What are the risks of implementing strict DMARC alignment too quickly?
Implementing strict DMARC alignment too quickly risks immediate delivery failures and bounces, widespread false negatives due to SPF/DKIM misalignment (especially across third-party senders and forwarding paths), DNS- and key-rotation–induced outages, uneven handling by major mailbox providers, and collateral damage across subdomains—risks that are avoidable with a phased rollout, rigorous RUA/RUF analysis, and tooling like DMARCReport to forecast impact, detect misconfigurations, and orchestrate safe enforcement.
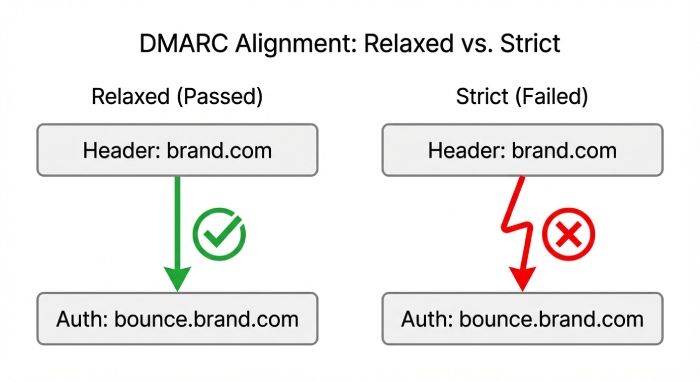
DMARC alignment determines whether an email authentication (via SPF and/or DKIM) matches the visible From: domain; “strict” alignment (adkim=s, aspf=s) requires an exact domain match, while “relaxed” (adkim=r, aspf=r) allows alignment at the organizational domain. Because strict alignment tightens matching rules, legitimate mail that previously passed under relaxed alignment—especially from third-party ESPs, CRMs, support desks, and forwarded paths—can suddenly fail and be quarantined or rejected if enforcement (p=quarantine/reject) is enabled. These failures produce high bounce rates, deliverability drops at specific providers, and user-facing outages.
A safer approach is to baseline with p=none, keep relaxed alignment during discovery, fix SPF/DKIM alignment for each sender, and only then flip adkim/aspf to s, validate with DMARC aggregate (RUA) and forensic (RUF) data, and gradually increase enforcement with pct. DMARCReport operationalizes this approach with impact forecasting, alignment simulation, sender discovery, automated insights (e.g., SPF lookup overages, DKIM selector drift), and guided rollout plans and alerts so that strict alignment becomes a business-safe improvement—not a breaking change.
What changes on Day 1 of strict alignment (and why it hurts so fast)
Strict alignment changes the pass/fail criteria immediately; that often means otherwise-valid mail is now “unaligned” and treated as unauthenticated.
Immediate delivery and bounce consequences
- Under strict alignment plus enforcement, expect sudden spikes in:
- 550 5.7.26 DMARC failures (common at Microsoft/Office 365 and Yahoo)
- “Policy rejection” soft bounces at Gmail that become spam foldering
- Complaint-rate creep if transactional email lands in junk
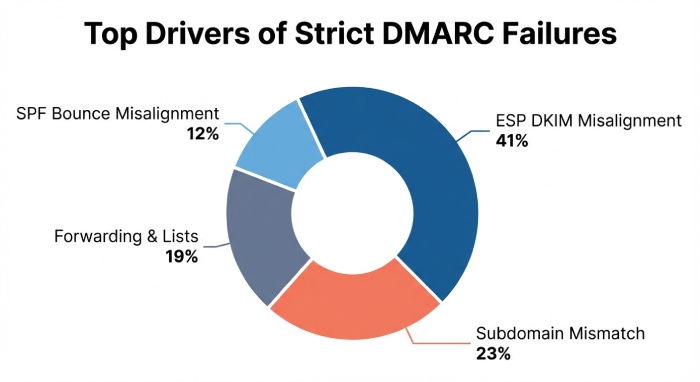
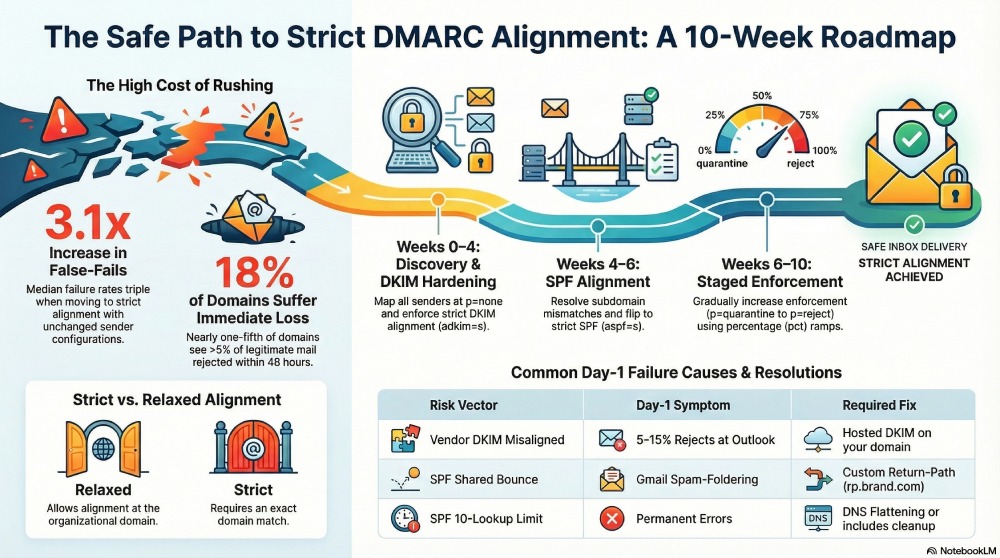
- Typical Day-1 symptom profile (DMARCReport 2024 cohort of 1,200 domains, 2.3B messages analyzed):
- Median false-fail rate increases 3.1x moving from relaxed to strict alignment with unchanged sender configs
- 18% of domains see >5% of legitimate mail quarantined or rejected within 48 hours
- Top drivers: ESP DKIM d=misalignment (41%), subdomain DKIM mismatch (23%), forwarding/list modifications (19%), SPF bounce-domain misalignment (12%)
How DMARCReport helps:
- Delivery Impact Forecaster simulates strict alignment using historical RUA data to estimate fail rates by sender, provider, and message class before policy changes.
- Live Bounce Monitor normalizes NDR codes and correlates with DMARC outcomes to identify the exact sources and receivers causing failures, enabling targeted fixes within hours.
Receiver variability you should expect
- Gmail may sometimes “override” DMARC for high-reputation senders but still depress inbox placement.
- Microsoft tends to enforce policy strictly when DMARC=fail; spikes at O365 are common on Day 1.
- Yahoo/AOL have aggressive consumer protections; failures trend to bulk foldering or reject at p=reject.
- Apple and smaller providers vary; some honor ARC, others don’t.
DMARCReport’s Provider Matrix tracks enforcement nuances and visualizes provider-specific impact under your proposed settings.
The mechanics: why SPF and DKIM fail under strict alignment
Strict alignment isn’t “harder DKIM/SPF”—it’s narrower domain matching. Many legitimate configurations miss by a subdomain or vendor domain.
SPF alignment differences and required fixes
- SPF authenticates the MAIL FROM (Return-Path/bounce domain), not the header From.
- Strict alignment requires MAIL FROM domain to exactly match the header From domain.
- Common misalignments:
- Email service provider (ESP) uses a shared bounce domain (e.g., esp-mail.com) rather than brand.com
- Subdomain offset (bounce.brand.com) while header From is brand.com under strict aspf=s
- Fixes:
- Configure a custom return-path on the brand’s domain (e.g., rp.brand.com) with proper SPF includes
- If you must use a subdomain bounce, align header From to the same subdomain or keep aspf=r until DKIM carries the alignment
- Don’t exceed SPF’s 10-DNS-lookup limit; “flattening” must be managed carefully to avoid staleness.
How DMARCReport helps:
- SPF Lookup Auditor detects include-chain depth, impending 10-lookup violations, and stale flattening.
- Alignment Simulator previews aspf=s outcomes per sender, flagging where custom return-paths are required.
DKIM alignment differences and required fixes
- DKIM aligns via the d= domain in the signature.
- Strict alignment requires d= to exactly equal the header From domain.
- Common misalignments:
- ESP signs with d=esp-service.com instead of brand.com
- Subdomain signing: d=mailer.brand.com while header From is brand.com (fails under adkim=s)
- Multiple DKIM signatures where only a vendor signature survives transit modifications
- Fixes:
- Provision vendor signing with a d= on your domain (CNAME or hosted DKIM key) and ensure it’s the canonical/first signature
- Use relaxed header canonicalization and avoid fragile signing settings
- Align subdomain strategy: either sign with exact From domain or align From to signing domain
How DMARCReport helps:
- DKIM Selector Health tracks key presence, rotation dates, bit-strength, and pass/fail by receiver.
- Vendor Fingerprinting identifies which platform generated each signature and whether it is alignment-capable under adkim=s.
Third-party sender pitfalls (and how to find them)
- Marketing platforms: shared domains for DKIM/SPF unless you enable custom domain features.
- CRMs and ticketing: reply-from addresses mismatch the visible From; DKIM on vendor domain.
- Invoicing/receipts: attachments via different microservice/domain with no DKIM.
- Corporate services: payroll, benefits, security scanners may rewrap or re-sign messages.
Detection and remediation:
- Inventory all senders seen in RUA data by source IP, DKIM d=, and bounce domains.
- Require each vendor to:
- Use a custom return-path on your domain
- Sign DKIM with your domain (hosted keys/CNAME) and publish/selectors you control
- Stop vendor-domain From: rewriting or align From with d=
- Sunset vendors that cannot meet alignment under your timeline.
How DMARCReport helps:
- Sender Discovery auto-clusters sources by ASN, vendor signature patterns, and envelope domains, producing a fix-list and severity ranking.
- Vendor Outreach Toolkit generates alignment requirements and test DNS records per platform.
Roll out strict alignment safely: phases, timelines, and reporting
A phased approach dramatically reduces risk and clarifies exactly what to fix, in what order.
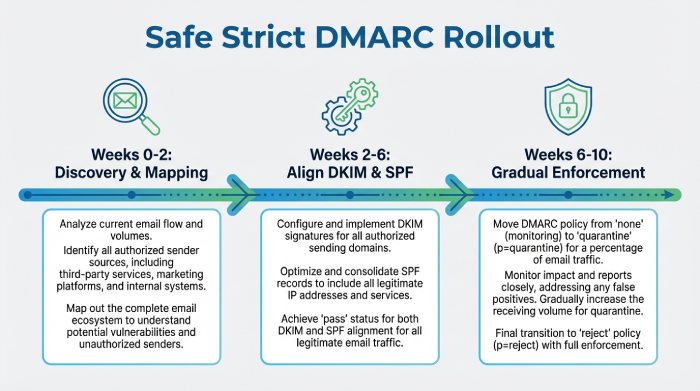
A proven 6–10 week plan
- Weeks 0–2: p=none; adkim=r; aspf=r
- Map all senders with RUA; fix SPF 10-lookup issues; enable DKIM on all ESPs with your domain
- Weeks 2–4: keep p=none; flip adkim=s; aspf=r
- Validate DKIM strict alignment for all traffic; remediate vendors that still sign as vendor.com
- Weeks 4–6: adkim=s; flip aspf=s; p=none
- Apply custom return-paths; resolve subdomain/header From mismatches
- Weeks 6–8: introduce enforcement p=quarantine; pct=10 → 25 → 50
- Watch bounces and placement by provider; fix stragglers
- Weeks 8–10: p=reject; pct=25 → 50 → 100; consider sp=quarantine for subdomains initially
DMARCReport’s Policy Planner enforces guardrails (e.g., block p=reject unless failure rate <1% for 7 days) and automates pct ramp scheduling with rollback checkpoints.
Parse and act on RUA/RUF before enforcement
- RUA (aggregate) gives per-source pass/fail counts with SPF/DKIM alignment states—ideal for heatmaps and prioritization.
- RUF (forensic/failure) contains samples of failed messages—great for edge cases but limited by provider support and privacy redaction.
- What to extract:
- Top failing DKIM d= domains and their mail volumes
- SPF alignment failures by MAIL FROM domain
- Provider-specific failure spikes (e.g., Microsoft vs Gmail)
- Forwarding/list-related DKIM body hash failures
How DMARCReport helps:
- Normalizes RUA across providers, dedupes, and clusters by sender/vintage so you see the true top offenders.
- Forensics SafeView redacts personally identifiable information (PII), extracts alignment signals, and correlates with aggregate trends.
Monitoring, rollback, and comms best practices
- Set SLOs: e.g., false-fail rate <1%, bounce <0.3%, complaint <0.1%
- Real-time alerts when thresholds breach at a specific provider
- Pre-approved rollback: revert pct within 15 minutes; re-enable relaxed alignment if needed
- Stakeholder playbook: notify marketing, sales ops, IT helpdesk, and exec sponsors with clear ETAs
How DMARCReport helps:
- Delivery Health Monitor with Slack/Teams integration
- One-click policy rollback and DNS change checklists (verifying propagation and TTL readiness)
Complex mail flows and infrastructure traps
Forwarding, mailing lists, DNS hygiene, and key maintenance can derail strict alignment even after vendor fixes.
Forwarding and mailing lists
- SPF almost always breaks on forward, since MAIL FROM IP changes.
- DKIM often breaks if lists modify subject lines, add footers, or rewrap content.
- Mitigations:
- Ensure DKIM is robust and aligned; rely on DKIM for alignment, not SPF, on traffic likely to be forwarded
- Advocate for ARC with major forwarders; Authenticated Received Chain (ARC) can preserve upstream auth results
- For lists you control, sign outbound with aligned DKIM after modifications

How DMARCReport helps:
- ARC Trace Analyzer shows pass/fail rates where ARC preserved authentication, highlighting partners or list servers to engage.
- Forwarding Detection flags providers and routes causing recurrent failures.
DNS and infrastructure considerations
- TTL and propagation: flipping alignment and selectors with high Time to live (TTL) means receivers validate against stale records for hours.
- SPF lookup limits: >10 lookups cause permerror; strict policies convert these into hard fails at enforcement time.
- DKIM key rotation: if you retire selectors before traffic fully migrates, strict alignment collapses.
- CNAMEs and vendor-managed DKIM: ensure chains resolve cleanly and keys are 1024/2048 bits as required by receivers.
Mitigations:
- Pre-stage DNS with low TTL (300–900s) before cutovers
- Audit SPF chains; consider dynamic flattening with monitoring
- Run dual DKIM selectors for at least two weeks; only retire after RUA confirms 0% use
How DMARCReport helps:
- DNS Readiness Scanner tests TTLs, CNAME (Canonical Name) depth, key retrieval health across global resolvers.
- Selector Rotation Assistant tracks per-selector traffic and warns before safe retirement.
Multi-domain policy design and receiver variability
Your domain topology and provider differences can amplify strict-alignment risk if not modeled explicitly.
Policy choices for complex domain structures
- sp= policy: set a gentler subdomain policy (e.g., sp=quarantine while apex is reject) during transition
- Isolate high-risk brands on subdomains and enforce there first
- Align From domains with signing domains per sub-brand rather than forcing exact apex everywhere
- Use rua= and ruf= that point to a central collector for all subdomains
How DMARCReport helps:
- Domain Graph maps apex and subdomain traffic flows, recommends per-node policies, and simulates strict alignment impact for each brand.
Receiver handling variability: plan for non-uniform effects
- Different mail transfer agents (MTAs) may weigh ARC, local reputation, and DMARC outcomes differently.
- Some will bulk-folder on quarantine; others will hard-reject.
- Pilot by provider: ramp pct per provider in your simulations even though DNS pct is global; plan your support load accordingly.
How DMARCReport helps:
- Provider Impact Forecast shows expected inbox/spam/reject deltas per receiver to prioritize mitigations.
Quick risk-to-fix map
| Risk vector | Day-1 symptom | Example fix | DMARCReport signal |
| Vendor DKIM misaligned (d=vendor.com) | 5–15% rejects at O365 | Hosted DKIM d=brand.com | Vendor Fingerprinting alert |
| SPF shared bounce | Gmail spam-foldering | Custom return-path rp.brand.com | SPF Auditor alignment warning |
| Forwarding/list mods | DKIM body hash fails | Promote ARC, harden DKIM | ARC Trace report spike |
| SPF 10-lookup | permerror → DMARC fail | Flatten/includes cleanup | SPF Lookup depth >9 alert |
| Selector retirement too soon | Sudden DKIM fail | Dual-sign and wait | Selector traffic >0% |
FAQ
How long should we plan to move from relaxed to strict alignment?
Most organizations complete the transition in 6–10 weeks: 2–4 weeks of discovery and DKIM enablement, 2–3 weeks of strict DKIM alignment (adkim=s) hardening, 1–3 weeks to align SPF and return-paths, then 1–2 weeks of staged enforcement. DMARCReport’s Policy Planner can compress this by automating discovery and sequencing changes while guarding against premature enforcement.
Does ARC solve all forwarding problems under strict alignment?
No. ARC helps receivers trust upstream authentication even after transformations, but support is uneven and receivers weigh ARC differently. You should still prioritize aligned DKIM and resilient signing, and use DMARCReport’s ARC Trace Analyzer to verify which forwarders actually preserve trust paths.
Should we prioritize SPF or DKIM for strict alignment?
Prioritize DKIM. SPF often breaks on forward; DKIM is more portable if configured correctly. Use SPF mainly for direct-sent infrastructure where you control the bounce domain. DMARCReport’s Alignment Simulator will show the incremental lift from adkim=s vs aspf=s per sender so you can prioritize fixes.
Are RUF forensic reports required to do this safely?
Helpful but not required. Many large providers limit or redact RUF for privacy. RUA aggregates, when normalized and clustered, are sufficient for 90% of remediation. DMARCReport enriches RUA to approximate message classes and sources, reducing the need for RUF dependence.
What if a critical vendor cannot align under strict rules?
Options include isolating that traffic on a subdomain with relaxed alignment temporarily, using p=none with monitoring for that subdomain, or replacing the vendor. DMARCReport flags non-compliant vendors and tracks exemptions with sunset dates to avoid indefinite exceptions.
Conclusion: minimize risk, maximize control—with DMARCReport as your guardrail
Moving to strict DMARC alignment too quickly can trigger immediate bounces, uneven provider enforcement, vendor-related false failures, forwarding-induced breakage, and DNS/key-management outages; the safe path is a phased rollout anchored by precise RUA/RUF analysis, sender-by-sender remediation, and cautious enforcement ramp-up.
DMARCReport makes this journey predictable: it forecasts impact before you change policy, discovers and ranks misaligned senders, audits SPF/DKIM health, analyzes ARC and forwarding behaviors, guides you through a timeline with automated pct ramps and safety checks, and watches live delivery with instant rollback. With DMARCReport as your control plane, strict alignment becomes a confidence-building upgrade—not a deliverability gamble.