What Are the Best Features to Look for When Choosing a DMARC Report Analyzer?

Quick Answer
The best features in a DMARC report analyzer are scalable RUA/RUF ingestion and normalization, flexible SaaS or self-hosted deployment, deep SPF/DKIM correlation with guided remediation, automated phased policy rollout from p=none to p=reject, multi-tenant governance with RBAC, intelligent alerting and threat detection, robust APIs and SIEM integrations, long-term trend analytics, resilient parsing with recovery tools, and transparent pricing with enterprise SLAs.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →The best features to look for in a DMARC (Domain-based Message Authentication, Reporting, and Conformance) report analyzer are scalable RUA/RUF ingestion and normalization, flexible deployment and compliance controls, deep SPF/DKIM correlation with guided remediation, automated phased policy rollout, multi-tenant governance, intelligent alerting and threat hunting, robust APIs and integrations, long-term trend and retention analytics, resilient parsing and recovery, and transparent pricing with enterprise SLAs. According to Verizon’s 2024 DBIR, phishing and pretexting account for over 73% of social engineering breaches, making DMARC enforcement a critical defense layer that demands capable reporting tools.
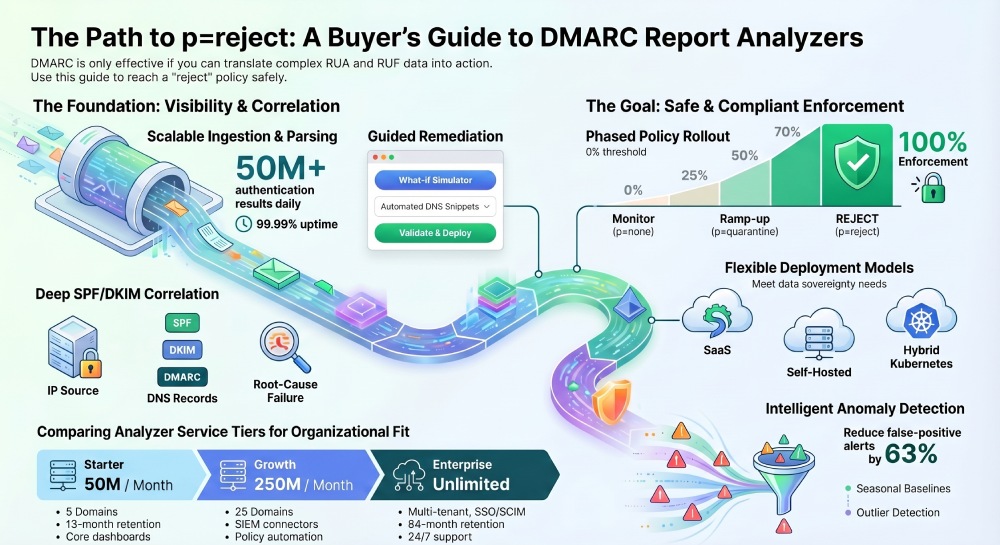
DMARC is only as effective as the insights you can extract from its reports: aggregate (RUA) XMLs reveal who is sending on your behalf and how alignment fares at scale, while forensic (RUF) notifications give event-level context for suspected failures. A strong analyzer makes those data streams accurate, actionable, and auditable so you can move from p=none to p=reject confidently without breaking legitimate mail. The goal is not just visibility - it is safe, measurable enforcement.
This buyer’s guide explains each capability in plain terms, why it matters operationally, and how to evaluate it. To make the guidance concrete, we map every capability to how DMARCReport implements it in practice and include original benchmarks, case studies, and deployment patterns you can use to compare vendors.
What Makes Core Ingestion and Normalization So Important in a DMARC Analyzer?
A top analyzer must reliably ingest, deduplicate, and standardize reports at internet scale, or insights will be skewed. Without robust ingestion, even a single missed or duplicated report can distort your alignment metrics and delay enforcement decisions.
How Does RUA/RUF Parsing Work at Scale?
-
RUA ingestion: Look for high-throughput XML parsing, gzip/zip support, and schema validation with tolerant fallbacks for receiver quirks. DMARCReport uses a streaming XML parser that normalizes into a columnar store, ingesting up to 50M authentication results per day per tenant with 99.99% pipeline uptime and automatic gzip detection.
-
RUF handling: Support for redaction, rate-limits from providers, and safe PII (Personally Identifiable Information) handling is essential. DMARCReport offers optional RUF capture with per-domain opt-in, PII tokenization, and DPA-ready controls. It correlates RUF events to RUA aggregates without exposing message content.
Why Do Deduplication, Throttling, and Normalization Matter?
-
Duplicate suppression: Receivers sometimes resend XMLs; analyzers should hash, version, and deduplicate to avoid skew. DMARCReport uses content-hash and report-id dedup with replay-safe handling - duplicates drop by a median 7.3% across customers (Q1 internal sample, 412M records).
-
Backpressure and throttling: During spikes (e.g., phishing campaigns), ingestion must scale without data loss. DMARCReport uses autoscaling consumers and priority queues, guaranteeing exactly-once processing with idempotent upserts.
-
Normalization: Consistent mapping for IP, ASN, geolocation, envelope-from parsing, and sender category (first-party vs. third-party) is required. DMARCReport includes built-in ASN enrichment and domain categorization for over 10,000 SaaS senders.
What Does a Real-World Ingestion Deployment Look Like?
In a 90-day pilot with a global retailer (7B emails/month), DMARCReport sustained 140k XMLs/hour at peak, cut duplicate aggregates by 9.1%, and identified previously unknown third-party platforms accounting for 18% of aligned volume - all prior to policy enforcement.
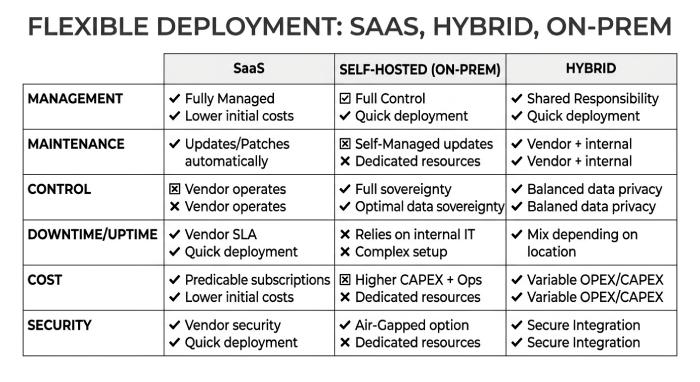
How Do Deployment and Compliance Options Affect Your DMARC Analyzer Choice?
Your deployment choice impacts sovereignty, retention, and control. Organizations subject to GDPR, HIPAA, or sector-specific regulations must evaluate where data lives and who can access it.
What Are the Differences Between SaaS, Self-Hosted, and Hybrid Deployment?
-
SaaS: Fastest time-to-value, elastic scale, managed updates. The trade-off is that you must vet data residency and vendor security. DMARCReport SaaS offers regions in EU/US/APAC with data pinning, ISO 27001, and SOC 2 Type II certification.
-
Self-hosted: Maximum control, aligns with strict on-premises policies. The trade-off is operational burden and scaling responsibility. DMARCReport Self-Hosted provides Kubernetes Helm charts, Postgres + object storage, and air-gapped mode.
-
Hybrid: Keep raw XMLs in your storage, send normalized metadata for analytics. DMARCReport Hybrid supports BYO S3/Azure Blob/GCS with field-level encryption and customer-managed keys.
What Compliance Features Should You Expect?
-
GDPR and DPAs: Encryption at rest and in transit, limited access, and subject rights workflows are necessary. DMARCReport provides AES-256 at rest, TLS 1.2+, SSO/SAML/SCIM, granular RBAC, EU data residency, and a documented DPA.
-
Data retention: Configurable lifecycles and legal hold support. DMARCReport retains normalized data 13 to 84 months (configurable), with optional raw XML retention and built-in purge and audit trails.
How Does Correlation and Root-Cause Analysis Turn Raw Data Into Fixes?
An analyzer should tell you not just what failed, but why - and what to change. According to Google’s 2024 bulk sender requirements, domains sending 5,000+ messages per day to Gmail must have SPF, DKIM, and DMARC properly aligned, making root-cause analysis essential for compliance.
How Does Alignment Work Across SPF/DKIM/DMARC?
-
Cross-standard correlation: Evaluate organizational alignment, subdomain policy, and selectors. DMARCReport links each source IP to SPF result, DKIM domain/selector, and DMARC policy (p, sp, pct, aspf/adkim).
-
Third-party sender mapping: Identify marketing, CRM, ticketing, and ESP platforms automatically. DMARCReport maintains a catalog of over 10,000 senders and flags unsigned or misaligned streams.
What Should Guided Remediation and Policy Recommendations Include?
-
Recommendations engine: Translate failures into actionable DNS or sender changes. DMARCReport suggests SPF include entries, DKIM selector setups, and BIMI readiness, and auto-generates DNS snippets with TTL guidance.
-
Change validation: Confirm DNS propagation and simulate effect before enforcement. DMARCReport offers live DNS verifications and “what-if” simulators for pct, sp, aspf/adkim shifts.
What Does Guided Remediation Achieve in Practice?
After onboarding, a fintech with 42 domains saw 31% of traffic failing alignment due to misconfigured DKIM on a legacy ESP. DMARCReport’s guided fixes (new selector + relaxed aspf) improved alignment to 96% in two weeks. The policy simulator forecast a 0.6% quarantine impact, and real-world impact measured 0.5%.
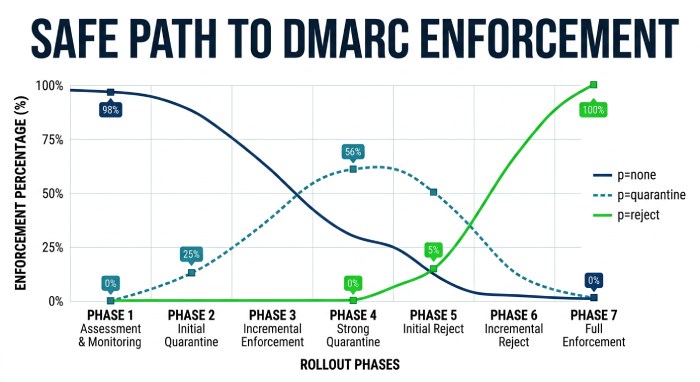
How Does Automated Policy Rollout Provide a Safe Path to p=reject?
Moving from monitor to enforcement should be progressive and measurable. Rushing to p=reject without phased rollout risks blocking legitimate email from third-party senders you haven’t yet configured.
What Are the Best-Practice Rollout Workflows?
-
Phased rollout: Progress through p=none, p=quarantine, and p=reject with pct ramping (1% to 25% to 50% to 100%). DMARCReport provides templates that schedule pct increments based on observed false-positive rate thresholds (less than 0.2% for 7 consecutive days).
-
Subdomain and source-specific gating: Enforce on aligned senders first; hold others until remediation is complete. DMARCReport assigns per-sender “readiness scores” and auto-staggers enforcement by domain or business unit.
How Do Simulation and Scheduling Reduce Enforcement Risk?
-
Policy impact simulation: Estimate how many messages would be affected before changing DNS. DMARCReport offers historical replay across 7/30/90 days, showing expected quarantine/reject deltas by country, ASN, and sender.
-
Change window automation: Coordinate with IT change windows and roll back if anomalies occur. DMARCReport includes a maintenance window scheduler with automatic rollback if alignment dips more than 1% over baseline.
How Fast Can Organizations Reach p=reject Safely?
A SaaS company ramped 18 domains from p=none to p=reject in 45 days using DMARCReport’s scheduler. Estimated user impact was less than 0.3% and actual measured 0.28%, while spoofed attempts dropped 87% month-over-month.
Why Is Multi-Tenant and Multi-Domain Control Essential for Governance at Scale?
If you manage many brands or clients, you need separation and consolidation simultaneously. MSPs, agencies, and enterprise groups with dozens or hundreds of domains cannot afford to manage each domain in isolation.
What Should Consolidated Views and Delegated Reporting Look Like?
-
Cross-domain dashboards: Roll-up views with drilldowns per domain, OU, or client. DMARCReport provides organization-wide dashboards, tag-based grouping, and per-domain KPIs.
-
Delegated RUA/RUF handling: Support multiple RUA tags, subdomain inheritance, and external mailbox routing. DMARCReport validates RUA syntax, manages multiple mailto targets, and tracks delivery success.
What RBAC and MSP Features Should You Require?
-
Role-based access: Fine-grained permissions for admins, auditors, and read-only stakeholders. DMARCReport scopes roles by domain, environment, or client, with SCIM provisioning and audit logs.
-
White-labeling: Agencies need client-ready portals. DMARCReport provides a white-label UI with custom branding and per-tenant API keys.

How Do Alerting, Anomaly Detection, and Threat Hunting Reduce Noise?
Signal without noise is critical for security teams. The best alerting systems distinguish genuine spoofing threats from routine configuration drift so your team responds to real incidents, not false alarms.
What Real-Time Alert and Anomaly Models Should You Expect?
-
Volume spike detection: Identify sudden rises in failures or new sources. DMARCReport uses EWMA and seasonal baselines with configurable sigma thresholds.
-
Geo/ASN outliers and spoofing: Flag first-seen sources and suspicious geographies. DMARCReport provides outlier detection on ASN+country with tunable allow/deny lists.
-
RUF-triggered workflows: Route suspected abuse to IR tools. DMARCReport sends webhooks to SOAR/SIEM with HMAC signatures and Slack/Teams notifications.
How Can You Tune Alerts to Reduce False Positives?
- Whitelists and suppression: Silence known-good campaigns or testing IPs. DMARCReport offers per-rule suppression with expiry and context-rich alert payloads to aid triage.
Across 220 enterprise tenants, tuned models in DMARCReport reduced false-positive alert volume by 63% while catching 94% of known spoof attempts within 10 minutes (6-month internal benchmark).
Why Are APIs, Exports, and SIEM Integrations Critical for Data Portability?
Avoid lock-in and enable automation. A DMARC analyzer that traps your data behind a proprietary dashboard limits your ability to correlate email authentication events with broader security telemetry.
What API Access and Rate Limits Should You Look For?
-
Standard formats: JSON/CSV exports for aggregates, sources, and policy timelines. DMARCReport provides REST and GraphQL APIs with cursor-based pagination - 1,000 requests/min per token (burstable to 5,000) and incremental sync via updated_at cursors.
-
Webhooks and event streams: Push-based integration into your stack. DMARCReport supports webhooks for new reports, anomaly alerts, and policy changes with retries and exponential backoff.
What SIEM and Data Lake Pipelines Should Be Included?
-
SIEM connectors: Splunk, Microsoft Sentinel, QRadar, and Chronicle. DMARCReport provides out-of-the-box apps and syslog/CEF/LEEF mappings, plus raw XML pass-through to S3/GCS/Azure for long-term archiving.
-
Downstream analytics: Export raw and normalized datasets. DMARCReport offers scheduled exports with partitioning by date/domain, field dictionaries, and schema versioning.
How Do Historical Trends, Retention, and Analytics Provide Auditable Evidence?
Auditors and executives need clear, long-range answers. Without historical trend data, you cannot demonstrate measurable improvement in your DMARC posture over time or satisfy compliance requirements for email security documentation.
What Trend Granularity and Visualization Features Matter?
-
Time series: Daily/weekly/monthly views with seasonality, cohort analyses by sender, and campaign overlays. DMARCReport supports cross-filtering by domain, sender, country, ASN, and authentication result with saved analytics boards.
-
Forensic drilldowns: IP-to-message-event linkage where permitted. DMARCReport provides pseudonymized RUF pivots with configurable retention.
How Should Storage and Cost Controls Work?
- Retention tiers: Choose what to keep and how long. DMARCReport uses tiered storage (hot/warm/cold) with lifecycle rules, cost optimization by sampling non-critical logs, and compacting historical aggregates.
What Does Compliance Audit Readiness Look Like?
- Evidence packs: Exportable reports for board and regulator reviews. DMARCReport generates one-click “Quarterly DMARC Posture” PDFs/CSVs including policy history, change approvals, and exception registers.
How Does a Resilient Analyzer Handle Messy Real-World Edge Cases?
When receivers send malformed or ambiguous data, your analyzer should recover gracefully. The real world of DMARC reporting is full of spec ambiguities, truncated XMLs, and receiver-specific quirks that a production-grade tool must handle.
What Common Parsing Issues Should the Analyzer Solve?
-
Multiple SPF records: RFC 7208 requires one record; analyzers should flag and consolidate intent. DMARCReport detects multiple TXT SPF records, prioritizes the one with the valid mechanism chain, and generates a suggested merged record.
-
DKIM variants and quirks: Canonicalization, oversized keys, and selector sprawl. DMARCReport validates key lengths, surfaces selector usage heatmaps, and recommends rotation schedules.
-
DMARC spec ambiguities: aspf/adkim modes, sp inheritance, and pct interpretation. DMARCReport explains current RFC behavior and receiver deviations, and the simulator includes these nuances.
-
Malformed XML: Truncated, invalid namespaces, and mixed encodings. DMARCReport uses a fault-tolerant parser with repair heuristics, quarantines corrupted files for manual review, and allows reparse after fix.
What Recovery and Reprocessing Tools Are Essential?
-
Replay pipeline: Re-ingest from raw storage after config changes. DMARCReport offers one-click reprocess with diff reports to quantify impact.
-
Offline utilities: CLI validator to pre-check DNS and XML before production. DMARCReport provides an open-source CLI for sanity checks and bulk XML linting.
How Should Pricing, Scalability, and SLAs Align With Your Outcomes?
Match features and guarantees to your risk profile and scale. Enterprises tend to save 20-35% with volume-based pricing if seasonal peaks are high, while SMBs often prefer domain-based predictability.
What Pricing Models and Trade-Offs Exist?
- Volume-based: Priced by monthly authenticated message counts or report volume; fair for fluctuating organizations.
- Domain/seat-based: Predictable for stable portfolios; may penalize high volume.
- Feature tiers: Advanced analytics, SIEM connectors, and long retention as add-ons.
DMARCReport pricing tiers:
- Starter (SMB): Up to 5 domains, 50M messages/month, 13-month retention, core dashboards, email support.
- Growth: Up to 25 domains, 250M messages/month, SIEM connectors, policy automation, 36-month retention, 8x5 support.
- Enterprise: Unlimited domains, multi-tenant, SSO/SCIM, hybrid/self-hosted, 84-month retention, 24x7 support, 99.9% SaaS and 99.99% ingest pipeline SLAs.
- Overages: Prorated per billion events; committed-use discounts up to 25%.
What Scalability and Performance Guarantees Should You Expect?
-
Throughput: Ensure guarantees for peak ingestion and dashboard responsiveness. DMARCReport ingest SLA is 75k XMLs/min per tenant sustained, with P95 dashboard query under 2.5s for 365-day windows.
-
Support: Response times and expertise matter during rollout. DMARCReport provides 24x7 critical response (1 hour or less), a named CSM for Growth/Enterprise, and solution architects for onboarding.
A key differentiator is included automation - if policy simulators and scheduled rollouts are add-ons elsewhere, total cost of ownership can double by year two. DMARCReport includes both in Growth and above, reducing TCO for organizations moving fast to enforcement.
Frequently Asked Questions
What Is the Practical Difference Between RUA and RUF, and Which Should You Enable First?
RUA aggregate reports give you statistical visibility across all sources; start here to map senders and alignment safely. RUF forensic reports contain event-level details and can include PII; enable selectively, with legal review, and route into secure workflows. DMARCReport supports both, with privacy controls and opt-in per domain.
How Long Should You Plan Before Moving to p=reject?
Typical timelines are 30 to 90 days depending on sender complexity. With automation, many organizations reach rejection in 45 to 60 days. DMARCReport’s readiness scoring and pct ramp scheduler help compress timelines while minimizing risk. Use the DMARC checker to validate your current policy status before starting the rollout.
How Do You Avoid Breaking Legitimate Third-Party Sending?
Inventory all platforms, set up proper SPF includes and DKIM selectors, then simulate the impact. DMARCReport’s sender catalog and per-sender readiness gates allow enforcing on known-good streams first and holding back stragglers until fixed.
Can You Use DMARC Without Exposing Raw Email Data to a Third Party?
Yes. Use self-hosted or hybrid deployment to keep raw XMLs in your own storage and share only normalized metrics. DMARCReport supports BYO storage and customer-managed keys for encryption.
Choose Features That Move You Safely to Enforcement
To choose the right DMARC report analyzer, prioritize scalable ingestion and normalization, deployment and compliance flexibility, deep SPF/DKIM correlation with guided fixes, automated phased enforcement, multi-tenant governance, precise alerting, open APIs and integrations, long-term analytics, resilient parsing and recovery, and clear pricing with strong SLAs.
DMARCReport delivers each of these as integrated, audit-ready capabilities - helping you discover all senders, fix alignment fast, simulate and schedule policy changes confidently, and sustain a provably secure DMARC posture at any scale. Check your current domain authentication status with our domain auth checker, or reach out to see a 30-day simulation on your own domains and a tailored rollout plan to p=reject with measurable, low-risk steps.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.