Uniswap Scam Ads, Meta Ads Malicious, ATM Jackpotting Surge
This is the 4th edition of the month, and here are the top 4 cyber mishaps from last week that you must know about. Uniswap Founder has raised concerns around spiked instances of phishing scams. Meanwhile, threat actors have started abusing Meta ads to carry out cyberattacks. Experts witnessed a steep spike in instances of ATM jackpotting in 2025. Besides, job seekers are being targeted by phishing actors by using fake Google Forms.
Uniswap is being targeted in scam ads!
Hayden Adams, the founder of Uniswap, is concerned about the spike in fake ads that impersonate a decentralized exchange. A crypto investor named Ika apparently fell prey to a phishing incident. Adams believes that currently, there has been a surge in crypto scam ads. Users who search for “Uniswap” keywords are being targeted by the cybercrooks.

Threat actors buy sponsored search results across major search engines based on “Uniswap” keywords. Then these paid advertisements are used to make the fake websites appear high up in search engine results.
These malicious websites look almost similar to the official Uniswap interface, making them look more credible. The moment a user connects their wallets and then goes ahead with transactions, threat actors can easily run away with the money.
A recent cyber mishap took an ugly turn when Ika lost his entire crypto portfolio after interacting with a malicious webpage that appeared to be Uniswap.
There has been an upsurge in crypto-related scams in the last couple of months. Scammers managed to wipe away funds worth $370 million in January 2026.
As cyber threats surge worldwide, businesses are increasingly adopting DMARC, DKIM, and SPF authentication protocols to strengthen email security and prevent phishing, spoofing, and domain impersonation attacks.

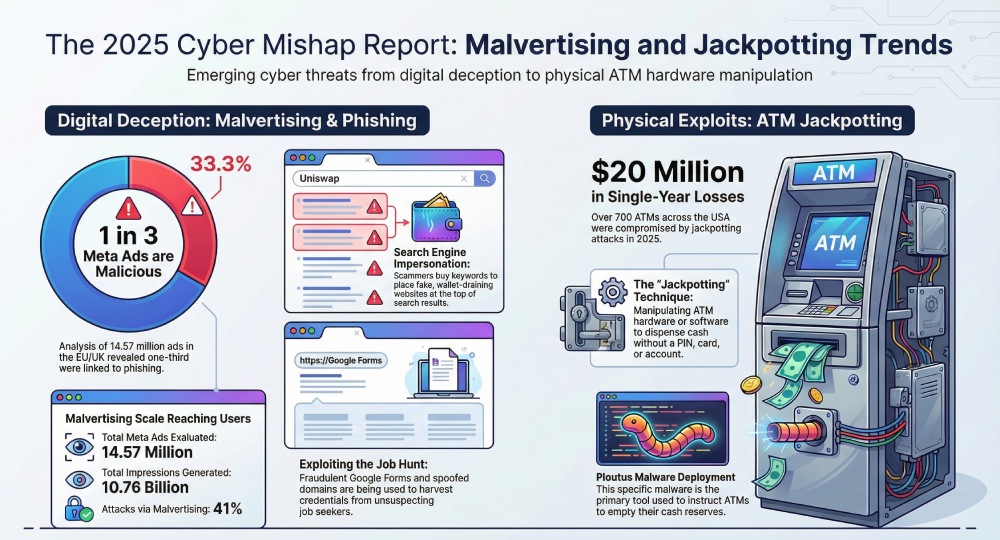
Apparently, one out of three Meta ads is malicious!
Running Meta ads to boost sales is a common practice nowadays. But even Meta ads are not safe- thanks to cybercriminals. Threat actors have started targeting Meta ads with malware to carry out scams.
Researchers evaluated a whopping 14.57 million Meta ads across the EU and the UK. These ads generated over 10.76 billion impressions. What’s concerning is that one-third of these ads were connected to phishing campaigns.

One of the major reasons why Meta ad scams are successful because they do not look suspicious. This is exactly why a massive 41% cyberattacks take place in the form of malvertising.
ATM jackpotting cases spiked in 2025!
Financial institutions invest time, money, and the latest technology to bolster their databases, apps, and fraud-detection mechanisms. But threat actors are smart enough to find out that one thing which banks have majorly overlooked- the ATMs.
Last year, threat actors managed to break into the systems of over 700 ATMs across the USA. experts call these attacks “jackpotting.” The US ATMs suffered a massive financial loss worth $20 million in a single year.
The FBI and the US Department of Justice have been working together to nab the culprits. They have already charged six Venezuelan nationals with plotting to deploy malware across ATMs.

Concerned authorities have nabbed around 93 individuals. Among the nabbed miscreants, the Tren de Aragua group is also there. This group has already been designated as a Foreign Terrorist Organization.
The jackpotting technique involves a cybercrook who manages to gain access to the internal electronics of the ATM machines. Next, they manipulate the hardware or software of the machines to dispense cash without requiring a PIN, bank account, or even an ATM card.
The most popular tactic used by these threat actors is to deploy malware named Ploutus to instruct the ATMs to empty all the cash.
Diebold Nixdorf, an expert in the ATM ecosystem, has recommended that banks and ATM operators to provide minimal physical access to ATMs. Using robust encryption systems, setting up alarms, and upgrading systems from time to time to prevent jackpotting incidents can also help avoid major jackpotting incidents.
Filling in that Google form during job hunting might land you in trouble!

A job-themed phishing campaign is doing the rounds, targeting unsuspecting job seekers. Threat actors have been leveraging fake Google Forms to collect victims’ login credentials. To carry out this phishing campaign, the cyberattackers are using spoofed domains and forms.google.ss-o.com.
What appears to be a legitimate Customer Support Executive job description is, in fact, a fraudulent page that urges job applicants to enter sensitive data. Once the victims enter their personal details and click the Sign In button, they are redirected to a malicious domain.
Researchers believe that the cybercrooks have been using a special script, generation_form.php, to bypass conventional security mechanisms.
Cybersecurity experts have urged job seekers to stay vigilant and avoid filling in any and every random Google form. They must verify job opportunities from credible channels and also practice cyber hygiene.