Fake Google Security, Beware Qatar Scams, AI Targets LinkedIn

Last week was all about the big names that got targeted by threat actors. The attacks look a bit more sophisticated. For instance, cybercrooks have been abusing Google Account security pages to gain access to sensitive data, such as passcodes. Qatar Airways suggests that agents use verified platforms. Australia-based LinkedIn accounts are being easily targeted by threat actors with the help of AI. On the other hand, Microsoft is concerned about the phishing campaigns that involve OAuth URL redirection tactics.
Hackers use fake Google Account security pages instead of an app to wipe away passcodes!
The researchers at Malwarebytes have discovered a new phishing campaign that involves phishing emails and a malicious phishing site called google-prism[dot]com. The victims are required to pass a four-step “security” check, which also includes a malicious PWA (Progressive Web Apps).
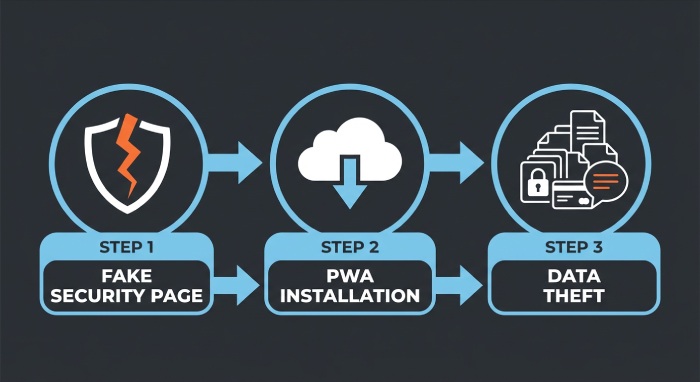
PWAs are a type of websites which need to be installed and run like any other app. But the user is required to operate the website through a browser. After installation, the PWA will seek permission to send notifications and access clipboard data. A service worker would be set up in order to carry out the background tasks, push notifications, and data staging.
Whenever a victim opens the app, the malware starts gathering data (one-time passwords, clipboard content, GPS data, cryptocurrency wallet addresses, fingerprint on the device, and so on). With the help of the PWA, threat actors can conveniently scan internal networks and gain access to local resources.
In extreme cases, hackers would ask the victim to download an app labeled as a “critical security update”. This app further seeks extensive permissions and registers itself as the device administrator. It enables hackers to carry out credential theft, SMS interception, notification monitoring, and so on.
Cyber experts emphasize that implementing DMARC, DKIM, and SPF is essential for strengthening email security and preventing phishing and spoofing attacks.
Qatar Airways warns against scammers amid rising tension!
Cyber scammers have already jumped into action amid regional tensions. So all the major airlines across the GCC have issued warnings against these threat actors. Qatar Airways has also started sending alerts to both customers and agents.

There are multiple fake accounts active currently that are pretending to be official Qatar Airways representatives. So the Doha-based airline has issued a notice for the agents. The notice states: “We are aware of fraudulent accounts impersonating Qatar Airways and requesting personal information.” They have warned against any message that requests OTPs, passwords, banking-related information, or other sensitive data.
Qatar Airways has recommended that both agents and the public to use only official platforms, such as the Qatar Airways app or qatarairways.com.
The National Cybersecurity Authority of Saudi Arabia has also issued similar warnings against fake travel agencies and airlines. Emirates and Etihad Airways have requested passengers and agents to check details only on their official websites and apps. Also, experts have urged the public to strictly avoid any message that claims too-good-to-be-true offers, such as premium upgrades, lucrative vouchers, or complete refunds.
Not only the aviation industry, but even the finance sector is also going through a critical situation. Wio, the digital bank of the UAE, has warned its customers against impersonation attempts. The scammers have been posing as government authorities and persuading people to share sensitive details such as their Emirates ID and relevant personal data.
Concerned authorities and Dubai police have been working together to nab the culprits.

Australia-based LinkedIn profiles targeted by scammers using AI!
Almost half of the Australian population is active on LinkedIn, the professional networking and job-hunting platform. However, scammers have started using LinkedIn as a goldmine for data. With the help of easily accessible and affordable AI tools, scammers are able to scale their attacks.
With AI, activities like early-stage profiling, evaluating posts, and mapping leadership teams can be automated easily.
The researchers atTrendAI believe that AI has introduced a massive shift from manual data collection and evaluation to automated, scalable workflows. Metadata, LinkedIn posts, and images can be converted into machine-readable inputs within a few minutes.
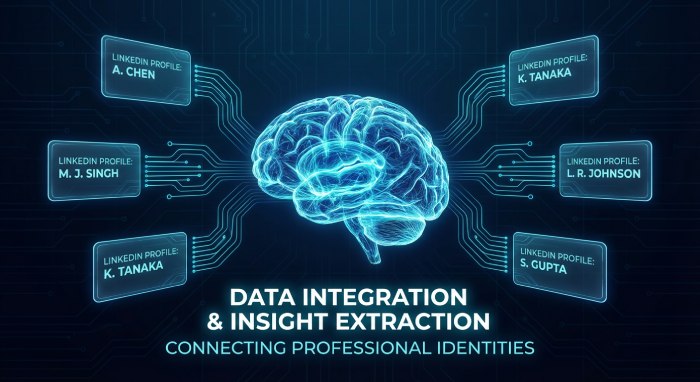
Cyber experts see this shift as a major change in the ecosystem of targeting where cyberscammers rely less on high-end skills and proficiency, and focus more on volume and scale.
The threat actors prefer to monitor employees’ digital footprints to gain context across different organizations. They keep a tab on work topics, event attendance, leadership structures, etc.
Cybersecurity experts urge organizations to think bigger and expand the scope of training to include tactical strategies, in order to prevent cyber mishaps through LinkedIn.
Microsoft issues a warning against OAuth Redirect Abuse!
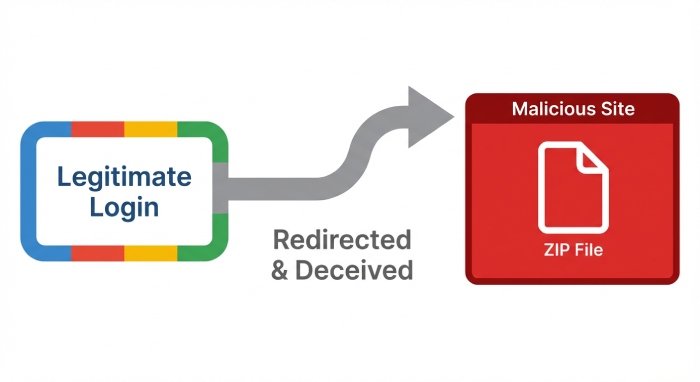
Threat actors have been using OAuth URL redirection strategies and phishing emails to evade traditional anti-phishing defenses deployed across browsers and emails. Microsoft believes that scammers are using this phishing tactic against public as well as private sector entities. The ultimate goal is to redirect the victims to a malicious infrastructure. Microsoft has stated that these phishing attacks operate as identity-based threats by leveraging OAuth.
The threat actors have been abusing OAuth login flows from renowned identity providers like Google Workspace and Microsoft Entra ID. Generally, there’s a feature in OAuth that enables users to log in through Google accounts or even their existing work accounts. The threat actors abuse the same feature to come up with malicious links that otherwise appear to be legitimate.
When the victim is redirected to a malicious website, they are asked to download a ZIP archive file. Downloading the same enables the threat actors to carry out hands-on keyboard attacks. Since these kinds of attacks use Google or Microsoft domains, conventional security filters may not be able to flag them.
Microsoft has been conducting a full-fledged investigation. In the process, different OAuth applications have beenneutralized by Microsoft. Experts have urged organizations to minimize user content, remove any overprivileged or unused apps, and also review application permissions from time to time. Users should be wary of unexpected authentication prompts and think twice before downloading any file, followed by login attempts.







