Understanding URL Manipulation & URL Rewriting – A DMARCReport Guide
In today’s digital world, almost everything we access online has a web address — a URL (Uniform Resource Locator). These seemingly ordinary strings of text are the doorways to websites, files, apps, cloud dashboards, support pages, videos, and more. But what many people don’t realize is that those URLs can be manipulated — sometimes for good reasons, and sometimes for dangerous ones.
At DMARCReport, we believe a solid understanding of how URLs work and how they can be misused is essential for anyone concerned about cybersecurity — from website owners and developers to security teams and everyday users clicking links in their email. In this comprehensive guide, we’ll break down URL manipulation and URL rewriting — what they are, how they work, why they matter, and how attackers exploit them.
In addition, implementing SPF, DKIM, and DMARC strengthens email authentication and helps prevent attackers from delivering malicious rewritten URLs through spoofed emails.
1. What Is a URL (and Why It Matters)?
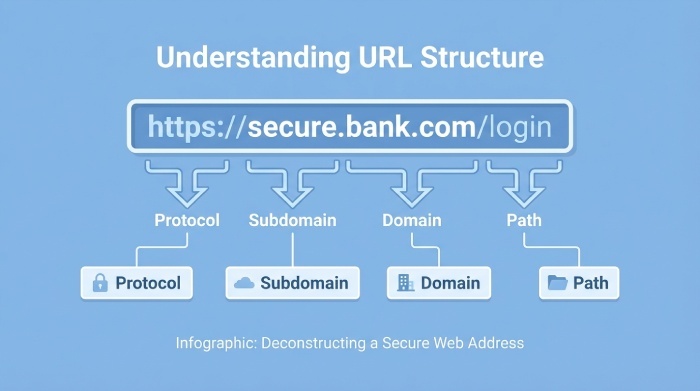
Before diving into URL manipulation, let’s take a moment to define what a URL is.
A URL (Uniform Resource Locator) is the unique address that identifies a resource on the internet. When youenter a web address into your browser, that URL tells the browser exactly where to go and what to retrieve — like a GPS coordinate for online content.
Here’s a typical example:
Let’s break that down:
- Protocol (https://) — Defines how data is transferred (secure HTTP in this case).
- Domain (www.example.com) — Points to the specific server hosting the content.
- Port (443) — Specifies the network port used (443 is default for HTTPS).
- Path (/path/to/resource) — Directs to a specific page or file.
- Query (?query=123) — Optional parameters for dynamic content.
- Fragment (#section) — A link to a section within a page.
Each of these components plays a role in how browsers, servers, and users interact with online content.
2. What Is URL Rewriting?
URL rewriting is the process of modifying a URL’s appearance or structure — either for legitimate purposes (like SEO and cleaner URLs), or malicious ones (like hiding the true destination). Though often grouped with URL manipulation, rewriting has both constructive and destructive uses.
Positive Uses of URL Rewriting
Website developers and administrators use URL rewriting to:
- Create user-friendly URLs that are easy to remember and read.
- Improve SEO (Search Engine Optimization) so pages rank better in search results.
- Hide internal query strings that aren’t meaningful to users.
- Mask dynamically generated URLs that might otherwise look messy or confusing.
For example, instead of a complex URL like:
With URL rewriting, that could become:
This cleaner format can boost user trust and SEO value.
Large companies like Amazon have used URL rewriting strategies to generate relevant, readable URLs at scale — helping improve both user experience and search visibility.
3. When URL Rewriting Becomes Dangerous
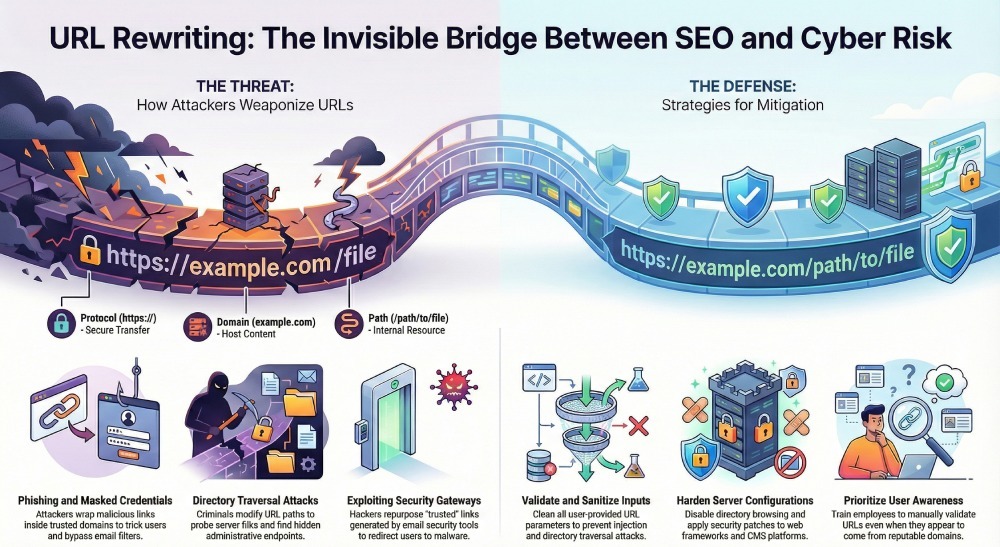
URL rewriting isn’t always benign. Because rewriting changes how URLs appear — and sometimes how they behave — attackers can use it as part of their malicious toolkits.
Here are some ways that URL manipulation can pose threats:
a. Directory Traversal and Sensitive Access
Cybercriminals may repeatedly modify URL paths to explore directories and file systems on a server. If they find sensitive files, hidden scripts, or administrative endpoints, they can exploit them to gain unauthorized access or take over parts of a website.

b. Phishing and Masked Credentials
Attackers have increasingly leveraged URL rewriting to wrap malicious links with seemingly trusted domains — especially in phishing emails. This technique often bypasses security filters and tricks users into clicking links that look legitimate but redirect to credential-stealing or malware-laden sites.
For example, rewriting might transform what appears to be a secure link like:
into:
Users and even email filters may trust the rewritten version — letting the malicious destination slip through.
c. Exploiting Email Security Tools
Some email security gateways automatically rewrite all URLs in incoming messages for scanning. However, attackers have learned to exploit this behavior by sending benign links through the system, then reusing the rewritten URL — once trusted — to point to malicious content.
This escalation in phishing sophistication shows just how nuanced URL manipulation threats can be.
4. URL Manipulation vs. URL Redirection
At this point, it’s worth noting a related concept: URL redirection.
While URL manipulation and rewriting refer to changing URLs for various purposes, URL redirection specifically means sending users from one URL to another. This is commonly used for:
- Redirecting old URLs to new ones after a site redesign.
- Shortening links while pointing to full destinations.
- Managing internal links for navigation.
However, redirection — like rewriting — can be abused if an attacker redirects a user from a legitimate link to a harmful site.
5. How Attackers Exploit Rewriting in Phishing
Recent cybersecurity research shows that threat actors are increasingly abusing URL rewriting mechanisms to launch phishing campaigns that evade detection.
Here’s how this typically works:
- Compromise a Legitimate Email Account: Attackers send an email from a legitimate source containing a malicious link.
- Automatic URL Rewrite: The organization’s email security system rewrites the link to route through a trusted domain for scanning.
Weaponization: After rewriting, the attacker modifies the link’s destination so it now redirects to a phishing site. - User Trust: Because the URL appears to come from a reputable domain, users are more likely to click — and credentials or sensitive data can be stolen.
This exploitation highlights how URL rewriting, when improperly understood or managed, can actually work against security goals.

6. Mitigating URL Manipulation Risks
So — what can organizations do to protect themselves from harmful URL manipulation and rewriting attacks?
Here are several key strategies:
1. Monitor and Filter Inputs
If your website accepts user input in URLs (such as resource identifiers or parameters), make sure to validate and sanitize them properly before processing. This helps prevent directory traversal and injection attacks.
2. Disable Directory Browsing
Server settings that allow browsing of directory structures make it easier for attackers to guess paths and find vulnerabilities. Turning this off limits exposure to hidden files.
3. Apply Security Patches
Keep web servers, frameworks, and CMS platforms up to date. Patches often fix vulnerabilities that attackers could exploit via manipulated URLs.

4. Use HTTPS Everywhere
HTTPS encrypts data in transit, so attackers can’t easily intercept or tamper with URL parameters or session data. This is foundational forsecure web architecture.
5. Harden Email Security
Be cautious with automatic URL rewriting tools. Make sure your security solution rescans URLs periodically and doesn’t rely solely on a potentially compromised rewrite result.
6. Educate Users
User awareness is one of the most powerful defenses. Teach employees how to recognize suspicious links — even if they look “safe” — and to validate URLs before clicking.
7. The Bottom Line
URL manipulation and rewriting are powerful techniques — and like most powerful tools, their value depends on how they’re used.
On the positive side, rewriting helps streamline URLs, improve SEO, and deliver a better user experience. Properly managed, it supports strong web architecture and navigation.
But on the negative side, attackers can exploit URL manipulation to bypass security, mask malicious links, escalate phishing attacks, and gain unauthorized access. This puts everyone at risk — from enterprise systems to individual users.
Understanding both sides of the equation is essential. By implementing best practices, constantly monitoring for anomalies, and educating users, organizations can enjoy the benefits of URL rewriting while minimizing risks.







