7 ways admins can contribute to protecting G Suite from phishing

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report 7 ways admins can contribute to protecting G Suite from phishing
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
7 ways admins can contribute to protecting G Suite from phishing
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-14029">
<source src="https://media.mailhop.org/dmarcreport/images/2024/06/7-Ways-Admins-Can-Contribute-To-Protecting-G-Suite-From-Phishing.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H2M12S">2:12</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-14029" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-14029" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-14029" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-14029" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/7-ways-admins-can-contribute-to-protecting-g-suite-from-phishing/&t=7 ways admins can contribute to protecting G Suite from phishing" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/7-ways-admins-can-contribute-to-protecting-g-suite-from-phishing/&url=7 ways admins can contribute to protecting G Suite from phishing" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/06/7-Ways-Admins-Can-Contribute-To-Protecting-G-Suite-From-Phishing.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/7-ways-admins-can-contribute-to-protecting-g-suite-from-phishing/" class="input-link input-link-14029" title="Episode URL" readonly />
<button class="copy-link copy-link-14029" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-14029” readonly/>
<button class="copy-embed copy-embed-14029" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
Threat actors spare no one, and hence, it’s important for **G Suite administrators to stay one step ahead. According to a Verizon Data Breach Investigations Report, phishing accounts for 36% of data breaches, making it one of the most prevalent forms of cyberattacks.
G Suite includes an extensive suite of cloud-based tools, which attracts more users and makes it a lucrative target for bad actors. However, with the right strategies and proactive measures , admins can significantly enhance their organization’s defense against phishing attempts. In this blog, we’ll explore 7 effective ways G Suite administrators can fortify their systems and protect sensitive data from these malicious attacks.
1. Turn on the two-step verification
Two-step verification ensures threat actors don’t get access to G Suite accounts even if they steal passwords. This feature prevents phishing by asking users for additional proof of identity to sign in. These proofs can be in the form of phone prompts, voice calls, mobile app notifications, etc.

Admins can also implement user-managed security keys. These keys send an encrypted signature and work only with authorized websites. Admins can deploy and monitor them directly from within the Admin console.
2. Deploy Password Alert Chrome extension
The Password Alert is a Google Chrome extension that checks each page users visit for impersonations of Google sign-in pages. It also notifies users if G Suite credentials are entered on a platform other than Google Pages.
To enable it, go to Google Admin Console and go to Device Management> App Management
Password Alert. Under ‘User Settings’ and ‘Public session settings,’ enable ‘Force installation.’
To enjoy further benefits, admins can **enable password alert auditing and set up email alerts . This will help them stay protected if G Suite credentials are used on untrusted websites.
3. Give access to important data to only trusted apps
Google’s OAuth app allows admins to list out apps that can access G Suite data. This prevents malicious apps from fooling users into accidentally giving access to unauthorized people and platforms. To use this feature, check the ‘Admin’ console under ‘G Suite API Permissions.’

4. Implement SPF, DKIM, and DMARC
SPF, DKIM, and DMARC are email authentication protocols that instruct recipients’ **mail servers on how to deal with unauthenticated emails sent from your company’s domain. Admins can direct the receiving servers to mark such emails as spam or reject their entries. For the initial days of deployment, admins can also instruct recipients’ mailboxes to take no action against such emails and place them in inboxes, as usual. However, this practice should discontinue once the number of false positives goes down.
Enabling DKIM signing also verifies that **email content was not tampered with in transit to the recipient.
Feel free to contact us to get started with DMARC.
5. Disallow access to those who don’t need it
Gmail clients (Android, iOS, Web) use Google Safe Browsing to **enhance anti-phishing security by disabling suspicious links and attachments and showing warnings to users about suspicious content.
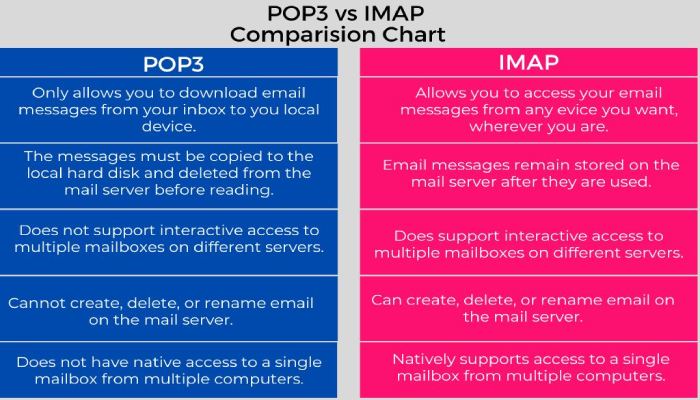
As admins, you can **enhance security by disabling POP and IMAP, Google Sync, and G Suite Sync for Microsoft Outlook, ensuring most G Suite users only use Gmail clients with built-in phishing protections . Additional measures include enabling the OAuth app to block third-party clients.
Note: Implementing these measures will prevent all third-party email clients, including native mobile mail clients, from working.
6. Encourage users to pay attention to external reply warnings
Gmail clients send warnings when users reply to emails sent from outside their domain by someone not listed in their contact list. This prevents users from getting manipulated by threat actors or even mistakenly sending an email to the wrong recipient.
Admins must encourage all users not to ignore these warnings and be careful if they choose to respond despite the warning. Admins can control these warnings by adjusting the ‘Advanced Gmail’ setting in the Admin console.
7. Enforce Android work profiles
With Android work profiles, users can separate their organization’s apps from personal apps. This way, their personal and work data are stored at different locations. If they start using the ‘Integrated device management’ feature in G Suite to enforce work profiles, they can allow approved applications to access **corporate data and block the installation of apps from unknown sources. This lets them control everything smoothly.

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.