Shadow IT in the Hybrid Workplace: Hidden Risks Beyond Email
Work looks different now, doesn’t it? Employees are the reason. Recent research from Gallup shows that six in ten employees prefer a hybrid work arrangement.
No wonder the offices are now spread out, and so is the control IT once had. That makes it much harder to keep everyone secure. This shift has amplified a longstanding but often overlooked threat, and that is, shadow IT.
This refers to the use of unauthorized software, applications, devices, or cloud services by employees without IT department approval or oversight.
Shadow IT isn’t new, but hybrid work makes it worse. When official tools are slow or difficult to access from home, employees turn to personal apps such as WhatsApp, Dropbox, or Google Drive. This creates security risks that go far beyond simple email threats.
Below, we’ll walk you through the risks of shadow IT that extend beyond email in the hybrid workplace.

#1 The Rise of the Citizen Integrator
Not long ago, connecting two business applications required a developer, and probably a few tense meetings about application programming interface (API) documentation.
But low-code and no-code (LCNC) platforms have handed that power to virtually anyone with a browser and an hour to spare. The result is a new kind of workplace persona, which is the citizen integrator.
In hybrid setups, where teams are scattered and collaboration tools are king, citizen integrators thrive. They solve immediate pain points, but often create ungoverned integrations that handle sensitive data without security controls.
The trend is exploding. Research from 2025 shows that about 65% of companies are letting regular employees (non-tech staff) build their own software tools to address unfinished IT work.
Risks go beyond inefficiency. Unmanaged integrations can leak data across apps or create compliance gaps, such as under the General Data Protection Regulation (GDPR).
The fix isn’t to ban no-code tools. That ship has sailed. The smarter approach is governance by design. You must establish an approved list of integration platforms, require business justification for new automations, and build lightweight review processes that don’t take weeks.
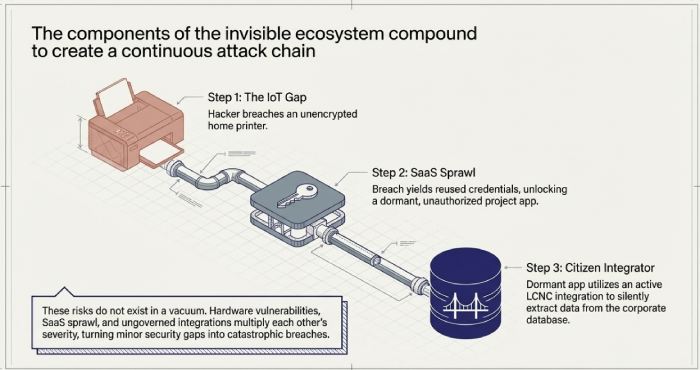
2. Hardware Shadowing and the Internet of Things (IoT) Gap
Shadow IT isn’t just software; it also includes hardware. Employees bring in personal laptops, smart home devices synced to work accounts, or unauthorized IoT gadgets like smart plugs.
The line between home and work blurs in the hybrid workplace. Someone might plug a personal router extender into their home setup for better Zoom calls, or connect a smart thermostat that logs into corporate cloud services. This creates a security blind spot.
Since the IT team doesn’t know these devices exist, they can’t protect them. That gives hackers an easy backdoor to access the company’s network.
One of the most overlooked risks in this IoT gap is the home printer. Unmanaged peripherals often lack the robust encryption found in office environments.
However, implementing wireless remote printing can ensure all data stays within a managed, encrypted tunnel.
eCopier Solutions explains that services like eZeep and PaperCut Mobility Print facilitate wireless remote printing. These cloud services use encryption to keep data safe and offer management features all without the hassle of a VPN.
That means you can safely print from your phone or personal laptop while maintaining a full audit trail for the IT department.
3. Proliferation of SaaS Sprawl
SaaS sprawl is the ultimate shadow IT multiplier. Employees sign up for tools like Notion, Slack alternatives, or niche project apps without the IT department’s knowledge. This sprawl happens fast in hybrid work, where teams need instant collaboration.
This leads to significant identity fragmentation. Employees often reuse passwords or fail to enable multi-factor authentication. This makes credential theft a high-value target for attackers.
Many unmanaged apps use Open Authorization (OAuth) tokens to integrate with sanctioned enterprise tools like Salesforce or Slack. This creates a fourth-party risk, where a breach in a seemingly minor, unmanaged tool can provide an attacker with a pathway into the organization’s most sensitive data.
In late 2025, a major supply chain attack exploited stolen OAuth tokens from a single integration to access customer environments across more than 700 organizations.
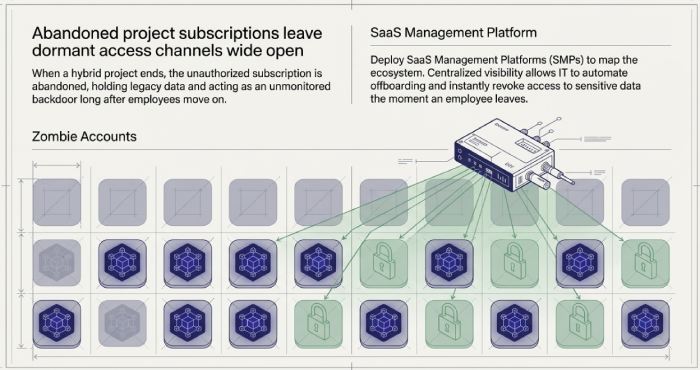
To mitigate this, you must hunt for zombie accounts. These are basically abandoned subscriptions that hold legacy data long after a project ends. These dormant apps remain unmonitored backdoors unless mapped through SaaS management platforms (SMPs) to centralize visibility and automate offboarding.
This ensures that access to sensitive data is revoked immediately when an employee leaves. This is a critical step in preventing breaches caused by orphaned accounts.
Turning Risks into Managed Innovation
Shadow IT in the hybrid workplace goes way beyond email. It’s an invisible ecosystem of SaaS sprawl, citizen integrator, and unmanaged IoT.
Once you acknowledge these risks, you can begin to build a security posture that is as flexible and dynamic as the workforce it protects.
Keep in mind, though, that shadow IT will never be fully eliminated nor should it be. The goal is to shrink the shadow by expanding what is trusted, sanctioned, and understood. That’s not just good security practice in the hybrid workspace, but good management.







