Things Financial Institutions Need to Know About Spoofing

Quick Answer
_According to the FBI's 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report Things Financial Institutions Need to Know About Spoofing
Related: Free DMARC Checker ·How to Create an SPF Record ·SPF Record Format

The support tickets we get after a spoofing incident all start the same way: ‘we didn’t know someone was sending email from our domain,’ says Vasile Diaconu, Operations Lead at DuoCircle. DMARC reporting would have caught it weeks earlier. The cost of monitoring is nothing compared to the cost of a successful impersonation attack.
_According to the FBI’s 2022 Internet Crime Report (IC3), 300,497 US-based victims reported phishing incidents in a single year, and Business Email Compromise (BEC) caused more than $2.7 billion in direct losses. DMARC Report
Things Financial Institutions Need to Know About Spoofing
<button title="Play" aria-label="Play Episode" aria-pressed="false" class="play-btn">
Play Episode
</button>
<button title="Pause" aria-label="Pause Episode" aria-pressed="false" class="pause-btn hide">
Pause Episode
</button>
<audio preload="none" class="clip clip-16933">
<source src="https://media.mailhop.org/dmarcreport/images/2024/10/Things-Financial-Institutions-Need-to-Know-About-Spoofing.mp3">
</audio>
<button class="player-btn player-btn__volume" title="Mute/Unmute">
Mute/Unmute Episode
</button>
<button data-skip="-10" class="player-btn player-btn__rwd" title="Rewind 10 seconds">
Rewind 10 Seconds
</button>
<button data-speed="1" class="player-btn player-btn__speed" title="Playback Speed" aria-label="Playback Speed">1x</button>
<button data-skip="30" class="player-btn player-btn__fwd" title="Fast Forward 30 seconds">
Fast Forward 30 seconds
</button>
<time class="ssp-timer">00:00</time>
/
<!-- We need actual duration here from the server -->
<time class="ssp-duration" datetime="PT0H1M57S">1:57</time>
<nav class="player-panels-nav">
<button class="subscribe-btn" id="subscribe-btn-16933" title="Subscribe">Subscribe</button>
<button class="share-btn" id="share-btn-16933" title="Share">Share</button>
</nav>
RSS Feed
<input value="https://dmarcreport.com/feed/podcast/dmarc-report" class="input-rss input-rss-16933" title="RSS Feed URL" readonly />
<button class="copy-rss copy-rss-16933" title="Copy RSS Feed URL" aria-label="Copy RSS Feed URL"></button>
Share
<a href="https://www.facebook.com/sharer/sharer.php?u=https://dmarcreport.com/blog/podcast/things-financial-institutions-need-to-know-about-spoofing/&t=Things Financial Institutions Need to Know About Spoofing" target="blank" rel="noopener noreferrer" class="share-icon facebook" title="Share on Facebook">
</a>
<a href="https://twitter.com/intent/tweet?text=https://dmarcreport.com/blog/podcast/things-financial-institutions-need-to-know-about-spoofing/&url=Things Financial Institutions Need to Know About Spoofing" target="blank" rel="noopener noreferrer" class="share-icon twitter" title="Share on Twitter">
</a>
<a href="https://media.mailhop.org/dmarcreport/images/2024/10/Things-Financial-Institutions-Need-to-Know-About-Spoofing.mp3" target="blank" rel="noopener noreferrer" class="share-icon download" title="Download" download>
</a>
Link
<input value="https://dmarcreport.com/blog/podcast/things-financial-institutions-need-to-know-about-spoofing/" class="input-link input-link-16933" title="Episode URL" readonly />
<button class="copy-link copy-link-16933" title="Copy Episode URL" aria-label="Copy Episode URL" readonly=""></button>
Embed
/*! This file is auto-generated */ ’ title=“Embed Code” class=“input-embed input-embed-16933” readonly/>
<button class="copy-embed copy-embed-16933" title="Copy Embed Code" aria-label="Copy Embed Code"></button>
The **global banking sector has been experiencing a severe surge in cyberattacks, and the US Banking industry is no different. Renowned financial institutions like SunTrust, JP Morgan Chase, and Bank of America have faced the brunt of cybercriminal activities such as spoofing and phishing multiple times. Large or small, no banking institution is safe now from threat actors.
The sharp spike in the number of cyberattacks in the **banking industry is associated with the easy availability of artificial intelligence systems. AI has made it convenient, less time-consuming, and easy for threat actors to devise refined and laser-focused cyberattacks on financial institutions. The smaller the financial company, the bigger the risk because of the lack of a cybersecurity budget and awareness training programs.

The government and relevant authorities have taken cognizance of the situation. The US Consumer Financial Protection Bureau, or CFPB, is taking **significant measures such as the Electronic Fund Transfer Act (Regulation E).
Apart from experts and government agencies , financial institutions too must stay updated about cyberattacks, especially spoofing. Awareness and preparations, along with close collaboration with relevant authorities, can hopefully bring down the rate of such attacks to a great extent.
Let’s first understand spoofing in detail.
What is spoofing?
Spoofing is a popular type of cyberattack whereby threat actors impersonate well-known companies and mimic their logos, email addresses, display names, website URLs, etc., in order to create a sense of credibility. They do so easily by making small tweaks to names, logos, letters, symbols, etc., which go unnoticed by the victims. Spoofing enables threat actors to download malware, coax victims into sharing personal and financial data, wire funds, and so on.
As of 2025, DMARC is mandatory under multiple compliance frameworks. CISA BOD 18-01 requires p=reject for US federal domains. PCI DSS v4.0 mandates DMARC for organizations processing payment card data as of March 2025. Google and Yahoo require DMARC for bulk senders (5,000+ messages/day) since February 2024, and Microsoft began rejecting non-compliant email in May 2025. The UK NCSC, Australia’s ASD, and Canada’s CCCS all mandate DMARC for government domains. Cyber insurers increasingly require DMARC enforcement as an underwriting condition.
There are majorly 7 types of spoofing tactics , namely:
-
Domain spoofing
-
Caller ID spoofing
-
Text message spoofing
-
Facial spoofing

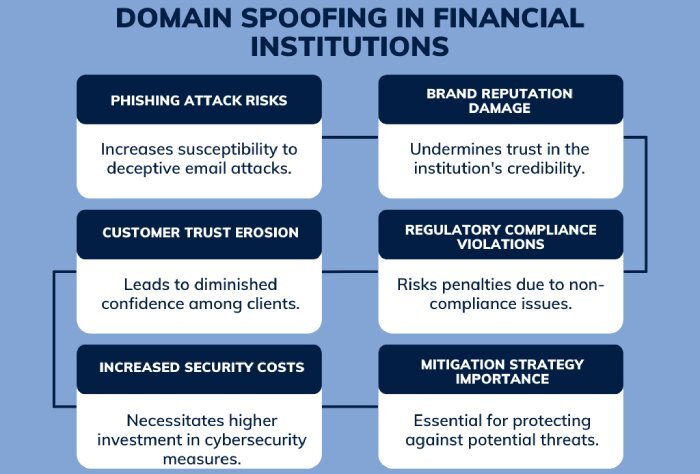
Domain Spoofing on Financial Institutions
According to research, around 62% of the 62,074 domains registered between January and June 2024 are involved directly or indirectly in spoofing activities. Major financial institutions like BBVA, PayPal, and HSBC have been frequent targets of spoofing attacks. Wells Fargo topped the list of the top 10 targeted companies in the first quarter of 2024 . The ‘Buy Now Pay Later’ scheme on cars, phones, clothes, and other products has also fueled spoofing attacks.
Cybercriminals target the **IT departments of financial institutions as well as their customers. The latter is targeted because of their lack of awareness and increased vulnerability. These threat actors create fake websites and drive traffic to the same by leveraging multiple tactics such as social media, phishing emails, text messages, etc.
They go to the extent of investing in **paid advertisements to rank their fake websites at the top of search engine results. When a naive user unknowingly clicks on any of these fake website links, they are asked to type in their login credentials, such as username and password.
Sophisticated spoofing attacks backed by artificial intelligence
The penetration of AI deep into our lives has made it easy for threat actors. With AI, they can easily plan and execute large-scale phishing and spoofing attacks. Not only this, AI also enables them to evade tracking mechanisms for quite a long time. With the help of artificial intelligence, threat actors also generate NSDs or **Newly Registered Domains to gain access to user data.
Artificial intelligence has made it quite convenient for cybercriminals to gain easy access to convincing phishing campaigns. Deep Learning, Natural Language Processing, and Machine Learning have been increasingly contributing to the creation of spoofs that can easily evade threat detection mechanisms. AI is a good learner, and with time, it will further make the spoofing tactics more sophisticated and flawless.
The attack on Pepco is a staggering reminder that **AI technology is being actively used to carry out sophisticated spoofing attacks.

What Is the Impact of advanced spoofing attacks on financial Institutions?
The damage does not stay restricted only to financial losses and individual victims. A spoof attack is a strong blow to the credibility and reliability of the banking sector. Multiple attacks on the same brand can further deteriorate its reputation and thereby affect its future relations with key stakeholders and customers.
Remedial steps and measures
It is high time financial institutions get strict with **prevention measures **in order to protect their employees as well as customers. To effectively combat the surge in cyberattacks in the banking sector, institutions should implement robust email authentication protocols such as SPF, DKIM, and DMARC to protect against spoofing and phishing threats.

Implementing threat intelligence can help prevent spoofing attacks by offering close monitoring day in and day out. It also helps **financial institutions stay a step ahead of threat actors by keeping them updated about the latest spoofing tactics and trends.
Using verifying redirections from **email or SMS text can also help check any kind of spoofing attempts.
Consumers should also be careful and practice cyber hygiene, such as using multi-factor authentication systems, strong passwords, and regularly updating banking apps.
Sources

General Manager
Founder and General Manager of DuoCircle. Product strategy and commercial lead for DMARC Report's 2,000+ customer base.
LinkedIn Profile →Take control of your DMARC reports
Turn raw XML into actionable dashboards. Start free - no credit card required.