DKIM Key Rotation Best Practices: Here’s What Large Organizations Should Know

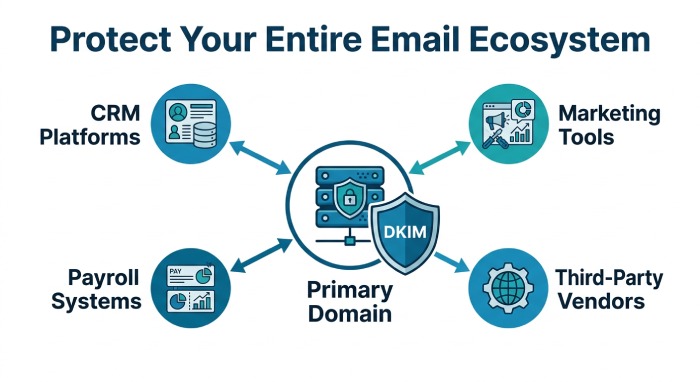
For large organizations, authenticating your domain with DKIM is not as straightforward as simply implementing the protocol for your primary domain.
After all, it’s not just a single domain that you have to protect.
From marketing tools to CRM platforms, payroll systems, and third-party vendors, there are many different systems that may be sending emails on your behalf. It is important that every email that goes out under your name reaches the recipient without any issues and is properly authenticated.
Let’s say you sent an invoice to your customer, but it was tampered with along the way. Or imagine that an attacker gets hold of one of your old DKIM keys and starts sending fake emails that appear to come from your business. Your customers may not realize that the emails are fraudulent because they still look legitimate and may even pass DKIM checks.
Such situations can only be avoided if you regularly rotate your DKIM keys and make sure that old keys are removed before they can be misused.
In this article, we will explain how to rotate your DKIM keys effectively, especially if you have a complex email ecosystem.
Why is it important to rotate your DKIM keys?
DKIM keys are cryptographic keys that are used to digitally sign your outgoing emails and prove that the message genuinely came from your domain and was not changed in transit. This is what makes them not only integral to your email security infrastructure but also a lucrative target for attackers.
Here are a few reasons why you should regularly rotate your DKIM keys:
Older DKIM keys are easier to misuse
If you use the same DKIM keys for too long, they become more susceptible to being stolen and misused by someone who shouldn’t have access to them in the first place. This is especially true for large organizations with complex email ecosystems.
If your old DKIM keys remain active in old mail servers, unused tools, or third-party platforms, attackers may be able to get access to them and send fake emails that appear to come from your organization.
Compromised DKIM keys can be used to send fraudulent emails
If your DKIM keys fall into the wrong hands, they can be used to send fraudulent emails that look like they are genuinely coming from your business. This happens when your DKIM keys haven’t been updated in a long time and are still active across different systems. Since these emails are signed with a valid DKIM key, they may still pass DKIM checks and look legitimate to recipients. As a result, your customers, employees, and partners may trust these emails and act on them.
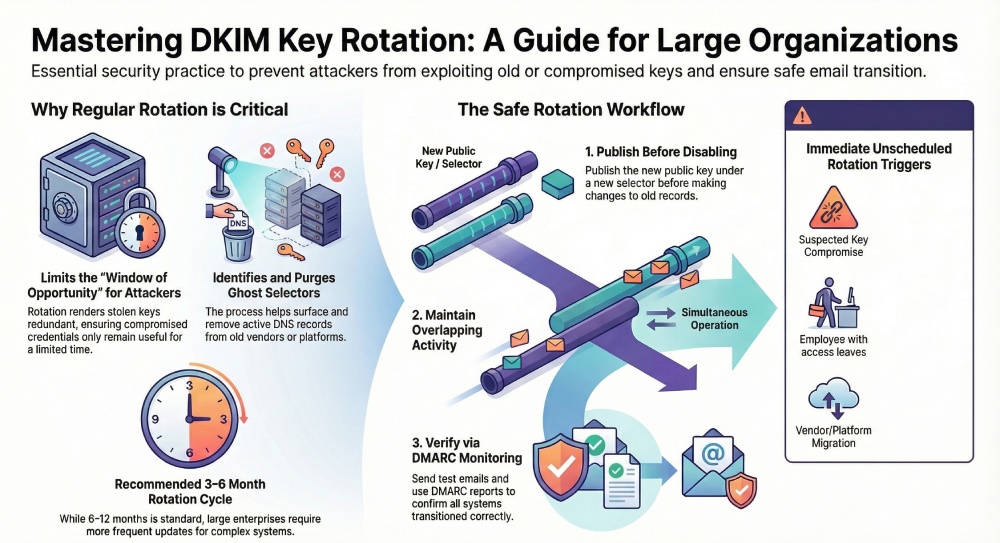
Regular key rotation limits the damage if a key is exposed
Even if an attacker gets access to your DKIM key, you can still rotate the key and replace it with a new one. By doing this, your previous key would be deemed redundant, and the attacker would no longer be able to send any further fraudulent emails using it.
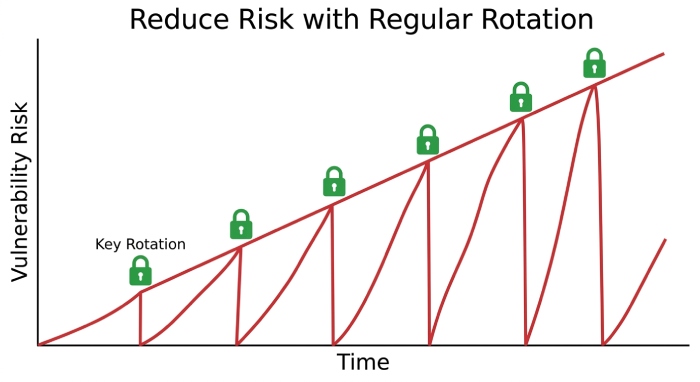
This reduces the time an attacker can misuse your DKIM key. If you rotate your keys regularly, even a stolen key only remains useful for a limited period before it is replaced and removed.
DKIM key rotation helps you identify outdated selectors
As a large enterprise, you might have multiple sending sources, each of which may use its own DKIM selector to sign emails. Over time, you might find that some selectors might no longer be in use, especially if you change vendors or switch platforms. However, their DNS records may still remain active.
By regularly rotating your DKIM key, you can review all your selectors, identify the outdated ones, and remove them before they become a security risk.
How often should you rotate DKIM keys?
There’s no deadline or fixed rule for when and how often you should rotate your DKIM keys. But that does not mean that you should keep using the same key for years.
It is often recommended that you rotate your DKIM keys every 6 to 12 months. But for large organizations with multiple email-sending sources and a complex ecosystem, the more frequently you do it, the better. Somewhere around 3 to 6 months might be a good starting point.
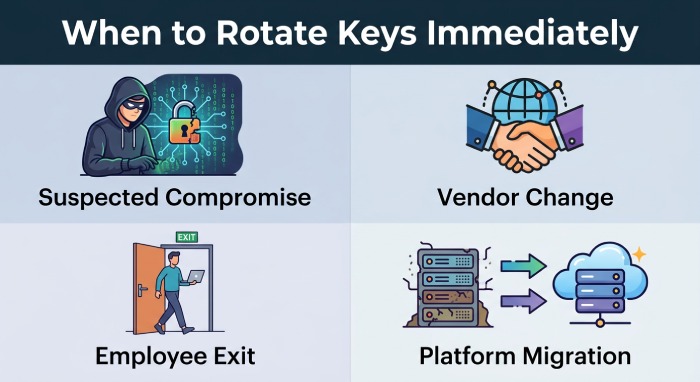
Apart from this, you should also rotate your DKIM keys immediately if you think a key has been compromised, if you stop using a vendor, if employees with access to your email systems leave the organization, or if you migrate to a new email platform.
The more sending systems you have, the more important it becomes to have a proper DKIM key rotation schedule in place so that old keys do not remain active longer than necessary. If you do not follow a schedule, chances are that you may forget to remove the old selectors or update the new ones.
How can you rotate DKIM keys without affecting email delivery?
- When you generate a new DKIM key pair, make sure that you publish the public key in your DNS under a new selector before making any changes to the old one.
- Once you have updated the new selector, do not disable the old one immediately; keep them both active for some time.
- Once this is done, update your mail servers, marketing tools, CRM platforms, and third-party vendors so that they start signing emails with the new selector.
- After you have updated your sending systems, make sure to send a few test emails and check whether DKIM is passing correctly.
- Remember to monitor your DMARC reports to stay on top of any issues during the transition and confirm that all your systems are using the new selector properly.
Implementing and managing email authentication protocols is not always straightforward. If you don’t get it right, it might cost you email deliverability, customer trust, and brand reputation. If you need help implementing DKIM or rotating your DKIM keys, our team is here to help. Get in touch with us!







