DMARC Report Analyzers in 2026: Why They Matter More Than Ever, What the Data Really Says, and How to Take Action Today

Quick Answer
A data-driven guide backed by 37 primary-source statistics from government PDFs, academic research, industry reports, and official standards bodies. Here is a paradox that should concern every organization sending email in 2026: DMARC adoption is growing faster than ever, yet the vast majority of domains remain completely unprotected against email spoofing.
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

Try Our Free DMARC Checker
Validate your DMARC policy, check alignment settings, and verify reporting configuration.
Check DMARC Record →A data-driven guide backed by 37 primary-source statistics from government PDFs, academic research, industry reports, and official standards bodies.
The Email Security Paradox No One Is Talking About
Here is a paradox that should concern every organization sending email in 2026: DMARC adoption is growing faster than ever, yet the vast majority of domains remain completely unprotected against email spoofing. Even among those that have adopted DMARC, most have done nothing more than plant a flag in the ground without turning on any actual defense.
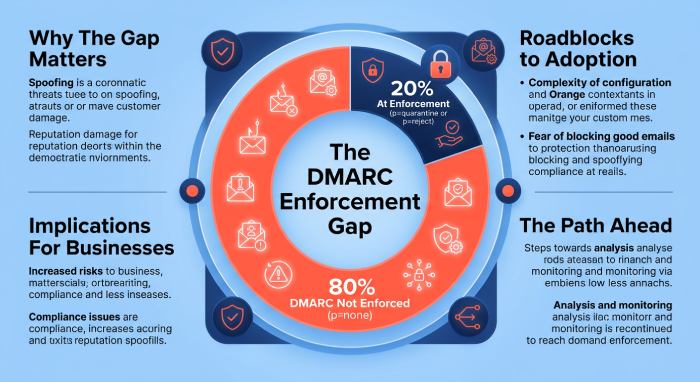
The numbers tell a striking story. According to the EasyDMARC 2025 DMARC Adoption Report, DMARC adoption among the top 1.8 million domains grew from 29.1% to 47.7% between 2023 and 2025, a63.9% surge. That sounds impressive until you realize what it actually means: more than half of the most-visited domains on the internet still have no DMARC record at all. And the situation is far worse when you look at enforcement. The EasyDMARC 2026 Report reveals that of 937,931 domains with valid DMARC records in early 2026, a staggering 525,996 remain stuck at p=none - the monitoring-only policy that does absolutely nothing to stop spoofed emails from reaching inboxes.
To put it plainly: more than half of all DMARC-enabled domains are using a policy that offers zero protection. They have installed a security camera but left the front door wide open.
This is where DMARC report analyzers become indispensable. Not as a nice-to-have. Not as a checkbox for compliance. But as the operational tool that transforms DMARC from a passive DNS record into an active, enforced shield against the most costly attack vector in cybersecurity today.
The Threat: Why Email Remains the Number One Attack Vector

Before we talk about DMARC analyzers, we need to understand why they exist. The answer begins with a simple, uncomfortable fact: email is the easiest and most profitable way to attack an organization, and it is getting worse.
In 2025, 3.8 million phishing attacks were recorded globally, with an estimated 3.4 billion phishing emails sent every single day. The average cost of a breach caused by phishing has reached $4.88 million according to IBM’s Cost of a Data Breach Report. Business Email Compromise (BEC) losses alone reached $2.77 billion in reported FBI complaints in 2024, and the actual number is believed to be three to five times higher due to chronic underreporting.
What makes this worse is the role of artificial intelligence. Industry analysis shows that 82.6% of phishing emails now contain AI-generated content. Manually crafted phishing emails that once took attackers 16 hours to produce can now be generated in as little as five minutes. AI-generated phishing content has surged 1,265% in 2025, making it virtually impossible for traditional spam filters to keep up. When AI can perfectly mimic your CEO’s writing style, the only reliable defense left is authentication at the protocol level: verifying that the email actually came from who it claims to come from.
That protocol-level defense is DMARC. And the tool that makes DMARC operationally usable is the DMARC report analyzer.
What this means for you: If your organization sends email without DMARC enforcement, you are leaving your brand, your customers, and your employees exposed to a threat that costs the global economy billions annually. The question is no longer whether to implement DMARC, but how fast you can move from monitoring to enforcement.
Understanding DMARC: What It Does and Why Enforcement Is Everything
DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It is an email authentication protocol that builds on two existing standards - SPF (Sender Policy Framework) and DKIM (DomainKeys Identified Mail) - and adds a critical layer: policy enforcement and reporting.
The NIST Special Publication 800-177 Rev. 1: Trustworthy Email, the authoritative federal guideline for email security, explains the mechanics: when an email is received, the receiving server checks the SPF and DKIM results against the DMARC policy published in the sending domain’s DNS. The DMARC record tells the receiver what to do if authentication fails, and instructs the receiver to send reports back to the domain owner detailing who is using their domain to send email.
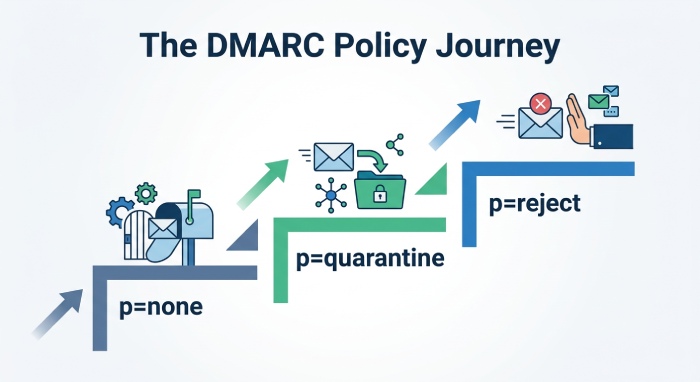
The Three DMARC Policies: A Critical Distinction
- p=none: Monitoring only. The receiving server takes no action on emails that fail authentication. This is the starting point for gathering data, but it provides zero protection against spoofing. Attackers can freely impersonate your domain.
- p=quarantine: Emails that fail authentication are routed to the recipient’s spam or junk folder. This provides moderate protection, reducing the chance a spoofed email will be seen, but it does not eliminate the risk.
- p=reject: Emails that fail authentication are blocked outright and never delivered. This is the gold standard. It is what the DHS Binding Operational Directive 18-01 mandates for all federal agencies, and what CISA’s Exchange Online guidance prescribes as a requirement, not a recommendation.
The Enforcement Gap: The Biggest Problem in Email Security
Here is the core problem. Research from Valimail, spanning multiple years of analysis, consistently finds that approximately 80% of domains that deploy DMARC never move past the monitoring-only policy of p=none. This enforcement failure rate has remained stubbornly consistent across industries and geographies. The Red Sift global analysis of 73.3 million domains found that as of December 2025, only 2.5% enforce the strictest p=reject policy, while 83.9% have no DMARC record at all.
The DMARCReport analysis puts it even more starkly: only 7.7% of top domains are fully protected with strict enforcement.
Why do organizations stall? According to PowerDMARC survey data, only 25.5% of senders using p=none plan to upgrade within the next year. A full 61% say they will only move to enforcement if forced by regulatory or business requirements. And 13% have no plans to strengthen their policy at all.
What this means for you: Publishing a DMARC record at p=none is like installing smoke detectors but disconnecting them from the fire department. You will know your building is on fire, but nobody will come to put it out. The only path from awareness to protection runs through enforcement, and the only practical way to get there is with a DMARC report analyzer.
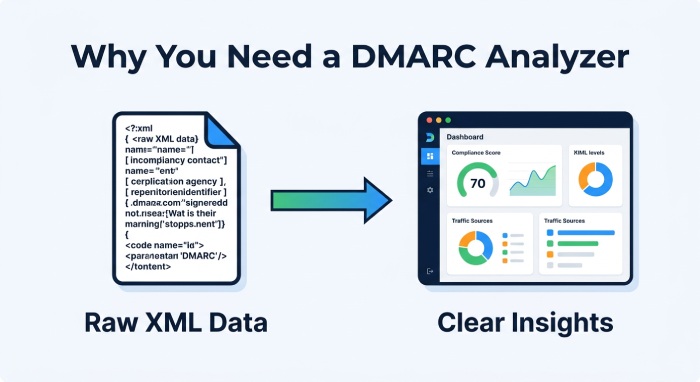
Why You Cannot Do DMARC Without a Report Analyzer
This is not an opinion. It is the official position of the United States government. In its Enhance Email and Web Security guidance, CISA explicitly states: “Reading and understanding DMARC reports is extremely difficult without a tool.”
To understand why, you need to know what DMARC reports actually look like. Every day, every mailbox provider that receives email claiming to be from your domain sends you an aggregate report. These reports are XML files containing sendingIP addresses, message counts, SPF and DKIM authentication results, disposition actions, and alignment data. A single organization with a dozen domains and multiple third-party email services can receive hundreds of reports daily, each containing thousands of data rows.
A University of Amsterdam research project that analyzed commercial DMARC tools confirmed this challenge. The researchers found that raw DMARC data requires extensive parsing, aggregation, and correlation to be actionable. Their gap analysis identified features like DNS record history tracking, outgoing report analysis, and volume correlation as essential capabilities that go far beyond simple XML parsing.
What a DMARC Report Analyzer Actually Does
A modern DMARC report analyzer transforms this raw data into operational intelligence. Based on extensive industry research, including tool comparisons from Valimail,Red Sift, and DMARCReport, the core capabilities include:
- Sender identification and mapping. The analyzer translates raw IP addresses into named sending services. Instead of seeing “104.195.127.15 sent 3,247 messages,” you see “Salesforce sent 3,247 messages.” Leading tools like Valimail claim to identify up to 100% of sending services by name, with catalogs of over 10,000 known senders.
- Authentication diagnostics. The analyzer cross-references SPF results, DKIM selectors, and DMARC alignment across every sending source. It shows you not just what failed, but why it failed and what DNS change to make. Some tools even auto-generate the exact DNS record snippets with TTL guidance.
- Phased enforcement management. Moving from p=none to p=reject is not a switch you flip overnight. Analyzers provide “what-if” simulations that model the impact of policy changes before you make them. They let you gradually increase enforcement using the percentage tag (pct), monitoring the results at each stage to catch legitimate email that might be misconfigured.
- Threat detection. When someone starts spoofing your domain, the analyzer flags it immediately. Without this visibility, a phishing campaign using your brand could run for weeks before anyone notices.
- Compliance reporting. With PCI DSS, CISA mandates, and provider requirements from Google, Yahoo, and Microsoft all converging, organizations need audit-ready evidence of their DMARC posture. Analyzers generate the compliance documentation automatically.
Practical next step: If you manage more than one domain or use any third-party email service (marketing platforms, CRMs, transactional senders), start with a free DMARC monitoring tool like Valimail Monitor, Postmark DMARC Digests, or Cloudflare’s built-in DMARC monitoring. These require zero cost and minimal setup: you add a single DNS record, and reports start flowing within 24 hours.
The Mandate Wave: Why 2024-2026 Changed Everything
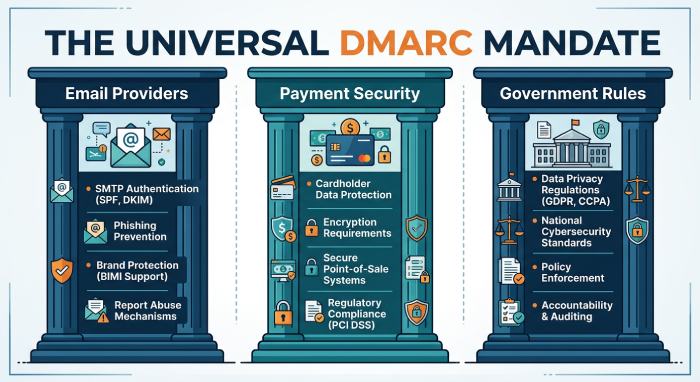
DMARC is no longer optional. A convergence of mandates from the world’s largest email providers, payment industry regulators, and government agencies has made DMARC enforcement a baseline requirement for doing business.
Google, Yahoo, and Microsoft: The Provider Mandates
In October 2023, Google and Yahoo announced that starting February 2024, any domain sending more than 5,000 emails per day to their users must implement DMARC with at minimum a policy of p=none. As of November 2025, non-compliant emails to Gmail receive permanent rejections (550 errors). Microsoft followed suit, requiring SPF, DKIM, and DMARC for bulk senders to Outlook.com, Hotmail.com, and Live.com starting May 5, 2025.
The impact has been measurable and massive. According to Google’s own data reported through Dark Reading, Gmail users saw 265 billion fewer unauthenticated emails in 2024 - a 65% reduction. During the 2024 holiday season, users encountered 35% fewer scams. PowerDMARC reports that 50% more bulk senders adopted best security practices following the mandates, and the reduced volume of unauthenticated email has been sustained with continued downward pressure.
PCI DSS v4.0: The Compliance Mandate
PCI DSS v4.0 Section 5.4.1 mandates anti-phishing mechanisms for all organizations that handle cardholder data, effective March 31, 2025. The standard specifically cites DMARC, SPF, and DKIM as the recommended anti-spoofing controls. This applies broadly to merchants, payment processors, acquirers, issuers, and service providers. As Mimecast notes, failure to comply with PCI DSS can result in fines and penalties up to losing the right to handle payments entirely.
Government Mandates: From the US to Global
The US government set the standard in 2017 when the Department of Homeland Security issued Binding Operational Directive 18-01, requiring all federal civilian agencies to implement DMARC at p=reject within one year. The directive also required agencies to send aggregate reports to a centralized CISA address (reports@dmarc.cyber.dhs.gov) for government-wide visibility.
CISA has since published additional guidance including healthcare-specific DMARC recommendations and counter-phishing recommendations for federal agencies that reinforce DMARC as a foundational security control.
The impact of government mandates is quantifiable. The EasyDMARC 2025 report found that countries with mandatory DMARC requirements, like the United States, saw phishing success rates plummet from 69% to 14%. By contrast, countries without enforcement mandates, like the Netherlands, saw phishing success rates rise to 97%. This is perhaps the single most powerful data point in the entire DMARC landscape: mandates work, and they work dramatically.
What this means for you: If you process payments, you likely need DMARC for PCI DSS compliance as of March 2025. If you send bulk email to Gmail, Yahoo, or Outlook users, you already need DMARC or your messages are being rejected. If you are in healthcare, government, or financial services, regulatory pressure is accelerating. A DMARC report analyzer is not just a security tool - it is a compliance tool.
Who Is Getting This Right (and Who Is Not)
DMARC adoption varies enormously depending on organization size, industry, and geography. Understanding where your organization sits relative to peers is essential for setting priorities and building the business case.
The Enterprise Leaders
The Red Sift global DMARC analysis shows that the Fortune 500 and S&P 500 lead the way with DMARC readiness scores of 81.2% and 81% respectively. These are the world’s largest publicly traded companies, and they have the resources and incentives to invest in email authentication. By comparison, EasyDMARC found that the Inc. 5000 - high-growth but smaller companies - lag significantly behind in enforcement. The gap between adoption and enforcement widens considerably as organizational size decreases.
The Lagging Industries
The Valimail 2025 Disinformation and Malicious Email Report paints a concerning picture of industry-specific gaps. Healthcare lags behind with just over one third of domains having implemented even the bare minimum p=none policy. The IT sector itself shows concerning gaps, with nearly a third of surveyed domains lacking the ability to prevent spoofing. Only 26% of leading fintech companies enforce DMARC at the strictest p=reject level, despite being prime targets for phishing and BEC attacks. And 41% of banking institutions lack DMARC protection entirely.
The Government Gap
Government domains fare poorly on a global scale. A SendLayer analysis of 187,482 organizations across 198 countries found that only 35% of government domains had DMARC enabled. In the United States, despite the BOD 18-01 mandate, as much as 60% of government domains examined had no DMARC protocols. German government data is similarly troubling: over 40% of government domains lack DMARC, and only 12.5% enforce it.
Practical next step: Benchmark your organization against your industry. If you are in healthcare, financial services, or government and have not yet reached p=reject, you are behind. Use a DMARC analyzer to assess your current posture, identify every service sending email on your behalf, and build a 90-day plan to move from monitoring to enforcement.
How to Choose a DMARC Report Analyzer: What Actually Matters
The DMARC analyzer market has matured significantly, with options ranging from free monitoring tools to enterprise platforms costing thousands per year. Based on extensive tool comparisons and independent reviews, here is what matters most at each stage of your DMARC journey.
Stage 1: Getting Started (Free Tools)
If you have not yet published a DMARC record or are in the early monitoring phase, a free tool is sufficient. Valimail Monitor handles unlimited email volume with clear dashboards. Cloudflare’s built-in DMARC monitoring works seamlessly if you already use their DNS. Postmark’s DMARC Digests translates XML reports into readable weekly email summaries with no dashboard required. At this stage, the goal is visibility: learn who is sending email as you, and whether those senders areproperly authenticated.
Stage 2: Moving to Enforcement (Paid Platforms)
When you are ready to move from p=none to p=quarantine and eventually p=reject, you need more sophisticated tooling. Look for platforms that offer sender identification by name (not just IP address), guided remediation with specific DNS change recommendations, phased enforcement simulation (“what-if” analysis before you change your policy), multi-domain management for organizations with complex domain portfolios, and real-time alerting when new unauthorized senders appear. The leading platforms in this space include Valimail Enforce, PowerDMARC, EasyDMARC, Red Sift OnDMARC, and dmarcian.
Stage 3: Enterprise and Compliance (Managed Solutions)
Large organizations managing dozens or hundreds of domains, with complex third-party sending ecosystems and regulatory compliance requirements, benefit from managed DMARC services. These include dedicated onboarding engineers, automated SPF flattening to avoid the 10-lookup DNS limit, SIEM integrations for security operations center (SOC) workflows, BIMI (Brand Indicators for Message Identification) setup for displaying verified brand logos in recipient inboxes, and audit-ready compliance reporting for PCI DSS, CISA, and EU DORA requirements.
Practical next step: Start free. Today. Right now. Visit your DNS provider and publish a DMARC record with p=none and a reporting address pointed at a free analyzer. You will have actionable visibility into your email ecosystem within 48 hours, at zero cost, with zero risk of disrupting email delivery.
The ROI of DMARC Enforcement: Beyond Security
The security case for DMARC is well established. But the business case extends far beyond threat prevention.
Deliverability Improvement
Valimail reports a 5-10% email deliverability increase following DMARC enforcement. This is not a minor improvement. For an e-commerce company sending millions of marketing and transactional emails monthly, a 5-10% improvement in inbox placement translates directly into revenue. Authenticated emails are more likely to land in the primary inbox rather than spam or quarantine folders, leading to higher open rates, better engagement, and more conversions.
Brand Protection
Without DMARC enforcement, anyone can send email that appears to come from your domain. Spoofing attacks cost large retailers up to $15 million annually in breaches, response costs, and brand fallout. Gartner reports that BEC payments crossed $6 billion globally in 2024. DMARC at p=reject eliminates exact-domain spoofing for all conforming mail receivers, making your domain a harder target and deterring attackers.
Measurable Threat Reduction
The data on enforcement effectiveness is clear. Organizations using enforced DMARC policies in 2025 saw up to 85% reduction in spoofed phishing emails.Google’s data shows 265 billion fewer unauthenticated emails in 2024 following the mandate wave. And countries with mandatory DMARC saw phishing success rates plummet from 69% to 14%. These are not marginal improvements. These are transformational reductions in risk.
Your 90-Day DMARC Enforcement Plan
The following roadmap is designed for organizations that are either starting from scratch or stuck at p=none. It is informed by best practices from NIST SP 800-177, CISA guidance, and DMARC.org’s deployment resources.
Days 1-14: Establish Visibility
Publish a DMARC record at p=none for every domain you own, including domains you do not actively use for sending email (attackers can spoof those too). Point the rua tag at a DMARC analyzer. Review the first week of reports to identify every service sending email on your behalf: marketing platforms, CRMs, transactional email providers, ticketing systems, and internal mail servers. You will almost certainly discover senders you did not know about.
Days 15-45: Authenticate Every Legitimate Sender
For each legitimate sending service identified, verify that SPF and DKIM are properly configured and aligned with your domain. Update your SPF record to include all authorized sending IPs. Work with third-party vendors to set up DKIM signing with your domain. Use your analyzer’s diagnostics to confirm that each source passes DMARC alignment checks. Document everything.
Days 46-70: Begin Enforcement
Move your DMARC policy to p=quarantine. Start with the pct tag set to 10-25%, which applies the quarantine policy to only a portion of failing messages while you monitor the results. Gradually increase the percentage over several weeks. Your analyzer’s alerting and simulation features are essential here: they will flag any legitimate email that starts failing, giving you time to fix configuration issues before they affect delivery.
Days 71-90: Reach Full Enforcement
Move to p=reject with pct=100%. At this point, all emails failing DMARC authentication will be blocked by receiving servers. Continue monitoring through your analyzer for new sending services, configuration drift, and any attempted spoofing activity. Set up automated alerts for unauthorized senders. Consider implementing BIMI to display your verified brand logo in recipient inboxes, further strengthening brand trust.
Critical reminder: Do not skip straight to p=reject without the monitoring and remediation phases. Doing so risks blocking legitimate email from misconfigured but authorized senders. The phased approach, guided by a DMARC analyzer, is the only safe path to enforcement.
The Growth Story: How We Got Here
DMARC’s growth trajectory provides important context for where the technology is heading. DMARC.org’s own data, sourced from DomainTools sensor analysis, shows that active valid DMARC records grew from 80,275 in December 2016 to over 5.5 million by mid-2022 - a nearly 70x increase in 5.5 years. By 2021 alone, valid DMARC policies rose 84% to nearly 5 million unique records, with the second half of the year averaging 288,000 new records per month.
Then came the 2024 mandate wave. DMARC adoption doubled, rising from 55,000 to 110,000 new domains per month. Red Sift data shows a 2.3 million domain increase in a single year following Google and Yahoo’s requirements. By September 2024, DuoCircle reports that nearly 6.8 million domains had email sender authentication configured globally.
The trajectory is unmistakable. DMARC is no longer emerging technology. It is maturing infrastructure. And the gap between early adopters at full enforcement and the vast majority still at monitoring-only represents both a risk and an opportunity. The organizations that move to enforcement now will be protected. Those that delay will find themselves increasingly exposed as attackers concentrate on the weakest targets.
The Bottom Line
The data across 37 primary-source statistics from government PDFs, academic research, industry reports, and official standards bodies tells a consistent story:
DMARC works. When enforced, it reduces spoofed phishing by up to 85%, cuts unauthenticated email volume by billions, and drops phishing success rates from 69% to 14% in countries that mandate it.
Most organizations are not enforcing it. Approximately 80% of domains with DMARC records remain at p=none, offering zero protection. Only 2.5% of domains globally enforce the strictest policy. The enforcement gap is the defining challenge in email security today.
DMARC report analyzers are the bridge. The US government itself says DMARC reports are unreadable without tools. Analyzers provide the visibility, diagnostics, and phased enforcement management needed to cross from monitoring to protection. From free tools for small businesses to enterprise platforms for complex domain portfolios, solutions exist at every price point and scale.
The mandate window is closing. Google, Yahoo, and Microsoft already reject non-compliant bulk email. PCI DSS v4.0 requires DMARC for payment processors. Government mandates are expanding globally. Organizations that have not yet moved to enforcement are running out of grace period.
Start today. Publish a DMARC record. Point it at a free analyzer. Begin the 90-day journey from visibility to enforcement. The data is overwhelming, the tools are accessible, and the cost of inaction is measured in billions.
References and Sources
All sources referenced in this article, with full URLs for verification:
1. Texas Coalition for Affordable Insurance Solutions / Texas Department of Insurance - Legislative Handout to the Committee on Insurance (May 2024). https://capitol.texas.gov/tlodocs/88R/handouts/C4502024091709001/5ebf3ef6-f2b1-4780-ba85-a94e758703a3.PDF
2. Mitchell International / Enlyte - “The Future of Paintless Dent Repair” White Paper (March 2022). https://hub.enlyte.com/m/937ff9de798ea26/original/Mitchell-The-Future-of-Paintless-Dent-Repair-White-Paper.pdf
3. Intent Market Research - Paintless Dent Repair (PDR) Service Market Report (March 2025). https://intentmarketresearch.com/latest-reports/paintless-dent-repair-pdr-service-market-8529
4. Market Research Future (MRFR) - Automotive Paintless Dent Removal Tools Market Report (2025). https://www.marketresearchfuture.com/reports/automotive-paintless-dent-removal-tools-market-30970
5. Mitchell International - Press Release: Vale PDR Technician Certification Program (October 2021). https://www.mitchell.com/insights/news-release/auto-physical-damage/mitchell-named-official-technology-provider-vale
6. South Bay Collision - Paintless Dent Removal vs. Traditional Repair: A Cost Comparison (January 2025). https://southbaycollision.com/2025/01/11/paintless-dent-removal-vs-traditional-repair-cost-comparison/
7. Engineer Fix - How Much Does Paintless Dent Repair Cost? (December 2025). https://engineerfix.com/how-much-does-paintless-dent-repair-cost/
1. Texas Coalition for Affordable Insurance Solutions / Texas Department of Insurance - Legislative Handout to the Committee on Insurance (May 2024). https://capitol.texas.gov/tlodocs/88R/handouts/C4502024091709001/5ebf3ef6-f2b1-4780-ba85-a94e758703a3.PDF
2. Mitchell International / Enlyte - “The Future of Paintless Dent Repair” White Paper (March 2022). https://hub.enlyte.com/m/937ff9de798ea26/original/Mitchell-The-Future-of-Paintless-Dent-Repair-White-Paper.pdf
3. Intent Market Research - Paintless Dent Repair (PDR) Service Market Report (March 2025). https://intentmarketresearch.com/latest-reports/paintless-dent-repair-pdr-service-market-8529
4. Market Research Future (MRFR) - Automotive Paintless Dent Removal Tools Market Report (2025). https://www.marketresearchfuture.com/reports/automotive-paintless-dent-removal-tools-market-30970
5. Mitchell International - Press Release: Vale PDR Technician Certification Program (October 2021). https://www.mitchell.com/insights/news-release/auto-physical-damage/mitchell-named-official-technology-provider-vale
6. South Bay Collision - Paintless Dent Removal vs. Traditional Repair: A Cost Comparison (January 2025). https://southbaycollision.com/2025/01/11/paintless-dent-removal-vs-traditional-repair-cost-comparison/
7. Engineer Fix - How Much Does Paintless Dent Repair Cost? (December 2025). https://engineerfix.com/how-much-does-paintless-dent-repair-cost/
https://www.txdmv.gov/sites/default/files/report-files/FY\_2024\_VTR\_FactSheet.pdf
18. Texas Department of Insurance - Insured Losses Resulting from the February 2021 Texas Winter Weather Event (September 2022). https://www.tdi.texas.gov/reports/documents/feb2021-tx-winter-weather-summary-mar2022.pdf
19. NOAA/NCEI - U.S. Billion-Dollar Weather and Climate Disasters: Events (2024). https://www.ncei.noaa.gov/access/billions/events.pdf
_ - End of Article - _
Topics

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.