcement, reached a new high in 2025: the FBI IC3 reported $3.046 billion in BEC losses, making it the most financially damaging enterprise-targeted cybercrime for yet another year (FBI IC3 2025 Annual Report). In 2023, BEC caused $2.9 billion in losses across 21,489 complaints (FBI IC3 2023 Annual Report). In 2024, the APWG confirmed $2.8 billion in reported U.S. BEC losses (APWG Q1 2025 Phishing Trends Report). The Travelers insurance company, drawing from its own claims data, reports that over the past decade, global BEC losses have exceeded $50 billion (Travelers Cyber Threat Report Q2 2025).
The AI dimension is now a reality, not a projection. The FBI’s 2025 report documents for the first time that cybercriminals are using AI to generate convincing phishing emails, create synthetic video content, and clone voices for social engineering. Over 22,364 AI-related cybercrime complaints were filed, with losses exceeding $893 million. BEC is particularly vulnerable to AI enhancement: attackers can now craft perfectly written, contextually appropriate emails that bypass traditional “spot the grammar errors” training.
Meanwhile, phishing volumes remain near record highs. The APWG observed 3.8 million phishing attacks in 2025, up from 3.76 million in 2024. The second quarter of 2025 alone saw 1,130,393 attacks, the highest quarterly total since mid-2023 (APWG Q4 2025 Phishing Trends Report). And the infrastructure behind these attacks is industrial: the FBI released a list of 42,000 phishing domains linked to a single phishing-as-a-service platform called LabHost (FBI FLASH Alert FLASH-20250429-001).
$3.05 billion in BEC losses in 2025. $50 billion in cumulative global BEC losses over the past decade. $893 million in AI-enabled cybercrime. 3.8 million phishing attacks in a single year. The question is not whether you can afford to implement DMARC enforcement, it is whether you can afford not to.
What This Means in Practice
DMARC alone does not stop every form of phishing. It specifically prevents domain spoofing, the technique where an attacker sends email that appears to come from your exact domain. This is the foundation of BEC attacks, where a spoofed email from the CFO instructs an employee to wire funds, or a fake supplier invoice redirects a payment. When your domain enforces p=reject, receiving mail servers block these spoofed messages before they ever reach an inbox.
For any organization that handles financial transactions, customer data, or partner communications, the ROI calculation is straightforward: the average BEC wire transfer request in Q2 2025 was $83,099 according to Fortra’s analysis published in the APWG Q2 2025 report. A single successful BEC attack likely exceeds the annual cost of any DMARC enforcement solution by a wide margin.
Proof That DMARC Enforcement Works: The Government Evidence
If there is any remaining doubt that DMARC enforcement produces measurable results, government data settles the question.
United States: The BOD 18-01 Mandate
In October 2017, the U.S. Department of Homeland Security issued Binding Operational Directive 18-01, requiring all federal civilian executive branch agencies to deploy DMARC at p=reject for all second-level domains. A subsequent GAO audit (GAO-20-133) confirmed that the directive produced measurable improvements in federal email security posture. EasyDMARC’s 2025 national-level analysis shows the downstream impact: phishing emails from U.S. domains using p=none policies dropped from over two-thirds of total phishing volume in 2023 to just 14.2% in 2025.
United Kingdom: 100% Central Government Enforcement
The UK’s National Cyber Security Centre reported a landmark achievement in its Active Cyber Defence 6th Year Report: by 2022, 100% of UK central government departments had adopted a strict DMARC enforcement policy (up from 91% at the end of 2021). The impact was immediate and quantifiable: in the 30 days before publication, over 80 million spoofed emails were blocked from central government domains as a direct result of strict DMARC implementation. An additional 1,124 domains across devolved administrations and Crown Dependencies moved to enforcement that year.
The UK achieved 100% DMARC enforcement across central government and blocked 80 million spoofed emails in a single month. This is not theoretical protection, it is measured, documented, and proven.
The Country-Level Contrast
EasyDMARC’s analysis of phishing email delivery across seven countries provides a controlled comparison. Countries with strict enforcement mandates, the United States, Czech Republic, and United Kingdom, saw the steepest declines in phishing successfully reaching inboxes. Countries with only recommended guidelines, like Germany and Norway, showed mixed results. And countries with minimal or unenforced policies, like the Netherlands and Qatar, saw phishing exposure remain essentially unchanged or worsen. In the Netherlands, the rate of phishing from p=none domains actually rose from 76.5% in 2023 to 97.1% in 2025 despite existing government guidance.
The pattern is consistent: mandates with enforcement produce results. Recommendations without accountability do not.
The Regulatory Ratchet: DMARC Is Becoming Mandatory
One of the most significant trends in email security is the convergence of government regulation, industry standards, and mailbox provider requirements around DMARC enforcement. Here is the timeline that every organization should be tracking:
| Date | Requirement | Impact |
|---|---|---|
| October 2017 | DHS BOD 18-01 | All U.S. federal civilian agencies required to implement DMARC at p=reject |
| February 2024 | Google & Yahoo Sender Requirements | Bulk senders (5,000+ emails/day) must have a DMARC record; opened the floodgate for p=none adoption |
| March 2025 | PCI DSS v4.0.1 Enforcement | Stricter email authentication became mandatory for organizations processing payment card data |
| May 2025 | Microsoft Sender Requirements | Outlook.com, Hotmail.com, and Live.com began rejecting non-compliant bulk senders outright |
| November 2025 | Gmail Full Enforcement | Gmail escalated from warnings to active rejection of non-compliant emails at the SMTP level; end of grace period |
| March 2026 | UK NCSC Mail Check Retirement | NCSC retired its centralized Mail Check service, shifting DMARC enforcement responsibility to individual organizations |
| Ongoing | EU DORA & NIS2 Alignment | Growing emphasis on DMARC as part of digital operational resilience and cybersecurity frameworks across EU member states |
The direction is unambiguous. What was a best practice in 2017 became a government mandate. What was a mandate for government became a requirement for bulk senders in 2024. By 2025, it is a compliance standard for financial services. The window for treating DMARC as optional is closing rapidly.
What to Do Next
Audit your current compliance obligations. If you process payment card data, PCI DSS v4.0.1 now expects email authentication controls. If you send more than 5,000 emails per day, Google, Yahoo, and Microsoft will penalize you for non-compliance. If you operate in or serve the public sector, check whether your jurisdiction has a DMARC mandate. And regardless of your industry: the cost of moving from p=none to p=reject is a fraction of the cost of a single successful BEC attack.
The Practical Roadmap: From p=none to p=reject
The data makes the case. The question is how to act on it. Here is a phased approach grounded in the best practices outlined across multiple sources, including the EasyDMARC report and the UK NCSC’s implementation guidance.
Phase 1: Visibility (Weeks 1-2)
Publish a DMARC record at p=none with an RUA tag pointing to a reporting address. This immediately begins collecting aggregate reports from every mailbox provider that receives email claiming to be from your domain. Use a platform like DMARC Report to ingest, parse, and visualize these reports. Your goal in this phase is to build a complete map of every service, system, and third-party vendor sending email on your behalf.
Phase 2: Alignment (Weeks 3-8)
Review your aggregate reports and identify all legitimate senders. For each one, ensure SPF and DKIM alignment: the domain in the SPF record and DKIM signature must match the domain in the visible From header. This is where most organizations get stuck, because they discover third-party services (marketing platforms, CRMs, ticketing systems) that send email on their behalf but are not properly aligned. Fix these configurations before moving forward.
Phase 3: Gradual Enforcement (Weeks 8-12)
Once you are confident that all legitimate senders are authenticated and aligned, move to p=quarantine. This tells receiving servers to send unauthenticated emails to spam rather than the inbox. Monitor your aggregate reports closely for any increase in authentication failures, this may indicate a legitimate sender you missed. DMARC also supports a “pct” tag that lets you apply the policy to a percentage of traffic (e.g., pct=25), allowing you to ramp up gradually.
Phase 4: Full Enforcement (Week 12+)
After a period at p=quarantine with stable authentication results, move to p=reject. This is the gold standard: any email that fails DMARC authentication is rejected outright by the receiving server. At this point, your domain is actively protected against impersonation.
Phase 5: Ongoing Monitoring (Continuous)
DMARC is not a set-and-forget protocol. New email-sending services get added. Configurations change. Vendors update their infrastructure. Keep your RUA reporting active and review your dashboards regularly. The UK NCSC explicitly recommends that organizations treat DMARC as a lifecycle, not a one-time deployment. As EasyDMARC’s report states: “Publishing a DMARC record is the beginning, not the end.”
The Bottom Line
The data is clear across every source we examined:
DMARC adoption is at an all-time high. Nearly 938,000 of the world’s top domains have valid records. Fortune 500 adoption exceeds 95%, with over 80% at enforcement. Gmail alone saw 265 billion fewer unauthenticated messages in 2024. Government mandates and mailbox provider requirements are compounding the pressure worldwide.
DMARC enforcement remains critically low. Only 159,691 domains meet best practices (p=reject + RUA). Over 525,000 domains remain stuck at p=none. Less than 11% of monitored domains globally have full reject protection. The gap between adoption and protection is narrowing slightly but remains enormous.
The cost of inaction is measurable and growing. $20.877 billion in total cybercrime losses in 2025. $3.05 billion in BEC alone. $893 million in AI-enabled cybercrime, a category that did not exist in prior FBI reports. 3.8 million phishing attacks in a single year. These are not projections, they are reported numbers.
Enforcement works. The UK blocked 80 million spoofed emails in 30 days after reaching 100% central government enforcement. Countries with mandates consistently outperform those with mere guidelines. The technology is proven. The data is unequivocal.
The only question remaining is whether your organization will be among the roughly 9% that are actually protected, or the 91% that have checked the box without locking the door.
Sources & References
All statistics and claims in this article are drawn from the following primary source documents. Every source is a publicly accessible PDF report from a government agency, nonprofit research organization, or industry institution.
1. EasyDMARC 2026 DMARC Adoption & Enforcement Report, Analysis of 1.8 million domains globally across 2023, 2025, and early 2026. Primary source for all DMARC adoption, enforcement, reporting, Fortune 500/Inc. 5000 comparison data. Source for 937,931 valid DMARC domains, 525,996 at p=none, 411,935 at enforcement, 159,691 at p=reject+RUA, and 553,586 with RUA reporting.
URL: https://easydmarc.com/blog/ebook/dmarc-adoption-report-2026
2. FBI IC3 2025 Annual Report, Official U.S. government cybercrime statistics. Source for $20.877 billion in total losses, 1,008,597 complaints, $3.046 billion in BEC losses, 191,561 phishing complaints, 22,364 AI-enabled cybercrime complaints with $893 million in losses, and first-ever AI-cybercrime documentation.
URL: https://www.ic3.gov/AnnualReport/Reports/2025_IC3Report.pdf
3. FBI IC3 2024 Annual Report, Source for $16.6 billion in cybercrime losses (33% increase from 2023) and 859,532 complaints in 2024.
URL: https://www.ic3.gov/AnnualReport/Reports/2024_IC3Report.pdf
4. FBI IC3 2023 Annual Report, Source for $2.9 billion in BEC losses across 21,489 complaints in 2023.
URL: https://www.ic3.gov/AnnualReport/Reports/2023_IC3Report.pdf
5. APWG Phishing Activity Trends Report, Q1 2025, Nonprofit research. Source for $2.8 billion in BEC losses in 2024 and Q1 2025 phishing volume (1,003,924 attacks).
URL: https://docs.apwg.org/reports/apwg_trends_report_q1_2025.pdf
6. APWG Phishing Activity Trends Report, Q2 2025, Source for 1,130,393 phishing attacks in Q2 2025 and $83,099 average BEC wire transfer request.
URL: https://docs.apwg.org/reports/apwg_trends_report_q2_2025.pdf
7. APWG Phishing Activity Trends Report, Q4 2025, Source for 3.8 million total phishing attacks in 2025 and 853,244 attacks in Q4 2025.
URL: https://docs.apwg.org/reports/apwg_trends_report_q4_2025.pdf
8. Travelers Cyber Threat Report, Q2 2025, Insurance industry perspective. Source for $2.7 billion in U.S. BEC losses in 2024 and $50 billion in cumulative global BEC losses over the past decade.
URL: https://www.corvusinsurance.com/hubfs/Ransomware_Reports/Q2_25_Travelers_Cyber_Threat_Report.pdf
9. Valimail, The Guaranteed Path to DMARC Enforcement, Vendor whitepaper. Source for the widely cited statistic that 75-80% of domains with DMARC records cannot reach enforcement.
10. DHS Binding Operational Directive 18-01, Enhance Email and Web Security, U.S. government directive requiring federal civilian agencies to implement DMARC at p=reject.
URL: https://cyber.dhs.gov/assets/report/bod-18-01.pdf
11. GAO Report GAO-20-133, DHS Directives Have Strengthened Federal Cybersecurity, Independent U.S. government audit confirming measurable improvements from DHS cybersecurity directives including BOD 18-01.
URL: https://www.gao.gov/assets/gao-20-133.pdf
12. UK NCSC Active Cyber Defence, The 6th Year Report, Official UK government report. Source for 100% central government DMARC enforcement and 80 million spoofed emails blocked in 30 days.
URL: https://www.ncsc.gov.uk/files/acd6-summary.pdf
13. FBI FLASH Alert FLASH-20250429-001, LabHost PhaaS Platform, FBI law enforcement bulletin disclosing 42,000 phishing domains linked to a single phishing-as-a-service operation.
URL: https://www.ic3.gov/CSA/2025/250429.pdf
14. dmarcreport.com, A Practical Guide to SPF, DKIM, and DMARC Implementation, Source for Microsoft’s May 2025 enforcement date and bulk sender requirements.
URL: Email Authentication Essentials PDF
15. DmarcDkim.com, DMARC Adoption Statistics 2026, Live monitoring of 859,048 domains worldwide. Source for 10.7% full protection rate and country-level enforcement data as of February 2026.
URL: https://dmarcdkim.com/dmarc-adoption
16. PowerDMARC, United States DMARC & MTA-STS Adoption Report 2026, Domain-level analysis of U.S. DMARC posture. Source for 95.8% DMARC coverage and 49.0% enforcement (p=reject) among analyzed U.S. domains.
17. PowerDMARC, Canada DMARC & MTA-STS Adoption Report 2026, Analysis of 555 Canadian domains. Source for 88.7% adoption rate with only 28.1% enforcement and IBM’s CA$6.98 million average breach cost.
18. Google/Valimail, Gmail Authentication Impact Data, Source for 65% reduction in unauthenticated messages, 265 billion fewer unauthenticated messages in 2024, and 50% more bulk senders following best practices.
URL: https://www.valimail.com/blog/google-stats-dmarc/
19. PowerDMARC, United Kingdom DMARC & MTA-STS Adoption Report 2026, Analysis of 875 UK domains. Source for NCSC Mail Check retirement (March 2026), sector-level enforcement data, and UK public sector DMARC posture.
URL: https://powerdmarc.com/uk-dmarc-mta-sts-adoption-report/
20. Google, Email Sender Guidelines FAQ, Official Google documentation confirming November 2025 enforcement escalation to active SMTP-level rejection of non-compliant messages.URL: https://support.google.com/a/answer/14229414?hl=en
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.