What Is a Zero-Day Exploit and How Can You Prevent It?
Cybersecurity threats are evolving rapidly, and organizations must constantly adapt to protect their digital infrastructure. Among the most dangerous threats today are zero-day exploits—cyberattacks that take advantage of unknown vulnerabilities in software or systems before developers have time to fix them. These attacks are highly effective because they exploit weaknesses that have not yet been discovered or patched.
At DMARCReport, we frequently analyze cyber threats that target businesses through email systems, applications, and networks. Zero-day vulnerabilities often serve as entry points for attackers to deliver malware, steal credentials, or launch phishing campaigns. Understanding how these exploits work and how to defend against them is essential for organizations that want to protect their data, reputation, and customers.
In this article, we explain what a zero-day exploit is, how it works, why it is dangerous, and what practical steps organizations can take to minimize the risks.
Understanding Zero-Day Exploits
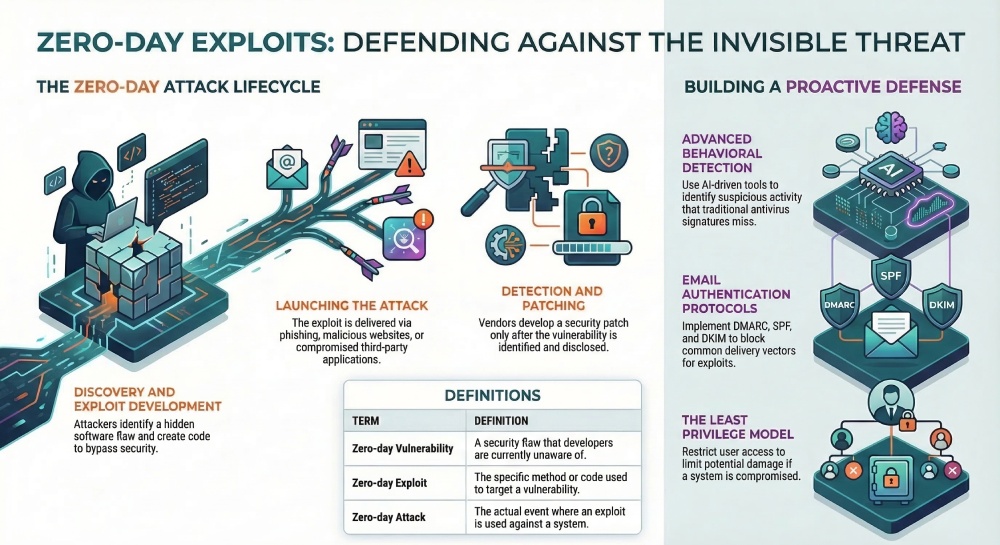
A zero-day exploit refers to a cyberattack that targets a previously unknown vulnerability in software, hardware, or firmware. The term “zero-day” indicates that developers have zero days to fix the vulnerability before attackers begin exploiting it.
To understand the concept more clearly, it helps to distinguish between three related terms:
- Zero-day vulnerability: A security flaw in software or hardware that developers are unaware of.
- Zero-day exploit: The method or code attackers use to take advantage of that vulnerability.
- Zero-day attack: The actual cyberattack that occurs when the exploit is used against a system.
Because these vulnerabilities are unknown to vendors and security teams, there are usually no patches or defensive mechanisms available at the time of exploitation. This makes zero-day attacks particularly dangerous compared with other cyber threats.
Zero-day exploits can affect many types of systems, including operating systems, browsers, enterprise software, mobile devices, and IoT devices. Attackers often sell or trade these vulnerabilities in underground markets, where high-value exploits can command extremely high prices.
Why Zero-Day Exploits Are So Dangerous
Zero-day exploits pose a major cybersecurity challenge because they give attackers a powerful advantage. Several factors contribute to their severity.
Unknown Vulnerabilities
The primary reason zero-day attacks are so dangerous is that the vulnerability is unknown to the software vendor. Since no one knows the flaw exists, no patch or mitigation is available. As a result, attackers can exploit systems freely until the issue is discovered.
High Success Rate
Because there are no existing defenses, zero-day exploits often have a high success rate. Traditional security tools that rely on known malware signatures may fail to detect them.
Targeted Attacks
Many zero-day attacks are used in targeted operations against governments, financial institutions, or large corporations. Cybercriminal groups and nation-state actors often invest significant resources into discovering and exploiting these vulnerabilities.
Rapid Damage
Once a zero-day exploit is discovered by attackers, it can spread quickly across vulnerable systems. Organizations may not realize they are under attack until significant damage has already occurred.
How Zero-Day Exploits Work
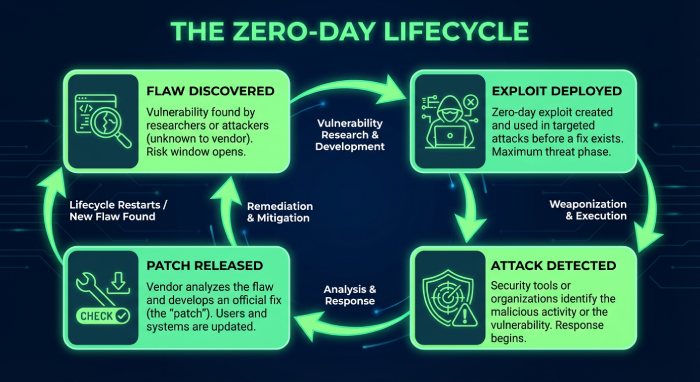
A zero-day exploit typically follows a lifecycle that begins with the discovery of a vulnerability and ends with the release of a patch. Understanding this lifecycle helps organizations recognize where defenses can be strengthened.
1. Vulnerability Creation
Software is complex, and even the most experienced developers can introduce security flaws unintentionally. These vulnerabilities may remain hidden for months or years.
2. Discovery by Attackers
Hackers, security researchers, or automated scanning tools eventually discover the vulnerability. If malicious actors find it first, they may develop an exploit before the vendor becomes aware of the flaw.
3. Exploit Development
The attacker creates code that takes advantage of the vulnerability to perform malicious actions such as executing unauthorized commands, gaining system access, or installing malware.
4. Launching the Attack
Once the exploit is ready, attackers distribute it through various methods, including phishing emails, malicious websites, infected software downloads, or compromised applications.
5. Detection and Disclosure
Eventually, security researchers or organizations detect suspicious activity and identify the vulnerability. The vendor is notified so they can begin working on a fix.
6. Patch Development
The software vendor develops and releases a security patch to fix the vulnerability. Organizations must then apply the patch to protect their systems.
Common Attack Vectors for Zero-Day Exploits
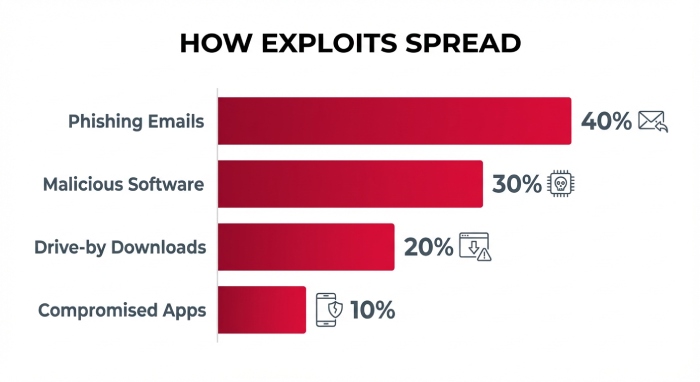
Zero-day exploits can be delivered through several attack methods. Cybercriminals often combine these techniques with social engineering or malware campaigns.
Malicious Email Attachments
Phishing emails frequently deliver files containing zero-day exploits. When a user opens the attachment, the exploit triggers and compromises the system.
Drive-By Downloads
Attackers may compromise websites and insert malicious scripts that automatically exploit vulnerabilities in visitors’ browsers.
Malware Distribution
Zero-day exploits are often embedded in malware such as ransomware, trojans, or worms that spread across networks.
Compromised Applications
Attackers sometimes hide exploits inside legitimate-looking applications or software updates.
Network Exploitation
Some zero-day attacks target network protocols or services to gain unauthorized access to servers and devices.
Real-World Examples of Zero-Day Exploits
Zero-day attacks have been responsible for several major cybersecurity incidents over the years.
For example, attackers once exploited a vulnerability in Adobe Flash through malicious spreadsheet attachments sent to employees of a security company. The exploit allowed hackers to gain remote access to systems and steal sensitive authentication data.
In recent years, large technology platforms such as browsers and enterprise software have also faced zero-day vulnerabilities. Security researchers continuously discover and patch these flaws to prevent widespread attacks.
These incidents demonstrate that even well-secured organizations can become targets if attackers discover a previously unknown vulnerability.
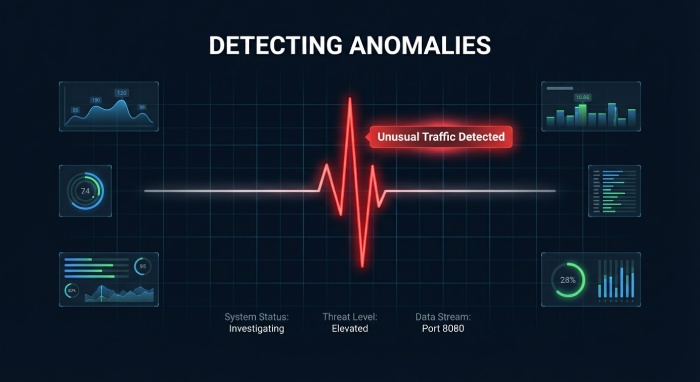
How to Detect Possible Zero-Day Attacks
Detecting zero-day exploits is challenging because they do not match known threat signatures. However, organizations can look for unusual system behavior that may indicate an attack.
Common warning signs include:
- Unexpected spikes in network traffic
- Suspicious activity on legitimate network ports
- Systems behaving abnormally despite being fully patched
- Unknown processes running on devices
- Unauthorized access attempts
Monitoring network behavior and system logs can help security teams detect anomalies that may signal a zero-day attack.
Best Practices to Prevent Zero-Day Exploits
Although zero-day vulnerabilities cannot always be prevented, organizations can significantly reduce their risk by implementing strong cybersecurity practices.
Keep Software Updated
Regularly updating operating systems, applications, and firmware ensures that known vulnerabilities are patched quickly. Software updates often contain critical security fixes that close potential entry points for attackers.
Use Advanced Threat Detection
Traditional antivirus solutions may not detect zero-day attacks. Advanced security tools that use behavioral analysis and machine learning can identify suspicious activity even when the threat is unknown.
Implement Network Monitoring
Continuous monitoring of network traffic helps detect unusual behavior that may indicate an exploit attempt. Intrusion detection and prevention systems are especially useful for identifying abnormal activity.
Restrict User Access
Applying the principle of least privilege ensures that users only have access to the systems and data necessary for their roles. This limits the damage attackers can cause if they compromise a user account.
Train Employees on Cybersecurity
Human error is one of the most common entry points for cyberattacks. Security awareness training can help employees recognize phishing emails, suspicious attachments, and malicious links.
Maintain Secure Data Backups
Regular backups ensure that organizations can recover quickly if a zero-day exploit leads to ransomware or data loss. A common approach is the 3-2-1 backup strategy, which keeps multiple copies of data stored in different locations.

The Role of Email Security in Zero-Day Defense
Email remains one of the most common delivery channels for cyberattacks. Phishing campaigns frequently use email attachments or links to distribute malware and exploit vulnerabilities.
At DMARCReport, we emphasize the importance of strong email authentication to prevent attackers from impersonating legitimate domains. Implementing protocols such as DMARC, SPF, and DKIM helps organizations detect spoofed emails and stop many attack attempts before they reach employees.
While these technologies cannot eliminate zero-day vulnerabilities themselves, they significantly reduce the chances of attackers delivering malicious payloads through email.
Final Thoughts
Zero-day exploits represent one of the most sophisticated and dangerous forms of cyberattack. By exploiting unknown vulnerabilities, attackers can bypass traditional defenses and compromise systems before patches are available.
For organizations, the key to reducing the risk of zero-day attacks lies in proactive security strategies. Continuous monitoring, advanced threat detection, regular patching, and strong email authentication all play critical roles in defending against these threats.
At DMARCReport, we believe that cybersecurity requires a layered approach. By combining robust email security with modern threat detection and employee awareness, organizations can significantly reduce their exposure to zero-day exploits and other advanced cyber threats.
Staying informed, vigilant, and prepared is the best defense in today’s rapidly evolving cybersecurity landscape.