What is a DKIM Replay Attack and How to Prevent it?

Quick Answer
DKIM (RFC 6376) signs email messages cryptographically, and unlike SPF, the signature survives email forwarding - which is why DMARC alignment via DKIM is more reliable than SPF alignment for forwarded mail. What is a DKIM Replay Attack and How to Prevent it?
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DKIM Lookup
Auto-discover DKIM selectors for any domain - scan 185 common selectors across all major providers.
Discover DKIM Selectors →
DKIM (RFC 6376) signs email messages cryptographically, and unlike SPF, the signature survives email forwarding - which is why DMARC alignment via DKIM is more reliable than SPF alignment for forwarded mail.
DKIM is the authentication protocol that survives email forwarding, says Brad Slavin, General Manager of DuoCircle. When SPF fails because a forwarder’s IP isn’t in the original record, DKIM alignment is the only path to DMARC pass. That’s why we monitor DKIM alongside SPF in every DMARC Report dashboard.
DMARC Report
What is a DKIM Replay Attack and How to Prevent it?
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-12276">
<source src="https://media.mailhop.org/dmarcreport/images/2024/04/What-is-a-DKIM-Replay-Attack-and-How-to-Prevent-it.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H1M46S">1:46</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-12276" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-12276" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-12276" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-12276" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/what-is-a-dkim-replay-attack-and-how-to-prevent-it/&t=What is a DKIM Replay Attack and How to Prevent it?" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/what-is-a-dkim-replay-attack-and-how-to-prevent-it/&url=What is a DKIM Replay Attack and How to Prevent it?" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/04/What-is-a-DKIM-Replay-Attack-and-How-to-Prevent-it.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/what-is-a-dkim-replay-attack-and-how-to-prevent-it/" class="input-link input-link-12276" title="Episode URL" readonly />
<button class="copy-link copy-link-12276" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-12276” readonly/>
<button class="copy-embed copy-embed-12276" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
In 2023, as many as 45.6% of total emails were identified as spam**. While CISOs and technology enthusiasts are trying their best to ward off these attacks, cybercriminals are not behind in exercising their brain muscles to come up with newer ways of exploitation .
One such relatively recent technique is a DKIM replay attack, where a threat actor exploits a **high-reputation mailbox and generates a legitimate DKIM signature. The signature is later used against billions of recipients to send spam emails that can pass authentication checks and other security filters. They may add another header or change the subject and send the emails to random or specific targets.
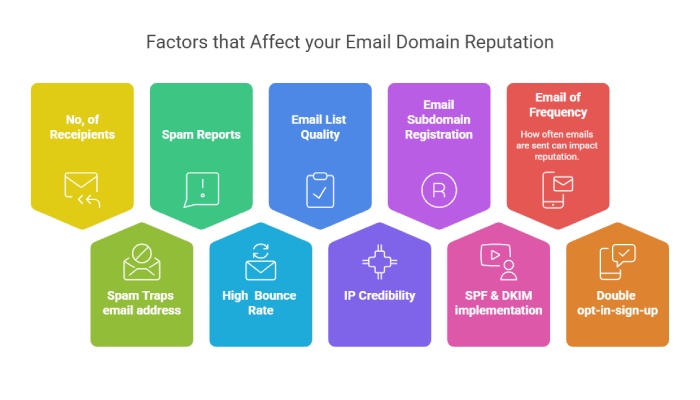
Apart from your DKIM signature being used in cyberattacks, your domain reputation can also take a toll, as recipients can block or report.
Let’s understand this topic better.
DKIM Replay Attack Definition
DKIM replay is a cyberattack technique in which an adversary intercepts a legitimate DKIM-signed email and resends it to a lot of people. As the email retains the original sender’s signature, receiving mail servers perceive it as legitimate and validate it as authentic . This is usually used for having malicious emails bypass security filters so that threat actors can spread malware and attempt phishing, spoofing, social engineering, and similar email-based menaces.
How Does DKIM Work?
DKIM is an email authentication protocol developed in 2004 and made public in 2007 . It works by adding a digital signature to an email’s header using public-key cryptography. The sending mail server generates this signature, and can be verified by the **receiving mail server using a public key stored in the DNS (Domain Name System) records of the sender’s domain.
How Does a DKIM Replay Attack Unfold?
Here’s a usual flow of a DKIM replay attack-
DKIM Signature Flexibility
DKIM lets the domain that signs the email be different from the domain mentioned in the ‘From’ header of the email. This reflects that even if an email has been sent from a specific domain in the ‘From’ header, the DKIM signature is still linked with a different domain.
DKIM Verification
Upon reception, the receiving mail server checks the signature to ensure the email has not been tampered with in transit. If the **signature is validated as authorized, the email passes the check .
Exploiting Highly Reputed Domains
This is the attacking stage. If an attacker gains unauthorized access to a mailbox linked with a reputed domain, they plan to exploit it through the DKIM replay technique. In some cases, they even create a new domain.
Sending the Initial Email
Threat actors send an email from the reputed domain to another mailbox under their control. The **first email is actually harmless or even legitimate so that no suspicion is raised.
Re-Broadcasting
Subsequently, the cybercriminal re-broadcasts the captured email to other recipients. As the DKIM signature is preserved from the reputable domain, email servers regard it as authentic.
How Can Senders Prevent DKIM Replay Attacks?
This is what senders can do on their part to safeguard their domain reputation and brand’s name-
Oversigning Email Headers
Oversigning email headers is a practice in which an email sender includes **multiple cryptographic signatures in the headers to provide redundancy and enhance authenticity. This ensures that nobody can change the date, subject, From, To, and CC details of an email.
Shorter Expiration Times
Using a shorter expiration time (x=) reduces the window of opportunity for DKIM replay attacks. Ensure your new domains have even shorter expiration than the older ones, as they are more likely to get attacked.
Timestamps and Nonces
The inclusion of timestamps and nonces challenges attackers to resend the same email later on, as the values no longer remain the same.
Rotating DKIM Keys Periodically
Rotate your DKIM keys at least twice a year. Rotating them **quarterly is even better if your organization’s operational structure and resource capacity allow that. A regular rotation of keys ensures bad actors don’t get the opportunity to keep using your keys for long if they compromise them.
You can read more about DKIM key rotation here.
How Can Receivers Prevent DKIM Replay Attacks?
The power doesn’t lie in the hands of domain owners only; even receivers can work towards **protecting themselves from being victims of phishing emails.
How Do You Implement Rate Limiting?
Set a limit on the number of emails your mailbox will accept from a **specific sender over a certain time frame. Rate limiting can be implemented based on various criteria, such as the number of emails sent per hour, per day, or per connection. It aims to ensure that legitimate senders can efficiently deliver their emails while mitigating the impact of malicious or abusive activities.
Educate Email Recipients
Propagate among recipients to imply DKIM so that the legitimacy of incoming emails **can be verified.
Network Security Measures
Enforce SPF, DKIM, and DMARC, and establish content filtering rules to block emails with specific keywords, file types, or attachments that can be potentially malicious and are commonly associated with spam or phishing.
If you are **seeking a professional to help you with SPF, DKIM, and DMARC, look no further and contact us. We are helpful; trust and try us.
Topics

Content Specialist
Content Specialist at DMARC Report. Writes vendor-specific email authentication guides and troubleshooting walkthroughs.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.