What Is Angler Phishing And How Can You Avoid It?
Social media has become one of the most important communication channels between businesses and their customers. Companies use platforms like Twitter, Facebook, and Instagram to provide support, respond to complaints, and engage with their audiences. However, cybercriminals have found ways to exploit this trust through a growing scam known as angler phishing.
Angler phishing is a deceptive technique where attackers impersonate legitimate customer support accounts on social media in order to trick users into revealing sensitive information. These attacks often target frustrated customers who publicly complain about a company’s service and are expecting help. The attacker steps in pretending to assist, but their real goal is to steal credentials, financial data, or other valuable information.
Because social media interactions feel informal and immediate, many users lower their guard. This makes angler phishing particularly effective. In this guide, DMARCReport explains how angler phishing works, why attackers use it, and what individuals and organizations can do to prevent it.
Understanding Angler Phishing
Angler phishing is a form of social engineering attack that occurs primarily on social media platforms. In this type of scam, cybercriminals create fake customer support accounts that closely resemble official company profiles. They then monitor social media for users complaining about a service or asking for help.
When a customer posts a complaint, the attacker quickly responds, pretending to be a support representative ready to solve the issue. Because the victim expects assistance, the message appears legitimate. The attacker then guides the user toward a malicious action—such as clicking a link, sharing login details, or providing personal information.
The name “angler phishing” comes from the anglerfish, a deep-sea creature that uses a glowing lure to attract prey. Similarly, attackers use fake support responses as bait to lure victims into a trap.
This tactic is especially dangerous because it occurs in a public environment where people expect quick responses and immediate solutions.
How Angler Phishing Attacks Work
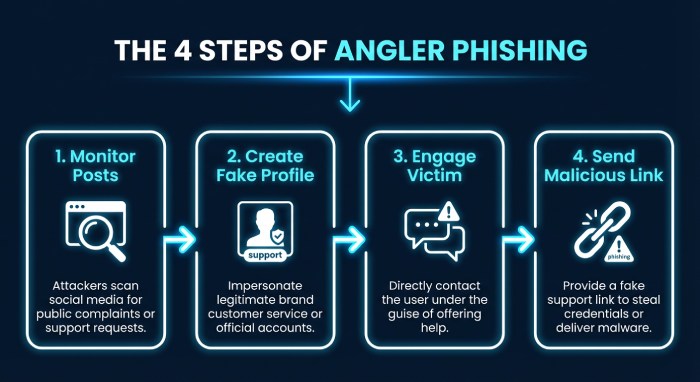
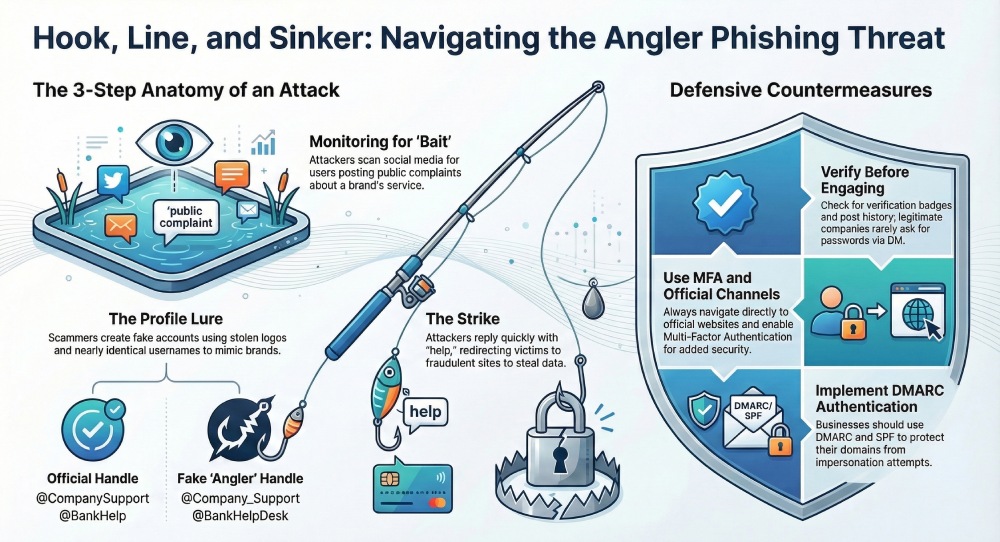
Angler phishing typically follows a predictable sequence. Understanding these steps can help both individuals and businesses recognize suspicious activity before damage occurs.
Monitoring Social Media Conversations
The first step in an angler phishing campaign involves monitoring social media platforms for mentions of a company or brand. Attackers look for posts where users are complaining about a product, service, or account problem.
For example, someone might tweet:
“My bank account isn’t working and customer service won’t respond.”
This message signals an opportunity for cybercriminals.
Creating Fake Customer Support Profiles
Attackers then create fake accounts that mimic official support pages. These profiles often copy company logos, usernames, and branding to appear legitimate.
Sometimes they slightly alter the username—for example:
- @CompanySupport → @Company_Support
- @BankHelp → @BankHelpDesk
These subtle differences are easy to overlook.

Engaging the Victim
Once the fake account is ready, the attacker replies to the victim’s post or sends a direct message offering assistance.
The message might say something like:
“Hello, we noticed your issue. Please DM us so we can help resolve your problem quickly.”
Because the victim expects support, they often respond without verifying the account.
Redirecting to a Malicious Site
After establishing contact, the attacker may ask the victim to click a link to “verify” their account or “reset” a password.
These links usually lead to fraudulent websites designed to collect login credentials or financial information. In some cases, the link may install malware on the victim’s device.
Once the attacker obtains the information, they can access accounts, commit identity theft, or carry out financial fraud.
Why Angler Phishing Is So Effective
Angler phishing works because it takes advantage of human emotions and expectations.
Customers Expect Fast Responses
When people post complaints online, they usually expect a quick response from the company. Attackers exploit this expectation by replying faster than the real support team.
Frustration Lowers Vigilance
Victims are often frustrated or angry about a service issue. In this emotional state, they may be less likely to verify whether the account contacting them is legitimate.
Fake Profiles Can Look Real
Modern social media profiles can be easily replicated. Attackers copy logos, branding, and language to mimic official support channels. Without careful inspection, many users cannot distinguish fake accounts from genuine ones.
Social Engineering Techniques
Angler phishing relies heavily on psychological manipulation. Attackers create urgency, offer quick solutions, and appear helpful in order to gain trust.
These tactics make victims more likely to follow instructions without questioning them.

Common Signs of an Angler Phishing Attack
Although angler phishing can be convincing, several warning signs often reveal the scam.
One common indicator is an unverified or suspicious account. Many legitimate company support accounts have verification badges or long activity histories. Fake accounts often lack these indicators.
Another red flag is a request for sensitive information. Legitimate companies rarely ask for passwords, financial details, or verification codes through social media messages.
Users should also be cautious of links that redirect to unfamiliar domains. Attackers frequently use fake websites that resemble legitimate login pages.
Finally, scammers often create pressure or urgency. Messages such as “Act immediately” or “Your account will be suspended” are common phishing tactics.
Recognizing these warning signs can help users avoid becoming victims.
How Individuals Can Protect Themselves
Protecting yourself from angler phishing requires awareness and caution when interacting with support accounts online.
Verify Official Accounts
Before responding to any support message, check whether the account is legitimate. Look for verification badges, follower counts, and a consistent posting history.
If you are unsure, visit the company’s official website and find the correct social media links.

Avoid Clicking Suspicious Links
Never click links sent through unsolicited messages. Instead, navigate directly to the company’s official website through your browser.
This simple habit can prevent many phishing attacks.
Use Multi-Factor Authentication
Multi-factor authentication (MFA) adds an extra layer of protection to your accounts. Even if attackers obtain your password, they cannot access the account without the second verification step.
Contact Companies Through Official Channels
If you receive a suspicious message from a support account, contact the company directly through verified channels such as their website or official customer support number.
This ensures that you are communicating with the real organization.
Report Fake Accounts
When you encounter a fake support profile, report it to the social media platform immediately. Reporting helps prevent others from falling victim to the same scam.
How Businesses Can Prevent Angler Phishing
Organizations also play a critical role in preventing angler phishing attacks.
Secure Your Brand With Email Authentication
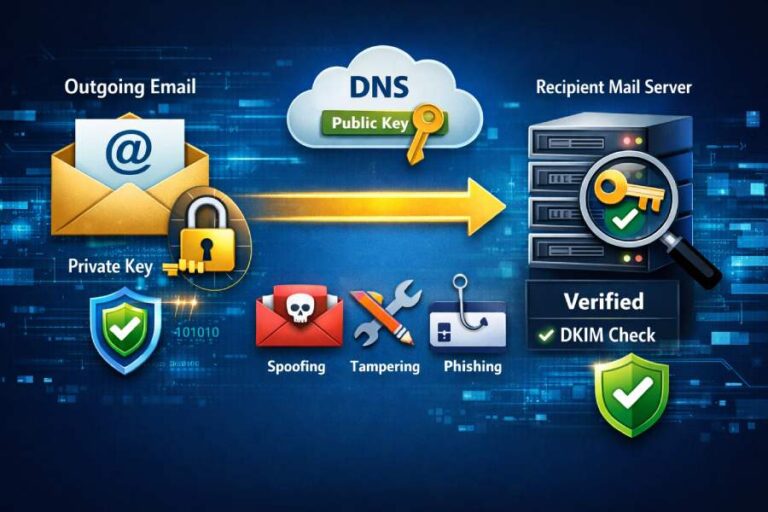
Technologies such as DMARC, DKIM, and SPF help protect organizations from email impersonation attacks that often accompany phishing campaigns.
DMARC allows organizations to instruct email providers on how to handle unauthorized messages claiming to come from their domain. This reduces the chances of attackers impersonating the company through email.
Solutions like DMARCReport provide monitoring and insights that help organizations detect spoofing attempts and strengthen domain protection.

Monitor Social Media for Impersonation
Companies should regularly monitor social media platforms for fake profiles impersonating their brand.
Automated monitoring tools can detect suspicious accounts using variations of company names or handles.
Educate Customers
Businesses should educate their customers about how legitimate support interactions work. For example, organizations can inform users that support agents will never request passwords or financial details through social media.
Providing clear guidelines helps customers recognize suspicious activity.
Maintain Verified Support Channels
Companies should maintain official, verified support accounts on major social media platforms. Visible verification badges help users distinguish genuine support teams from impostors.
The Role of Awareness in Preventing Angler Phishing
Technology alone cannot stop angler phishing attacks. Human awareness remains the most powerful defense.
Both individuals and organizations must understand how these scams work and stay alert when interacting online. Cybercriminals rely on deception and urgency, but informed users are much less likely to fall for these tactics.
Training employees, educating customers, and promoting cybersecurity awareness can significantly reduce the success of social engineering attacks.
Final Thoughts
Angler phishing is a sophisticated form of social engineering that exploits trust in social media customer support interactions. By impersonating legitimate support accounts, attackers lure victims into revealing sensitive information or clicking malicious links.
These scams succeed because they target people who are already seeking assistance and expecting help. However, with the right knowledge and precautions, angler phishing attacks can be avoided.
Users should always verify support accounts, avoid clicking suspicious links, and contact companies through official channels when in doubt. At the same time, organizations must monitor social media, educate customers, and implement strong email authentication protocols such as DMARC.
At DMARCReport, we believe that proactive email authentication, brand monitoring, and cybersecurity awareness are essential for protecting both businesses and customers from modern phishing threats.
As cybercriminal tactics continue to evolve, staying informed and vigilant remains the best defense against attacks like angler phishing.