What Is a Password Attack in Cyber Security?
Understanding Methods, Risks, and Prevention Strategies
Passwords remain one of the most widely used authentication mechanisms in modern digital systems. From personal email accounts to enterprise cloud platforms, passwords protect sensitive data and system access across the internet. However, because they are so common, they have also become one of the most targeted elements in cyberattacks.
At DMARCReport, we frequently observe how compromised credentials become the starting point for much larger cyber incidents, including phishing campaigns, business email compromise, and domain impersonation. Among the most common techniques used by cybercriminals is the password attack, a method designed to gain unauthorized access to systems by stealing or cracking login credentials.
Understanding how password attacks work—and how to defend against them—is essential for organizations that want to maintain strong cybersecurity and protect their digital infrastructure.
What Is a Password Attack?
A password attack is a type of cyberattack in which an attacker attempts to gain access to a system, network, or account by obtaining or guessing a user’s password. This process may involve automated tools, social engineering tactics, malware, or stolen credential databases.
The primary objective of a password attack is unauthorized access. Once attackers successfully obtain credentials, they can infiltrate systems, steal data, send malicious emails, or escalate privileges within an organization’s network.
Because many users rely on weak or reused passwords, attackers often find password attacks to be one of the most effective entry points into corporate environments. In many data breaches, compromised login credentials serve as the initial access vector before attackers move laterally through the system.
From a security perspective, passwords represent both a necessity and a vulnerability. While they provide basic authentication, they can also become a weak link if not properly managed.
Why Password Attacks Are So Effective
Password attacks continue to succeed for several reasons related to human behavior and system design.
First, many users still choose predictable passwords. Common patterns such as birthdays, pet names, or simple combinations like “Password123” remain widespread. These weak credentials make it easy for attackers to guess passwords using automated tools.
Second, password reuse significantly increases security risks. When a user reuses the same password across multiple services, a single breach can expose several accounts. Attackers exploit this behavior through automated credential testing across multiple platforms.
Third, organizations sometimes lack sufficient security controls such as multi-factor authentication or login monitoring. Without these protective layers, attackers can repeatedly attempt login combinations until they successfully gain access.
Because of these factors, password attacks remain one of the most common cyber threats targeting both individuals and enterprises.
How Password Attacks Work
In most cases, password attacks rely on automated tools designed to test thousands or even millions of possible password combinations. These tools analyze common password patterns, leaked credentials, and known word lists to accelerate the cracking process.
The attack typically follows several stages.
First, attackers identify potential targets. This may involve collecting email addresses, usernames, or account details through phishing campaigns, data breaches, or publicly available information.
Next, attackers deploy specialized software to attempt login combinations or exploit stolen credential lists. These automated tools can rapidly test thousands of login attempts within seconds.
If successful, attackers gain unauthorized access to the account. From there, they may steal sensitive data, distribute malware, or impersonate the victim to launch additional attacks.
Because these processes are often automated, password attacks can be conducted on a massive scale, targeting thousands of accounts simultaneously.
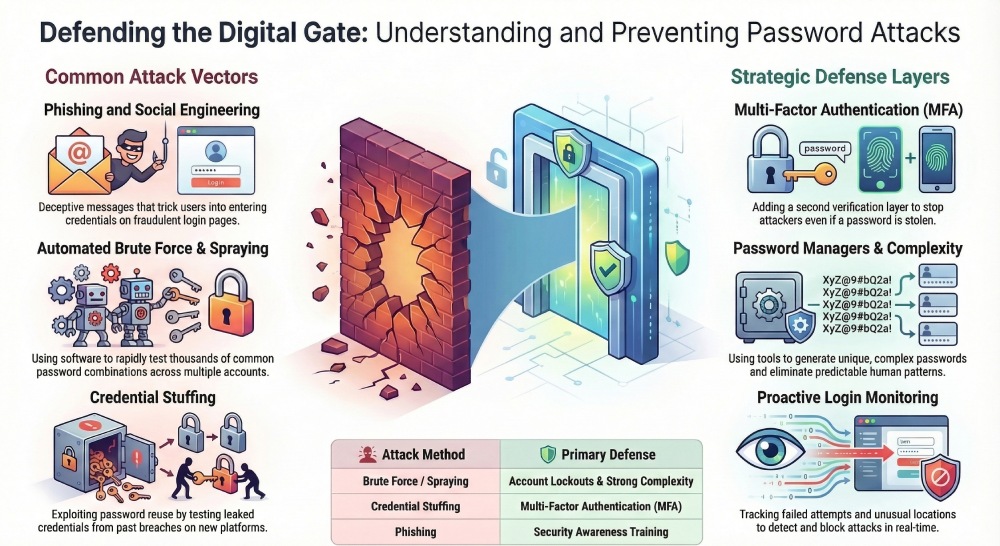
Common Types of Password Attacks
Password attacks take many forms, depending on the techniques and tools used by cybercriminals. Understanding the different types can help organizations recognize and prevent them more effectively.
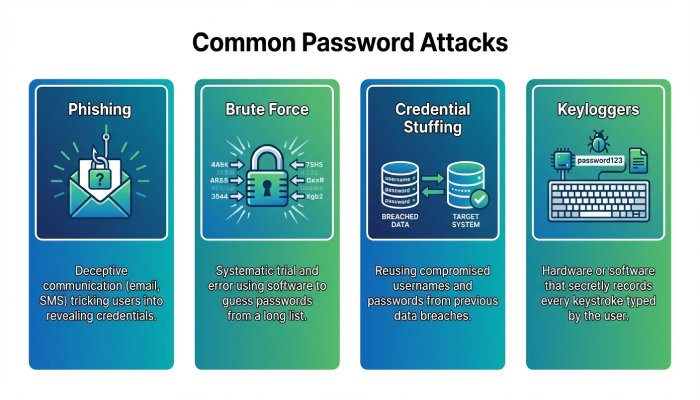
Phishing Attacks
Phishing is one of the most common techniques used to steal passwords. In this attack, cybercriminals send fraudulent emails or messages that appear to come from legitimate organizations.
Victims are usually asked to click a link and log in to their account to resolve an issue or verify their identity. However, the link leads to a fake login page designed to capture the user’s credentials.
Once the victim enters their username and password, the attacker records the information and uses it to access the real account.
Phishing remains highly effective because it targets human psychology rather than technical vulnerabilities.
Brute Force Attacks
A brute force attack is a trial-and-error method where attackers systematically test numerous password combinations until they find the correct one. Automated tools enable attackers to attempt thousands of guesses within a short period of time.
These attacks rely on computational power rather than deception. Weak or short passwords can often be cracked quickly using this approach.
Two common variations of brute force attacks include password spraying and dictionary attacks.
Password Spraying
Password spraying involves testing a small number of commonly used passwords across many different accounts.
Instead of attempting many passwords on one account, attackers try the same password across multiple accounts. This technique helps avoid triggering account lockouts that occur after too many failed attempts.
For example, attackers might test passwords such as “Welcome123” or “Company2025” across hundreds of employee accounts.
Because organizations often enforce similar password policies, password spraying can sometimes lead to successful compromises.
Dictionary Attacks
Dictionary attacks rely on lists of commonly used words and phrases. Attackers use precompiled dictionaries that include popular passwords, common names, movie characters, and frequently used phrases.
Rather than testing every possible character combination, the attacker focuses on likely password choices based on human behavior.
This significantly reduces the time required to crack weak passwords.
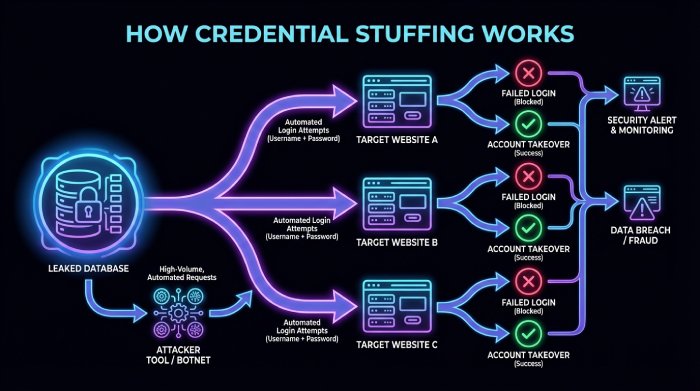
Credential Stuffing
Credential stuffing is another widespread password attack technique. Instead of guessing passwords, attackers use credentials that were previously leaked in data breaches.
They then attempt to log in to other websites using those same username-password combinations. This method works because many users reuse the same password across multiple accounts.
Automated scripts allow attackers to test millions of credential pairs against login pages across different platforms.
If even a small percentage of those credentials work, attackers can gain access to a large number of accounts.
Keylogger Attacks
Keylogger attacks involve malware that records every keystroke typed on a device. When a victim types a password, the malware captures the information and sends it to the attacker.
Keyloggers may be installed through malicious downloads, phishing emails, or compromised websites.
Because keyloggers capture passwords directly from user input, they can bypass even complex password policies.
Man-in-the-Middle (MitM) Attacks
In a Man-in-the-Middle attack, the attacker intercepts communication between a user and a legitimate service. This often occurs on unsecured networks such as public Wi-Fi.
The attacker secretly captures login credentials as they are transmitted between the user and the server.
Once intercepted, these credentials can be used to access the victim’s account without their knowledge.
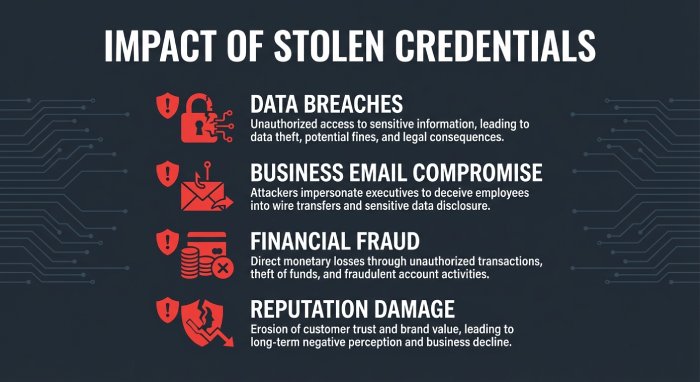
Real-World Impact of Password Attacks
The consequences of successful password attacks can be severe. Compromised credentials can allow attackers to infiltrate email systems, cloud services, financial platforms, and internal business applications.
For organizations, the risks include:
- Data breaches and information theft
- Business email compromise (BEC) attacks
- Financial fraud and unauthorized transactions
- Loss of customer trust and brand reputation
- Regulatory penalties and legal consequences
Additionally, attackers who gain access to email accounts may launch further phishing campaigns from legitimate addresses, making their attacks more convincing.
This is why organizations increasingly combine password security with email authentication technologies such as SPF, DKIM, and DMARC to strengthen overall protection against cyber threats.
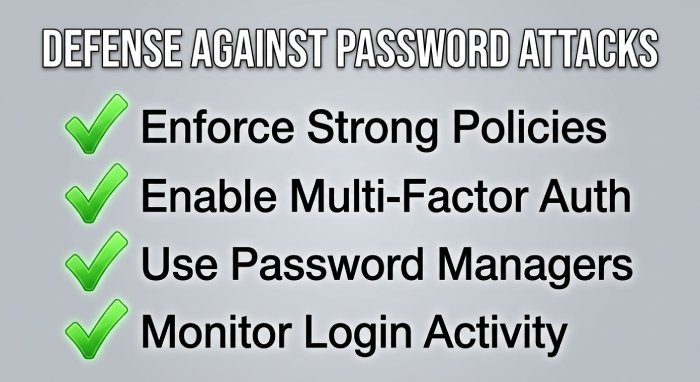
How to Prevent Password Attacks
While password attacks are common, they can be significantly reduced through proper security practices and organizational policies.
Enforce Strong Password Policies
Strong passwords remain one of the most effective defenses against password attacks. Passwords should include a mix of uppercase and lowercase letters, numbers, and special characters.
Organizations should also enforce minimum length requirements and discourage predictable patterns such as names or birthdates.
Encouraging the use of unique passwords for every account also prevents credential reuse vulnerabilities.
Enable Multi-Factor Authentication
Multi-factor authentication (MFA) adds an additional security layer beyond the password. Even if attackers obtain a password, they still need a second authentication factor such as a one-time code or biometric verification.
This simple measure dramatically reduces the success rate of password attacks.
Implement Security Awareness Training
Employees are often the first line of defense against password attacks.
Security awareness training can help users recognize phishing attempts, suspicious login pages, and other tactics used to steal credentials.
Educating employees about safe password practices can significantly reduce organizational risk.
Use Password Managers
Password managers help users create and store complex passwords securely. Instead of relying on memory, users can generate unique passwords for each service.
This reduces the temptation to reuse credentials across multiple platforms.
Monitor Login Activity
Organizations should implement monitoring systems that detect unusual login patterns such as multiple failed attempts, logins from unknown locations, or suspicious IP addresses.
Early detection allows security teams to respond quickly before attackers gain deeper access to systems.
Final Thoughts
Password attacks remain one of the most persistent threats in cybersecurity. By exploiting weak passwords, credential reuse, and human behavior, attackers can gain unauthorized access to sensitive systems and data.
However, organizations can significantly reduce this risk through strong password policies, multi-factor authentication, employee training, and proactive monitoring.
At DMARCReport, we emphasize that password security should always be part of a broader cybersecurity strategy. Protecting user credentials, strengthening email authentication, and maintaining visibility into account activity all contribute to a more resilient digital environment.
As cyber threats continue to evolve, organizations that prioritize password security will be far better prepared to defend against unauthorized access and safeguard their critical assets.