Phishing in 2025: A DMARCReport Perspective on Trends, Risks, and Defense
Phishing is no longer just a nuisance—it has evolved into one of the most persistent and damaging cybersecurity threats facing organizations today. At DMARCReport, we continuously analyze global email traffic, authentication patterns, and attack vectors to understand how phishing is evolving and what organizations must do to stay protected.
What the data shows is clear: phishing is not slowing down. It is becoming more targeted, more sophisticated, and more difficult to detect. Organizations that fail to adopt strong email authentication protocols are increasingly exposed—not only to financial loss, but also to reputational damage and operational disruption.
This report provides a comprehensive breakdown of current phishing statistics, industry trends, and the growing role of DMARC in modern cybersecurity.
The State of Phishing: A Global Threat That Won’t Fade
Phishing has been a dominant cyberattack method since the early days of the internet, and its effectiveness remains alarmingly high. Attackers continue to exploit human trust, using deceptive emails, spoofed domains, and malicious links to steal credentials and sensitive information.
Recent data confirms that phishing remains the most common entry point for cyberattacks. In fact, studies indicate that a significant percentage of security breaches begin with a phishing email, making it one of the most dangerous initial attack vectors.
What makes phishing particularly dangerous is its adaptability. Attackers are now leveraging automation, artificial intelligence, and social engineering techniques to craft highly convincing messages that bypass traditional detection methods. These emails often appear indistinguishable from legitimate communications, increasing the likelihood of user interaction.

Key Phishing Statistics You Should Know
From a global perspective, the scale of phishing activity is staggering. DMARCReport analysis highlights several critical findings:
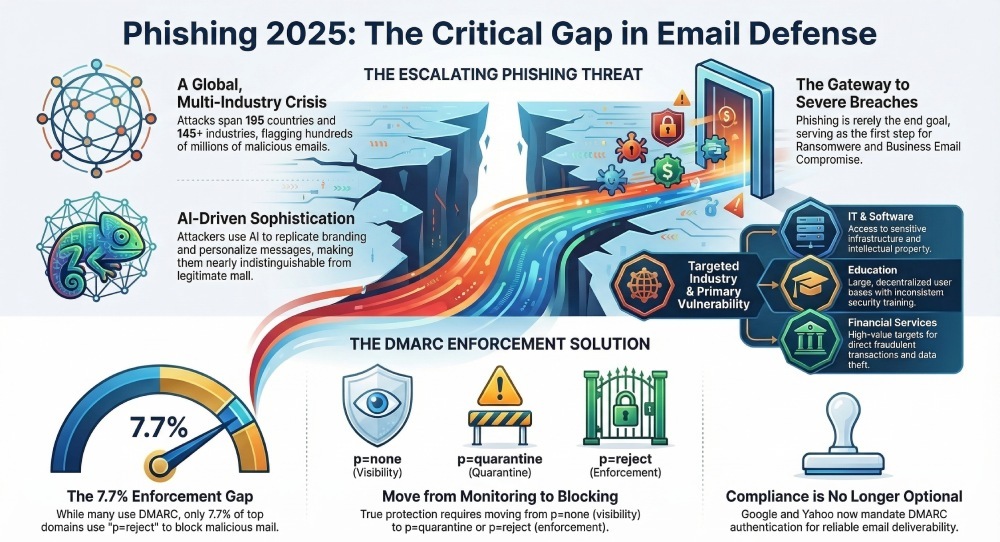
- Phishing attacks have been detected across 195 countries, targeting organizations worldwide.
- Over 145 industries and tens of thousands of companies have been affected.
- Hundreds of millions of suspicious emails are flagged annually as non-compliant or malicious.
These numbers underscore a critical reality: no organization is too small or too large to be targeted. Phishing is not selective—it is opportunistic, scalable, and relentless.
Even more concerning is the growth trajectory. The volume of phishing attempts continues to rise year over year, fueled by increasingly accessible attack tools and global digital expansion.
Industries Most at Risk
While phishing affects every sector, some industries are disproportionately targeted due to the value of their data or operational vulnerabilities.
1. IT and Software Services
The IT sector consistently ranks as the most targeted industry, accounting for a significant share of phishing attacks. This is largely due to its access to sensitive infrastructure, credentials, and intellectual property.
2. Education
Educational institutions are another major target. With large, decentralized user bases—including students, faculty, and administrative staff—these organizations often lack uniform cybersecurity training, making them more susceptible to phishing attempts.
3. Financial Services
Financial organizations remain prime targets because of the direct monetary gain attackers can achieve. Phishing campaigns in this sector often aim to access accounts, authorize fraudulent transactions, or steal customer data.
Across all industries, the common denominator is human vulnerability combined with insufficient email authentication controls.

Geographic Trends: Where Attacks Originate and Land
Phishing is a global issue, but certain regions stand out both as targets and as sources of attacks.
The United States, for example, remains the most targeted country, accounting for a substantial portion of phishing activity. This is largely due to its large digital economy and concentration of high-value organizations.
At the same time, phishing campaigns often originate from regions where compromised infrastructure, botnets, or less stringent cybersecurity enforcement enable attackers to operate at scale.
This global distribution highlights an important point: phishing is not confined by borders. Organizations must adopt security measures that are equally global in scope.
Why Phishing Remains So Effective
Despite widespread awareness, phishing continues to succeed at alarming rates. There are several reasons for this:
Human Behavior
Employees remain the weakest link in cybersecurity. Even with training, users can still be tricked by well-crafted emails, especially those that create urgency or mimic trusted sources.
Technological Sophistication
Attackers now use AI-driven tools to generate realistic email content, replicate branding, and personalize messages. This significantly increases the success rate of phishing campaigns.
Email Infrastructure Limitations
Traditional email systems were not designed with strong identity verification in mind. Without additional authentication layers, it is relatively easy for attackers to spoof domains and impersonate legitimate senders.
The Critical Role of DMARC in Phishing Prevention
At DMARCReport, we emphasize that phishing cannot be effectively mitigated without proper email authentication—and this is where DMARC becomes essential.
DMARC (Domain-based Message Authentication, Reporting & Conformance) works alongside SPF and DKIM to verify that emails are legitimately sent from authorized sources. It allows domain owners to define policies that instruct receiving servers on how to handle unauthenticated messages.
When properly implemented, DMARC can:
- Prevent domain spoofing
- Block fraudulent emails before they reach inboxes
- Provide visibility into email activity and threats
- Improve email deliverability and trust
Without DMARC enforcement, attackers can easily impersonate domains, making phishing attacks far more effective.
The Adoption Gap: A Major Security Concern
Despite its effectiveness, DMARC adoption remains surprisingly low.
Research shows that only a small percentage of domains have implemented strong DMARC policies that actively reject malicious emails. In fact, just 7.7% of top domains are fully protected with strict enforcement (p=reject).
Even more concerning:
- Over half of domains lack basic DMARC implementation
- Many organizations use passive policies that do not block threats
A significant portion lacks proper reporting configurations
This gap creates a massive opportunity for attackers. Without enforcement, DMARC becomes a monitoring tool rather than a protective barrier.

The Impact of New Email Security Requirements
Recent policy changes by major email providers have further highlighted the importance of authentication.
Companies like Google and Yahoo have introduced stricter requirements for email authentication, pushing organizations to adopt DMARC and improve their email security posture.
These changes mark a shift toward a more secure email ecosystem, where unauthenticated messages are more likely to be rejected or sent to spam.
For organizations, this means that DMARC is no longer optional—it is becoming a baseline requirement for reliable email communication.
Phishing as a Gateway to Larger Attacks
Phishing is rarely the end goal. Instead, it is often the first step in a larger attack chain.
Successful phishing attempts can lead to:
- Credential theft
- Business Email Compromise (BEC)
- Ransomware deployment
- Data breaches
Because of this, phishing acts as a gateway threat—one that enables more severe and costly cyber incidents.
Stopping phishing at the email level is therefore one of the most effective ways to prevent broader security breaches.
Why DMARC Enforcement Matters
Not all DMARC implementations are created equal.
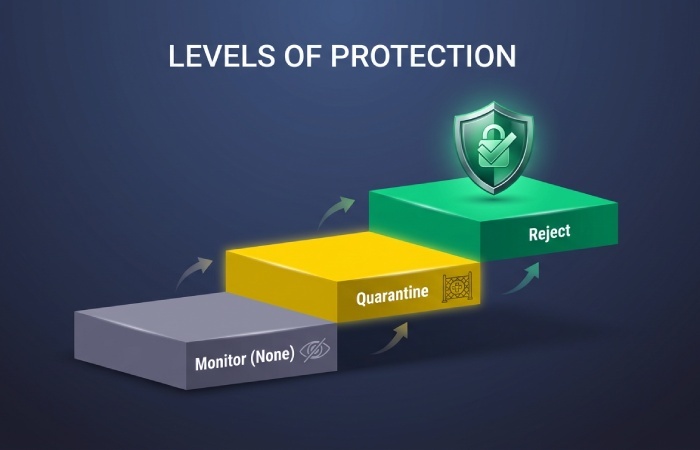
There are three primary policy levels:
- p=none – Monitoring only
- p=quarantine – Suspicious emails sent to spam
- p=reject – Unauthorized emails blocked entirely
Organizations that remain at p=none gain visibility but do not actively prevent phishing. True protection comes from moving to enforcement policies such as quarantine or reject.
As our analysis shows, partial implementation is not enough. Without enforcement, organizations remain vulnerable—even if they have DMARC records in place.
The Future of Phishing and Email Security
Phishing is not going away. In fact, it is becoming more advanced and more difficult to detect.
Several trends are shaping the future:
- Increased use of AI in phishing campaigns
- More personalized and targeted attacks
- Greater reliance on compromised infrastructure
- Continued expansion of digital communication channels
At the same time, we are seeing positive developments:
- Growing awareness of email authentication
- Increased adoption of DMARC
- Stronger enforcement by major email providers
These trends suggest that while phishing will remain a threat, the tools to combat it are also improving.
Final Thoughts from DMARCReport
Phishing is a persistent, evolving threat that demands a proactive and strategic response. The data is clear: organizations that fail to implement strong email authentication are at significantly higher risk.
DMARC stands out as one of the most effective defenses available today. When properly configured and enforced, it can dramatically reduce phishing risk and protect both organizations and their customers.
However, implementation alone is not enough. Organizations must:
- Move beyond monitoring to enforcement
- Continuously monitor and adjust configurations
- Educate employees on phishing risks
- Adopt a layered approach to email security
The fight against phishing is ongoing, but with the right tools and strategies, it is one that organizations can win.
At DMARCReport, we believe that stronger authentication, better visibility, and continuous vigilance are the keys to building a safer email ecosystem.