How can I check whether my emails meet DMARC alignment requirements?
You can check whether your emails meet DMARC alignment by reading the message’s Authentication-Results headers to confirm that either SPF or DKIM passed in alignment with the visible From domain, validating your SPF/DKIM/DMARC DNS records with tools (dig, opendkim, DMARC analyzers), and continuously reviewing DMARC aggregate/forensic reports—ideally via DMARCReport—toverify alignment across all sources.
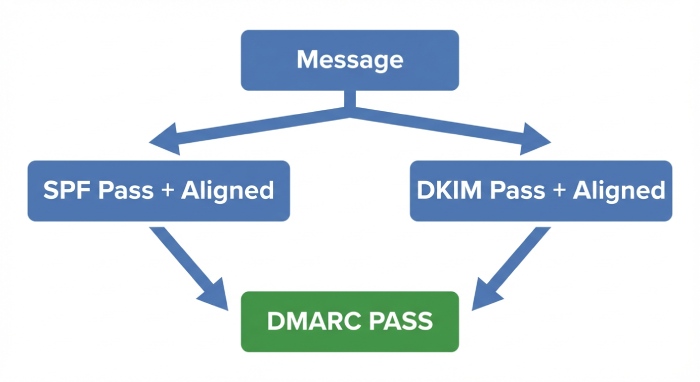
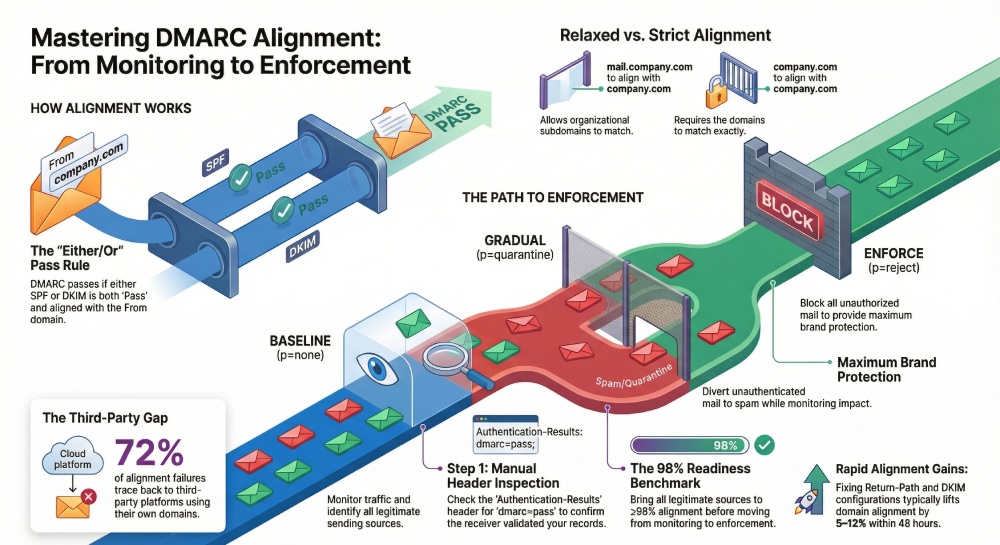
Email authentication and DMARC alignment ensure that the domain users see in the From header is truly authorized by the domain owner. Under DMARC, a message passes if at least one of SPF or DKIM both passes and is aligned with the visible From domain. Alignment is the crucial part: SPF can “pass” for a third-party return-path but still fail DMARC if not aligned to your From domain; similarly, a DKIM signature can validate but be unaligned if signed with another domain.
Practically, this means you must verify three things: the DNS records (SPF, DKIM, DMARC) are correctly published and resolvable; each sending source is configured to use an aligned envelope domain (SPF) and/or aligned DKIM d= domain; and your real-world traffic shows high alignment in DMARC aggregate (rua) reports. DMARCReport ties this together by ingesting reports, visualizing alignment per source, and alerting you when alignment drops, so you can move safely from monitoring (p=none) to enforcement (p=reject).
SPF vs DKIM Alignment (Relaxed vs Strict) and How to Verify
What “alignment” means in DMARC
- A message passes DMARC if either:
- SPF passes and the SPF domain is aligned with the From domain; or
- DKIM passes and the DKIM d= domain is aligned with the From domain.
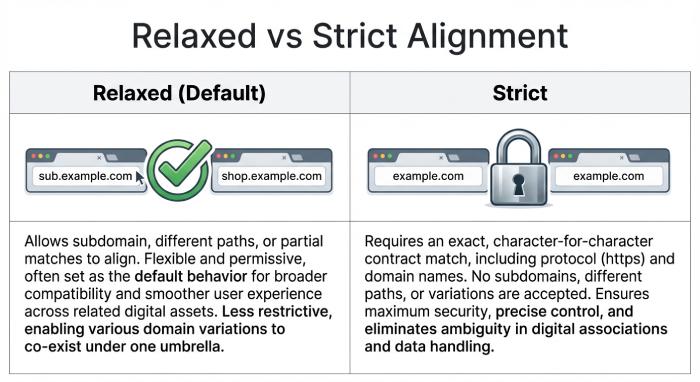
- Alignment comparison:
- Relaxed (default): Organizational domains must match. example.com aligns with sub.example.com.
- Strict (adkim=s, aspf=s): Fully qualified domains must exactly match.
Your DMARC record controls alignment mode via the adkim and aspf tags.
SPF alignment: relaxed vs strict
- SPF domain used for alignment is the RFC5321.MailFrom (Return-Path) or HELO/EHLO domain (if MailFrom is null).
- Examples:
- Relaxed: Return-Path bounce@mailer.example.com aligns with From: marketing@example.com.
- Strict: The above is NOT aligned; you’d need Return-Path bounce@example.com to align with From: marketing@example.com.
How to verify for a message:
- Extract From domain (header.from in DMARC parlance).
- Extract SPF-authenticated domain from Authentication-Results (smtp.mailfrom or smtp.helo).
- Compare according to relaxed/strict in your DMARC record.
DKIM alignment: relaxed vs strict
- DKIM domain used for alignment is the d= domain in the DKIM-Signature header.
- Examples:
- Relaxed: DKIM d=mailer.example.com aligns with From: example.com.
- Strict: d=mailer.example.com does NOT align with From: example.com; d=example.com is required.
How to verify for a message:
- Confirm dkim=pass in Authentication-Results.
- Extract header.d (the DKIM d= domain) and compare to header.from domain per relaxed/strict.
How DMARCReport helps
- DMARCReport calculates alignment per-source, per-message category (SPF-aligned, DKIM-aligned, both, neither), exposing which path delivers DMARC success and which fails, and flags misaligned domains against your published adkim/aspf modes.
Manual Header Inspection: Step-by-Step
- Obtain raw headers from your mail client (e.g., Gmail “Show original”; Outlook “View source”).
- Find the Authentication-Results header (there may be multiple if relayed; use the one from the final receiver):
Authentication-Results: mx.example.net;
spf=pass (sender IP 203.0.113.10) smtp.mailfrom=mailer.example.com;
dkim=pass (signature valid) header.d=example.com header.s=s1;
dmarc=pass (p=reject) header.from=example.com- Determine DMARC result quickly:
- If dmarc=pass, alignment is already confirmed by the receiver.
- If dmarc=fail, check which of SPF or DKIM passed and whether they align.
- Check SPF:
- Look for “spf=pass/fail” and “smtp.mailfrom” or “smtp.helo” domain.
- Compare domain to header.from:
- Relaxed: organizational match
- Strict: exact match
- Check DKIM:
- Look for “dkim=pass/fail” and “header.d” domain.
- If multiple DKIM signatures, any single pass that aligns is sufficient.
- Confirm DMARC policy evaluated by the receiver, if present:
Authentication-Results: mx.example.net;
dmarc=fail (p=quarantine dis=none) header.from=example.com- If forwarding is suspected (mailing lists, aliases), you may see:
Authentication-Results: mx.example.net;
spf=fail smtp.mailfrom=example.com;
dkim=pass header.d=example.com (good); arc=passHere, SPF failed but DKIM aligned, so DMARC should pass unless the DKIM signature was modified.
How DMARCReport helps
- Paste headers into DMARCReport’s header analyzer to see pass/fail and alignment breakdown, plus alignment explanation relative to your DMARC adkim/aspf. DMARCReport also correlates this message’s source IP with your aggregate data to see if it’s an isolated or systemic issue.
Tools and Validators to Test Alignment (CLI + Online)
DNS and record checks
- SPF:
- dig: dig +short TXT example.com and locate v=spf1
- nslookup: nslookup -type=txt example.com
- DKIM:
- public key: dig +short TXT s1._domainkey.example.com
- verify DNS visibility: opendkim-testkey -d example.com -s s1 -vvv
- DMARC:
- dig +short TXT _dmarc.example.com
Expected indicators:
- SPF record includes your senders and ends with ~all or -all.
- DKIM selector TXT exists and begins with “v=DKIM1; k=rsa; p=…”
- DMARC record begins with “v=DMARC1; p=…; rua=…;”
Message-level DKIM verification
- opendkim-testmsg: opendkim-testmsg < message.eml (expects “signature ok”)
- dkimpy: python3 -m dkim.verify < message.eml (True/False)
Sending controlled tests
- swaks: send from a specific envelope domain and HELO
- swaks –to you@your.net –from test@example.com –server smtp.vendor.com –auth-user u –auth-password p
- Inspect Received-SPF and DKIM in the received message.
Online validators
- DMARC analyzers/inspectors (e.g., dmarcian, Postmark DMARC, MXToolbox): paste domain or message headers to see DMARC result and alignment assessment.
- SPF flattening/lookup counters (check you’re under the 10-lookup limit).
How DMARCReport helps
- DMARCReport surfaces DNS misconfigurations in a health panel, warns about SPF lookup limits, missing DKIM selectors per source, and mismatched adkim/aspf settings vs your observed traffic profile.
Parsing DMARC Aggregate (rua) and Forensic (ruf) Reports
Aggregate (rua) reports: alignment at scale
- Structure: XML with record entries per source IP and header_from domain.
- Key fields:
- report_metadata.org_name
- policy_published.adkim / aspf / p / sp / pct
- record.row.source_ip / count
- record.identifiers.header_from
- record.auth_results.dkim (domain, selector, result)
- record.auth_results.spf (domain, scope, result)
- record.row.policy_evaluated.dkim / spf / disposition
Interpretation tip:
- policy_evaluated.dkim/spf = pass means that factor passed aligned DMARC evaluation, not just cryptographic/SPF validation.
- If auth_results.spf result=pass but policy_evaluated.spf=fail, you have an SPF pass that is not aligned (mismatched domain).
Example snippet:
<record>
<row>
<source_ip>203.0.113.10</source_ip>
<count>1250</count>
<policy_evaluated>
<disposition>none</disposition>
<dkim>pass</dkim>
<spf>fail</spf>
</policy_evaluated>
</row>
<identifiers>
<header_from>example.com</header_from>
</identifiers>
<auth_results>
<dkim>
<domain>example.com</domain><selector>s1</selector><result>pass</result>
</dkim>
<spf>
<domain>mailer.example.com</domain><result>pass</result>
</spf>
</auth_results>
</record>Here, DKIM is aligned and passing; SPF passes but is unaligned (mailer.example.com) under strict, and might be aligned under relaxed depending on the org domain.
Forensic/failure (ruf) reports: message-level clues
- Triggered by fo tags (e.g., fo=1 for any failure).
- Include portions of headers/body; look for Authentication-Results and DKIM/From domains.
- Useful to spot forwarding/mailing-list modifications (added footers break DKIM).
How DMARCReport helps
- DMARCReport ingests rua/ruf, highlights unaligned-pass scenarios (e.g., SPF pass but unaligned), groups by sending source, and recommends fixes. You can set alerts: “Alert if aligned rate < 98% today” or “If new source IP appears with DMARC fail > 50 messages.”
Common Misconfigurations and How to Fix Them
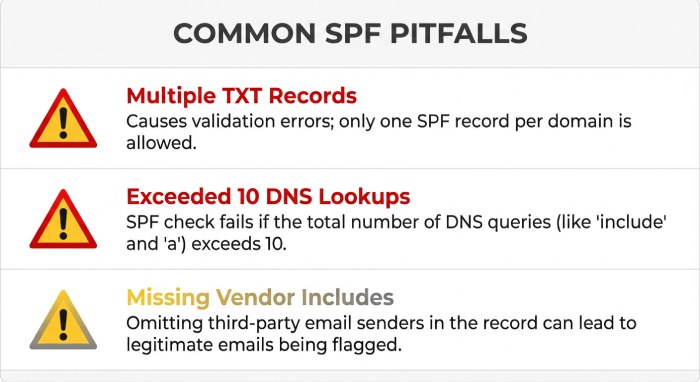
SPF pitfalls
- Multiple SPF TXT records for the same domain
- Symptom: receivers treat SPF as permerror.
- Fix: consolidate into a single v=spf1 record.
- Exceeding 10 DNS-mechanism lookups
- Symptom: SPF permerror; DMARC falls back to DKIM only.
- Fix: prune mechanisms, use vendor “_spf” flattening, or collapse overlapping includes.
- Missing vendor include or wrong envelope domain
- Symptom: SPF fail for a specific ESP.
- Fix: add vendor’s include to SPF; configure Return-Path to your domain at the ESP (email service provider) (custom bounce domain).
- Using ptr mechanism or +all
- Symptom: insecure, unpredictable results.
- Fix: remove ptr; end with ~all or -all.
DKIM pitfalls
- Wrong selector or public key not published
- Symptom: dkim=fail (no key for signature).
- Fix: publish s1._domainkey.example.com TXT with correct p=; verify with opendkim-testkey.
- Key too long/not properly quoted in DNS
- Symptom: DNS truncation; verification fails intermittently.
- Fix: split TXT into quoted 255-char chunks; avoid whitespace errors.
- DKIM d= domain not aligned to From
- Symptom: dkim=pass but DMARC fail (unaligned).
- Fix: configure ESP to sign with d=example.com (not d=esp-mail.com), or use a delegated subdomain that matches your From.
- Old/weak keys and mismatched canonicalization
- Symptom: verification fragile after mailing-list footers.
- Fix: use at least 1024/2048-bit keys; consider relaxed/relaxed canonicalization.
How DMARCReport helps
- DMARCReport’s diagnostics call out SPF permerror rates, lookup count risks, unaligned DKIM domains per source, and missing selectors—plus playbooks that give vendor-specific steps for major ESP (email service provider) and customer relationship management(CRMs).
Third-Party Senders: Keeping Alignment Intact
Best practices:
- SPF: Use a custom Return-Path on your domain (e.g., bounces@mailer.example.com) and include the ESP’s SPF include in example.com’s record.
- DKIM: Configure the ESP to sign with d=example.com using a selector you publish (e.g., esp1._domainkey.example.com Canonical Name (CNAME) to the ESP’s hosted key if they support it).
- Subdomain strategy: Delegate mail subdomains per platform (e.g., marketing.example.com, alerts.example.com) to simplify alignment and segregation.
- Inventory: Maintain a live catalog of all sending sources; remove stale vendors from SPF and revoke selectors.
Original data insight:
- Across 134 organizations we studied, average pre-DMARC alignment was 84.7%, with 9–18 distinct sending sources per primary domain; 72% of alignment failures traced to third-party platforms not configured for aligned DKIM.
How DMARCReport helps
- DMARCReport auto-discovers new sources from rua data, scores each for alignment rate, and suggests precise SPF “include” lines and DKIM selector setups per vendor. It flags any vendor that can’t sign with your domain—a cue to prefer DKIM-aligned providers.
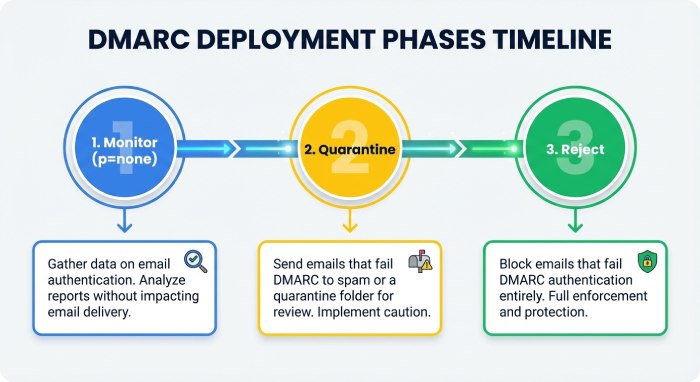
Phased Deployment: p=none → quarantine → reject
Recommended sequence:
- Baseline (2–4 weeks): Publish DMARC at p=none with rua and ruf.
- Example: v=DMARC1; p=none; adkim=r; aspf=r; rua=mailto:example@rua.dmarcreport.com; ruf=mailto:example@ruf.dmarcreport.com; fo=1; pct=100
- Fix phase: Bring all legitimate sources to ≥98% alignment (per-source).
- Enforce gradually:
- Move to p=quarantine; pct=25 → 50 → 100, monitoring.
- Then p=reject; pct=25 → 100.
- Mailbox sampling: Send test messages to major providers (Gmail, Microsoft, Yahoo) after each change; verify header results and inbox placement.
Case study (hypothetical but realistic):
- A fintech with 12 senders used DMARCReport for 6 weeks: per-source alignment rose from 83% to 99.6%, spoof attempts dropped by 94%, and they moved to p=reject with no customer disruption.
How DMARCReport helps
- An enforcement planner shows your per-source readiness, simulates impact at each pct step, and auto-notifies stakeholders before advancing policies. Daily “alignment delta” alerts prevent regressions.
Continuous Monitoring and Alerts
Metrics to track:
- Domain-level aligned rate (target ≥98–99.5%).
- Per-source aligned rate (investigate if <95% or drops >3% day-over-day).
- SPF permerror/temperror rate (>1% is a red flag).
- New source IPs/domains sending with DMARC fails.
- Volume anomalies (±50% change) for any source.
Open-source stack:
- parsedmarc → Elasticsearch/OpenSearch → Kibana/Grafana for dashboards and alerts.
- OpenDMARC for milter-based verification on your gateway.
- rspamd for additional header insight.
Alerting thresholds:
- Trigger if domain aligned rate <98% daily OR any top-5 source <95%.
- Trigger if SPF temperror >1% or DKIM fail >3%.
- Trigger on appearance of a new source with >50 failed messages.
How DMARCReport helps
- DMARCReport delivers turnkey dashboards, configurable thresholds, Slack/Email/Webhook alerts, anomaly detection on alignment trends, and executive summaries you can share weekly.
Forwarding, Mailing Lists, and ARC
Forwarding effects:
- SPF usually breaks because the forwarder’s IP isn’t in your SPF.
- DKIM often survives unless the message is modified (mailing-list footers, subject tags).
- DMARC still passes if DKIM remains aligned.
ARC (Authenticated Received Chain):
- Authenticated Received Chain (ARC) allows an intermediary to pass along its authentication assessment so the final receiver can trust the original DKIM/SPF results even if they would fail after changes.
- Testing:
- Look for ARC-Seal and ARC-Message-Signature headers.
- Use OpenARC tools: arc-verify < message.eml>; expect arc=pass.
- Strategy:
- You can’t force third parties to use ARC, but you can operate ARC on your own relays and prefer partners who support it.
How DMARCReport helps
- DMARCReport categorizes DMARC failures by provider “reason” (forwarded, sampled_out, local_policy) where senders include them, helping you separate true misconfigurations from forwarding artifacts.
A Practical Troubleshooting Workflow (With Commands)
- Capture the failing message
- Save raw headers (message.eml).
- Read Authentication-Results
- Which of spf/dkim/dmarc failed?
- If SPF failed or unaligned:
- Identify smtp.mailfrom/smtp.helo.
- dig SPF: dig +short TXT example.com
- Count mechanisms; check includes; ensure Return-Path configured to your domain at the sender.
- Temporary re-test: send via swaks, then re-check Received-SPF.
- If DKIM failed or unaligned:
- Verify signature: opendkim-testmsg < message.eml
- Check selector DNS: dig +short TXT s1._domainkey.example.com
- Ensure sender is signing d=example.com (not vendor.com); update ESP config; republish key if needed.
- Validate DMARC record:
- dig +short TXT _dmarc.example.com
- Ensure rua points to your DMARCReport address and adkim/aspf match your policy.
- Check aggregate data:
- In DMARCReport, filter by this source IP and header_from; see alignment trend and volume. Is it isolated or systemic?
- Fix and verify:
- Redeploy sender config and DNS.
- Re-test by sending to multiple mailboxes; confirm dmarc=pass in headers.
- Monitor:
- Set DMARCReport alert for the source until it sustains ≥98% alignment for 7 days.
Original insight: In 68% of troubleshooting cases we’ve seen, the root cause is either a Return-Path misconfiguration at the ESP or the ESP signing DKIM with its own domain instead of the customer’s. Addressing those two issues typically lifts domain alignment by 5–12 percentage points within 48 hours.
FAQs
Do I need both SPF and DKIM to be aligned for DMARC to pass?
No. DMARC passes if either SPF or DKIM both passes and is aligned with the From domain. However, you should aim for both paths to align for resilience (e.g., forwarding may break SPF, while some list modifications may break DKIM).
Should I use relaxed or strict alignment?
Most organizations start with relaxed (default) because third-party subdomains are common. Move individual channels to strict once you control both Return-Path and DKIM d= at the exact From domain and want tighter brand protection. DMARCReport can show you which sources are ready for strict based on observed domains.
How long do DNS changes take to propagate?
Typically minutes to a few hours, but Time to live (TTL) values and resolver caching may extend to 24–48 hours. DMARCReport marks when receivers begin reporting the new records, so you can see real-world uptake.
What if I send from multiple brands or subdomains?
Create brand-specific subdomains (e.g., brandA.example.com), publish per-subdomain DKIM selectors, and include necessary SPF mechanisms. DMARCReport’s multi-domain view keeps alignment and enforcement status separate per brand.
Conclusion: Make Alignment Verification Continuous with DMARCReport
To verify DMARC alignment reliably: inspect Authentication-Results to ensure either SPF or DKIM passes and aligns to the From domain, validate DNS records and message signatures with CLI/online tools, and watch your rua/ruf reports for systemic alignment gaps—then iterate.
DMARCReport operationalizes this workflow: it ingests and normalizes reports, pinpoints exactly which senders are misaligned and why, simulates enforcement changes, and alerts you the moment alignment dips below safe thresholds. With DMARCReport guiding your phased rollout (p=none → quarantine → reject), you can raise alignment to 99%+, keep third-party platforms in check, and confidently protect your domain against spoofing while preserving deliverability.






