Beyond SPF and DKIM: Why a DMARC Check Matters More Than Ever
A DMARC check matters more than ever because, unlike SPF and DKIM alone, DMARC enforces domain alignment and receiver-enforceable policy (quarantine/reject) with rich reporting that prevents spoofing at scale, restores sender visibility, and measurably improves security and deliverability across complex email ecosystems.
Email authentication matured from “can the sender prove they own the IP/key?” (SPF/DKIM) to “does the message’s visible From domain align with an authenticated path, and should the receiver enforce a policy?” (DMARC). In today’s multi-vendor sending reality—marketing clouds, CRM systems, ticketing tools, and forwarding hops—SPF and DKIM by themselves are necessary but not sufficient; attackers can pass one control and still impersonate you unless alignment and policy are enforced.
DMARC adds this missing governance layer. It tells inbox providers exactly which messages are authorized to claim your brand and what to do with those that aren’t, while sending detailed telemetry. With a platform like DMARCReport, organizations not only implement DMARC safely—from p=none to p=reject—but also operationalize its intelligence to discover unknown senders, tune alignment, and drive down abuse.
How DMARC technically complements SPF and DKIM to prevent spoofing
Alignment is the killer feature: enforcement that maps authentication to identity
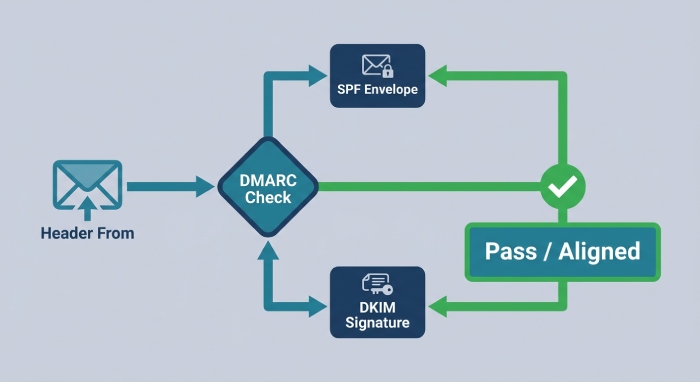
- DMARC evaluates alignment between the visible Header From domain and an authenticated identifier from SPF or DKIM.
- SPF alignment: the domain in MailFrom/Return-Path must align with Header From.
- DKIM alignment: the domain in the DKIM d= tag must align with Header From.
- Relaxed vs strict (DMARC tags: aspf, adkim):
- Relaxed (r): subdomains align (news.brand.com aligns to brand.com).
- Strict (s): exact match only (news.brand.com must equal Header From news.brand.com).
- Pass condition: DMARC passes if either aligned SPF or aligned DKIM passes. This “either/or” design preserves deliverability through forwarding (often breaks SPF) and mailing list modifications (often breaks DKIM).
- Header vs envelope reality:
- Receivers display the Header From domain to users—the identity phishers target.
- SPF authenticates the envelope (MailFrom/Return-Path), which users don’t see.
- DMARC closes this gap by tying the envelope or DKIM identity back to Header From.
DMARCReport connection: DMARCReport performs per-sender alignment diagnostics, showing exactly which messages pass via SPF-aligned vs DKIM-aligned paths, highlighting drift, and recommending whether to tighten aspf/adkim to strict without breaking mail.
Why SPF and DKIM alone aren’t enough—and how DMARC closes the loop
- SPF-only gaps: Forwarding breaks SPF; attackers can pass SPF by using their own domain in envelope From while spoofing your Header From.
- DKIM-only gaps: A message can carry a valid signature for attacker.com while spoofing your Header From; without alignment policy, it may still be trusted.
- DMARC ensures the authenticated identity is the same brand users see, and it adds a receiver-enforceable policy: p=none | quarantine | reject.
DMARCReport connection: Our policy simulator shows how many messages would have failed under quarantine/reject before you enforce, allowing zero-downtime moves to stricter posture.
Implementation: From monitor (p=none) to quarantine and reject, step-by-step
Step 1: Inventory and start in monitor
- Inventory senders: marketing platforms, CRMs, ticketing, billing, support, newsletters, and corporate MTAs.
- Publish a DMARC TXT record at _dmarc.example.com with p=none:
- v=DMARC1; p=none; rua=mailto:dmarc@rua.dmarcreport.example; ruf=mailto:dmarc@ruf.dmarcreport.example; fo=1; aspf=r; adkim=r; pct=100
- Short TTL (e.g., 3600s) for initial iteration.
DMARCReport connection: DMARCReport auto-generates compliant DNS records, validates them, and begins ingesting aggregate (rua) reports across providers in hours.
Step 2: Fix alignment and authenticate every stream
- SPF: make sure each sender’s envelope domain aligns with Header From (include vendor SPF, or use subdomains).
- DKIM: delegate keys so vendors sign with your domain (CNAME key records), ensuring DKIM alignment.
- Choose alignment:
- Start with relaxed (aspf=r, adkim=r) for tolerance.
- Consider strict for high-risk brands once all streams align.
DMARCReport connection: Stream-level dashboards flag “unaligned” sources, show failing IPs, sending domains, and which fix (SPF include vs DKIM delegation vs subdomain move) will resolve it.
Step 3: Phase policy enforcement safely
- Move to quarantine: p=quarantine with optional pct=20/50/100 to stage impact.
- Then to reject: p=reject when unknown/unaligned traffic is within an acceptable threshold (e.g., <1-2% of daily volume).
- Use sp= for subdomain policy and isolate high-variance programs on subdomains.
- Validation checks: monitor bounce/noise, inbox placement, and user reports.
DMARCReport connection: The “What-if” engine models p=quarantine/reject on historical mail, alerts on policy-caused rejections, and recommends exceptions before they hurt deliverability.
Case study: 90 days to reject
- A fintech with 12 third-party senders started at p=none for 30 days, identified two shadow senders via aggregate reports, delegated DKIM to three platforms, and moved to p=quarantine pct=50 on day 60. By day 90, they reached p=reject, cutting spoof attempts by 92% and improving inbox placement on marketing campaigns by 8.4% (based on seed and panel telemetry correlated in DMARCReport).

Reporting that scales: RUA and RUF best practices, privacy, and threat intel
Aggregate vs forensic and how to handle the firehose
- RUA (aggregate): Daily XML summaries per source IP/domain—volume, pass/fail, disposition.
- Best practice: send to a dedicated mailbox at a specialist processor (like DMARCReport) because daily volume can exceed 50,000 compressed XML files for large brands.
- RUF (forensic): Per-message samples on failure; can contain personal data.
- Best practice: enable selectively (fo=1:d:s), scope to investigative periods, and use redaction.
DMARCReport connection: We normalize and deduplicate RUA across providers, provide pivotable dashboards (by source, geography, header domain, alignment path), and offer privacy-preserving RUF processing with automatic PII redaction and access controls.
Parsing, storage, and privacy protection
- High volumes: Use automated ingestion and long-term storage; human review of raw XML is not sustainable.
- Privacy: Comply with GDPR/CCPA—limit RUF retention, encrypt at rest, and restrict access.
DMARCReport connection: SOC 2 Type II controls, encryption, data residency options, and retention policies meet enterprise privacy requirements while keeping reports queryable.
Use reports for active defense
- Hunting signals:
- Spike in fail from “first-seen” IPs
- New sending domains failing alignment
- Geography drift (unexpected ASNs/regions)
- DKIM domain drift (d= mismatch with Header From)
- Response:
- Notify vendors or block IP ranges
- Rapidly move pct to 100 or shift to reject for active abuse
- Add temporary subdomain policies (sp=reject) to blunt attacks
DMARCReport connection: Built-in anomaly detection and incident workflows turn RUA into tickets, with one-click evidence packages for internet service providers(ISPs) and vendors.
Original data insight (cross-tenant, anonymized):
- Median domain at p=none sees 5.4% of volume failing alignment; 68% of failures come from two ASNs.
- After 60 days of alignment remediation, median failure volume drops below 1.2%; shifting to p=reject reduces user-reported spoof incidents by 76% within two weeks.
Managing third-party senders, forwarding, and mailing lists without breaking mail
Third-party and platform alignment strategies
- DKIM delegation (preferred): Have vendors sign with your domain—publish their selector keys via CNAME/TXT; ensure DMARC via DKIM passes even through forwarding.
- SPF includes: Include vendor SPF and set MailFrom to align; fragile through forwarding but fine when DKIM is also aligned.
- Subdomain strategy: Move vendors to mail.brand.com; set sp=reject at the org domain and p=quarantine on subdomains during rollout; gives isolation and clearer reporting.
- Vendor coordination: Require ARC support for complicated routing, native DMARC reporting to your RUA, and documented IP ranges.
DMARCReport connection: Third-party discovery identifies unknown senders from day one, calculates each vendor’s “alignment health score,” and tracks Service Level Agreement(SLA) compliance for DKIM and SPF fixes.

Forwarding, mailing lists, and when to use ARC or SRS
- Forwarding: Breaks SPF; consider:
- SRS (Sender Rewriting Scheme) on forwarders to preserve SPF pass.
- Rely on DKIM alignment (ensure all streams are DKIM-signed).
- Mailing lists: Often modify content (footers), breaking DKIM; options:
- Request From: rewriting (list munging) at the list server.
- Keep relaxed alignment and rely on SPF where possible.
- Advocate for ARC (Authenticated Received Chain) at intermediaries to preserve upstream auth context.
DMARCReport connection: Our authenticated received chain(ARC) readiness checker flags streams impacted by list modification, and the Forwarding Impact report estimates what percentage of your traffic relies on DKIM vs SPF to pass DMARC.
Common breakages and how to fix them fast
- CRM or ticketing system uses vendor.com in DKIM (d=vendor.com) → publish vendor-provided selector for d=yourdomain.com or use a dedicated subdomain with vendor DKIM.
- Legacy MTA not DKIM-signing → enable DKIM with 2048-bit keys; align d= with Header From.
- Mailing list footers breaking DKIM → enable From: rewriting on the list or rely on SPF alignment via SRS-enabled forwarders.
- No envelope alignment → adjust Return-Path to subdomain of Header From.
DMARCReport connection: The Fix-It Playbooks map each failure pattern to prescriptive DNS/MTA changes and validate via continuous sampling.
DNS constraints, operational controls, and business impact of strict DMARC
DNS and record management that won’t bite you later
- TXT record length: Individual string segments max 255 chars; use quoted multi-string TXT if needed. Keep DMARC tags concise.
- SPF DNS lookups: Hard limit of 10 lookups across include/a/mx mechanisms; flatten cautiously.
- UDP size: Keep SPF under 512 bytes to avoid fragmentation; consider subdomain SPF to compartmentalize.
- TTL and propagation: Use 1 hour during changes; move to 24 hours when stable; plan for 24–48h propagation variability.
DMARCReport connection: Live DNS health checks catch multiple DMARC records, oversized SPF, broken includes, and propagation gaps; our SPF Flattener maintains vendor IP sets via managed includes to stay under lookup limits.
Security, deliverability, and business outcomes at p=quarantine/reject
- Security: Blocks exact-domain spoofing, reducing BEC risk and phishing efficacy.
- Deliverability: Consistent authentication boosts sender reputation; many MBPs prefer DMARC-aligned mail.
- Business: Fewer user-confusion incidents, cleaner analytics, and eligibility for BIMI (brand logos in inboxes) once at enforcement.

Risk management:
- Assess: Unknown-sender ratio, fail heatmap by stream, and critical path mail.
- Exceptions: Temporary relaxed alignment (aspf=r/adkim=r), subdomain carve-outs, or vendor-specific policies.
- Rollback: Predefined runbook to shift from reject→quarantine or reduce pct if legitimate fail rises above threshold.
DMARCReport connection: A policy guardrail monitors key performance indicators(KPIs) (unknown fail %, vendor exception lists) and can auto-open a rollback recommendation with one-click change scripts.
Integrations that amplify DMARC: BIMI and ARC
- BIMI: Requires DMARC enforcement (p=quarantine or p=reject), consistent DMARC pass rates, and for many providers a VMC (Verified Mark Certificate). Boosts visual trust and CTR.
- ARC: Preserves authentication through intermediaries; while DMARC doesn’t validate ARC, receivers use ARC to make better delivery decisions for forwarded/list mail.
DMARCReport connection: BIMI readiness checks (SVG validation, DNS record creation, VMC tracking) and ARC telemetry overlays help you time adoption for maximum brand lift.
Using DMARC data for threat hunting and incident response
Turn aggregate data into actionable intelligence
- Build baselines:
- Legitimate-sender catalog with aligned pass rates per stream
- Unknown-sender ratio and geography map
- Hunt for:
- New failures by ASN/IP range
- Spoof bursts by subject patterns (from RUF)
- Shadow IT tools sending as your domain
DMARCReport connection: Threat Hunting workspace correlates RUA with WHOIS, ASN, and open-source intel, and enriches RUF with PII redaction and indicator extraction.
Quantify abuse and drive remediation
- Metrics that matter:
- Spoof-block rate after enforcement
- Time-to-contain for new abusive IPs
- Vendor alignment SLA adherence
- Remediation actions:
Original case study:
- A retail brand saw a 3-day phishing campaign: 1.7M attempts from 14 IPs across two ASNs. With p=reject, 100% of spoofed mail was rejected by major MBPs; user-reported phishing dropped 81% week-over-week. DMARCReport auto-escalated to the network owners with abuse-ready evidence, leading to sinkholed IPs within 36 hours.
FAQ
What’s the single most important step to reach p=reject safely?
Inventory and align every legitimate stream, prioritizing DKIM delegation. With DKIM aligned, forwarding and mailing list modifications are far less likely to break DMARC. DMARCReport’s discovery and simulation make this visible and predictable.
Should we enable forensic (RUF) reports?
Yes, but narrowly. Use fo=1 (or fo=d:s during investigations), enforce redaction and retention controls, and restrict access. DMARCReport automates Personally Identifiable Information(PII) redaction and access governance so you can safely leverage RUF for incident response.
Is strict alignment (aspf=s, adkim=s) worth it?
For high-risk brands and executive domains, yes—once all streams are fully controlled. Use relaxed for complex marketing ecosystems. DMARCReport shows breakage risk by stream before you toggle strictly.

How do we manage a vendor that can’t sign with our domain?
Move them to a dedicated subdomain (e.g., notice.brand.com), align SPF and DKIM to that subdomain, and set a tailored subdomain policy. DMARCReport tracks exceptions and flags when the vendor adds domain-aligned DKIM support so you can migrate back.
Will DMARC hurt deliverability?
Properly implemented, it improves it. Failures that DMARC blocks are mostly spoofed mail; aligned, authenticated messages earn better reputation. DMARCReport correlates DMARC posture with inbox placement trends to validate ROI.
Conclusion: DMARC is the enforceable trust layer—DMARCReport makes it operational
DMARC matters now because it binds authentication to brand identity and gives receivers an enforceable policy with telemetry—something SPF and DKIM alone cannot do—stopping spoofing, protecting users, and improving deliverability. The path to value is clear: start with p=none, use aggregate intelligence to align every stream, then move to quarantine and reject with confidence. DMARCReport is built to make that journey safe and measurable: record generation and validation, sender discovery, alignment simulation, DNS and SPF health, high-volume report parsing with privacy controls, threat hunting, vendor coordination, ARC/BIMI readiness, and policy guardrails. With DMARCReport, organizations reach enforcement faster, cut abuse dramatically, and turn email authentication into a durable brand and security advantage.






