What Is ARP Spoofing and How to Prevent It
Cyber threats continue to evolve as networks become more interconnected and data moves constantly between devices. While many organizations focus heavily on email-based threats such as phishing or domain spoofing, attackers also exploit weaknesses inside local networks. One of the most common techniques used to intercept network traffic is ARP spoofing.
ARP spoofing is a dangerous attack that allows cybercriminals to manipulate how devices communicate on a local network. By sending forged network messages, attackers can redirect traffic, steal sensitive data, or disrupt communication between systems. Understanding how this attack works and how to prevent it is essential for maintaining strong cybersecurity practices.
In this guide, the DMARCReport team explains what ARP spoofing is, how it works, the risks it creates for organizations, and the most effective ways to prevent it.
Understanding ARP and Its Role in Network Communication
Before exploring ARP spoofing, it is important to understand the purpose of ARP itself.
The Address Resolution Protocol (ARP) is responsible for translating an IP address into a physical hardware address known as a MAC address. This process allows devices within the same local area network (LAN) to communicate with each other efficiently. Address Resolution Protocol
When one device wants to send data to another device in the same network, it must know the recipient’s MAC address. If the MAC address is not already stored in the sender’s ARP cache, the device sends a broadcast request asking which device owns the target IP address. The device with the matching IP address replies with its MAC address, allowing communication to proceed.
This process happens automatically and continuously on local networks. However, the protocol was designed for efficiency rather than security, which leaves it vulnerable to manipulation.
Because ARP does not verify whether the messages it receives are legitimate, attackers can send fake responses that trick devices into accepting incorrect information.
What Is ARP Spoofing?
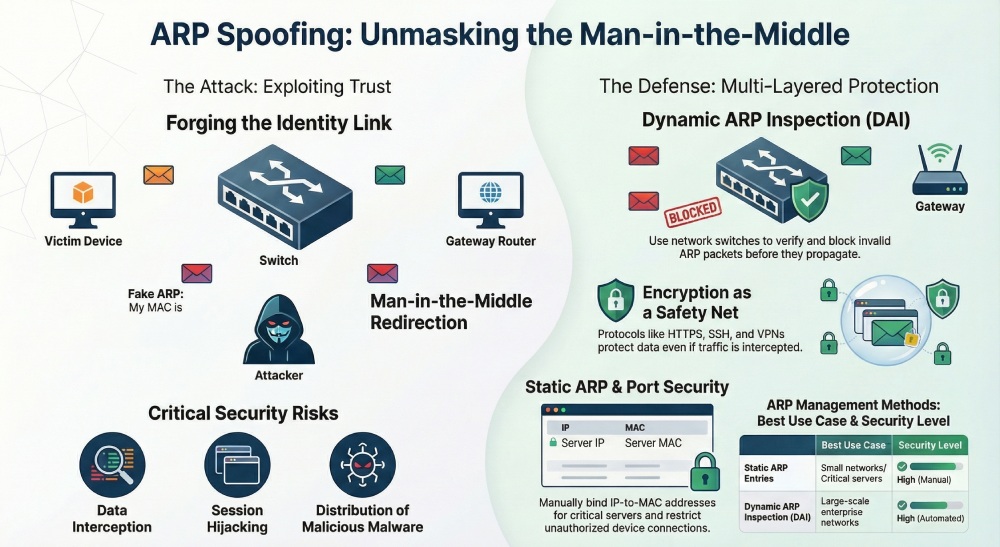
ARP spoofing, also known as ARP poisoning, is a cyberattack in which an attacker sends forged ARP messages across a network to associate their MAC address with the IP address of another device.
Once this mapping is accepted by other devices, network traffic intended for the legitimate device is instead redirected to the attacker’s machine.
This gives the attacker several capabilities:
- Intercept sensitive information
- Modify transmitted data
- Monitor communication between devices
- Block network traffic completely
Because the attacker inserts themselves between communicating devices, ARP spoofing is commonly used as a man-in-the-middle attack.
The victim devices continue to operate normally, unaware that their traffic is being rerouted. As a result, the attack can remain undetected for long periods.
How ARP Spoofing Attacks Work
To understand the impact of ARP spoofing, it helps to look at how attackers manipulate the protocol.
In a normal network communication process, a device sends an ARP request asking for the MAC address associated with a particular IP address. The correct device responds with its MAC address, and the information is stored in the ARP cache for future communication.
During an ARP spoofing attack, the attacker sends fake ARP responses claiming that their MAC address belongs to the IP address of a trusted device, such as a gateway or server. Because ARP lacks authentication, the receiving devices update their ARP cache with the malicious mapping.
As a result, traffic intended for the legitimate device is redirected to the attacker instead.
This manipulation allows attackers to position themselves between two communicating devices and control the flow of information. From this point, they can:
- Monitor network traffic
- Capture login credentials
- Modify data packets
- Inject malicious content
- Interrupt communication entirely
The attack works particularly well on local networks where devices frequently update their ARP tables.
Risks and Consequences of ARP Spoofing
Although ARP spoofing occurs within local networks, its impact can extend far beyond a single system. Once attackers gain the ability to intercept traffic, they can exploit multiple types of vulnerabilities.
Data Interception
One of the primary goals of ARP spoofing is to capture sensitive information such as usernames, passwords, or confidential files. If traffic is not encrypted, attackers can easily read intercepted data.
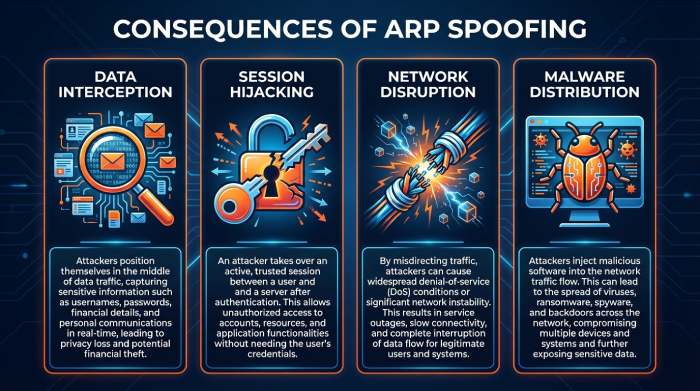
Session Hijacking
Attackers may hijack active sessions between users and applications. By stealing session cookies or authentication tokens, they can impersonate legitimate users and gain unauthorized access to systems.
Network Disruption
Attackers can also use ARP spoofing to disrupt communication across the network. By manipulating ARP tables, they can block traffic entirely and create denial-of-service conditions.
Malware Distribution
When attackers control network traffic, they may inject malicious code into communications or redirect users to harmful websites.
Reputation and Financial Damage
For businesses, successful network attacks can result in data breaches, regulatory penalties, and loss of customer trust.
These risks highlight why organizations must monitor network behavior and implement strong defensive measures.
How to Detect ARP Spoofing
Because ARP spoofing operates at the network level, detection can sometimes be challenging. However, several indicators may reveal suspicious activity.
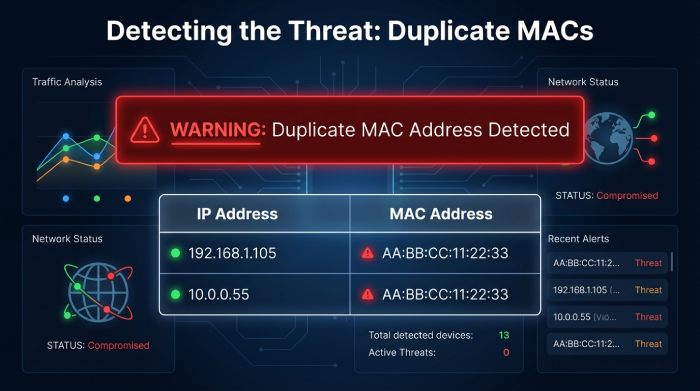
One common warning sign is frequent or unexpected changes in ARP table entries. If a single MAC address suddenly appears associated with multiple IP addresses, this could indicate malicious manipulation.
Network monitoring tools can also detect unusual ARP traffic patterns, duplicate IP-to-MAC mappings, or abnormal routing behavior. Security systems such as intrusion detection systems (IDS) can raise alerts when they identify spoofing patterns within network traffic.
Administrators may also use command-line tools to inspect ARP tables and identify suspicious mappings manually.
Although detection methods exist, prevention remains the most effective strategy.
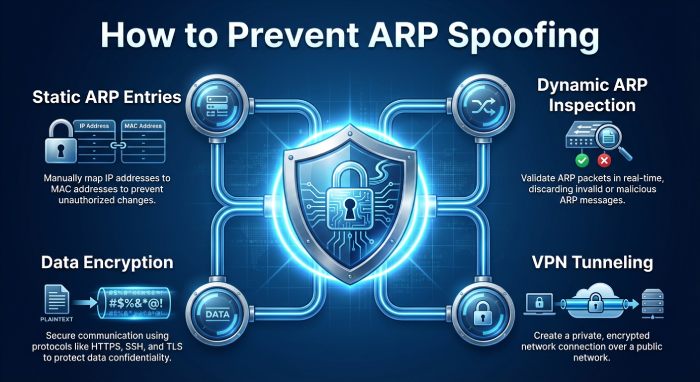
Effective Methods to Prevent ARP Spoofing
Organizations can significantly reduce the risk of ARP spoofing by implementing several security measures.
Static ARP Entries
One of the simplest defenses involves creating static ARP entries for important devices such as routers or servers.
Static entries bind a specific IP address to a known MAC address and prevent unauthorized updates to that mapping. This reduces the risk of attackers altering the ARP table with forged messages.
However, this approach requires manual configuration and may not scale well in large networks.
Dynamic ARP Inspection
Dynamic ARP Inspection (DAI) is a security feature available on many network switches. It verifies ARP messages against trusted records before allowing them to propagate across the network.
If an ARP packet contains invalid information, the switch blocks it automatically. This prevents attackers from successfully poisoning ARP tables.
Encryption Protocols
Encrypting network communication is one of the most important defenses against interception.
Even if attackers manage to redirect traffic using ARP spoofing, encryption prevents them from reading or altering the intercepted data. Secure protocols such as HTTPS, SSH, and TLS ensure that sensitive information remains protected.
Virtual Private Networks (VPNs)
A virtual private network(VPN) creates a secure encrypted tunnel between devices and the network.
When traffic is encrypted through a VPN, attackers cannot easily view or manipulate intercepted communications. This is especially important for remote workers using public Wi-Fi networks.
Packet Filtering
Packet filtering tools analyze network traffic and block suspicious ARP packets before they reach target devices.
By monitoring network activity in real time, these systems can identify spoofed messages and prevent them from entering the network.
Port Security
Switch port security limits which devices can connect to specific network ports. By restricting the allowed MAC addresses, administrators can prevent unauthorized devices from participating in network communication.
This reduces the chances that attackers can inject malicious ARP messages into the network.
Continuous Network Monitoring
Proactive monitoring is essential for detecting early signs of spoofing attempts.
Security teams should track ARP traffic patterns, monitor unusual device behavior, and respond quickly to anomalies. Early detection helps minimize the potential damage caused by an attack.
Why ARP Spoofing Still Matters Today
Although ARP spoofing has been known for many years, it remains a relevant threat because many networks still rely on legacy protocols that lack built-in authentication.
The growth of remote work, shared networks, and Internet-connected devices has increased the number of environments where attackers can exploit ARP vulnerabilities.
Cybercriminals frequently combine ARP spoofing with other techniques such as phishing, malware distribution, or credential theft to launch more sophisticated attacks.
For organizations focused on protecting email systems and domain reputation, network-level security is just as important as email authentication.
Security frameworks that include both network protection and email authentication protocols provide stronger overall defense against modern threats.
DMARC, DKIM, and SPF are essential email authentication protocols that protect your domain from spoofing, phishing, and unauthorized use by verifying sender identity and ensuring message integrity.
Final Thoughts
ARP spoofing is a powerful technique that attackers use to manipulate network communication, intercept data, and launch man-in-the-middle attacks. Because the protocol itself lacks authentication, malicious actors can exploit it by sending forged ARP messages that redirect traffic through their own systems.
The good news is that organizations can significantly reduce the risk by implementing proper security measures. Static ARP entries, dynamic ARP inspection, encryption protocols, VPNs, and network monitoring all play important roles in defending against these attacks.
At DMARCReport, we believe that cybersecurity requires a layered approach. Protecting your network infrastructure, encrypting communications, and strengthening email authentication protocols together create a more resilient defense against modern cyberthreats.
By understanding how attacks like ARP spoofing work and implementing proactive security strategies, organizations can protect their networks, safeguard sensitive information, and maintain trust in their digital communications.







