What Is Baiting in Cybersecurity? Techniques, Real Examples, and Protection Strategies
Cybercriminals constantly develop new ways to exploit human behavior. While many organizations focus heavily on technical defenses like firewalls, endpoint protection, and encryption, attackers frequently target the weakest link in cybersecurity: people.
One common social engineering tactic used by attackers is baiting. This technique relies on curiosity, temptation, and human psychology to trick victims into compromising their systems or revealing sensitive information. A well-executed baiting attack can allow threat actors to install malware, steal credentials, or gain access to corporate networks without ever needing to exploit a software vulnerability.
At DMARCReport, we regularly analyze cyber threats that originate from email and social engineering. Baiting attacks often intersect with phishing campaigns, malicious downloads, and spoofed messages. Understanding how baiting works is an important step toward strengthening organizational security and preventing data breaches.
In this guide, we explain what baiting in cybersecurity is, how attackers execute these attacks, common examples seen in the real world, and practical strategies organizations can use to defend against them.
What Is Baiting in Cybersecurity?
Baiting is a social engineering attack in which a cybercriminal offers something enticing—such as free software, a reward, or valuable information—to lure victims into performing an action that compromises security.
The attacker places a “bait” that appears attractive or useful to the victim. Once the victim interacts with the bait—by clicking a link, downloading a file, or plugging in a device—the attacker can deploy malware or collect sensitive information.
Unlike other cyberattacks that rely on technical exploits, baiting primarily manipulates human curiosity and desire for rewards. Attackers design the bait to encourage victims to act quickly without verifying its legitimacy.
Historically, baiting scams have existed for centuries, but the digital era has amplified their reach. Today, these attacks frequently appear through email messages, malicious advertisements, fake downloads, or infected storage devices.
For organizations, the consequences can be severe. A single employee interacting with a malicious bait can unintentionally introduce ransomware, spyware, or credential-stealing malware into the corporate network.
Why Baiting Attacks Are So Effective
Baiting works because it targets basic human instincts. People naturally respond to opportunities that promise rewards or valuable information.
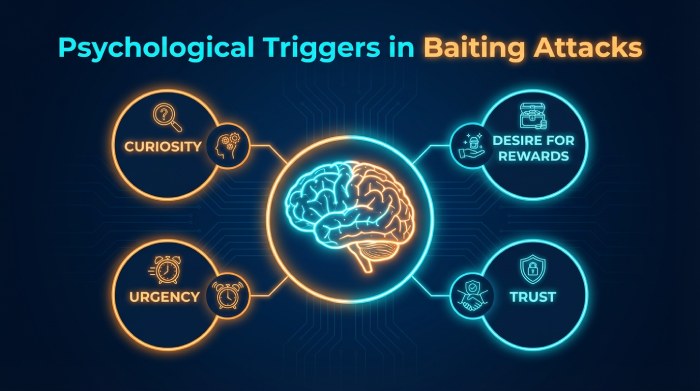
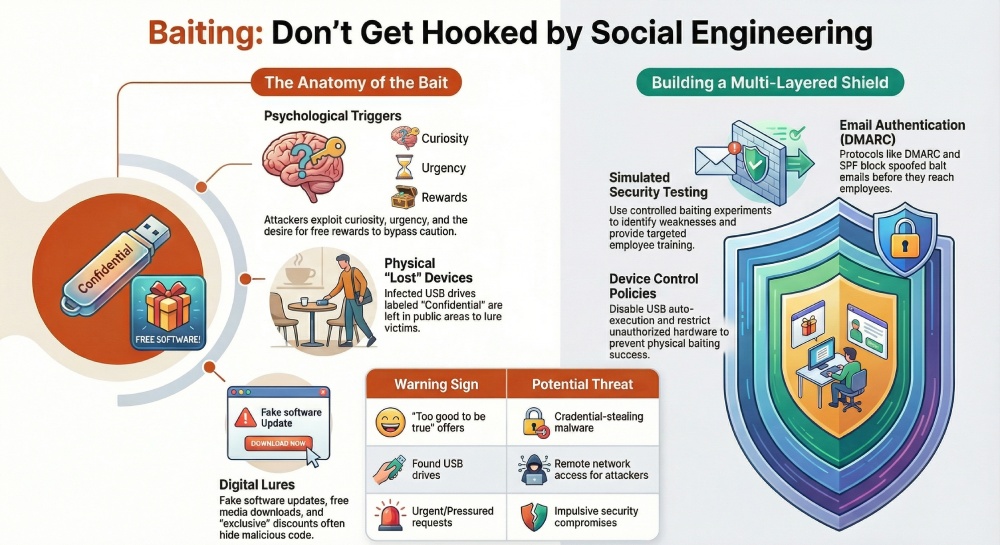
Cybercriminals often exploit psychological triggers such as:
- Curiosity about unknown files or devices
- Desire for free products, discounts, or prizes
- Urgency created by limited-time offers
- Trust in seemingly legitimate messages
These psychological triggers encourage victims to act before they carefully evaluate the situation.
For example, an email promising a free smartphone or a USB drive labeled “Confidential Salary Data” can easily attract attention. If the recipient acts impulsively, they may unknowingly allow malware into their system.
In controlled studies, researchers have demonstrated just how powerful this technique can be. Experiments have shown that a significant percentage of people will plug in USB drives they find in public places, even when they understand cybersecurity risks.
This demonstrates that even well-trained employees can occasionally fall victim to baiting when curiosity overrides caution.

Common Baiting Techniques Used by Cybercriminals
Attackers employ several different methods to deliver bait. While the tactics vary, the underlying strategy remains the same: tempt the victim with something appealing.
1. Malicious Email Offers
One of the most common baiting methods is sending emails that promise rewards or special offers.
Examples include:
- “You’ve won a prize—claim it now!”
- “Download this premium software for free”
- “Exclusive discount available today only”
These emails often contain links that lead to malicious websites or download files infected with malware.
Once the victim clicks the link or downloads the file, the attacker can install spyware, ransomware, or credential-stealing tools.

2. Infected USB Drives and External Devices
Physical baiting is another effective technique used by attackers.
In this scenario, cybercriminals intentionally leave infected USB drives in public areas such as:
- Office parking lots
- Cafeterias
- Company lobbies
- Conference rooms
The device may be labeled with enticing text like:
- “Employee Bonuses 2025”
- “Company Financials”
- “Confidential HR Documents”
When someone plugs the device into a computer, hidden malware automatically executes and infects the system.
This method is particularly dangerous in corporate environments because a single infected machine can allow attackers to spread malware across an entire network.
3. Fake Software or Media Downloads
Another widespread baiting technique involves offering free downloadable content.
Examples include:
- Free movies or music files
- Cracked software applications
- Fake antivirus programs
- Game downloads
These downloads may appear legitimate but actually contain malicious code designed to steal data or monitor user activityFake software updates are also commonly used. A pop-up message might claim that a user’s browser or operating system requires an urgent update. If the victim installs the update, malware is installed instead.
4. Social Media Giveaways and Promotions
Cybercriminals frequently use social media platforms to distribute baiting campaigns.
These scams may appear as:
- Fake giveaways
- Contests promising gift cards
- “Limited time” promotional offers
- Free subscriptions or trial access
Users are usually required to click a link, download an application, or provide personal information to claim the reward.
In many cases, the attacker’s true goal is to collect personal data, which can later be used for identity theft or targeted phishing attacks.
5. Fake Job Opportunities
Job-related baiting attacks have increased significantly in recent years.
Cybercriminals often target job seekers through email or professional networking platforms. These scams may advertise attractive opportunities such as remote work or high-paying freelance projects.
Victims are then asked to:
- Download a job application file
- Install a company communication tool
- Provide personal or financial details
Unfortunately, these downloads often contain malware, and the collected information can be used for identity theft.
Real-World Examples of Baiting Attacks
Understanding real-world examples helps illustrate how baiting attacks operate in practice.
The “Free Software” Trap
A user receives an email offering a premium software license for free. The email includes a link to download the program.
Once installed, the software secretly installs a keylogger that records everything typed on the keyboard—including login credentials and banking information.
The “Lost USB Drive” Attack
An attacker leaves several USB drives in a company parking lot. Curious employees pick them up and plug them into their work computers to see what files are stored on them.
The drives automatically install malware that allows attackers to remotely access the company network.
Fake Delivery Notifications
Another common baiting tactic involves fake shipping notifications.
Victims receive a message claiming they missed a package delivery and must confirm their address. The message contains a link to a website that collects personal details or installs malicious software.
Although these scams may appear harmless at first glance, they can allow attackers to gather information that eventually leads to identity theft or financial fraud.
Warning Signs of a Baiting Attack
Recognizing baiting attempts is one of the most effective ways to prevent them.
Some common warning signs include:
- Offers that seem too good to be true
- Messages from unknown or suspicious senders
- Unexpected attachments or download links
- Urgent requests that pressure users to act quickly
- Unknown devices found in public places
Whenever something appears suspicious, it is best to verify the source before interacting with it.

How Organizations Can Protect Against Baiting Attacks
Preventing baiting attacks requires a combination of technology, training, and security policies.
1. Security Awareness Training
Employees should be trained to recognize social engineering tactics such as baiting, phishing, and pretexting.
Training programs should teach employees how to:
- Identify suspicious emails and links
- Avoid plugging in unknown USB devices
- Report potential threats to IT teams
Regular awareness training significantly reduces the likelihood of successful attacks.
2. Strong Email Authentication
Many baiting campaigns originate through email messages. Implementing strong email authentication protocols can prevent attackers from sending spoofed messages.
Technologies such as:
- SPF (Sender Policy Framework)
- DKIM (DomainKeys Identified Mail)
- DMARC (Domain-based Message Authentication, Reporting, and Conformance)
help verify that emails actually originate from legitimate sources.
At DMARCReport, we emphasize the importance of implementing DMARC policies to prevent attackers from impersonating trusted domains. When properly configured, DMARC blocks fraudulent emails before they reach employee inboxes.
3. Endpoint Security and Antivirus Protection
Modern endpoint protection tools can detect malicious downloads, suspicious files, and unauthorized software installations.
Organizations should ensure that:
- Antivirus software is installed on all devices
- Security tools are updated regularly
- malware detection systems monitor network activity
These protections help stop malicious files before they cause damage.
4. Device Control Policies
Organizations should enforce strict policies regarding external devices.
For example:
- Disable automatic execution of USB drives
- Restrict the use of unknown external storage devices
- Require IT approval before connecting new hardware
These policies significantly reduce the risk of physical baiting attacks.
5. Simulated Security Testing
Companies can test employee awareness by running simulated phishing or baiting campaigns.
For example, security teams might intentionally place USB drives in visible areas or send simulated phishing emails. The results help identify security weaknesses and provide opportunities for additional training.
The Role of Email Security in Preventing Baiting
Many baiting attacks originate through malicious email campaigns. Attackers frequently impersonate legitimate brands or organizations to make their bait appear trustworthy.
Implementing email authentication technologies such as DMARC, SPF, and DKIM can prevent domain spoofing and significantly reduce the success rate of these attacks.
At DMARCReport, our mission is to help organizations strengthen their email security infrastructure and prevent cybercriminals from abusing their domains. By combining email authentication with security awareness training and endpoint protection, organizations can dramatically reduce the risk of social engineering attacks.
Final Thoughts
Baiting remains one of the most deceptive social engineering techniques used in modern cyberattacks. By exploiting curiosity and the promise of rewards, attackers can trick individuals into installing malware or revealing sensitive information.
Whether the bait appears as a free download, a suspicious USB drive, or a fake promotional offer, the goal is always the same: gain unauthorized access to systems and data.
The best defense against baiting is a combination of education, vigilance, and strong security controls. Organizations that invest in employee awareness, implement robust email authentication protocols, and enforce strict device policies are far better equipped to prevent these attacks.
Cybersecurity threats will continue to evolve, but with the right strategies in place, organizations can significantly reduce their exposure to baiting and other social engineering attacks.






